To implement fine-grained permission management for Security Center features, you can attach system policies or custom policies to Resource Access Management (RAM) users. This topic describes how to grant system and custom policies to RAM users for fine-grained permission management.
Background information
Resource Access Management (RAM) provides default system policies for Alibaba Cloud services and lets you create custom policies. System policies are created by Alibaba Cloud and cannot be modified. You can use custom policies to precisely control the access of RAM users to Security Center and the operations they can perform.
Security Center supports the AliyunYundunSASFullAccess policy, which grants RAM users full permissions for all Security Center features, and the AliyunYundunSASReadOnlyAccess policy, which grants RAM users read-only access to all data in Security Center.
Create a RAM user
For more information, see Create a RAM user.
Grant a system policy to a RAM user
Alibaba Cloud provides system policies for User Center and for accessing and managing Security Center. If a RAM user receives a No Permission message when they attempt to purchase, renew, or unsubscribe from a Security Center instance, or a No Permission. Check Your Permissions. message when they access Security Center, grant the required system policies to the RAM user as follows.
System policies in the User Center apply to all cloud products. When you grant these policies to a RAM user, the user is granted permission to purchase, renew, and cancel subscriptions for all cloud products.
Log on to the RAM console as a RAM administrator.
-
In the navigation pane on the left, choose .
On the Users page, find the required RAM user, and click Add Permissions in the Actions column.

You can also select multiple RAM users and click Add Permissions in the lower part of the page to grant permissions to the RAM users at a time.
-
In the Grant Permission panel, grant permissions to the RAM user.
Configure the Resource Scope parameter.
Account: The authorization takes effect on the current Alibaba Cloud account.
Resource Group: The authorization takes effect on a specific resource group.
ImportantIf you select Resource Group for the Resource Scope parameter, make sure that the required cloud service supports resource groups. For more information, see Services that work with Resource Group. For more information about how to grant permissions on a resource group, see Use a resource group to restrict a RAM user to managing only specific ECS instances.
Configure the Principal parameter.
The principal is the RAM user to which you want to grant permissions. The current RAM user is automatically selected.
-
Select a system policy based on the scenario and click OK.
Scenario
System policy
Purchase, renew, or unsubscribe from Security Center instances
AliyunBSSOrderAccess, AliyunBSSRefundAccess
Read-only access to Security Center
AliyunYundunSASReadOnlyAccess
Manage Security Center
AliyunYundunSASFullAccess
Click Close.
Grant a custom policy to a RAM user
Follow these steps to use custom permissions to precisely control the access of a RAM user to Security Center and the operations they can perform.
Step 1: Create a custom policy for Security Center
Log on to the RAM console as a RAM administrator.
In the left-side navigation pane, choose .
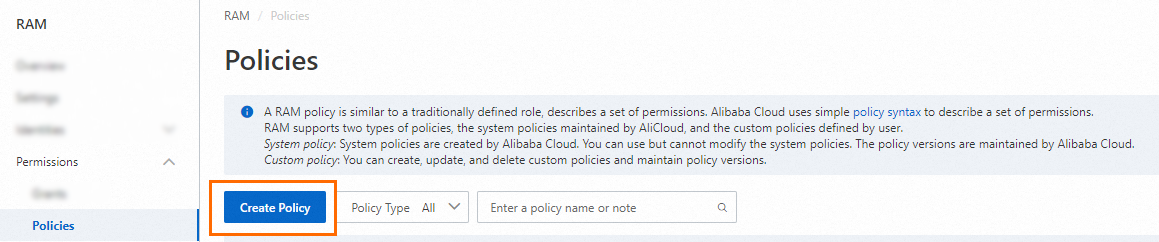
On the Policies page, click Create Policy.
