You can use a resource directory to manage multiple accounts and share a virtual private cloud (VPC) with these accounts.
Background information
As cloud computing becomes popularized, an increasing number of enterprises deploy services in the cloud and purchase more and more cloud resources. An issue arises: How can enterprises manage cloud resources in an efficient manner? Enterprises have high requirements for the division of business, business isolation, and multiple payment methods. The single-account mode can no longer support the sustainable development of enterprises. To resolve this issue, enterprises can use the multi-account mode to meet business development requirements. However, the following issues may arise during the use of the multi-account mode:
Management of multiple accounts
Enterprises may not be able to manage multiple isolated Alibaba Cloud accounts in a centralized manner. Therefore, more refined management is required.
Communication among multiple accounts
Enterprises can use Cloud Enterprise Network (CEN) to connect VPCs that belong to different accounts. This way, cloud resources within different accounts can communicate with each other. However, as the business complexity increases, the following issues may occur:
Complex network O&M due to isolated deployment of network resources
The network of an enterprise can be large and complex because the network resources may be deployed and managed by different accounts. As a result, it is difficult for O&M personnel to manage an enterprise network in a centralized manner.
Increased costs due to frequent network resource configurations
O&M and instance costs increase due to frequent VPC configurations by different accounts.
Increased network complexity due to an increasing number of VPCs
To meet business requirements, more and more VPCs need to be deployed. As a result, issues such as complex network, difficult management, and resource quota limits arise. For example, the number of VPCs attached to a CEN instance may reach the upper limit.
Solution
Alibaba Cloud offers the Resource Directory service to facilitate the management of multiple accounts and offers the Resource Sharing service and VPC sharing feature to facilitate communication among multiple accounts. The following descriptions provide details:
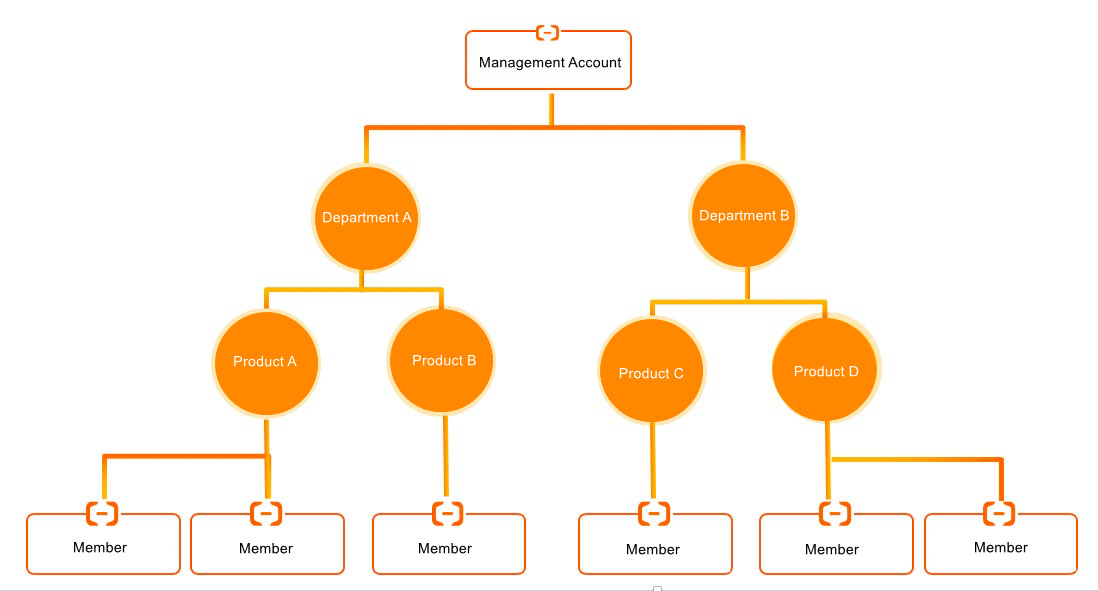
Use Resource Directory to manage multiple accounts
The Resource Directory service provided by Alibaba Cloud allows you to manage the relationships among multiple levels of resources and accounts. You can enable a resource directory and create folders in the resource directory based on the organizational structure or business form of your enterprise. Then, you can consolidate the accounts used by your enterprise into the resource directory to establish multi-level relationships for the accounts and the resources within the accounts. This way, you can manage the accounts and resources in a centralized manner based on the relationships. In addition, your requirements for finance, security, audit, and compliance can be met. For more information, see Resource Directory.
