This topic provides a step-by-step guide for configuring user-based single sign-on (SSO) from Google Workspace to Alibaba Cloud. After you complete the configuration, users in your Google Workspace organization can log on to the Alibaba Cloud Management Console by using their Google credentials.
Prerequisites
A Resource Access Management (RAM) administrator with the AliyunRAMFullAccess policy attached. For information about how to create a RAM user and grant permissions, see Create a RAM user and Grant permissions to a RAM user.
A Google Workspace account with super administrator permissions.
Configuration overview
The process involves establishing a trust relationship by exchanging metadata between Google Workspace (the IdP) and Alibaba Cloud (the SP).
Get Service Provider (SP) metadata from Alibaba Cloud. You will get the necessary URLs to configure Google Workspace.
Configure a custom SAML app in Google Workspace. You will add Alibaba Cloud as a trusted application.
Configure Alibaba Cloud with Google Workspace IdP metadata. You will provide the metadata from Google to complete the trust relationship.
Create and map users. You will ensure users exist in both systems and are correctly mapped.
Verify the SSO configuration. You will test both SP-initiated and IdP-initiated logon.
Step 1: Get SP metadata from Alibaba Cloud
First, you need to retrieve Alibaba Cloud's SAML configuration details to provide to Google Workspace.
Log on to the RAM console as a RAM administrator.
In the left-side navigation pane, choose .
Select the User-based SSO tab.
In the SAML Service Provider Metadata URL section and copy the URL.
Open the URL in a new browser tab. From the XML metadata document, note the following two values for use in the next step:
The
entityIDvalue from the<EntityDescriptor>tag.The
LocationURL from the<AssertionConsumerService>tag.
Step 2: Configure a custom SAML app in Google Workspace
Next, you will create a custom SAML application in Google Workspace to represent Alibaba Cloud.
Log on to the Google Admin console as a super administrator.
In the left-side navigation pane, choose .
Click .
In the App details step, enter an App name (such as
AlibabaCloudUserSSO) and click Continue.In the Google Identity Provider details step, download the IdP metadata by clicking DOWNLOAD METADATA. Save this XML file for the next step. Click Continue.
In the Service provider details step, configure the following fields using the information you noted from Step 1:
ACS URL: Paste the
LocationURL.Entity ID: Paste the
entityIDvalue.Start URL (Optional): Specify the Alibaba Cloud console page where users are redirected after a successful SSO logon. If you leave this empty, users are redirected to the homepage of the Alibaba Cloud Management Console.
NoteFor security reasons, the URL for Start URL must belong to an Alibaba-owned domain name, such as *.aliyun.com, *.hichina.com, *.yunos.com, *.taobao.com, *.tmall.com, *.alibabacloud.com, or *.alipay.com. If you specify a URL from an unauthorized domain name, the Start URL will be ignored.
Click Continue.
In the Attribute mapping step, you do not need to add mappings for user-based SSO. Click Finish.
On the application's page, expand the User access section.
Select ON for everyone to enable the application for all users in your organization, then click Save.
Step 3: Configure Alibaba Cloud with Google Workspace IdP metadata
Now, return to the Alibaba Cloud RAM console to complete the trust relationship.
In the RAM console, navigate to and select the User-based SSO tab.
Set SSO Status to Enabled.
NoteThis is a global setting that affects all RAM users. After you enable it, RAM users can no longer log on with a username and password. If you are logged on as a RAM user, do not enable SSO until you have verified the configuration is correct. To avoid being locked out, we recommend performing this configuration while logged on with your Alibaba Cloud account.
In the Metadata File section, click Upload Metadata File and select the IdP metadata file you downloaded from Google Workspace in Step 2.
Click Edit on the right of Auxiliary Domain Name. Enable the feature and enter your Google Workspace account's email suffix (such as
example.com). This tells Alibaba Cloud to trust SAML assertions containing usernames with this email suffix.
Step 4: Create and map users
For SSO to work, a user must exist in both Google Workspace and Alibaba Cloud RAM, and their identities must match.
