Transparent data encryption (TDE) encrypts data files in real time as they are written to disk and decrypts them when read into memory — without requiring any changes to your application. Use TDE when you need data-at-rest encryption to meet security compliance requirements, protect sensitive database content from direct storage access, or safely share backup files with third parties.
After TDE is enabled, data file sizes do not increase.
How it works
TDE uses a layered key hierarchy to protect your data.
Operating system layer — Windows Data Protection API (DPAPI) is a built-in Windows API that manages encryption keys and algorithms transparently. DPAPI is the root of the TDE key hierarchy and protects the service master key (SMK).
SQL Server instance layer — The service master key (SMK) is generated when a SQL Server instance is created. It serves as the root encryption key for the database engine and is protected by DPAPI. The SMK encrypts the database master key (DMK).
Database layer — TDE operates on both the master database and user databases:
Master database: When TDE is enabled, a DMK and a certificate are created in the master database. The DMK is a symmetric key encrypted by the SMK; the certificate encrypts the database encryption key (DEK) stored in user databases.
User databases: Each user database stores a DEK encrypted by the certificate in the master database. When SQL Server reads or writes data, it uses the certificate's private key to decrypt the DEK in memory, then uses the DEK to encrypt or decrypt data files in real time. This process is transparent to applications and users.
If the TDE certificate is not present in the master database, SQL Server cannot decrypt the DEK. This means you cannot restore backup files from a TDE-enabled database or attach the database to another instance.
Prerequisites
Before you begin, make sure that:
The RDS instance meets all of the following conditions:
The instance belongs to the general-purpose or dedicated instance family. Shared-performance instances are not supported. For more information, see Instance families.
The billing method is subscription or pay-as-you-go. Serverless instances are not supported. For more information, see Serverless ApsaraDB RDS for SQL Server instances.
The instance runs one of the following SQL Server versions: SQL Server 2019 SE, SQL Server 2022 SE, or SQL Server EE.
The instance is not a read-only RDS instance.
Your Alibaba Cloud account has authorized the RDS instance to access Key Management Service (KMS). For more information, see Authorize ApsaraDB RDS to access KMS.
(Required for Bring Your Own Key (BYOK) only) You have the certificate file, private key file, and password ready.
Limitations and usage notes
Limitations
When TDE is enabled on an RDS instance:
You cannot update the minor engine version of the instance.
If the instance uses Premium Local SSDs and runs SQL Server 2008 R2, you cannot upgrade the major engine version from SQL Server 2008 R2 to SQL Server 2012 or SQL Server 2016.
Backup files can be used to restore data to a new RDS instance, but cannot be used to rebuild the RDS instance or restore data to another existing RDS instance.
If you use the Alibaba Cloud service key, backup files generated after TDE is enabled cannot restore data to an on-premises device.
Performance impact
TDE is CPU-intensive and involves I/O operations. Based on official Microsoft documentation:
Overall performance decreases by approximately 3%–5% under typical conditions.
If most accessed data is in memory, the impact is minimal.
If CPU utilization is already high, performance loss can reach approximately 28%.
Enable TDE
Go to the Instances page. In the top navigation bar, select the region where the RDS instance resides, then click the instance ID.
In the left-side navigation pane, click Data Security.
On the TDE tab, turn on the switch next to Disabled.
TDE can only be enabled when all prerequisites are met.
In the dialog box, select a key type and click OK.
Use the key automatically generated by Alibaba Cloud
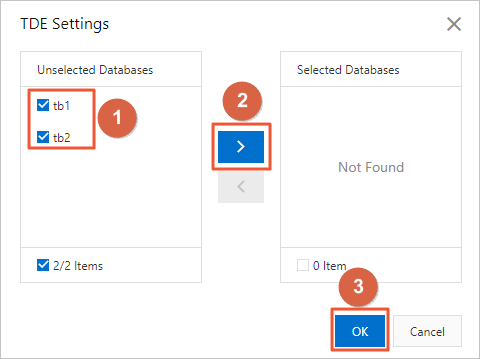
Select databases from the Unselected Databases section, click the ![]() icon to move them to the Selected Databases section, and then click Confirm.
icon to move them to the Selected Databases section, and then click Confirm.
Encrypt with your own SQL Server key (BYOK)
Upload the certificate file and the private key file to your OSS bucket. For more information, see Upload objects.
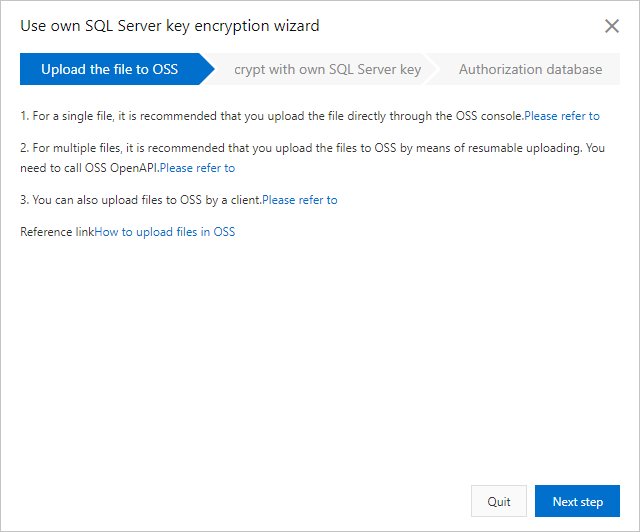
Click Next step and configure the following parameters.
