Transparent data encryption (TDE) encrypts PolarDB for PostgreSQL data files at rest in real time. Data is encrypted before it is written to disk and decrypted when it is read into memory — with no increase in file size and no changes needed in your application code or configuration.
TDE cannot be disabled after it is enabled. Enabling TDE restarts the PolarDB cluster. Schedule this operation during a maintenance window to minimize impact.
Prerequisites
Before you begin, ensure that you have:
Activated KMS by purchasing a dedicated KMS instance
A PolarDB for PostgreSQL cluster running one of the following minor engine versions: To check your current minor engine version, run
SHOW polardb_version;in the console or view the minor engine version in the console. If the version is below the minimum, upgrade the minor engine version before proceeding.PostgreSQL version Minimum minor engine version PostgreSQL 14 2.0.14.12.23.1 PostgreSQL 16 2.0.16.9.6.0 PostgreSQL 17 2.0.17.6.4.0 PostgreSQL 18 2.0.18.0.1.0
How TDE works
TDE operates at the database layer. It prevents anyone who bypasses the database — such as OS users reading tablespace files directly, or parties accessing raw disk or backup data — from viewing plaintext data.
Keys for TDE are generated and managed by Key Management Service (KMS). PolarDB does not provide the keys or certificates used for encryption. Two key types are available:
| Key type | Who controls it | Life cycle management |
|---|---|---|
| Default key (CMK) | Alibaba Cloud | Fully automatic — you have no management tasks |
| Custom key | You | You control rotation, deletion, and access grants |
Use a default key when you want encryption with zero key-management overhead. Use a custom key when your security policy requires you to control key access — for example, to meet PCI-DSS or HIPAA requirements, or to implement separation of duties between security and database teams.
Limitations
TDE cannot be disabled. Once enabled, encryption persists for the lifetime of the cluster.
Distributed clusters are not supported. TDE is only available on standard PolarDB for PostgreSQL clusters.
The only supported key type is `Aliyun_AES_256`. Other key algorithms are not accepted.
Performance: For I/O-intensive workloads, enabling TDE may reduce database performance.
Custom key requirements:
You must use an Alibaba Cloud account or an account with the AliyunSTSAssumeRoleAccess permission.
Disabling, scheduling for deletion, or deleting the key material makes the key unavailable immediately.
Revoking KMS authorization and then restarting the cluster renders the cluster unavailable.
Enable TDE for an existing cluster
Enabling TDE restarts the cluster. Schedule this operation during a maintenance window to minimize impact.
Log in to the PolarDB console. In the left navigation pane, click Clusters. Select the region where your cluster is located, then click the cluster ID.
In the left navigation pane, choose Settings and Management > Security.
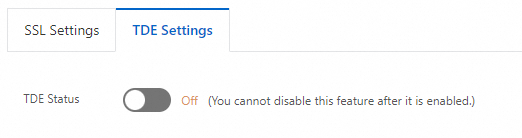
On the TDE Settings tab, turn on the TDE Status switch.
