This topic describes how to configure an Secure Access Service Edge (SASE) connector to connect to your corporate intranet. You can also integrate Global Accelerator (GA) to provide your globally distributed employees with fast, stable, and secure access to internal corporate applications.
Prerequisites
Before you begin, make sure that the following prerequisites are met:
You have activated Secure Access Service Edge (SASE).
You have an Alibaba Cloud account and the required permissions to manage SASE, GA, VPC, and ECS.
The SASE client is installed on employee devices in the acceleration region.
Acceleration traffic workflow
The following figure shows an example of a user in Shanghai, China, accessing a service in Silicon Valley, USA.

Costs
When you enable GA, a pay-as-you-go GA instance is automatically created in Global Accelerator (GA). Be aware that this feature incurs additional fees.
Configure SASE identities and users
Step 1: Create an identity source
Go to the Identity Access page and click the Identity synchronization tab.
Click Create IdP. This topic uses a Custom IdP as an example.
NoteIn a production environment, integrate SASE with your corporate Identity Provider (IdP), such as Active Directory (AD), LDAP, DingTalk, or WeCom.
In the Basic Configurations section, enter an IdP Name and a Description. Set IdP Status to Enabled. Click Next.
In the Logon Settings section, set PC Logon Method and Mobile Device Logon Method. This example uses the default configurations. You can enable Two-factor Authentication if needed.
After you confirm the settings, click Confirm.
Step 2: Create users and user groups
Go to the Identity Access page and click the Employee Center tab. From the drop-down list on the left, select the identity source that you created in the previous step. Click Add User.

In the Add User panel, enter the username, password, and other information. In the Department field, assign the user to a department.

Click the User Group Management tab. Click Create User Group, enter a name such as
dev-group, and select a Group Scope as needed.
After you confirm the information, click OK.
Configure a connector to establish network connectivity
To establish network connectivity with a SASE connector, deploy the connector in your on-premises data center or on a server or virtual machine from another cloud provider that hosts your business resources. Then, enable the connector instance.
Step 1: Add a SASE connector
Log on to the Secure Access Service Edge console. In the navigation pane on the left, choose .
On the Non-Alibaba Cloud Services tab, add a connector.
On the Connectors tab, click Add Connector.
In the Add Connector dialog box, configure the parameters as needed. Then, click OK.

Parameter
Description
Region
The region of the connector. To ensure access quality, select the region closest to your server.
Instance Name
The name of the connector.
Instance Switch
SASE end users can access the applications associated with the connector only when the instance switch is set to On.
You can also enable the instance in the connector list or on the connector Details panel.
ImportantIf you disable the connector instance, end users cannot access internal network applications using the SASE app. Proceed with caution.
After the connector is added, it appears in the connector list.
Enable GA.
Find the connector instance that you created. In the Actions column, click Details.
On the instance details page of the connector, find the Global Acceleration section and enable the feature.

In the Enable GA dialog box, enter the following information:
ImportantWhen you enable GA for the first time, you are prompted to authorize the automatic creation of the service-linked roles AliyunServiceRoleForGaCdt and AliyunServiceRoleForGaVpcEndpoint. GA uses these roles to access your resources in SASE.
Parameter
Description
GA Instance Name
Required. Enter a name for the GA instance.
ImportantGA fees include instance fees, capacity unit (CU) fees for performance capacity, and data transfer fees.
Resource Group
Select a resource group.
Terms of service
By clicking Submit, you agree to the relevant service agreements.
After you confirm the information, click Next.
Configure the Acceleration Region and Allocate Bandwidth.
Parameter
Description
Acceleration Region
Configure the acceleration region. Select a region that is close to your users.
NoteThe Dubai region is not supported as an acceleration region.
Allocate Bandwidth
The bandwidth can be set to a value from 2 to 10000. The following bandwidth allocation methods are supported:
Allocate Bandwidth by Region: Customize the peak bandwidth for each acceleration region.
Batch Set: Set a uniform peak bandwidth for all regions.
After the configuration is complete, click OK. The acceleration instance takes some time to create.
After the acceleration instance is created, you can view its details on the details page.

Step 2: Deploy the connector on the business resource server
In the Actions column of the added connector, click Deploy. In the Deploy panel, obtain the deployment command.
Log on to the server or virtual machine where you want to deploy the connector as the root user and run the deployment command. The Deploy panel also provides commands to upgrade or uninstall the connector and to export logs.

After the deployment is complete, you can view information such as the instance ID in the instance information section of the details page. The instance status changes to Connected.