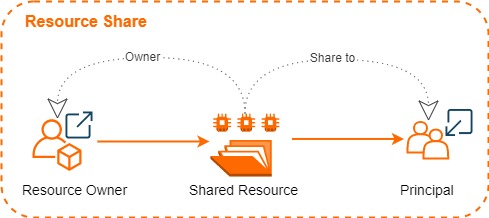
Use Resource Sharing to share resources with members within the same resource directory
The Resource Sharing service provided by Alibaba Cloud allows you to share resources with one or more members within your resource directory. To use this feature, create a resource share and add the resources and members to the resource share. For more information, see What is Resource Sharing?.
Term
Description
resource share
A resource share is an instance of the Resource Sharing service. It is also a resource and has a unique ID and an Alibaba Cloud Resource Name (ARN). A resource share consists of a resource owner, principals, and shared resources.
resource owner
A resource owner initiates resource sharing and owns shared resources.
principal
A principal is invited to use the resources of resource owners and has specific operation permissions on the shared resources.
NoteThe operation permissions of each principal on the shared resources are determined by the Alibaba Cloud service to which the resources belong. For example, the operation permissions of principals on the shared vSwitches in a VPC are determined based on the VPC service. For more information, see Permissions related to VPC sharing.
shared resource
A shared resource is a resource of an Alibaba Cloud service. For more information about the types of resources that can be shared, see Services that work with Resource Sharing.
resource sharing
Resource sharing allows you to share your resources with all members in your resource directory, all members in a specific folder in your resource directory, or a specific member in your resource directory. For more information, see Enable resource sharing within a resource directory.
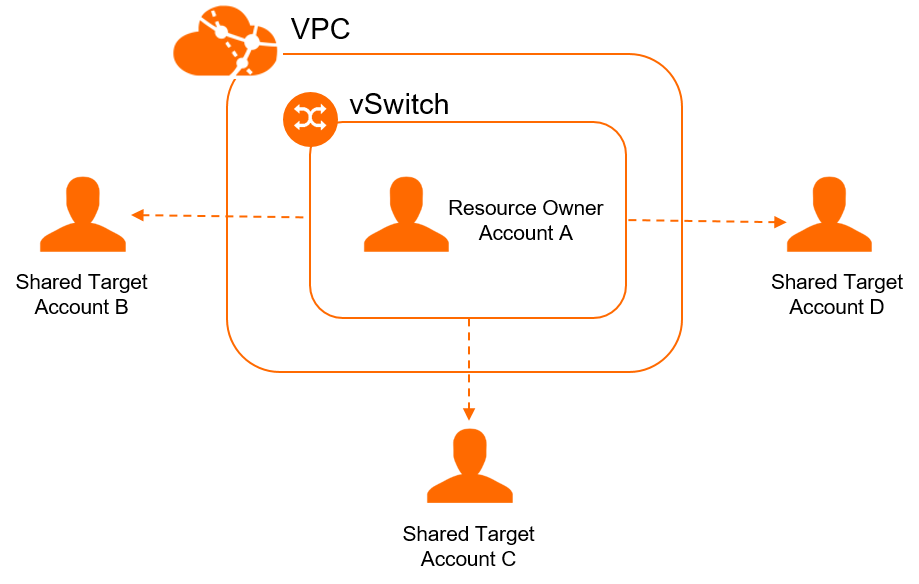
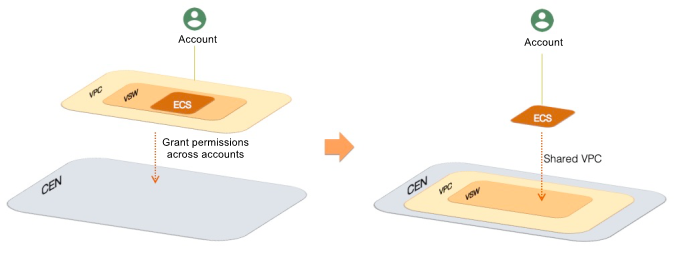
Share a VPC with members within the same resource directory
You can use the Resource Sharing service to share the vSwitches in a VPC that belongs to a member (resource owner) with other members (principals) within the same resource directory. This way, the principals can create resources, such as Elastic Compute Service (ECS) instances, Server Load Balancer (SLB) instances, and ApsaraDB RDS instances, in the shared VPC. The resources created by the resource owner and principals can communicate with each other within the shared VPC. For more information, see VPC sharing.