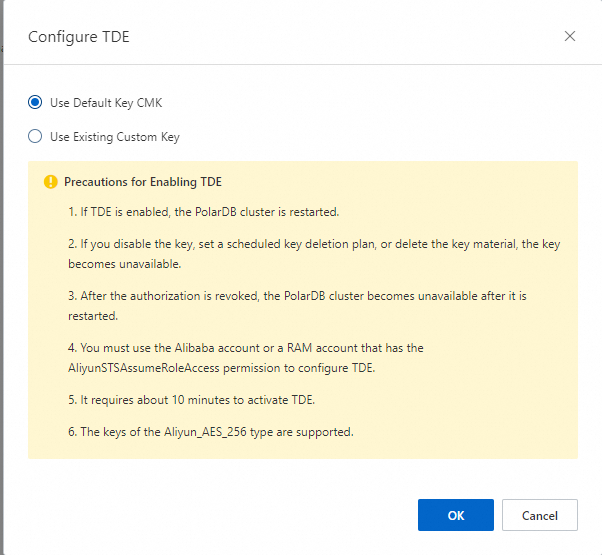
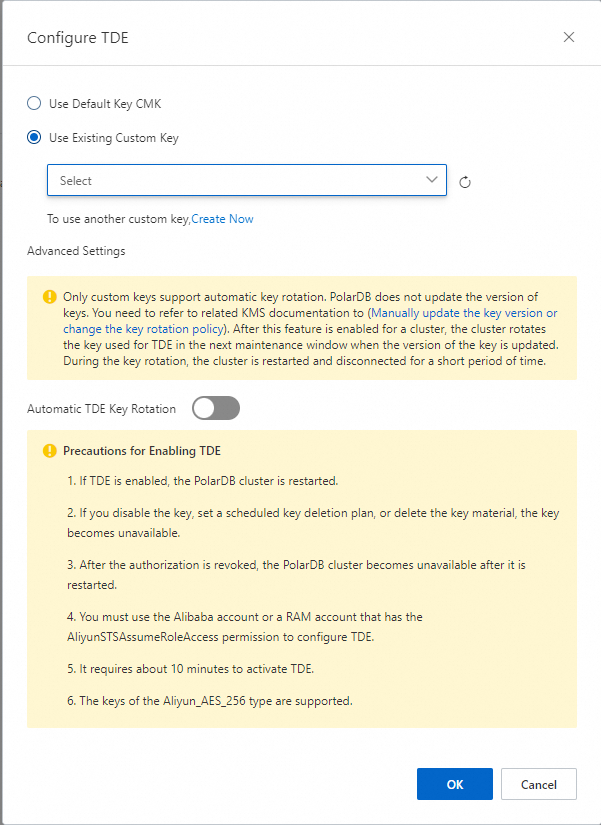
In the Configure TDE dialog box, select a key type:
Use Default Key CMK — Click OK to enable TDE immediately.
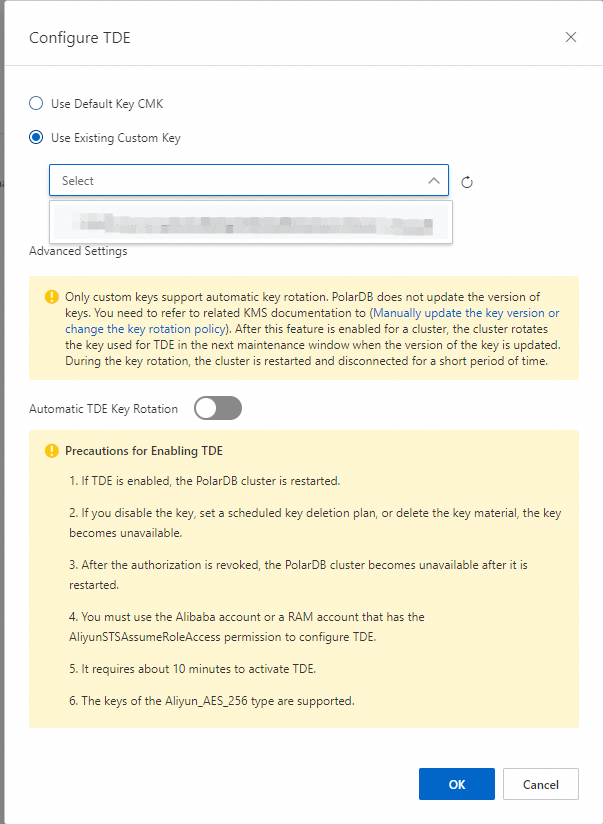
Use Existing Custom Key — Select a KMS key from the drop-down list, then click OK.
 If you do not have a custom key yet, click Create Now to create one in the KMS console. For details, see Create a key.
If you do not have a custom key yet, click Create Now to create one in the KMS console. For details, see Create a key.