Step 3 (Optional): Configure a managed object in the GA console
If you require higher network transmission quality, you can follow these steps to change the Transmission Network Type.
Go to the Instances page in the GA console and view the managed object and its status.

If your account supports Cross-border Express Connect, the automatically created managed GA instance defaults to the Cross-border Express Connect mode. Otherwise, it defaults to the BGP (Multi-ISP) Pro mode.

Step 4: Add an endpoint in the application
Go to the Application Management page and click Add Application.
In the Basic Configuration section, configure the following parameters:
Application Name: Enter a name for the application.
Description: Enter a description for the application.
Tags: Select tags for the application.
Status: Set the application status to Enabled or Disabled.
Access Mode:
APP Access: Users must install the SASE app to access office applications. This mode supports access to Layer 4 and Layer 7 applications, is suitable for employee office and O&M scenarios, and supports various endpoint security detection and control policies.
Browser-based Access: Users can access corporate web apps using a browser without installing the SASE app. This mode does not support endpoint security detection and control policies.
After you confirm the settings, click Next. On the Application Address page, enter the following information:
Application Address: Enter the domain name or IP address of the application server.
Port: Enter the port range for the application.
Description: Enter a description for the application.
Protocol: Select TCP or UDP.
Web Application Access Reinforcement (Advanced Settings): Optional. Configure access hardening as needed.
After you confirm the application address information, click OK.
The configuration is complete, as shown in the following figure:
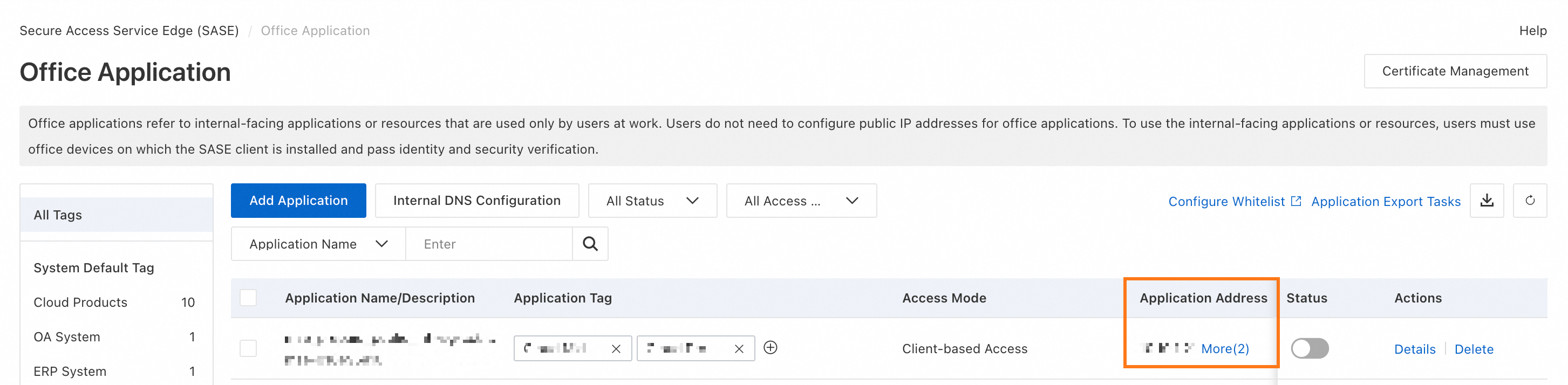
Use the configured access mode, such as APP Access, to access the corresponding accelerated address and verify the connection.
Step 5: Configure a connector forwarding rule
On the Connectors tab, click Forwarding Rules.
On the Forwarding Rules page, click Create Policy.
In the Create Policy panel, configure the parameters as needed. Then, click OK.
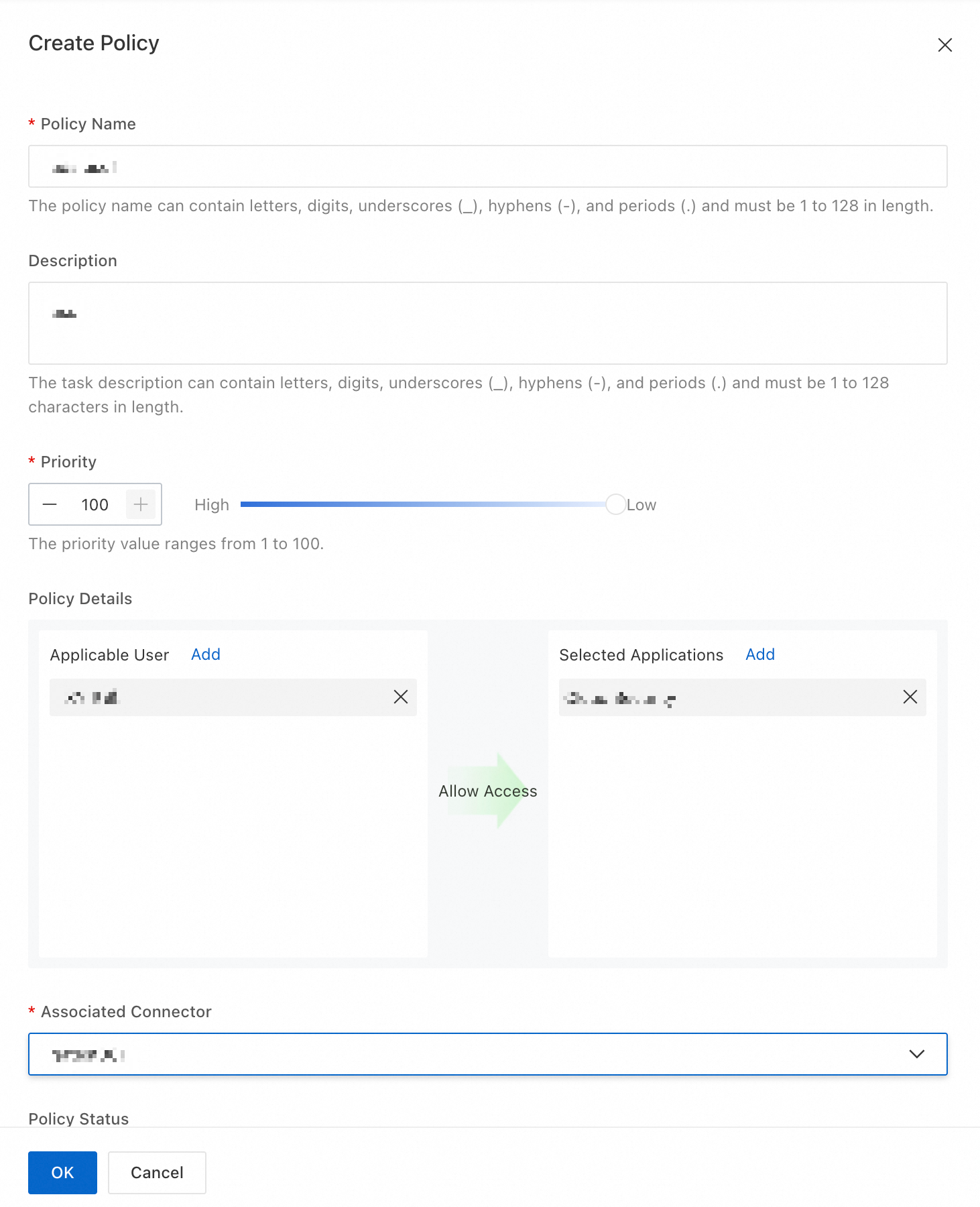
Parameter
Description
Policy Name
The name of the connector forwarding rule.
Description
The description of the policy.
Priority
The policy priority. The value can be from 1 to 100. A smaller value indicates a higher priority.
Policy Details
Add the users to which the policy applies and the associated applications.
Associated Connector
Select the connector to associate with the policy.
Policy Status
