The end-to-end canary release feature of SAE lets you implement comprehensive traffic control without changing your business code. This topic describes how to configure an end-to-end canary release based on a cloud-native API gateway to implement an end-to-end canary deployment.
Terms
Cloud-native API gateway: A next-generation gateway product that is compatible with the Kubernetes (K8s) Ingress standard. It combines the features of traditional API gateways, traffic gateways, microservice gateways, and security gateways. It supports multiple service discovery methods, such as Container Service for Kubernetes (ACK) and Nacos, and various authentication methods to quickly build a security layer. For more information, see What is a cloud-native API gateway?.
Lane: A set of isolated environments for applications of the same version. Only request traffic that meets the traffic shaping and routing rules is routed to the tagged applications in the corresponding lane. An application can belong to multiple lanes, and a lane can contain multiple applications. The relationship between applications and lanes is many-to-many.
Lane group: A collection of lanes. Lane groups are mainly used to distinguish between different teams or scenarios.
Baseline environment: Untagged applications belong to the baseline environment. This environment serves as a fallback for other environments.
Scenarios
This topic uses a simulated call chain to demonstrate how to implement an end-to-end canary release based on a cloud-native API gateway without modifying business code. You only need to set traffic rules for the ingress application. The traffic tag is then passed through the call chain to subsequent applications. During the invocation process, traffic that meets the rules is routed to the corresponding canary application. If a canary application does not exist, the traffic is automatically routed to the baseline application.
The test applications are as follows:
Test application: end-to-end-canary-release-demo.zip. This file contains three backend applications, A, B, and C. These backend applications can be used for both baseline and canary deployments.
Backend application | Baseline application | Canary application | Tag on the canary application |
A | sae-a | sae-a-a1 | alicloud.service.tag:g1 |
sae-a-a2 | alicloud.service.tag:g2 | ||
B | sae-b | sae-b-b2 | alicloud.service.tag:g2 |
C | sae-c | sae-c-c1 | alicloud.service.tag:g1 |
sae-c-c2 | alicloud.service.tag:g2 |
The following figure shows how traffic is distributed.

Normal traffic call chain:
API service gateway -> Application sae-a -> Application sae-b -> Application sae-c.
Tagged traffic call chain:
t=g1 traffic: API service gateway -> Application sae-a-a1 -> Application sae-b -> Application sae-c-c1.
t=g2 traffic: API service gateway -> Application sae-a-a2 -> Application sae-b-b2 -> Application sae-c-c2.
Prerequisites
You have activated the Professional or Enterprise Edition of Microservice Engine (MSE) microservice governance. For more information, see Activate MSE microservice governance.
You have created a cloud-native API gateway instance. For more information, see Create a gateway instance.
You have created an MSE Nacos instance and a namespace. For more information, see Create an instance and Create a namespace.
The cloud-native API gateway instance and the baseline application can use the same VPC or different VPCs. If they are not in the same VPC, you must configure the network to enable communication between them. For example, you can use Alibaba Cloud's Cloud Enterprise Network (CEN) or other network products to enable cross-VPC communication.
Limits
End-to-end canary release is applicable only to microservice applications that are created on or after November 8, 2023.
The end-to-end canary release feature is supported only in the new version of the console.
The end-to-end canary release feature integrates the tag-based routing feature of MSE microservice governance. This feature is different from the tag-based routing feature of MSE cloud-native gateways. Therefore, we recommend that you do not configure both canary release and tag-based routing rules for applications that are part of an end-to-end canary release.
1. Deploy baseline applications and enable microservice governance for them
1.1 Deploy the baseline applications
Create three baseline applications: sae-a, sae-b, and sae-c. This topic describes only the key steps. For the complete procedure, see Deploy an application.
In the SAE Application List, select a region and namespace from the top menu bar, and then click Create Application.
On the Basic Information wizard page, configure the parameters in the Basic Information Settings and Capacity Settings sections, and then click Next: Advanced Settings.
In this example, the three baseline applications sae-a, sae-b, and sae-c are deployed by uploading code packages.
Find and expand the Service Registration and Discovery section. Set Nacos-based Registry Service and Discovery to MSE Nacos Professional Edition, and select the target MSE Nacos Instance and Namespace. For information about other advanced configurations, see Advanced configurations.
