Secure Access Service Edge (SASE) connects to your cloud-native application resources, allowing you to view and manage their public endpoints. To improve security, you can disable public network access if your business permits. This action restricts application access to the virtual private cloud (VPC) internal network. This topic describes how to access cloud-native applications over a private network and how to disable public network access.
Prerequisites
You have purchased Secure Access Service Edge.
Configure private network access for cloud-native applications
Private network access uses Software-Defined Perimeter (SDP) technology and provides zero trust network access as a Software as a Service (SaaS) solution. The SASE solution allows your employees to securely access cloud resources without exposing public addresses or changing your network architecture. SASE also provides precise control over access permissions.
Step 1: Configure an identity source
Identity sources are used to provide identity authentication for your employees. SASE supports both third-party and self-managed identity authentication systems, such as LDAP, DingTalk, WeCom, Lark, IDaaS, and custom identity sources. If your business uses multiple identity sources, you can configure all of them. This lets you use the SASE service with your various identity sources.
This topic uses a custom identity source as an example to demonstrate the feature.
Log on to the Secure Access Service Edge console.
In the navigation pane on the left, choose .
On the Identity synchronization tab, find Custom IdP and click Edit in the Actions column. Follow the configuration wizard to configure the custom identity source. For more information, see Configure SASE identity sources.
Step 2: Configure a user group
When you configure an access policy, you must specify the user group to which it applies.
In the navigation pane on the left, choose .
On the User Group Management tab, click Create User Group.
In the Create User Group panel, configure the parameters for the user group, such as Organizational Structure, Account Name, Email Address, and Mobile Phone Number. Then, click OK. For more information, see User group management.
Step 3: Enable network connection
In the navigation pane on the left, choose .
On the Network Settings page, on the tab, view the network resources that are synced by SASE.
Find the target CEN instance or a VPC-connected instance associated with the CEN instance. Turn on the Network Connection switch.
In the Network Connection dialog box, select Enable Network Connection for All Cloud Applications or Custom Connection to Cloud Applications.
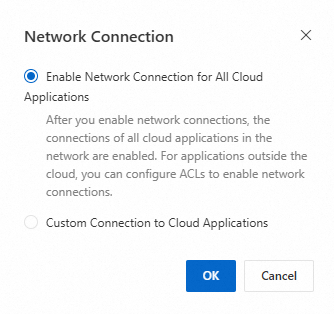
Enable Network Connection for All Cloud Applications: After you select this option, all cloud applications are automatically connected. Non-cloud applications can be connected by configuring ACL rules. Cloud applications that are created in the VPC later are also connected by default.
NoteCurrently, only some cloud-native applications of cloud databases are supported. You can view the supported cloud application types on the tab by checking the Application Type.
Custom Connection to Cloud Applications:
Select Custom Connection to Cloud Applications and click OK.
In the Custom Connection to Cloud Applications panel, select the cloud database instances that you want to connect and click OK.
Step 4: Create a private application
Before you use SASE for private access, you must add the IP address or domain name of your business application to SASE. Employees can access only the business applications that you have added to the SASE app.
Log on to the Secure Access Service Edge console.
In the navigation pane on the left, choose .
Click Add Application. In the Add Application panel, on the Manual Configuration tab, configure the parameters as described in the following table.
Configuration Item
Description
Example
Application Name
The name of the application.
The name must be 2 to 100 characters in length and can contain letters, digits, hyphens (-), underscores (_), and periods (.).
Cloud-native Application
Status
The status of the application. Valid values are Enabled and Disabled.
Enable
Access Mode
Select an access mode.
Client-based Access: Users must install the SASE app to access business applications. This mode supports access to Layer 4 and Layer 7 applications for both regular work and O&M tasks. It also supports a wide range of endpoint security detection and control policies.
Browser-based Access: Users can access your web applications through a browser without installing the SASE app. This mode does not support endpoint security detection and control policies.
Client-based Access
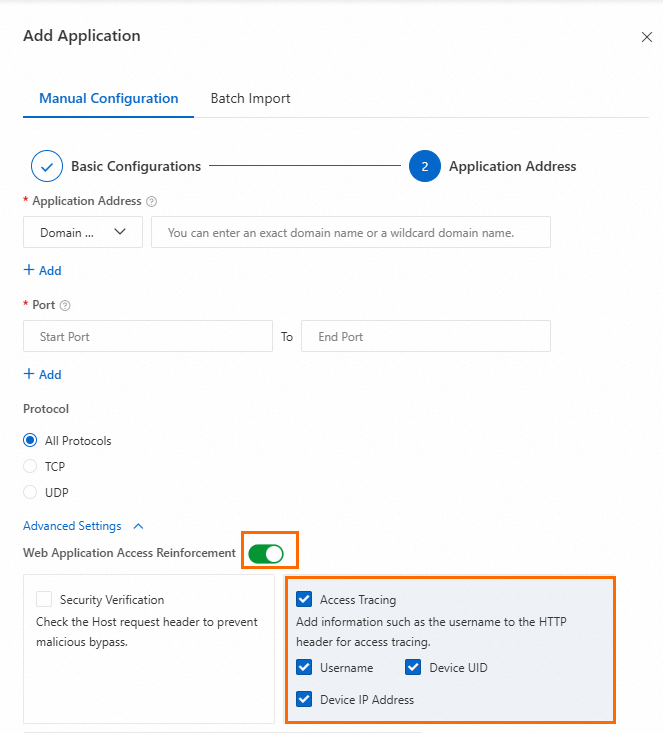
Click Next. Configure the Application Address, Port, and Protocol for the application, and then click OK.
To trace application access, enable the Web Application Access Reinforcement feature. Select Access Tracing, choose the field name to add to the HTTP header, and then fetch it from your business service.
Step 5: Create a zero trust policy
In the navigation pane on the left, choose .
On the Zero Trust Policies tab, click Create Policy.
In the Create Policy panel, configure the policy to allow specified users to access the cloud-native application. Then, click OK.

Step 6: Verify the configuration
Open the SASE app that you installed.
Enter the enterprise verification ID and click OK.
You can log on to the Secure Access Service Edge console. In the navigation pane on the left, on the Settings page, obtain the Enterprise Authentication Identifier.
Log on with the initial account name and password that you received in an email or text message.
Click Connect To Intranet.
Access the private application. If you can access the application, the configuration is successful.
Disable public network access for the cloud-native application
In the navigation pane on the left, choose .
On the tab, view the application types that support disabling public network access and the list of instances for which network connection is enabled.
For an instance that is exposed to the Internet, click Not Disabled in the Actions column.
In the Disable dialog box, make a selection in the Select the public endpoint for which you want to disable access. section, and then click OK.
ImportantAfter you disable this feature, all public network access is denied. This action converges access points and improves security. This operation is irreversible. You can still access the application through SASE. Ensure that you have configured and enabled zero trust policies for all cloud applications.
Attempt to access the cloud application using its public address. If the attempt fails, the configuration is successful.