Cloud disk encryption protects data on ApsaraDB RDS for MariaDB instances by encrypting every data disk at the block storage level. Even if backup data is leaked, it cannot be decrypted without the corresponding key. Snapshots created for an encrypted instance are automatically encrypted, and no application changes are required.
The feature is free of charge. Read and write operations on encrypted disks incur no additional cost.
Prerequisites
Before you begin, ensure that you have:
-
An RDS instance being created — cloud disk encryption cannot be enabled after an instance is created
-
An instance created in standard mode
-
A key created based on the MariaDB version of the instance — see Create a CMK
Choose a key type
The key type you can use depends on the MariaDB version and instance type.
| MariaDB version | Instance type | Supported key types |
|---|---|---|
| 10.3 | Any | Customer master key (CMK) only |
| 10.6 | General-purpose | Service key managed by ApsaraDB RDS only |
| 10.6 | Dedicated | Service key managed by ApsaraDB RDS, or a CMK |
Service key: Managed by ApsaraDB RDS, permanently valid, and auto-created when you select Default Service CMK in the console. The key specification is Aliyun_AES_256. Key rotation is disabled by default — to enable it, purchase the key rotation feature in the Key Management Service (KMS) console. See Configure key rotation.
For MariaDB 10.6 instances, use the service key managed by ApsaraDB RDS. It is permanently valid and eliminates the risk of instance lockout from accidental key deletion.
Enable cloud disk encryption
When creating an RDS instance, configure the Storage Type parameter, select Disk Encryption, and then configure the Key parameter. For full creation steps, see Create an ApsaraDB RDS for MariaDB instance.
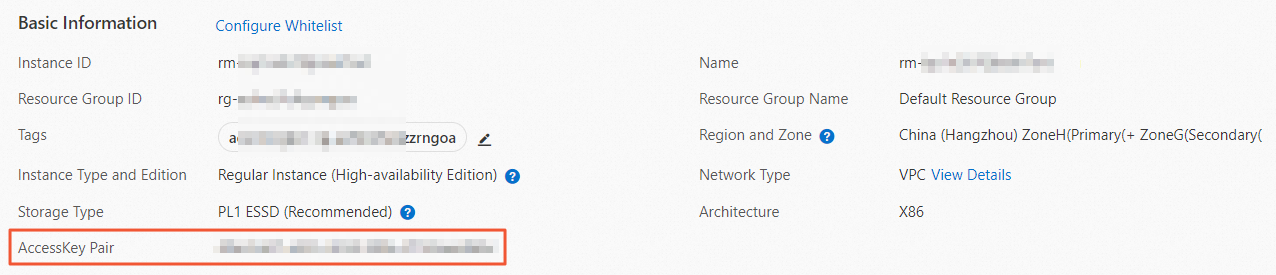
After the instance is created, view the key used for disk encryption on the Basic Information page of the instance.
Verify encryption
-
Go to the Instances page. In the top navigation bar, select the region where the instance resides. Find the instance and click its ID.
-
In the Basic Information section, check whether the AccessKey Pair parameter appears. If it does, cloud disk encryption is enabled.
Limitations
-
Cloud disk encryption cannot be disabled after it is enabled.
-
Cloud disk encryption does not interrupt your business, and no application changes are required.
-
If you create a new instance from an encrypted snapshot using cloud disks, cloud disk encryption is automatically enabled for the new instance.
-
If your Alibaba Cloud KMS account becomes overdue, cloud disks cannot be decrypted. Keep your KMS account in good standing. See What is KMS?
-
If the KMS key used for encryption is disabled or deleted, the RDS instance is locked and becomes inaccessible. The following operations are blocked: backups, instance specification changes, cloning, restarting, high-availability switchover, and parameter modifications.
View service keys in KMS
In the KMS console, go to Keys in the left navigation pane and click the Default Key tab. If the Key Usage column shows Service Key, the key is managed by an Alibaba Cloud service. The alias of the service key managed by ApsaraDB RDS is alias/acs/rds. If no key is listed, no service key has been created in that region yet — it is created automatically when you enable cloud disk encryption and select Default Service CMK during instance creation.
API reference
| Operation | Description |
|---|---|
| CreateDBInstance | Creates an instance |