The data loss prevention (DLP) feature of Secure Access Service Edge (SASE) lets you add watermarks to screens and applications to deter sensitive information leaks and trace their source. Visible watermarks discourage users from photographing or screenshotting sensitive content. Invisible watermarks embed tracing data that you can extract to identify the source of a leak.
This topic explains how to create watermark policies, extract invisible watermark data, view print-behavior detection results, and manage the watermark whitelist.
Prerequisites
Before you begin, make sure you have:
Purchased Internet Access DLP of SASE. For billing details, see Billing overview.
Added users and user groups. See Connect an LDAP IdP to SASE and Configure a user group.
Create a watermark policy
Log on to the SASE console.
In the left-side navigation pane, choose Data Loss Prevention > Policy Center.
Click the Watermark Management tab. On the Screen Watermark or Application Watermark tab, click Create Policy.
In the Create Policy panel, configure the following parameters.
Basic information
Parameter Description Policy name A name for the policy. Must be 2–32 characters and can contain letters, digits, hyphens (-), and underscores (_). Status Whether the policy is active. Valid values: Enabled or Disabled. The policy takes effect only when enabled. Priority The order in which policies are evaluated. Valid values: 1–100. A lower value means higher priority. User group The users or user groups the policy applies to. If you assign a user or user group to both a screen watermark policy and a printer watermark policy, both policies apply. Applicable application The applications covered by the policy. Required for application watermark policies. Before specifying applications, enable the web application access reinforcement feature for the corresponding office applications. Watermark settings
Parameter Description Visible watermark Configures the appearance of the visible watermark. Turn on Preview to see a live preview. To make the watermark clearly visible, set opacity to the maximum value. Invisible watermark Configures the invisible watermark that embeds tracing data. Configure based on your traceability requirements. Click OK.
After the policy is created, the policy is displayed in the policy list.
Extract invisible watermark data
After a suspected leak occurs, upload the affected file to extract the embedded tracing information.
Go to Watermark Management > Watermark Extraction.
Select a watermark type.
Upload the file that contains the invisible watermark.
SASE automatically extracts the invisible watermark data after the upload completes.
To export the extraction results, click Export on the right side of the page.
View sensitive behavior detection results
When a user prints a document, DLP automatically detects the printed file and logs it as a sensitive behavior event. Detection results cover the last 24 hours, 7 days, and 30 days.
In the left-side navigation pane, choose Data Loss Prevention > Sensitive Behavior Detection.
On the Sensitive Behavior Detection page, review the print statistics for the time range you need.
In the list, find the user and click Details in the Actions column.
Find the file and click Details to view its sensitive message, hit policy, office terminal, and outbound transfer channel.
Configure a watermark whitelist
If you want SASE not to audit and manage the sensitive behaviors of specific users, you can configure a watermark whitelist to allow specific users to perform sensitive operations.
On the Watermark Management tab, click Watermark Whitelist.
On the Whitelist > Data Loss Prevention tab, add the users to the screen watermark whitelist and the application watermark whitelist.
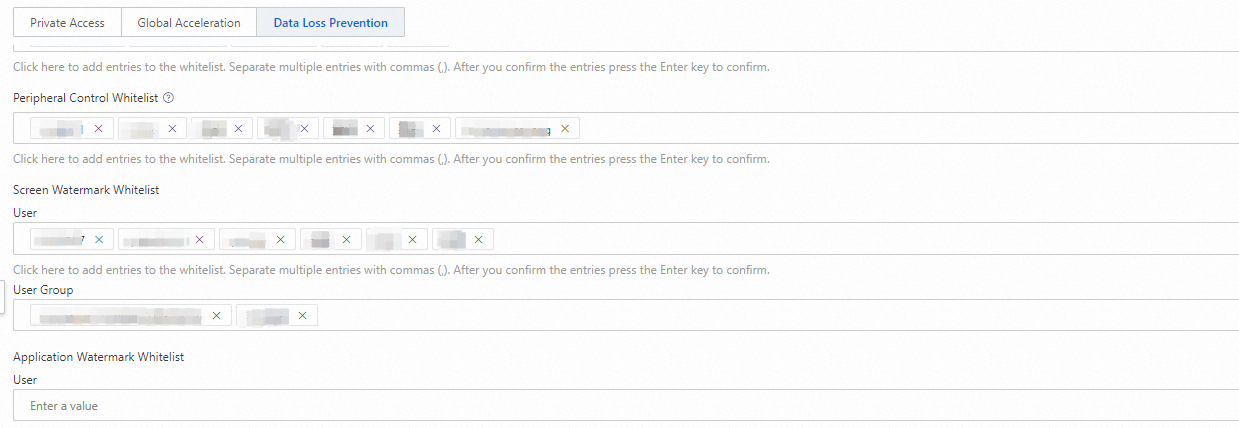
Click Submit.
More operations
Adjust policy priority
On the Watermark Management page, click the ![]() icon next to a policy and enter a new priority value (1–100). A lower value means higher priority.
icon next to a policy and enter a new priority value (1–100). A lower value means higher priority.

Disable a policy
In the policy list, turn off the toggle in the Policy status column. The policy is retained and can be re-enabled at any time.
Delete a policy
In the policy list, click Delete in the Actions column.
Deleted policies cannot be restored.
What's next
To view and trace outbound transfer logs for sensitive files, see Sensitive file detection.
To detect files transferred outside your organization, see Monitor outbound file transfers to ensure data security.
To control user access to peripherals, see Manage peripherals to ensure data security.