Agent Security Center provides full lifecycle security management for AI Agents. It supports asset inventory, relationship diagram display, risk detection, and security protection. This topic describes the features and usage of the Agent Security Center overview page.
View Agent Overview Information
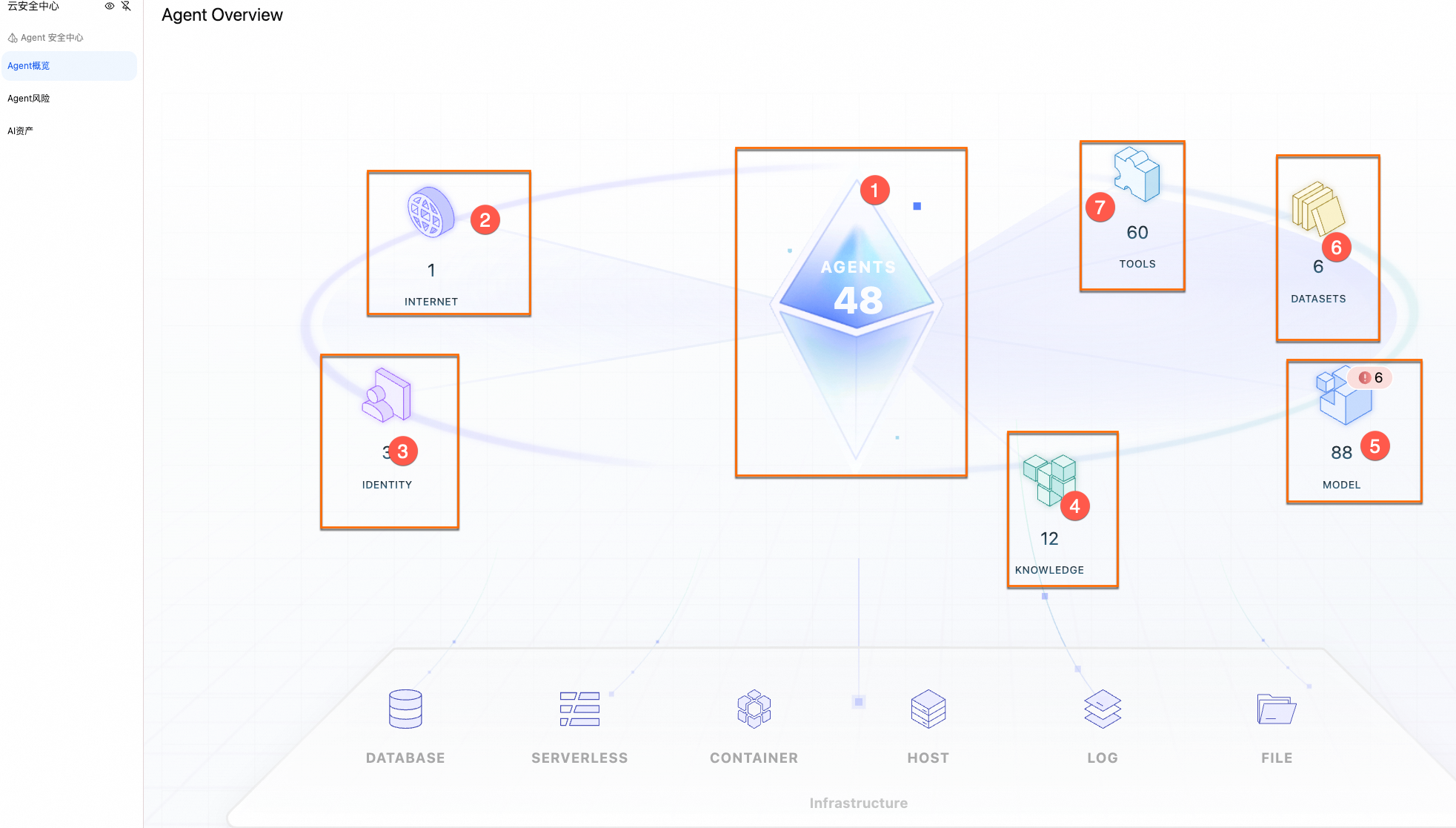
The Agent Overview page displays statistics and a list of all currently connected AI Agents. This helps you quickly understand your overall security posture.