In Google Workspace: Ensure the user who needs SSO access exists. For example, a user with the primary email
u2@example.com.In Alibaba Cloud RAM: Create a RAM user. The logon name of the RAM user must match the local-part of the Google user's email (such as
u2). The resulting User Principal Name (UPN) of the RAM user will beu2@example.com(assuming the auxiliary logon suffix is configured), which will match the identity sent by Google. For more information, see Create a RAM user.
Verify the SSO configuration
You can verify the configuration by initiating SSO from both Alibaba Cloud (SP-initiated) and Google Workspace (IdP-initiated).
SP-initiated logon
Log on to the RAM console. On the Overview page, copy the logon URL for RAM users.
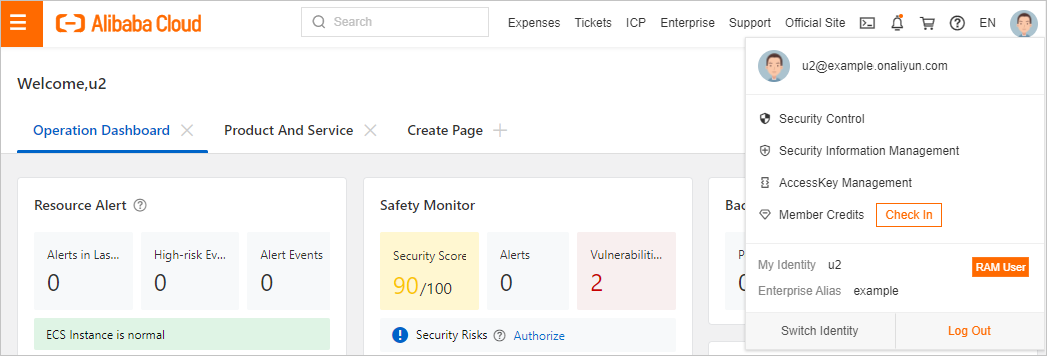
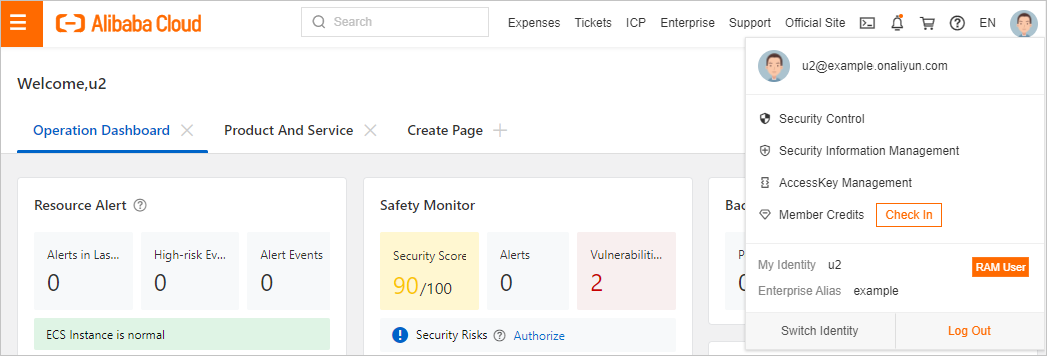
Hover over the profile picture in the upper-right corner and click Log Out. Then, navigate to the RAM user logon URL.
Click Login with Cloud Account. You are redirected to the logon page of Google.

Enter the credentials for your Google Workspace user (such as
u2@example.com).After successful authentication, you are automatically logged on to the Alibaba Cloud Management Console. You are redirected to the page specified by the Start URL parameter. If Start URL is not set or is invalid, you are redirected to the Alibaba Cloud Management Console homepage.
IdP-initiated logon
Log on to your Google account.
From the Google Apps menu (the "waffle" icon), find and click the custom SAML application you created (such as
AlibabaCloudUserSSO).You should be automatically logged on and redirected to the Alibaba Cloud Management Console.