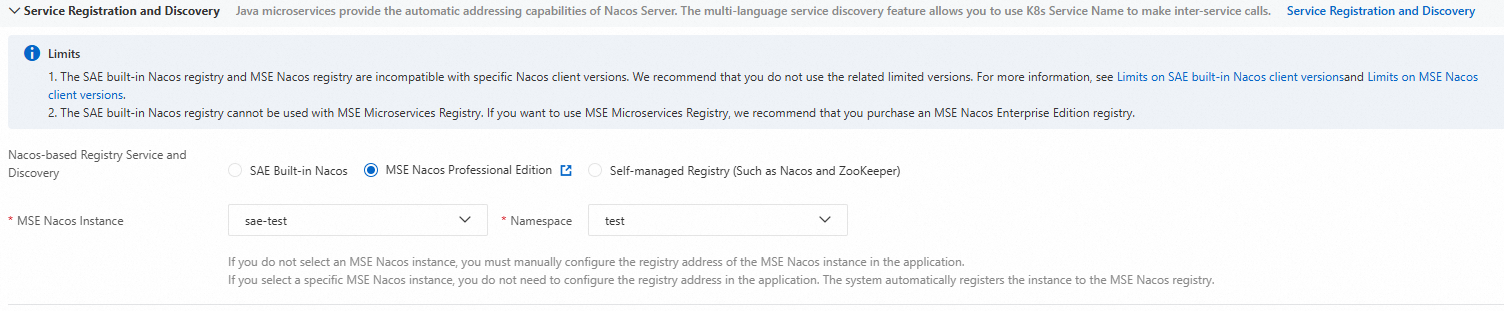 Important
ImportantAll three baseline applications use the same MSE Nacos instance and namespace.
Click Create Application.
1.2 Enable microservice governance for the baseline applications
End-to-end canary release is a feature of the Professional Edition of MSE microservice governance. All applications in the call chain must have microservice governance enabled.
In the SAE Application List, select a region and namespace from the top menu bar, and click the ID of the target application to open its details page.Click , and then turn on the switch for Microservices Governance.
The version of microservice governance enabled for the application must be the same as the MSE version.
If your application is not connected to the commercial edition of MSE, see Upgrade the microservice governance feature with a single click to upgrade the feature.
When you enable this feature, all instances of the application are restarted. Perform this operation during off-peak hours.
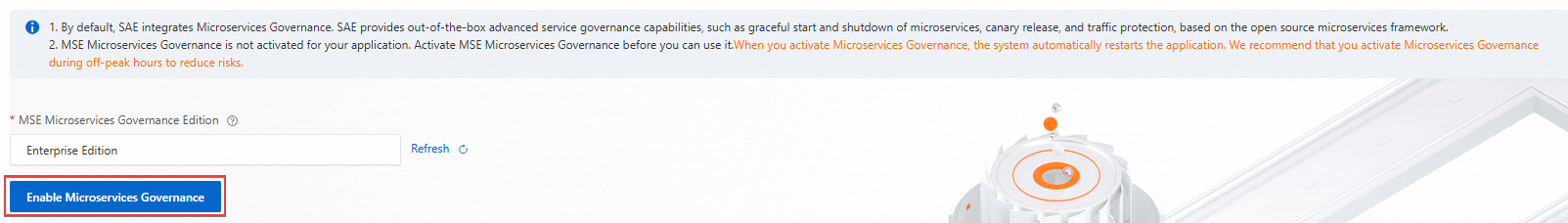
The process takes 1 to 2 minutes to complete.
2. Deploy canary applications
Deploy canary applications based on the baseline applications:
The baseline application sae-a has two canary applications: sae-a-a1 and sae-a-a2.
The baseline application sae-b has one canary application: sae-b-b2.
The baseline application sae-c has two canary applications: sae-c-c1 and sae-c-c2.
Perform the following steps:
On the application list page, click the
 icon in the row of the baseline application, and then click Create Canary Application.Note
icon in the row of the baseline application, and then click Create Canary Application.NoteYou cannot create a canary application if microservice governance is not enabled for the baseline application. For information about how to enable the feature, see Enable microservice governance for the baseline applications.
On the Basic Information wizard page, configure the following information, and then click Next: Advanced Settings.
In the Basic Information Settings section, set the canary Application Name and select a method to deploy the canary application. For more information, see Deploy an application.
