Use Resource Access Management (RAM) to grant a RAM user the permissions needed to manage ApsaraDB RDS instances. This lets you control exactly which RDS operations each RAM user can perform—without sharing your Alibaba Cloud account credentials.
For example, if you grant a RAM user the permission to call the CreateDBInstance operation, the RAM user can create an RDS instance in the ApsaraDB RDS console. The following procedure demonstrates granting permission to view RDS instance information.
Prerequisites
Before you begin, ensure that you have:
A RAM user. To create one, see Create a RAM user.
(Conditional) The
AliyunHDMFullAccesspermission granted to the RAM user, if the user needs access to performance optimization and diagnosis features.
Best practices
Grant only the permissions a RAM user needs for their role. For example, a monitoring engineer typically needs only read permissions (rds:Describe*), not write permissions. Applying least-privilege permissions reduces the impact if credentials are compromised.
For fine-grained access control, RAM authorization supports:
ARN-based authorization — scope permissions to a specific instance, region, or account
Resource group-based authorization — manage permissions by resource group
Tag-based authorization — control access using resource tags
For an example of granting read-only access to a single instance, see Grant a RAM user the read-only permissions on a specific ApsaraDB RDS instance.
Grant RDS permissions to a RAM user
The following example grants a RAM user permission to view RDS instance information (rds:Describe*). Other permissions follow the same pattern.
Step 1: Create a policy
Log on to the RAM console.
In the left-side navigation pane, choose Permissions > Policies.
Click Create Policy.
Choose a policy creation mode:
Visual editor — fill in a form to build the policy
JSON — write the policy document directly (more efficient for complex policies)
Visual editor
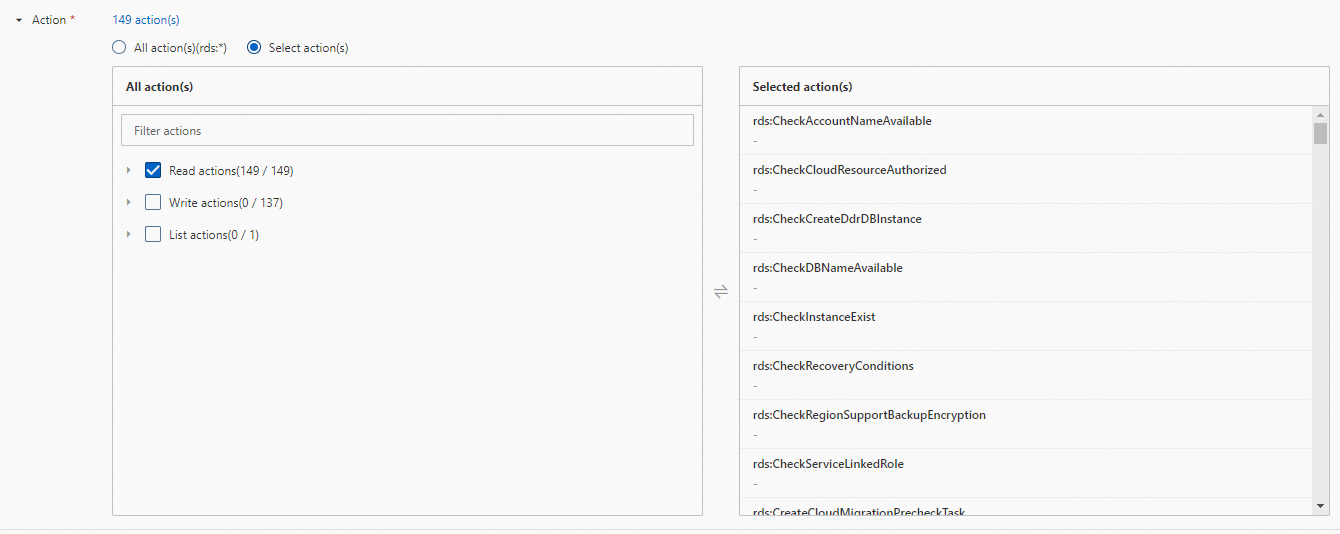
Configure the following parameters:
| Parameter | Description |
|---|---|
| Effect | Select Allow to grant the permissions. |
| Service | Select ApsaraDB RDS/RDS. |
| Action | Select the API operations to allow. To grant read-only access, select all Read actions. Include DescribeDBInstances — without it, the RAM user cannot view the instance list. If the policy document exceeds the length limit due to a large number of selected actions, submit a ticket to increase the limit. |
| Resource | Select All resource(s)(*) to apply to all instances, or select Specified resource(s) to scope by Alibaba Cloud Resource Name (ARN). See the ARN reference below. |
| Condition | (Optional) Add constraints such as restricting the source IP addresses from which the RAM user can log on. See Policy elements. |
ARN formats for specified resources
Configure the ARNs tagged as Required to make sure the policy works as expected. Without acs:rds:*:{#accountId}:dbinstance/*, the RAM user cannot view instances in the instance list.
| ARN format | Scope | Required |
|---|---|---|
acs:rds:{#regionId}:{#accountId}:dbinstance/{#dbinstanceId} | Region + account + instance ID | Yes |
acs:rds:{#regionId}:{#accountId}:dbinstance/* | Region + account | No |
acs:rds:*:{#accountId}:dbinstance/* | Account | Yes |
acs:rds:*:{#accountId}:dbinstance/{#dbinstanceId} | Account + instance ID | Yes |
JSON
Paste the following policy document into the code editor:
{
"Version": "1",
"Statement": [
{
"Effect": "Allow",
"Action": "rds:Describe*",
"Resource": "*"
}
]
}The policy has a single statement with three fields:
Effect:
Allowgrants the specified permissions.Action:
rds:Describe*matches all RDS API operations starting withDescribe, covering all read operations. Adjust to the specific operations your use case requires.Resource:
*applies to all RDS resources in the account. Replace with a specific ARN to scope the permissions further.
JSON mode is more efficient than the visual editor when you need to match multiple operations by prefix (for example, rds:Describe*) or copy an existing policy document.
Click OK. In the Create Policy dialog box, enter a Policy Name and an optional Description, then click OK.
Step 2: Attach the policy to the RAM user
In the left-side navigation pane, choose Identities > Users.
Find the RAM user, then click Add Permissions in the Actions column.
In the Policy section, select Custom Policy from the drop-down list.
Find and select the policy created in Step 1, then click OK.
Click Grant permissions.
Verify the configuration
Log on to the ApsaraDB RDS console using the RAM user's credentials and confirm that the user can view the RDS instance list. If the instance list is empty or inaccessible, check that the policy includes DescribeDBInstances and that the required resource ARNs are configured.
What's next
Review the full list of ApsaraDB RDS API operations you can grant: List of operations by function.
Learn how policy conditions, effects, and resource elements work together: Policy elements.