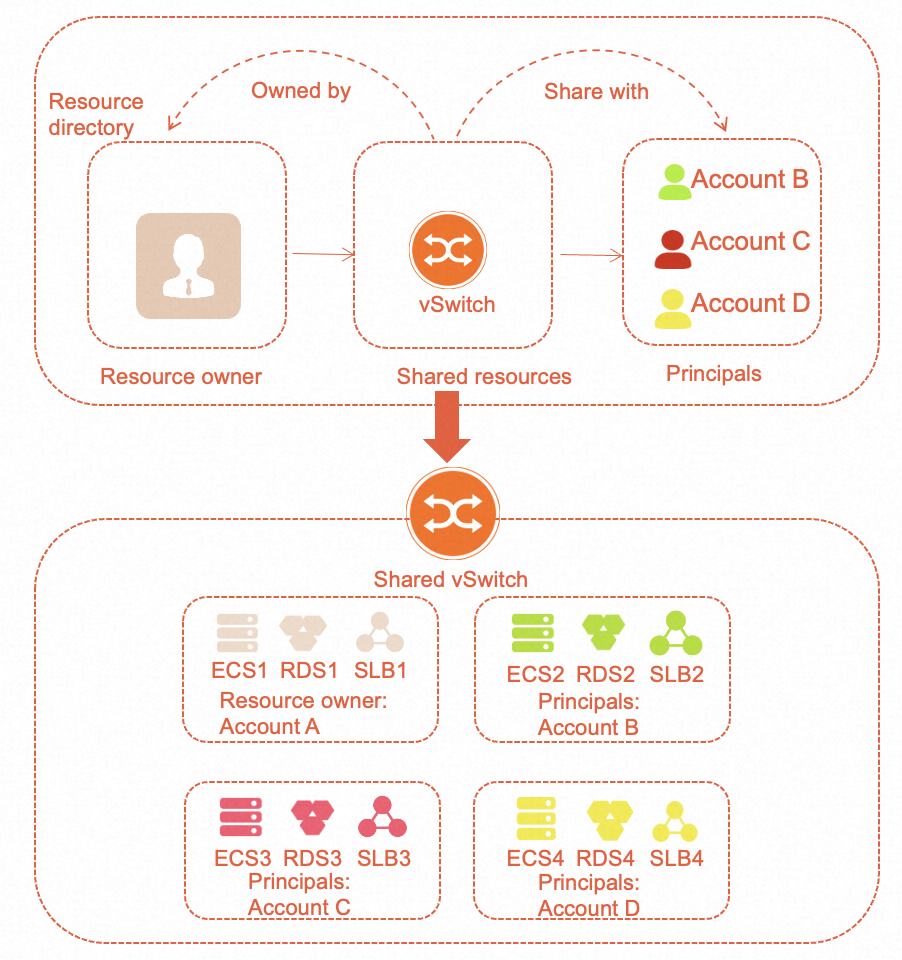
The following figure and descriptions provide details about how a VPC is shared.
vSwitch sharing among multiple accounts
You can share a vSwitch in a VPC with multiple accounts without the need to configure a VPC for each account. This reduces the number of VPCs.
Permissions of the vSwitch owner and principals
Resource
Owners
Participants
Cloud resources (such as ECS and RDS)
Each account can only view and manage cloud resources and security groups it creates. It cannot view and manage those created by other accounts.
Security groups
Elastic network interfaces (ENIs)
Call DescribeNetworkInterfaces to view ENIs created by participants. Managing ENIs created by participants is not supported.
View and manage ENIs the participant creates. The participant cannot view ENIs of other accounts.