NoteThe Namespace of the canary application is automatically inherited from the baseline application. You do not need to change it.
The Application Deployment Method is also automatically inherited from the baseline application. In this example, you do not need to upload the code package again. However, in a production environment, adjust the configuration as needed.
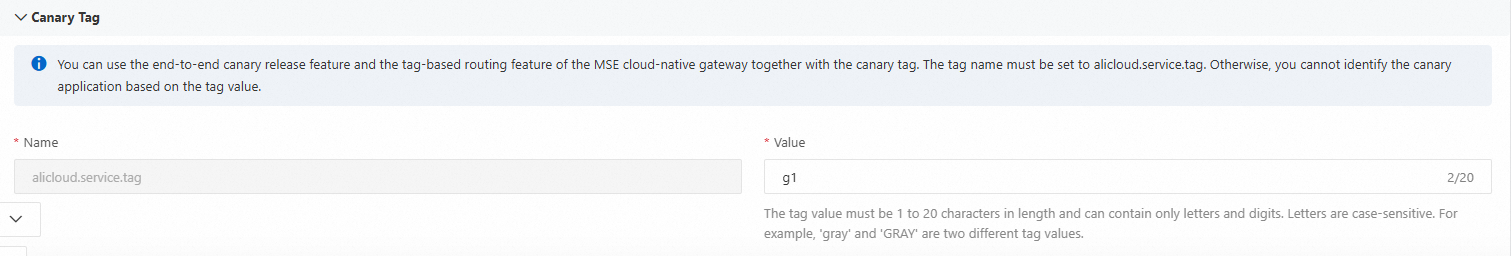
In the Canary Tag section, set the tag Value. For the tag configuration in this example, see Scenarios.
In the Capacity Settings section, configure the single-instance specifications and the number of instances.
On the Advanced Settings wizard page, configure related features as needed. For more information, see Advanced configurations.
NoteThe service discovery feature of the canary application is automatically inherited from the baseline application. You do not need to change it.
Click Create Application.
3. Create a cloud-native API Gateway route
In SAE Gateway Routing, select a region and namespace from the top menu bar, and then click Create Gateway Route.
On the Create Route page, create a cloud-native API gateway route. This topic describes only the key steps. For detailed configuration instructions, see Configure a cloud-native API Gateway routing rule for an SAE application.
NoteThe configurations in this topic are for demonstration purposes only. In a production environment, adjust the configurations as needed.
Set Gateway Type to Cloud-native API Gateway.
For Gateway Instance, select the gateway instance that you created.
Set Path to Prefix and enter
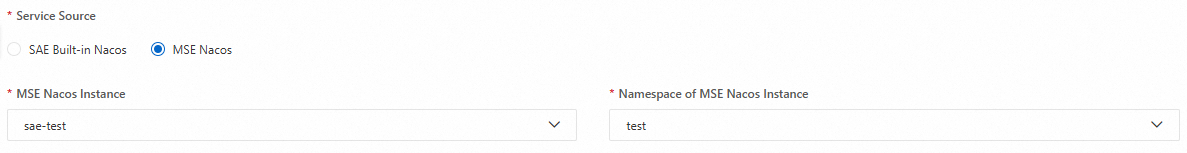
/.Set Service Source to MSE Nacos.
For MSE Nacos Instance and MSE Nacos Namespace, select the same MSE Nacos instance and namespace as the baseline application.
Set Scenario to Single Service.
For Backend Services, set Application Name to sae-a, Service Name to sc-A, Terms of Service to HTTP, and Service Port to
20001.
Click Save.
4. Create a lane group and lanes
4.1 Create a lane group
In SAE Microservice Governance, select a region and namespace from the top menu bar. Click End-to-end Canary Release, and then click Create Lane Group and Lane.