You can go to Security Center console > Agent Security Center > Agent Overview. In the upper-left corner of the page, select the region where your assets are located: Chinese Mainland or Outside Chinese Mainland.
In the central area of the Agent Overview homepage, you can view overall statistics for AI Agents across all connected platforms and cloud products.
Area
Term
Description
Figure 1
Agents
Agents with autonomous decision-making and tool calling capabilities.
Figure 2
Internet
Network access entry point, mainly referring to the public network, such as URLs and domain names through which Agents provide external services.
Figure 3
Identity
Related to identity and credentials.
Figure 4
Knowledge base
Knowledge base, such as RAG.
Figure 5
Model
Refers to AI core algorithm files (such as .safetensors) or model services hosted by cloud vendors.
Figure 6
Training dataset
Dataset used for AI training.
Figure 7
Tools
Specific functional interfaces or script plugins that Agents can invoke.
You can click Figure 1 (AGENTS icon) to go to the Agent List page and view all currently connected Agents.
View Agent Relationship Diagram
The Agent relationship diagram visually displays the relationships between a single Agent and its associated instances, such as models, tools, and knowledge bases. This helps you intuitively understand the Agent's architecture and dependencies.
In the central area of the Agent Overview homepage, you can click the Agent icon to go to the Agent List page.
View Relationship Diagram
You can click the target Agent to view its relationship diagram, which includes information about models, tools, and other components, in the central area on the right.
You can click the corresponding module icon in the diagram to view associated details. For example, if you click a model, you can view the list of models associated with the current Agent.
View Risks and Security Status
You can click the target Agent to view the following information on the right side of the relationship diagram:
Pending Risks: These are risks detected by the current Agent that need to be addressed. You can click the risk name to view risk details and Recommended Actions. For more information about risks, see Agent Risks.
Security Status:
Alibaba Cloud Security Products: These are Alibaba Cloud security products that provide security detection and protection services. If activated, you can click
 to go to the console of the corresponding product.Note
to go to the console of the corresponding product.NoteCurrently, only Security Center, WAF, IDaaS, and AI Guardrails are supported.
AI Red Teaming:
Billing: Free for a limited time.
Detection Scope: It supports security risk scanning for AI models related to the current Agent, such as prompt injection, jailbreak attacks, obfuscation and smuggling attacks, and instruction and privacy leakage.
NoteThe specific model scope depends on the console.
Configuration Instructions: You can configure specific AI models and API keys. For details, see Detect Agent Risks.
View Security Product Activation Status
In the Agent Overview section, in the Security Service area, you can view the activation status of Alibaba Cloud security products under your current account. You can currently view the following products:
Security Center: Security Center is an intelligent cloud-native application protection platform (CNAPP) that integrates prevention, detection, response, administration, and visibility. It effectively protects the security of workloads, such as hosts, containers, and virtual machines, in multicloud environments. For more information, see What is Security Center.
WAF: Web Application Firewall (WAF) detects and protects against malicious characteristics in service traffic for websites or applications. It effectively ensures the business security and data security of websites. For more information, see What is Web Application Firewall.
IDaaS: IDaaS provides centralized and secure services for unified identity and access management. For more information, see What is Application Identity Service IDaaS.
AI Guardrails: AI Guardrails provides one-stop protection services for the input and output of Large Language Models (LLMs) and AI Agents. It covers risk scenarios, such as content compliance, sensitive data, prompt attacks, malicious files, malicious URLs, model hallucination, and prompt crawlers. It also supports digital watermarking for generated content. For more information, see What is AI Guardrails.
ImportantAI risks detected by AI Guardrails are synchronized to Agent Risks.