-
On the Create Policy page, click the JSON tab. The following code provides common script examples:
-
Renewal and refund
Scenario
Script
Query the price for auto-renewal (
bssapi:QueryAvailableInstances) and configure auto-renewal settings (bssapi:SetRenewal){ "Version": "1", "Statement": [ { "Action": [ "bssapi:QueryAvailableInstances", "bssapi:SetRenewal", "bss:ModifyPrepaidInstanceAutoRenew", "bss:PayOrder", "bss:QueryPrice", "bss:RefundBatchRemainRefund" ], "Resource": "*", "Effect": "Allow" } ] }Modify auto-renewal settings (
bss:ModifyPrepaidInstanceAutoRenew)Pay for renewal and upgrade/downgrade orders (
bss:PayOrder)Display discounted prices (
bss:QueryPrice)Request a refund (
bss:RefundBatchRemainRefund) -
Read-only access to Asset Center
{ "Version": "1", "Statement": [ { "Action": [ "yundun-sas:DescribeCloudCenterInstances", "yundun-sas:DescribeFieldStatistics", "yundun-sas:DescribeCriteria" ], "Resource": "*", "Effect": "Allow" } ] } -
Security check in Asset Center
{ "Version": "1", "Statement": [ { "Action": "yundun-sas:ModifyPushAllTask", "Resource": "*", "Effect": "Allow" } ] } -
Read-only access to vulnerability management
{ "Version": "1", "Statement": [ { "Action": [ "yundun-sas:DescribeVulFixStatistics", "yundun-sas:DescribeVulDefendCountStatistics", "yundun-sas:DescribeVulMetaCountStatistics", "yundun-sas:DescribeVulListPage", "yundun-sas:DescribeVulNumStatistics", "yundun-sas:DescribeVulConfig", "yundun-sas:DescribeGroupedVul", "yundun-sas:DescribeVulDetails", "yundun-sas:DescribeVulList", "yundun-sas:DescribeVulWhitelist", "yundun-sas:DescribeAppVulScanCycle", "yundun-sas:ListVulAutoRepairConfig", "yundun-sas:DescribeEmgUserAgreement", "yundun-sas:DescribeEmgVulItem", "yundun-sas:DescribeUuidsByVulNames", "yundun-sas:DescribeTarget", "yundun-sas:DescribeVulTargetStatistics", "yundun-sas:DescribeConcernNecessity", "yundun-sas:DescribeOnceTask", "yundun-sas:GetOnceTaskResultInfo", "yundun-sas:DescribeCycleTaskList", "yundun-sas:DescribeVulExportInfo", "yundun-sas:DescribeInstanceRebootStatus", "yundun-sas:DescribeMachineCanReboot" ], "Resource": "*", "Effect": "Allow" } ] } -
Vulnerability management
{ "Version": "1", "Statement": [ { "Action": [ "yundun-sas:OperateVuls", "yundun-sas:ModifyCreateVulWhitelist", "yundun-sas:DeleteVulWhitelist", "yundun-sas:ModifyVulWhitelistTarget", "yundun-sas:ModifyOperateVul", "yundun-sas:ModifyStartVulScan", "yundun-sas:ModifyVulConfig", "yundun-sas:ModifyEmgVulSubmit", "yundun-sas:ModifyVulTarget", "yundun-sas:ModifyCycleTask", "yundun-sas:ModifyAppVulScanCycle", "yundun-sas:ModifyAutoDelConfig", "yundun-sas:ModifyConcernNecessity", "yundun-sas:DeleteVulAutoRepairConfig", "yundun-sas:CreateVulAutoRepairConfig", "yundun-sas:ExportVul", "yundun-sas:RebootMachine", "yundun-sas:DescribeVulFixStatistics", "yundun-sas:DescribeVulDefendCountStatistics", "yundun-sas:DescribeVulMetaCountStatistics", "yundun-sas:DescribeVulListPage", "yundun-sas:DescribeVulNumStatistics", "yundun-sas:DescribeVulConfig", "yundun-sas:DescribeGroupedVul", "yundun-sas:DescribeVulDetails", "yundun-sas:DescribeVulList", "yundun-sas:DescribeVulWhitelist", "yundun-sas:DescribeAppVulScanCycle", "yundun-sas:ListVulAutoRepairConfig", "yundun-sas:DescribeEmgUserAgreement", "yundun-sas:DescribeEmgVulItem", "yundun-sas:DescribeUuidsByVulNames", "yundun-sas:DescribeTarget", "yundun-sas:DescribeVulTargetStatistics", "yundun-sas:DescribeConcernNecessity", "yundun-sas:DescribeOnceTask", "yundun-sas:GetOnceTaskResultInfo", "yundun-sas:DescribeCycleTaskList", "yundun-sas:DescribeVulExportInfo", "yundun-sas:DescribeInstanceRebootStatus", "yundun-sas:DescribeMachineCanReboot" ], "Resource": "*", "Effect": "Allow" } ] } -
O&M engineer permissions
NoteIn the O&M engineer permissions scenario, this policy script allows a RAM user to use the vulnerability scan, vulnerability fixing, baseline check, and Asset Center features and perform related operations. After you attach this policy, refer to the actions and their descriptions in the Appendix: Common custom permission policies for features table in this topic to learn about the specific operations that the RAM user can perform.