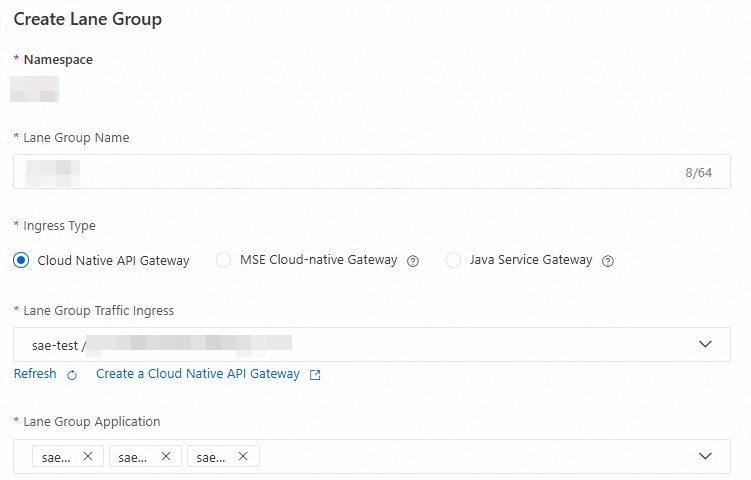
In the Create Lane Group panel, configure the following parameters, and then click OK.
Enter a custom Lane Group Name.
Set Ingress Type to Cloud-native API Gateway.
For Lane Group Traffic Ingress, select the cloud-native API gateway instance that you created.
For Lane Group Application, select all baseline applications.
4.2 Create lanes
Within a lane group, you can create lanes by content or by traffic ratio. However, after the first lane is created, you cannot change the canary release mode for subsequent lanes.
The examples in the following tables are for demonstration purposes only. In a production environment, adjust the configurations as needed.
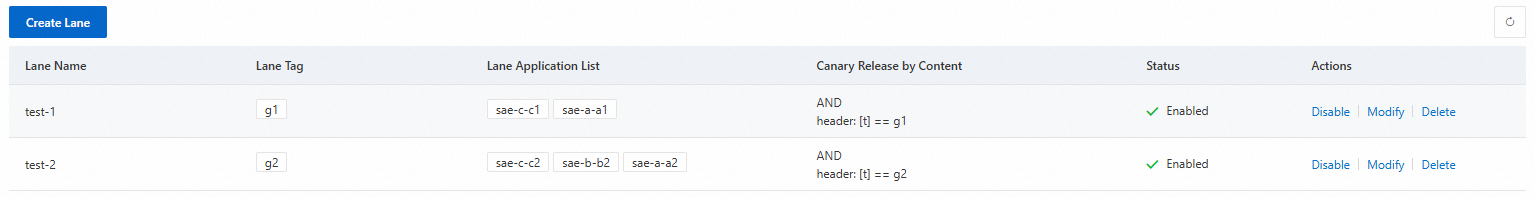
Canary Release by Content
Create two lanes as follows.
On the End-to-end Canary Release page, click Create First Split Lane.
ImportantAfter the first lane is created, click Create Lane to create the second lane.
In the Create Lane panel, configure the following parameters, and then click OK.
Configuration item
Example
Description
Lane Name
First lane name: test-1
Second lane name: test-2
Enter a custom name for the lane. Each lane name must be unique.
Lane Tag
First lane tag: g1
Second lane tag: g2
From the drop-down list, select the tag value for the request. This is the tag that you configured when you created the canary application.
Lane Status
The status of both lanes is Enabled.
The lane is enabled by default.
Canary Release Mode
For both lanes, select Canary Release by Content.
Select Canary Release by Content. For a description of this mode, refer to the description in the console.
Canary Condition
Canary condition for the first lane:
All of the following conditions are met
Parameter type:
HeaderParameter:
tCondition:
==Value:
g1
Canary condition for the second lane:
All of the following conditions are met
Parameter type:
HeaderParameter:
tCondition:
==Value:
g2
When a request meets the configured canary condition, the request is marked with the specified lane tag.
The following two filter conditions are supported:
All of the following conditions are met: The request is tagged only if all the specified conditions are met.
Any of the following conditions is met: The request is tagged if any of the specified conditions is met.
You can filter requests by the following parameters:
Parameter Type: Header, Cookie, and Parameter are supported.
Parameter: You can enter a custom parameter.
Condition:
==,!=,in, percentage, regular expression matching, and prefix matching are supported.Value: You can enter a custom value.
