Password-free logon eliminates the need for employees to manually authenticate every time they open the SASE client — corporate devices connect and authenticate automatically. This guide walks IT administrators through configuring the feature.
Prerequisites
Before you begin, make sure you have:
An active Secure Access Service Edge (SASE) subscription. Apply for a 7-day free trial or purchase the service
SASE client version 4.8.5 or later installed on all corporate devices that will use password-free logon
(If using a corporate identity source) Completed identity synchronization and enabled the identity source to sync your organization's structure
After you activate SASE, the system automatically creates a custom identity source. To enable it, go to Identity Authentication > Identity Access, open the Identity synchronization tab, and turn on the custom identity source. To add users manually, use the Employee Center tab. For details, see Employee Center.
Choose a sign-in scope
Before you enable the policy, decide which devices will use password-free logon and what identity they connect with. Your choice determines which steps you need to complete.
| Scope | How it works | Additional configuration |
|---|---|---|
| All Devices | Every device in the endpoint list — including manually imported corporate devices — connects with an anonymous identity. Data protection and endpoint protection policies still apply. Internal network access policies require manual logon. | None — SASE creates the extended authentication source automatically |
| Authenticated Devices | Only devices registered in the extended authentication source connect, using the device owner's identity. Username from the identity source record, or Company Employee if no user match is found. | Must manually create an extended authentication source and upload a device list |
Step 1: Enable the password-free logon policy
Log on to the SASE console.
In the navigation pane, choose Identity Authentication > Identity Access.
On the Authentication Management tab, click Single Sign-On Policy.
In the Client Auto-Sign-In Policy panel, enable the policy.
Set Scope of Automatic Sign-In to All Devices or Authenticated Devices based on your decision above.
Review Automatic Sign-In Status to see the devices the policy currently covers. Click the device count to open the Terminals page.
Click OK.
Step 2: Add an extended authentication source
If you selected All Devices: Skip this step. SASE automatically creates the extended authentication source, and all devices in the endpoint list can use password-free logon immediately.
If you selected Authenticated Devices: Follow these steps to manually create an extended authentication source.
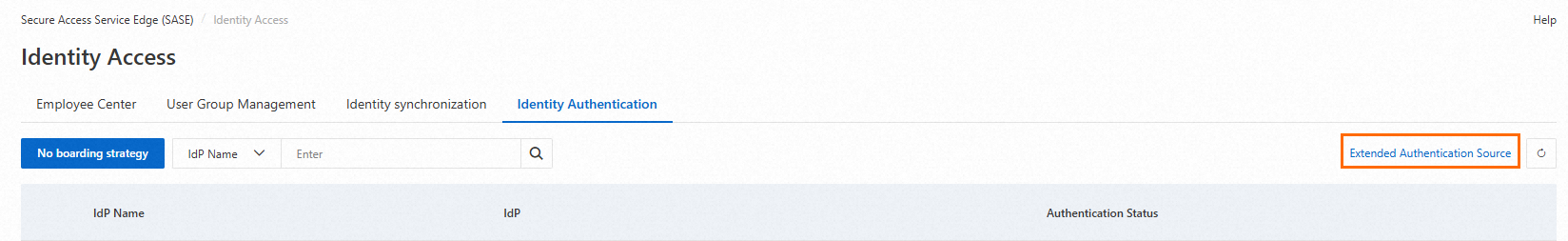
On the Authentication Management tab, click Extended Authentication Source in the upper-right corner.
On the Extended Authentication Source page, click Add Extended Authentication Source.
In the Add panel, configure the following settings, then click OK.
Configuration item Description Authentication Source Name A name for this authentication source. Use 2–100 characters. Supported characters: Chinese characters, letters, digits, hyphens (-), and underscores (_). Description A description that appears as the logon title in the SASE client, helping you identify the identity source during logon. Extended Authentication Source Configuration > Authentication Source Type Select Device Authentication. Associated IdP Select the identity provider to associate with this source. Under Authentication Source Type, click Download Import Template. Fill in the device information and user information for each device that will use password-free logon.
Field group Required fields Device information MAC address, SN, hostname User information Name, phone number, email 
Drag the completed file into the upload area, or click to browse and select it.
If the uploaded file contains duplicate information, password-free logon will not be enabled for that device.
How SASE matches device and user records:
Device record matches → password-free logon is enabled for that device.
User record also matches → the employee's username is displayed after logon.
User record does not match → the username is displayed as Company Employee.
Step 3: Verify logon on the client
After configuration is complete, ask an affected employee to verify the logon experience:
Open the SASE client on the corporate device.
Enter the enterprise identity and click Confirm. The client logs in automatically — no password prompt appears.
Check the displayed username:
If device authentication matched a user record, the employee's own username appears.
If no user match was found, the username shows as Company Employee.
If an employee is in the All Devices scope but needs access to internal network resources, they must still log on manually. Consider switching to Authenticated Devices scope and uploading a complete device list to enable identity-based access.
What's next
To manage devices covered by this policy, go to Terminal Management > Terminals in the SASE console.
To add employees to the custom identity source, use the Employee Center tab under Identity Authentication > Identity Access.