SSL encryption establishes encrypted connections at the transport layer between clients and your PolarDB for MySQL cluster, protecting data integrity and confidentiality in transit. SSL was developed by Netscape and supports encryption algorithms such as RC4, MD5, and RSA. The Internet Engineering Task Force (IETF) upgraded SSL 3.0 to Transport Layer Security (TLS). Although the term "SSL encryption" is still used in the industry, SSL encryption in this topic refers to TLS encryption. Enabling SSL increases network connection response time.
When to enable SSL
Internet-facing connections -- A client that connects to a PolarDB cluster over the Internet traverses an untrusted network. SSL encryption prevents man-in-the-middle attacks.
Compliance requirements -- Regulations such as PCI-DSS and GDPR require sensitive data to be encrypted in transit.
Cross-network communication -- In hybrid cloud or multi-VPC architectures, data that crosses network boundaries requires SSL encryption to maintain confidentiality and integrity.
Before you begin
Before you begin, ensure that you have:
A PolarDB for MySQL cluster running in any supported region
Access to the PolarDB console with sufficient permissions to modify cluster settings
A maintenance window scheduled during off-peak hours. Enabling SSL restarts the cluster
An automatic reconnection mechanism in your application code. Cluster restarts terminate active connections
Usage notes
Certificate validity -- SSL certificates are valid for one year. Update the certificate before it expires and re-download and configure the CA certificate. Otherwise, client applications that use encrypted connections will fail to connect.
Cluster restart -- The following operations restart the cluster: enabling or disabling SSL encryption, updating the certificate validity period, modifying the protected endpoint, and automatic certificate rotation. Perform these operations during off-peak hours and make sure your application has an automatic reconnection mechanism.
Endpoint length limit -- The endpoint of a PolarDB cluster with SSL enabled must be less than 64 characters long. For more information about how to modify an endpoint, see Configure database proxy.
Enable SSL encryption
Enabling SSL encryption restarts the cluster. Perform this operation during off-peak hours.
Log on to the PolarDB console. In the upper-left corner, select the region where the cluster is deployed. In the navigation pane on the left, click Clusters. Then, click the ID of the cluster.
In the navigation pane on the left, choose Settings and Management > Security.
On the SSL Settings tab, click the slider next to SSL Status to enable SSL encryption.
SSL can be configured for the primary endpoint, cluster endpoint, and custom endpoints.
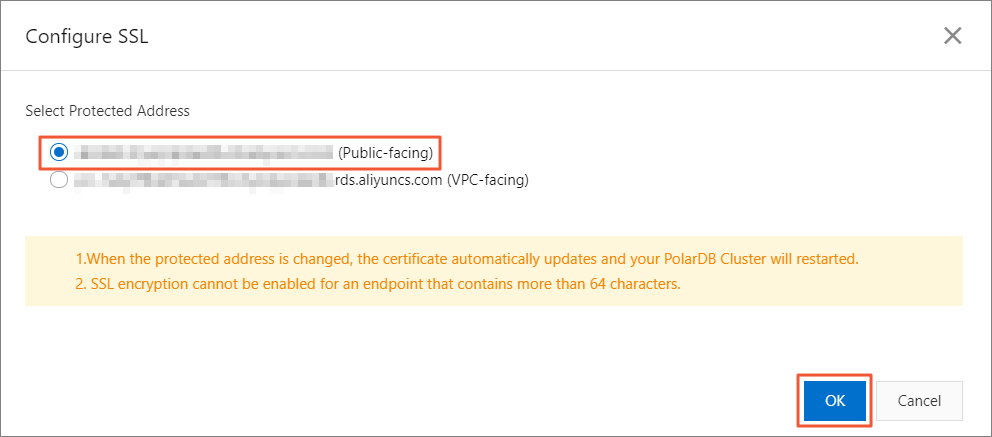
In the Configure SSL dialog box, select the endpoint for which you want to enable SSL encryption, and click OK.
You can encrypt the private endpoint or the public endpoint, but only one endpoint at a time.
Download the certificate
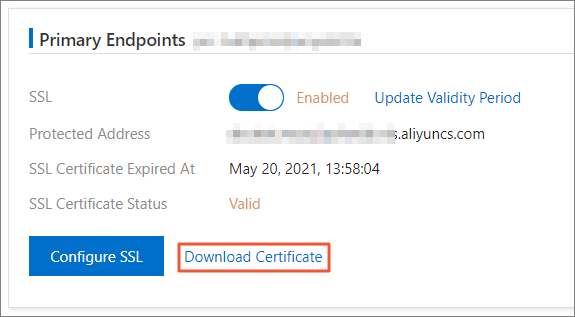
After you enable SSL encryption, download the CA certificate to verify the authenticity of the database server when connecting from a client.
On the SSL Settings tab, click Download in the corresponding endpoint section.