The policy takes effect only when its status is Enabled.
Step 6: Configure a zero trust policy
On the Zero Trust Policy page, click Create Policy.
In the Create Policy panel, configure the parameters as needed. Then, click OK.
Parameter
Description
Policy Name
The name of the zero trust policy.
Description
The description of the policy.
Priority
The policy priority. The priority can be a value from 1 to 45. The value cannot start with 0.
Action
You can set this to Allow (default) or Prohibit.
Policy Details
Add the users to which the policy applies and the associated applications.
Trusted Process
Disabled by default.
NoteIf you enable this feature, the zero trust gateway checks whether the process that initiates the access is a trusted process. Access from untrusted processes is blocked.
Security Baselines
Select a security baseline. This parameter is optional.
Trigger Templates
Select a trigger template. This parameter is optional.
Policy Status
Enabled by default. The policy takes effect only when its status is Enabled.
Add a private access whitelist
If you do not want to audit traffic for specific IP addresses or domain names, you can add them to a private access whitelist.
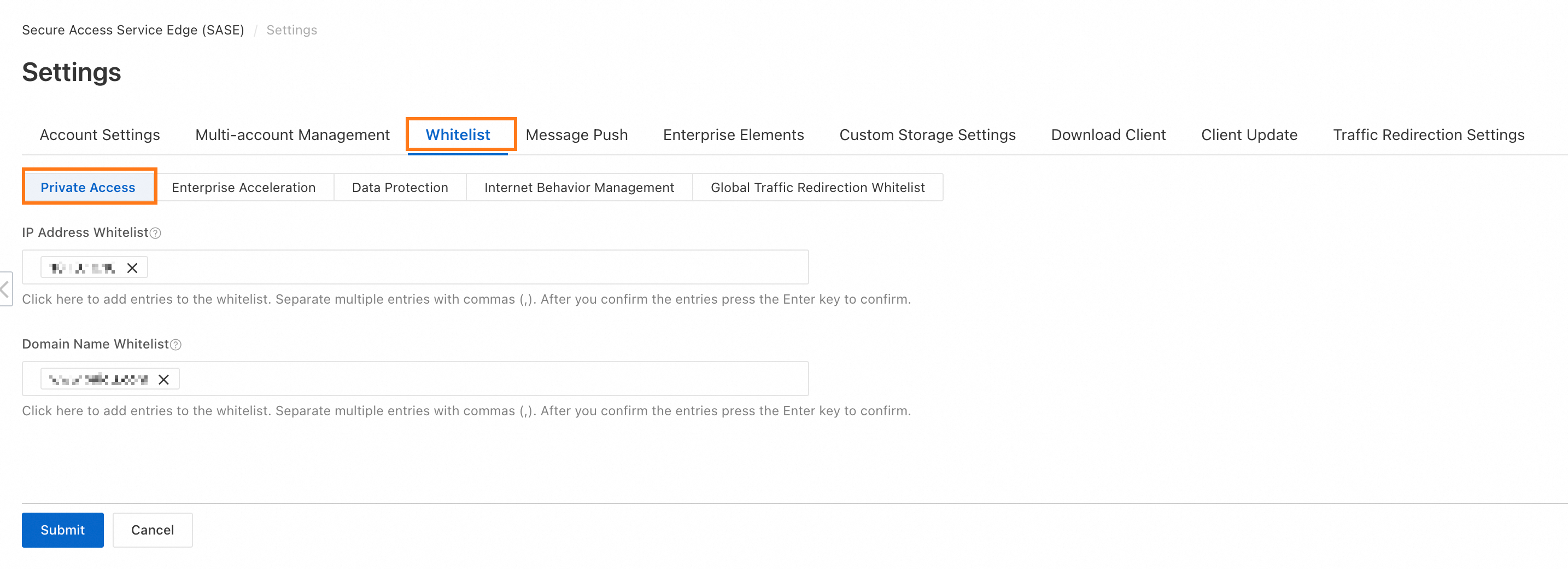
Perform the following steps:
Go to the Whitelist page and click the Private Access tab.
In the IP Address Whitelist section, add the IP addresses that you want to whitelist. You can add multiple IP addresses.