Parameter Description OSS Bucket The OSS bucket where you uploaded the certificate and private key files. Certificate The certificate file you uploaded to the OSS bucket. Private key The private key file you uploaded to the OSS bucket. Password The password of your SQL Server key. 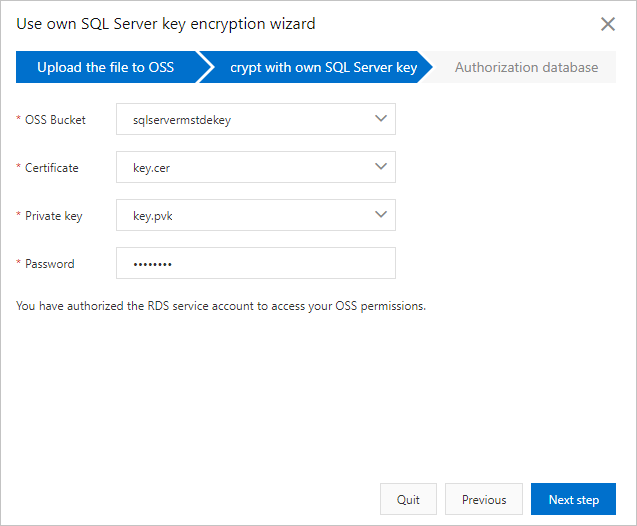
Click Next step to go to the Authorization database step.
Select databases from the Unselected Databases section, click the
 icon to move them to the Selected Databases section, and then click Confirm.
icon to move them to the Selected Databases section, and then click Confirm.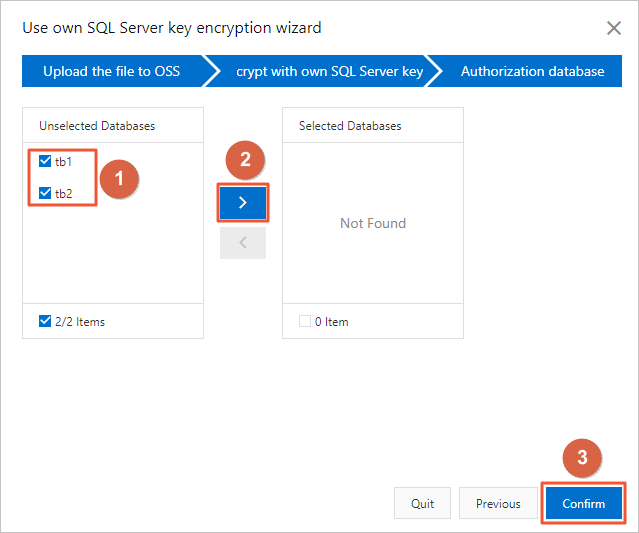
Disable TDE
Disabling TDE decrypts all data, which is a resource-intensive operation that consumes significant CPU, memory, and I/O resources. Decryption time scales with data volume — for a database with approximately 200 GB of data, decryption may take more than 40 minutes.
To disable TDE for specific databases: remove those databases from the Selected Databases section.
To disable TDE for the entire instance: remove all databases from the Selected Databases section. The system then disables TDE for the instance.
Steps:
Go to the Instances page. In the top navigation bar, select the region where the RDS instance resides, then click the instance ID.
In the left-side navigation pane, click Data Security.
Click the TDE tab, then click TDE Settings.
Select databases from the Selected Databases section, click the
 icon to move them to the Unselected Databases section, and then click OK.
icon to move them to the Unselected Databases section, and then click OK.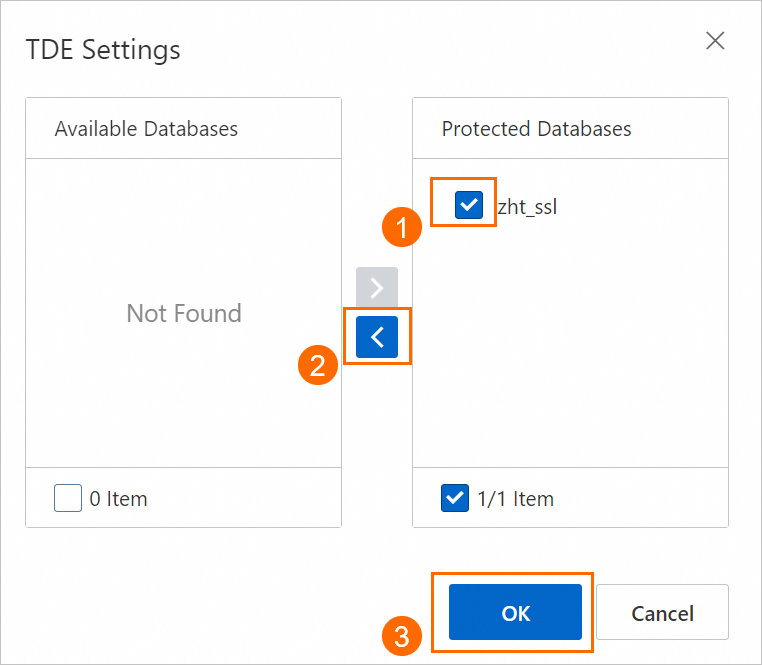
To check decryption progress after disabling TDE, run the following SQL statement:
SELECT
db_name(database_id) AS DatabaseName,
encryption_state,
percent_complete
FROM
sys.dm_database_encryption_keys;What's next
To enable TDE by calling an API operation, see ModifyDBInstanceTDE.
To encrypt connections to the RDS instance using SSL, see Configure the SSL encryption feature.