This topic answers frequently asked questions about the application protection feature in Security Center.
Application protection vs. WAF
Application Protection RASP (Runtime Application Self-Protection) and Web Application Firewall (WAF) are two different technologies that protect applications. RASP excels at protecting against attacks that target servers, such as zero-day attacks and attacks over encrypted traffic. WAF excels at defending against traffic-based attacks at the front end. The security capabilities of these two technologies are complementary, and we recommend that you configure both Application Protection and WAF.
Item | Application protection (RASP) | WAF |
Focus | Secures the application internally, regardless of the traffic source. | Filters and blocks attacks based on traffic signatures at the network layer. |
Common protection scope | Both provide defense against common web vulnerabilities, such as SQL injection, remote code execution, file inclusion, and webshells. | |
Specialization | Protects against zero-day vulnerabilities, attacks in complex encoded or encrypted traffic, in-memory webshells, non-HTTP protocol threats, and lateral movement within an internal network. | Protects against Denial-of-Service (DoS) attacks, web scrapers, and scanners, and provides access control and API security. |
Detection method | Analyzes application behavior to detect attacks. | Matches and filters traffic based on attack signatures. |
Deployment | On the server, integrated directly into the application runtime. | At the network edge, typically as a reverse proxy or in-line before the server. It is not installed on the application server. |
Performance impact | Consumes a small amount of server resources. | Consumes WAF resources. No performance impact on the application or origin server. |
Remediation | Applies a virtual patch and can pinpoint the exact line of code being exploited. | Applies a virtual patch and reports the signature of the exploit attempt. |
Zero-day vulnerability prevention | Supported by default. | Requires custom rules based on the specific exploit pattern. |
Verify application protection
Log on to the Security Center console.
In the left-side navigation pane, choose . In the upper-left corner of the console, select your asset region: Chinese Mainland or Outside Chinese Mainland.
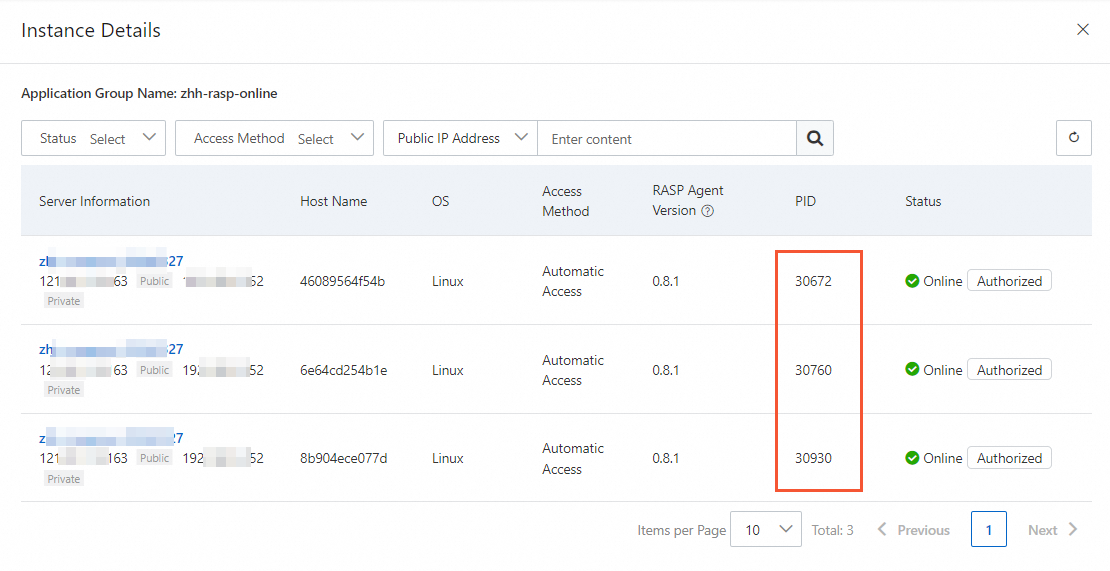
On the Application Protection page, click the Application Configurations tab. Find the target application group and click the number in the Authorized Process column.
In the instance details panel, view the list of protected applications.
If the process ID (PID) of your application appears in the list, your application is protected.
Performance impact
Application protection has minimal impact on system performance, compatibility, and stability. In performance tests, enabling application protection resulted in a CPU overhead of less than 1%, less than 50 MB of additional memory usage, and an application latency increase of less than 1 millisecond.
To further ensure stability, application protection includes safeguards such as a soft circuit-breaking mechanism. For more information, see Enable application protection.
Choose a protection mode
Attacks detected by application protection represent real security threats. Unlike traditional traffic-based detection, the false positive rate is extremely low. Therefore, treat all detected attacks seriously. By default, application protection operates in Monitor mode. After you verify that your application runs stably, you can switch to Block mode.
Why is no attack data displayed?
This may occur for two main reasons:
The target application is not fully integrated. Try enabling protection for the application process again. For more information, see Enable application protection.
No real attacks have occurred. Unlike a traditional firewall that alerts on malicious signatures, application protection only reports verified attacks that have a real impact. For example, an attack that exploits a PHP vulnerability is harmless in a Java environment and would not be reported. A verified attack from application protection means an attacker has likely bypassed your perimeter defenses. While you may not see a high volume of these attacks, each one is a critical event that requires immediate attention. You should block the attack or patch the underlying vulnerability.
Weakness detection vs. baseline checks
The weakness detection feature analyzes an application's runtime behavior and memory to identify potential risks. The baseline check feature scans for security risks in system configurations, such as compliance with CIS Benchmarks, and detects issues in static files.
Why protection enablement fails
Protection can fail for the following reasons:
If anti-virus software is installed on the host, it may quarantine the Security Center agent or the RASP agent. Check the quarantine log of your anti-virus software.
On a Linux server, check if the password for the root account has expired.
Identifying service blocks
If you find a AliCloudRaspSecurityException runtime exception in your service logs, it means RASP has detected a potential security threat and blocked the corresponding process. If this block is a false positive and you want to allow this behavior, add the process to a whitelist. For more information, see Create whitelist rules.