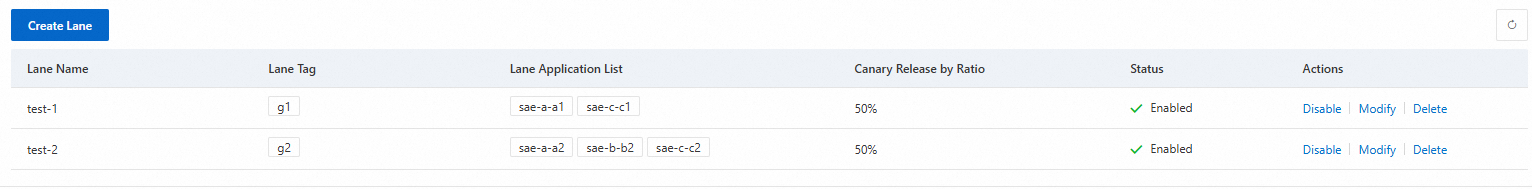
Canary Release by Ratio
Create two lanes as follows.
On the End-to-end Canary Release page, click Create First Split Lane.
ImportantAfter the first lane is created, click Create Lane to create the second lane.
In the Create Lane panel, configure the following parameters, and then click OK.
Configuration item
Example
Description
Lane Name
First lane name: test-1
Second lane name: test-2
Enter a custom name for the lane. Each lane name must be unique.
Lane Tag
First lane tag: g1
Second lane tag: g2
From the drop-down list, select the tag value for the request. This is the tag that you configured when you created the canary application.
Lane Status
The status of both lanes is Enabled.
The lane is enabled by default.
Canary Release Mode
For both lanes, select Canary Release by Ratio.
Select Canary Release by Ratio. For a description of this mode, refer to the description in the console.
Traffic Ratio
First lane traffic percentage: 50%
Second lane traffic percentage: 50%
Set the traffic percentage for the selected route or path. By default, all routes or paths within the lane use the same traffic percentage.
5. Verify the results
5.1 Test access
Log on to the cloud-native API gateway console. In the navigation pane on the left, click Instances. In the top menu bar, select the target region, and then click the ID of the API gateway instance that you created.
On the Overview page of the API gateway instance, click the Endpoints tab. On the Access Domain Name and IP Address tab, view the endpoint and instance IP provided by the console.
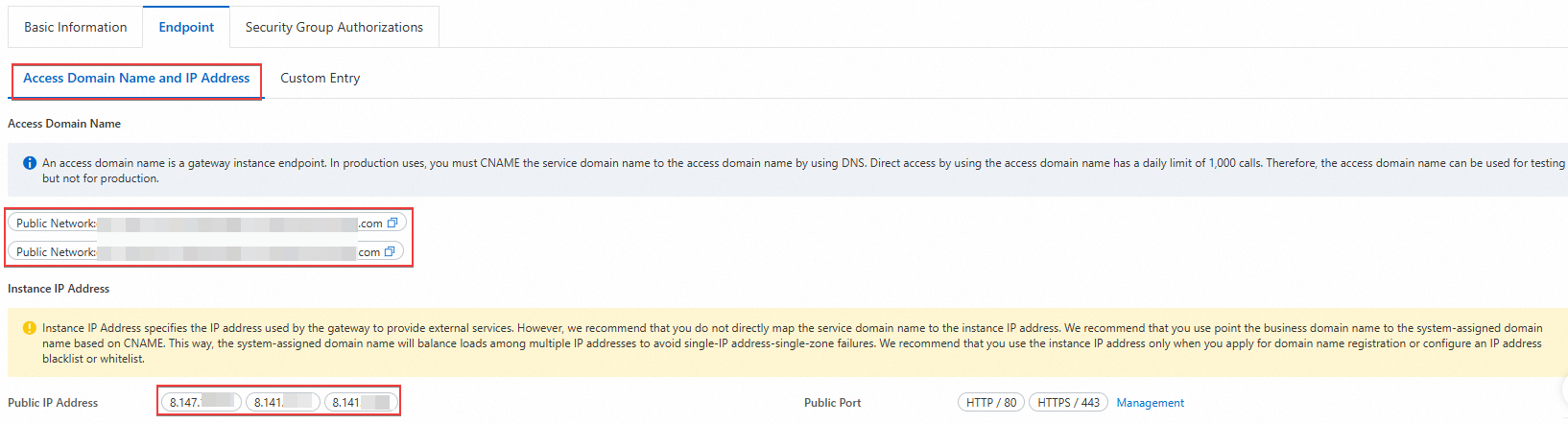 Important
ImportantThe endpoint is the access entry point of the gateway instance. In a production environment, you must add a CNAME record that maps your business domain name to this endpoint. Direct access through the endpoint is limited to 1,000 requests per day. This method is suitable for testing only and not for production environments.
