Real-time log tracing lets you stream filtered request logs instantly to diagnose abnormal access behavior in your Tair instance. This feature records only the requests that match your filter rules, keeping the performance impact significantly lower than that of audit logs.
How it works
When you create a tracing rule, the system matches incoming requests against your filter conditions — by command type, client IP, key name, or payload size — and prints only the matching logs in real time. The task stops automatically when either end condition (log count or duration) is reached.
Use cases
Hot key and large key analysis: Identify which clients access specific keys to adjust your cache policies.
Abnormal command tracing: Trace suspicious commands to locate malicious scans or resource abuse.
Real-time log tracing is designed for temporary, real-time diagnosis. For long-term auditing, use the Audit Log feature.
Version requirements
Your instance must be a memory-optimized Tair (Enterprise Edition) instance running minor version 25.10.1.0 or later.
Create a tracing rule
Prerequisites
Before you begin, ensure that you have:
A memory-optimized Tair (Enterprise Edition) instance running minor version 25.10.1.0 or later
Steps
Log on to the console and go to the Instances page. In the top navigation bar, select the region where your instance is deployed. Find the instance and click its ID.
In the left navigation pane, click CloudDBA > Instance Session.
Click the Instance Tracing tab, then click Create Tracing Rule.
NoteUp to five tracing rules can run simultaneously.
In the panel that appears, configure the tracing rule parameters.
Rule Name is the only required parameter. All other parameters use a logical AND (&&) operator — the rule matches only requests that satisfy all specified conditions. Leave unneeded parameters at their default values.
Category Parameter Description Name Rule Name (required) A name for the tracing rule. Match conditions Command Settings - Select Add or exclude command groups or individual commands. Supports custom combinations. Command Settings - Input Enter tracing rules using Redis Access Control List (ACL) syntax. For example, +@write +@hash +@string -hsetnxtraces write commands for Hash and String but excludes HSETNX. More specific rules (for example,+hset) have lower overhead than broader groups (for example,+@hash).Key Match Select All Keys or specify a Key Pattern. Wildcard characters are supported. Channel Match For Pub/Sub commands only. Select All Channels or specify a Channel Pattern. Wildcard characters are supported. Client IP Match Select All IPs or specify an IP Pattern in CIDR format. For example, 192.168.1.0/24covers 192.168.1.0 to 192.168.1.255.Response Size Limit Filter by response payload size, in bytes. Default: 0(no limit).Request Size Limit Filter by request payload size, in bytes. Default: 0(no limit).End conditions End by Log Count Stop the task after a set number of log entries. Monitoring Duration Stop the task after a set duration, in seconds. The task stops when either end condition is met.
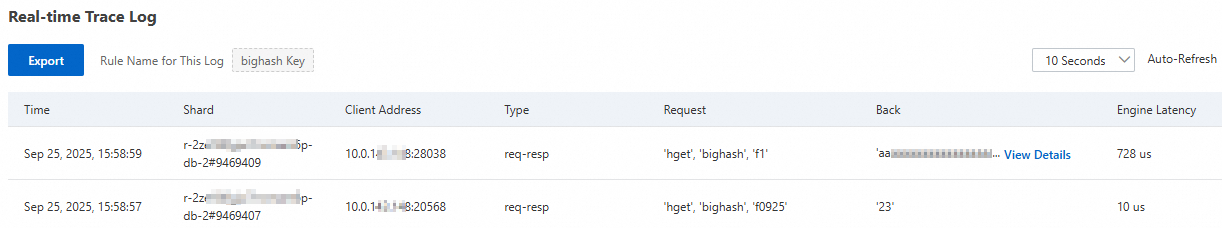
Example: To find which clients are accessing the large key
bighash, configure the rule as follows and leave all other parameters at their defaults:Rule Name:
bighash KeyCommand Settings - Input:
+@hashKey Match: Select Key Pattern and enter
bighash
Click Create And Run.
The tracing task starts immediately. Refresh the Real-time Tracing Log list to view matching request logs.
The task stops automatically when an end condition is met. After the task stops, you can modify, delete, or re-run the rule.
WarningRe-running a rule overwrites the existing logs. Export and save the logs before re-running.
If you delete a rule, the logs associated with that rule are also deleted.
Troubleshooting
Use the client IP address and command type from the tracing logs to investigate your service logic or configure access control settings.