When employees send files outside your organization, SASE inspects each transfer against your classification and categorization detection rules. Files that match a rule trigger the enforcement action defined in your outbound policy. This topic explains how to define those rules.
Prerequisites
Before you begin, ensure that you have:
Purchased the Office Data Protection Edition of SASE for Internet access security. For more information, see Billing overview and Get started
SASE app version 4.3.1 or later installed on your corporate endpoints
Configuration methods
SASE provides three ways to configure detection rules for outbound files. Choose the one that fits your situation:
| Method | When to use |
|---|---|
| Built-in rules | Start here. SASE includes detection rules for common file types. Select them when creating an outbound policy—no additional setup required. |
| Custom rules | Use when built-in rules do not cover your requirements. Define conditions across multiple dimensions: file content, filename, file extension, and data source. |
| AI Recommendation library | Use when you have completed asset mapping. The large model learns from your files and generates detection rules automatically. |
To use detection rules from the AI Recommendation library, complete asset mapping first. The large model then learns from your files to intelligently generate the corresponding detection rules. For more information, see Create an asset mapping task.
Configure custom rules
Custom rules are built in two stages:
Create data elements — Define the raw detection ingredients: sensitive word libraries (dictionaries and regular expressions), file extensions, and data sources.
Create a detection rule — Combine those elements into a rule with conditions and a sensitivity level. SASE evaluates this rule against each outbound file.
Step 1: Create data elements
Data elements are the building blocks of custom detection rules. SASE organizes them across four tabs under Data Protection > Data Classification > Data Elements.
Log on to the Secure Access Service Edge console.
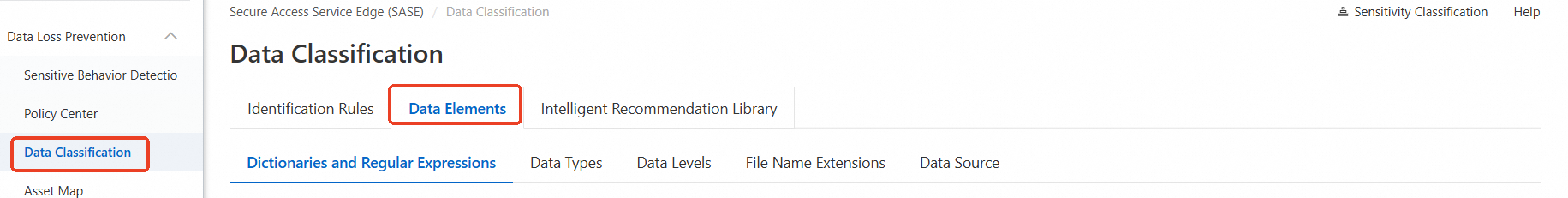
In the left navigation pane, choose Data Protection > Data Classification.
On the Data Classification page, click the Data Elements tab.
Configure each tab as needed:
Dictionaries and regular expressions
Build sensitive word libraries that SASE matches against file names and file content.
To create a sensitive word library:
Click Create Sensitive Word Library.
In the Create Sensitive Word Library panel, set the following parameters and click OK.
Dictionary: Enter the words or phrases to detect. Add multiple entries at once by separating them with commas (,) and pressing Enter.
Regular Expression: Enter a custom regular expression. For example,
([A-Za-z0-9]+)matches one or more uppercase or lowercase letters or numbers. After entering the expression, click Test Regular Expression and enter a test string to validate it.
Parameter Description Name A name for the sensitive word library Type Select Dictionary or Regular Expression
Other operations:
Filter libraries by type or data source.
To delete a library, click Delete in the Actions column.
A library associated with a detection rule cannot be deleted. Remove the association from the rule first.
Data types
SASE provides built-in algorithm classifications. When you configure a detection rule, select the appropriate algorithm classification. SASE uses it together with the file type to detect file content.
To see which detection rules use a given algorithm classification, check the Associated Rules column.
Data levels
SASE provides built-in algorithm categorizations. When you configure a detection rule, select the appropriate algorithm categorization. SASE uses it together with general definitions of data sensitivity and the amount of sensitive data to detect file content.
To see which detection rules use a given algorithm categorization, check the Associated Rules column.
File name extensions
SASE includes built-in file extensions. Add custom extensions to detect files by their extension.
To add a file extension:
Click Add File Extension.
In the Add File Extension panel, enter the file extension and click OK.
Other operations:
Filter extensions by data source.
To delete a custom extension, click Delete in the Actions column.
Data source
Register Web Applications and Code Repository as data sources. When a file downloaded from a registered source is sent outbound, SASE automatically triggers detection.
To add a data source:
Click Create Application.
In the Add Data Source panel, configure the fields for your source type:
Web Applications:
Parameter Description Example Application Name A name for the application — Application Address The URL and file path. Click Add to register multiple addresses. URL: www.aliyun.com/api/file; Path:/api/fileCode Repository:
Parameter Description Repository Name A name for the repository Git Repository URL The Git repository address Click OK.
Step 2: Create a detection rule
Detection rules combine data elements into conditions that SASE evaluates against each outbound file. Each rule belongs to a data category and carries a sensitivity level.
Create a detection rule
Log on to the Secure Access Service Edge console.
In the left navigation pane, choose Data Protection > Data Classification.
On the Data Classification page, click the Identification Rules tab.
In the Data Category area on the left, click Create, then click Create Category.

In the Create Category dialog box, enter a classification name and click OK.
To the right of the data classification you created, click Create Rule Group.

In the Create Group panel, configure the following and click OK.
Parameter Description Rule name 2–32 characters. Supports Chinese characters, letters, digits, hyphens (-), and underscores (_). Data category The data classification this rule belongs to. Sensitivity level The sensitivity tier of the files this rule targets. See Sensitivity levels below. Rule configuration The detection conditions. For example, a rule "Filename contains salary" flags any file whose name includes "salary".  Configure multiple conditions and set the logical relationship to AND or OR to match your business needs.
Configure multiple conditions and set the logical relationship to AND or OR to match your business needs.
Sensitivity levels
| Level | Scope |
|---|---|
| L4: Confidential data | Customers' sensitive personal information; macro-level feature data, predictive data, and credit data aggregated across departments. Unauthorized disclosure causes severe negative impacts, systemic threats, or major legal liability. Covers communication records of personnel involved in major decisions, investments, and financing. |
| L3: Secret/private data | Customer information and business data aggregated at department level. Unauthorized disclosure could directly or indirectly harm the company, customers, or employees—leading to financial, commercial, or reputational losses and potential legal liability. |
| L2: Internal data | Company data and customer information accessible only to employees or third parties who have signed a non-disclosure agreement. Unauthorized disclosure causes minor negative impacts. |
| L1: Public data | Data that is publicly accessible or approved for public release. No security or legal risk from public dissemination. |
Detection rule parameters
Manage detection rules
You can edit, enable, disable, or extend custom detection rules and rules generated by the large model.
Edit: Click Edit Group Information to view and modify a detection rule.
Enable/Disable: Click the Rule status switch to toggle a detection rule.
Sub-rules: Create sub-rules under an existing detection rule for more granular control.

What's next
To generate detection rules automatically from your file assets, see Intelligent rule generation.
To apply classification and categorization rules in an outbound file detection policy, see Configuration file exfiltration detection policy.
To set up asset mapping, see Create an asset mapping task.