{ "Version": "1", "Statement": [{ "Action": [ "yundun-sas:OperateVul", "yundun-sas:ModifyStartVulScan" ], "Resource": "*", "Effect": "Allow" }, { "Action": [ "yundun-sas:FixCheckWarnings", "yundun-sas:IgnoreHcCheckWarnings", "yundun-sas:ValidateHcWarnings" ], "Resource": "*", "Effect": "Allow" }, { "Action": "ecs:RebootInstance", "Effect": "Allow", "Resource": "*", "Condition": { "Bool": { "acs:MFAPresent": "true" } } }, { "Action": "ecs:*", "Effect": "Allow", "Resource": [ "acs:ecs:*:*:*" ] }, { "Action": "ecs:CreateSnapshot", "Effect": "Allow", "Resource": [ "acs:ecs:*:*:*", "acs:ecs:*:*:snapshot/*" ] }, { "Action": [ "ecs:Describe*" ], "Effect": "Allow", "Resource": "*" }, { "Action": [ "yundun-sas:ModifyPushAllTask", "yundun-sas:DeleteTagWithUuid", "yundun-sas:ModifyTagWithUuid", "yundun-sas:CreateOrUpdateAssetGroup", "yundun-sas:DeleteGroup", "yundun-sas:ModifyAssetImportant", "yundun-sas:RefreshAssets" ], "Resource": "*", "Effect": "Allow" } ] }
-
-
Click Continue To Edit Basic Information, and then enter a Name and Note for the policy.
-
Click OK.
Step 2: Grant permissions to the RAM user
Log on to the RAM console as a RAM administrator.
In the left-side navigation pane, choose .
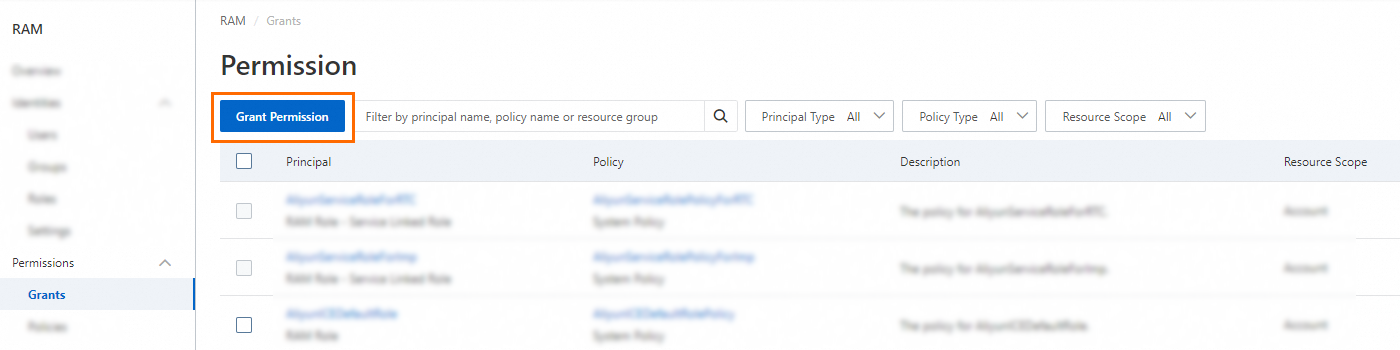
On the Permission page, click Grant Permission.
-
In the Grant Permission panel, grant permissions to the RAM user.
A newly created RAM user has no permissions by default.
Configure the Resource Scope parameter.
Account: The authorization takes effect on the current Alibaba Cloud account.
Resource Group: The authorization takes effect on a specific resource group.
ImportantIf you select Resource Group for the Resource Scope parameter, make sure that the required cloud service supports resource groups. For more information, see Services that work with Resource Group. For more information about how to grant permissions on a resource group, see Use a resource group to restrict a RAM user to managing only specific ECS instances.
Configure the Principal parameter.
The principal is the RAM user to which you want to grant permissions. You can select multiple RAM users at a time.
-
Select policies.
-
Search for and select the AliyunYundunSASReadOnlyAccess policy. This system policy grants the O&M engineer read-only access to Security Center.
-
Search for and select the custom policy that you created in Step 1: Create a custom policy for Security Center.
-
-
Click OK.
Appendix: Common custom permission policies for features
When a RAM user uses a specific feature of Security Center, you must grant the RAM user the corresponding custom permissions for the feature. The following sections describe the custom permission policy scripts for common feature modules of Security Center.
In most cases, each action in a RAM custom policy corresponds to an API operation of the Alibaba Cloud service.