In the Domain Name Whitelist section, add the domain names that you want to whitelist. You can add multiple domain names.
After you add the entries, click Submit.
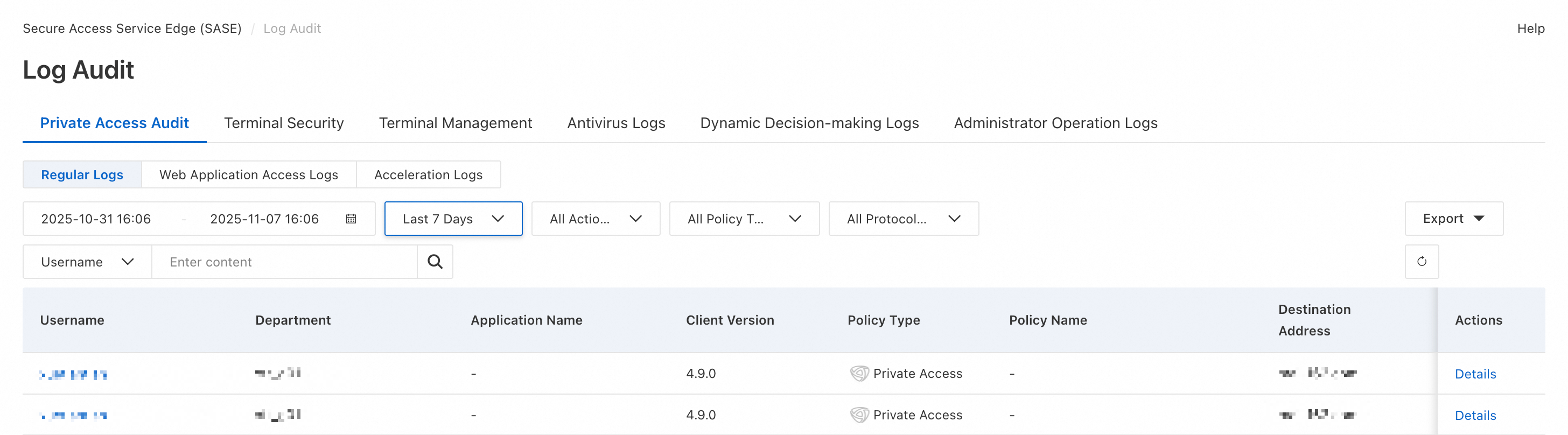
Private access audit
Go to the General Logs page under Private Access Audit. On this page, you can search for and view logs after a client accesses an application.
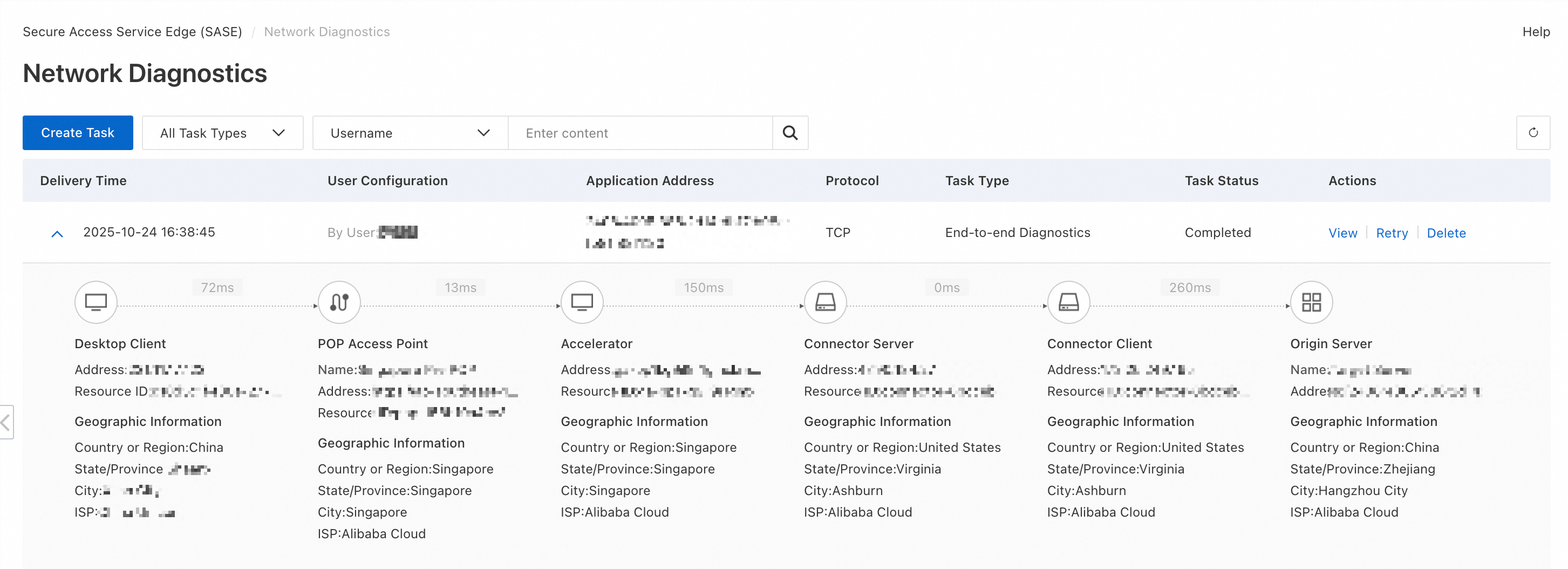
Network diagnostics
Create a diagnostic task
Go to the Network Diagnostics page and click Create Task.
In the panel that appears, configure the following parameters:
Task Type: Select End-to-end Diagnostics or Application Diagnostics. For an office acceleration diagnostic task, select Full-link Diagnostics.
Task Object: Specify the objects for this diagnostic task. You can add multiple objects.
Username: Select a user.
Application Protocol: You can select TCP or UDP.
Application Address: Enter the domain name or IP address and the port number of the application.
Access Point: The default value is Automatic Selection. You can also manually specify an access point.
After you confirm the information, click OK.
View diagnostic results
Go to the Network Diagnostics page and find the diagnostic task that you created in the task list.
Click View in the Actions column to view the detailed diagnostic results.