VPC, vSwitch, route table, network ACL, and secondary CIDR block
All permissions
View only
Reserved CIDR blocks
All permissions
No permissions
IPv6 gateway
All permissions
Allocate/delete IPv6 private addresses for resources such as ECS, ENIs, and NLB instances.
View IPv6 addresses in its own account.
Enable/disable public bandwidth, and set/delete egress-only rules for IPv6 addresses in its own account. The public bandwidth fee is paid by the participants.
Flow logs
Create flow logs at the VPC and vSwitch levels, which only apply to owner ENIs.
Create flow logs at the ENI level, which only apply to owner ENIs.
Create flow logs at the ENI level, which only apply to participant ENIs.
NAT gateway, VPN gateway, Cloud Enterprise Network, and VPC peering connection
All permissions
No permissions to view or manage, but can connect to external networks through these resources.
Tags
Tags configured by the vSwitch owner are not affected. Owners and participants can configure tags for their own resources. These tags are not visible to and do not affect each other.
Isolation
If you share vSwitches in the same VPC with different accounts, the vSwitches can communicate with each other by default. If you want to isolate the vSwitches in some scenarios, use one of the following methods:
Configure a network access control list (ACL) to isolate the vSwitches.
Configure a security group to isolate the instances that belong to the vSwitches. You can use security groups that belong to other accounts.
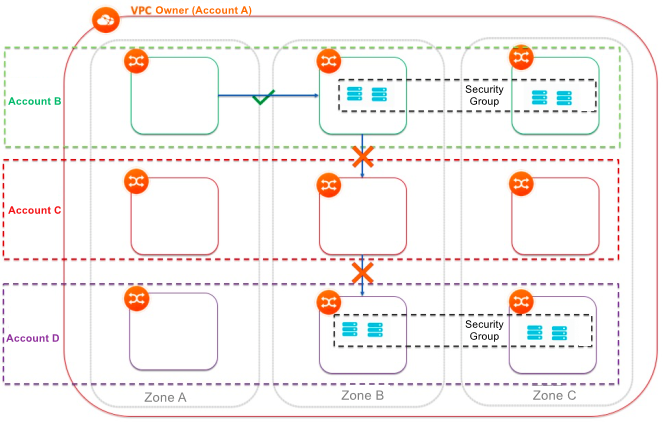 Note
NoteYou can configure ACL rules to isolate instances that belong to different vSwitches. However, if you want to isolate instances that belong to the same vSwitch, you can configure security group rules for the instances. You can use security groups that belong to other accounts. To isolate networks between different vSwitches and different accounts, configure source and destination IP addresses in security groups.
Benefits
The solution has the following benefits:
The O&M department can plan, configure, and manage VPCs in a centralized manner. In addition, the O&M department can share the vSwitches in the VPCs with the business department.
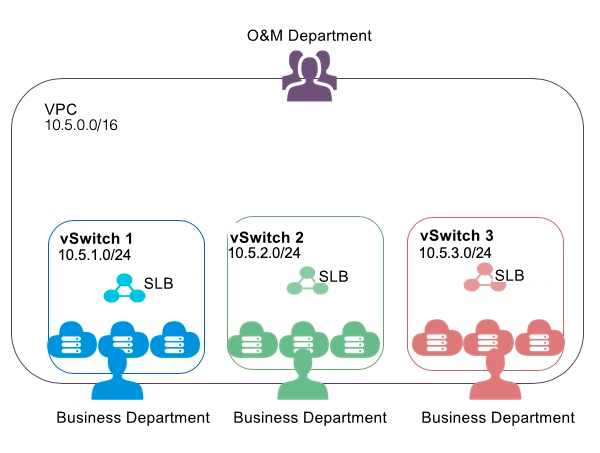
The business department can view and manage only the resources that belong to the shared vSwitches. In addition, the business department can create resources in the shared vSwitches or delete resources from the shared vSwitches, such as cloud instances and databases, based on business requirements.
In this solution, your enterprise uses a unified network architecture and security policy. This allows the business department to focus on business requirements.
You can use the network and security capabilities as a service for the business department, and standardize the O&M system. This improves the IT efficiency throughout your enterprise.