Enabling TDE takes about 10 minutes.
To enable TDE at cluster creation instead, see Create a database cluster.
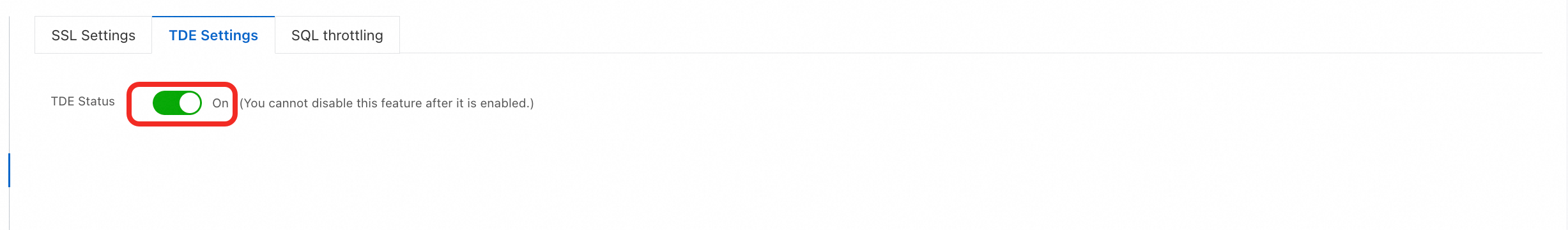
View the TDE status
Log in to the PolarDB console. In the left navigation pane, click Clusters. Select the region, then click the cluster ID.
In the left navigation pane, choose Settings and Management > Security.
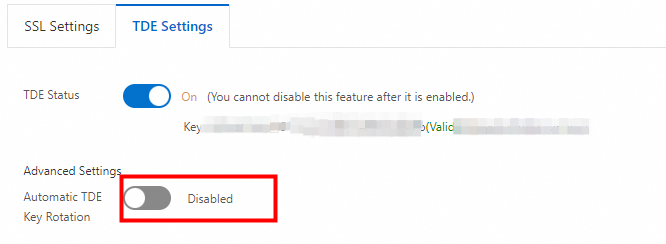
On the TDE Settings tab, check the TDE Status switch.
Switch to a custom key
Log in to the PolarDB console. In the left navigation pane, click Clusters. Select the region, then click the cluster ID.
In the left navigation pane, choose Settings and Management > Security.
On the TDE Settings tab, click the TDE Status switch.
In the dialog box, select Use Existing Custom Key, choose a KMS key from the drop-down list, and click OK.
For more information about using a custom key, see the notes in the Limitations section above.
Configure automatic key rotation
Automatic key rotation is available only when TDE is enabled with a custom key. PolarDB does not update the master key version itself — you manage key versions in KMS. When PolarDB detects that the master key version has been updated, it rotates the TDE key during the next maintenance window. The cluster restarts during this process.
To manually update or schedule key rotation in KMS, see Key rotation.
Enable automatic key rotation using either method:
During TDE setup: In the Configure TDE dialog box, expand Advanced Settings and turn on Automatic TDE Key Rotation.
After TDE is enabled: On the Configure TDE tab, expand Advanced Settings and turn on Automatic TDE Key Rotation.
FAQ
Can I still use tools like Navicat after enabling TDE?
Yes. TDE is transparent to authenticated applications and database tools. No client-side changes are needed.
Why does my data appear in plaintext after I enable TDE?
TDE encrypts data at rest — on disk and in backups. When you query data, the database decrypts it into memory before returning results, so it always appears as plaintext in query output. The encryption protects against unauthorized access to the raw storage files, not to authenticated queries.
API reference
| API | Description |
|---|---|
| ModifyDBClusterTDE | Enable TDE for a cluster or modify the encryption method |
| DescribeDBClusterTDE | Query the TDE settings of a cluster |
| CreateDBCluster | Create a cluster with TDE enabled (set DBType to PostgreSQL) |