The instance IP is the public IP address that the gateway uses to provide services. We recommend that you do not directly map your business domain name to the instance IP. Instead, add a CNAME record that maps your business domain name to the endpoint. The endpoint load balances traffic across multiple IP addresses to prevent failures caused by a single point of failure in an IP address or zone. Use the instance IP only when you are applying for domain name registration or configuring IP address blacklists and whitelists.
Copy the endpoint or public IP address and test the access in a browser.
In this example, the URL format for access by domain name is:
http://<Endpoint>/<Access path>. For example:http://env-cu2c******/a.In this example, the URL format for access by public IP address is:
http://<Public IP address:80>/<Access path>. For example:http://8.147.XX.XX:80/a.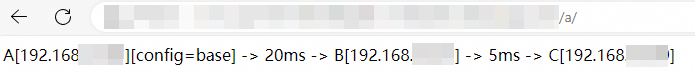
5.2 Verify canary traffic
You can use the public IP address exposed by the cloud-native API gateway to verify access. However, in a production environment, we recommend that you do not directly map your business domain name to the public IP address. Instead, add a CNAME record that maps your business domain name to the second-level domain of the environment.
Verify content-based canary traffic
Use the curl command to test the baseline traffic:
# Test command curl 8.130.XX.XX/a # Test result A[192.168.XX.XX][config=base] -> B[192.168.XX.XX] -> C[192.168.XX.XX]Use the curl command to test the canary traffic. The following example uses the Header parameter type:
# Test command curl 8.130.XX.XX/a -H "tag: ${tag}" # Test result A${tag}[192.168.XX.XX][config=base] -> B[192.168.XX.XX] -> C${tag}[192.168.XX.XX]NoteWhen the parameter includes
tag: ${tag}, the request hits the canary tag and is passed through the call chain.
Verify percentage-based canary traffic
Use the curl command to verify.
# Test command
curl 8.130.XX.XX/a
# Test result
A[192.168.XX.XX][config=base] -> B[192.168.XX.XX] -> C[192.168.XX.XX]
A${tag}[192.168.XX.XX][config=base] -> B[192.168.XX.XX] -> C${tag}[192.168.XX.XX]5.3 Microservice governance observability
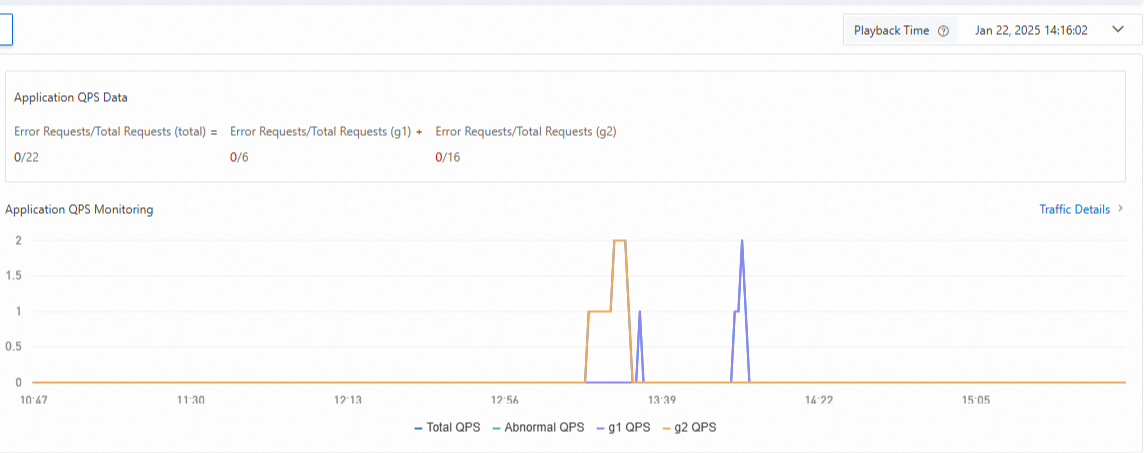
On the End-to-end Canary Release page, in the Lane Groups and Involved Applications section, click the target application. In the Application QPS Monitoring section, you can view the traffic for the baseline and canary versions for the corresponding lane. Select a time range to display the metric data for that period.
You can also click Traffic Details in the Application QPS Monitoring section to view more detailed information.