Asset Center
|
Action in RAM policy |
Description |
Supported API |
|
yundun-sas:DescribeCloudCenterInstances |
Queries a list of assets. The information includes the asset type, whether security alerts exist, and the online status of the client. |
|
|
yundun-sas:DescribeFieldStatistics |
Queries the statistics of servers among your assets. |
|
|
yundun-sas:DescribeCriteria |
Obtains the query condition information that corresponds to the value you entered for a fuzzy search when you query assets. |
|
|
yundun-sas:ModifyPushAllTask |
Performs a security check task on servers. |
|
|
yundun-sas:DeleteGroup |
Deletes an asset group. |
|
|
yundun-sas:DescribeSearchCondition |
Queries the filter conditions for assets. |
|
|
yundun-sas:DescribeImageStatistics |
Queries the risk statistics of container image assets. |
|
|
yundun-sas:DescribeGroupedTags |
Queries the statistics of asset tags. |
|
|
yundun-sas:DescribeDomainCount |
Obtains the number of domain name assets. |
|
|
yundun-sas:DescribeCloudProductFieldStatistics |
Obtains the statistics of Alibaba Cloud services. |
|
|
yundun-sas:DescribeCloudCenterInstances |
Queries asset information. |
|
|
yundun-sas:DescribeAllGroups |
Queries information about all server groups. |
|
|
yundun-sas:CreateOrUpdateAssetGroup |
Creates a server group or modifies the servers in a server group. |
|
|
yundun-sas:DescribeInstanceStatistics |
Queries the risk statistics of assets. |
|
|
yundun-sas:PauseClient |
Enables or pauses the agent client. |
|
|
yundun-sas:ModifyTagWithUuid |
Modifies the name of an asset tag or modifies the assets that are included in a specified tag. |
ModifyTagWithUuid - Modify the name or associated assets of an asset tag |
|
yundun-sas:RefreshAssets |
Synchronizes the latest assets. |
|
|
yundun-sas:ExportRecord |
Exports the check results from pages such as Asset Center, Cloud Security Posture Management, Image Security Scan, Attack Analysis, and AccessKey Pair Leakage Detection to an Excel file. |
|
|
yundun-sas:DescribeExportInfo |
Views the progress of an asset export task. |
DescribeExportInfo - Describes the progress of an asset list export |
|
yundun-sas:DescribeDomainList |
Queries a list of domain name assets. |
|
|
yundun-sas:DescribeDomainDetail |
Obtains the details of a domain name asset. |
|
|
yundun-sas:DescribeAssetDetailByUuid |
Queries the details of an asset using the universally unique identifier (UUID) of the asset. |
Vulnerability management
|
Action in RAM policy |
Description |
Supported API |
|
yundun-sas:DescribeVulWhitelist |
Performs a paged query to query the vulnerability whitelist. |
|
|
yundun-sas:ModifyOperateVul |
Handles detected vulnerabilities. You can fix, verify, or ignore the vulnerabilities. |
|
|
yundun-sas:ModifyVulTargetConfig |
Configures vulnerability detection for a single server. |
|
|
yundun-sas:DescribeConcernNecessity |
Queries information about the necessity of fixing vulnerabilities that you follow. |
|
|
yundun-sas:DescribeVulList |
Queries vulnerability information based on the vulnerability type. |
|
|
yundun-sas:ModifyOperateVul |
Handles detected vulnerabilities. You can fix, verify, or ignore the vulnerabilities. |
|
|
yundun-sas:DescribeImageVulList |
Views the details of vulnerabilities that are detected by image security scans and a list of container images that are affected by the vulnerabilities. |
|
|
yundun-sas:ExportVul |
Exports a list of vulnerabilities. |
|
|
yundun-sas:DescribeVulExportInfo |
Views the progress of a vulnerability export task. |
Cloud Security Posture Management
|
Action in RAM policy |
Description |
Supported API |
|
yundun-sas:FixCheckWarnings |
Fixes baseline check risks. |
|
|
yundun-sas:IgnoreHcCheckWarnings |
Ignores or stops ignoring baseline check risks. |
IgnoreHcCheckWarnings - Ignore or unignore threats in a baseline in batches |
|
yundun-sas:ValidateHcWarnings |
Verifies baseline check risks. |
References
Policy elements: A RAM policy is used to describe the content of an authorization. A policy consists of basic elements such as Effect, Action, Resource, Condition, and Principal.
Policy structure and syntax: Learn about the structure and syntax of policies to create or update them.
Use RAM to manage the permissions of multiple O&M engineers: If your enterprise has various O&M requirements, you can use RAM to control the permissions of each type of O&M engineer to simplify permission management and control.
Use RAM to restrict the IP addresses that can be used to access Alibaba Cloud resources: You can use RAM to allow users to access your enterprise's cloud resources only from specified IP addresses. This improves access security.
Use RAM to restrict the period of time during which RAM users can access Alibaba Cloud resources: You can use RAM to allow users to access your enterprise's cloud resources only during a specified period. This improves access security.