The downloaded package contains three files:
File type Purpose .p7b Import the CA certificate on Windows. .pem Import the CA certificate on other operating systems or in other applications. .jks A Java truststore certificate file. The password is apsaradb. Use this file to import the CA certificate chain into Java applications. The password cannot be changed.
If you use a JKS certificate file in Java, modify the default JDK security configuration for JDK 7 and JDK 8. On the server that connects to the PolarDB database, update the following two settings in the jre/lib/security/java.security file: Without this change, Java throws the following error:
jdk.tls.disabledAlgorithms=SSLv3, RC4, DH keySize < 224
jdk.certpath.disabledAlgorithms=MD2, RSA keySize < 1024javax.net.ssl.SSLHandshakeException: DHPublicKey does not comply to algorithm constraintsConnect from a client
Whether the connection uses SSL depends on the client type and settings. Configure SSL on the client side to establish an encrypted connection and verify the identity of the PolarDB cluster.
If you use DMS to log on to and manage a PolarDB cluster, you do not need to encrypt the data link.
Command line
For MySQL clients version 5.7.11 and later, add the --ssl-mode option to configure SSL encryption:
| Mode | Behavior |
|---|---|
--ssl-mode=DISABLED | No encryption. |
--ssl-mode=PREFERRED (default) | Attempt an encrypted connection. Fall back to an unencrypted connection if SSL is unavailable. |
--ssl-mode=REQUIRED | Require an encrypted connection. Fail if SSL is unavailable. |
--ssl-mode=VERIFY_CA | Require an encrypted connection. Verify the server certificate against the local CA certificate. |
--ssl-mode=VERIFY_IDENTITY | Require an encrypted connection. Verify the server certificate and confirm that the hostname or IP address matches the certificate. |
Attempt an encrypted connection with fallback:
mysql -h {endpoint} -u {username} -p --ssl-mode=PREFERREDRequire an encrypted connection with CA verification:
mysql -h {endpoint} -u {username} -p --ssl-mode=VERIFY_CA --ssl-ca={path_to_CA_certificate}/ApsaraDB-CA-Chain.pemReplace {endpoint}, {username}, and {path_to_CA_certificate} with your actual values.
For more information about the --ssl-mode option, see the official MySQL documentation.
MySQL Workbench
Open MySQL Workbench and choose Database > Manage Connections.
Enter the PolarDB endpoint, username, and password.
On the SSL tab, set the Use SSL parameter. For the SSL CA File parameter, specify the path to the downloaded PEM-format CA certificate. Then, click Test Connection or OK.
For information about the options for the Use SSL parameter, see the description of the --ssl-mode option for command-line connections.
Java
This example uses Connector/J (mysql-connector-java), the official MySQL JDBC driver. Add the following Maven dependency:
<dependency>
<groupId>mysql</groupId>
<artifactId>mysql-connector-java</artifactId>
<version>8.0.19</version>
</dependency>The following sample code uses the sslMode property, which is supported in mysql-connector-java version 8.0.13 and later. For earlier versions, use the useSSL, requireSSL, and verifyServerCertificate properties instead. For more information, see the MySQL documentation.
package com.example.ssltest;
import com.mysql.cj.jdbc.MysqlDataSource;
import java.sql.Connection;
import java.sql.ResultSet;
import java.sql.SQLException;
import java.sql.Statement;
public class Main {
public static void main(String[] args) {
Connection conn = null;
MysqlDataSource mysqlDS=null;
try{
mysqlDS = new MysqlDataSource();
// Set SslMode as needed. For more information about the options for this property, see the command-line connection method.
mysqlDS.setSslMode("VERIFY_IDENTITY");
// The truststore is used to store the CA certificate. Set the truststore type to JKS.
mysqlDS.setTrustCertificateKeyStoreType("JKS");
// Replace the path after file:/ with the path to your ApsaraDB-CA-Chain.jks file.
mysqlDS.setTrustCertificateKeyStoreUrl("file://{path_to_CA_certificate}/ApsaraDB-CA-Chain.jks");
// The password for the downloaded JKS file is apsaradb and cannot be changed.
mysqlDS.setTrustCertificateKeyStorePassword("apsaradb");
// Your database endpoint
mysqlDS.setServerName("your_polardb_host");
// Your database port
mysqlDS.setPort(3306);
// Your database username
mysqlDS.setUser("your_username");
// Your database password
mysqlDS.setPassword("your_password");
// Your database name
mysqlDS.setDatabaseName("your_database");
System.out.println("Attempting to connect to the database...");
conn = mysqlDS.getConnection();
System.out.println("Database connection successful!");
// Use try-with-resources to ensure that Statement and ResultSet are automatically closed
try (Statement stmt = conn.createStatement();
ResultSet rs = stmt.executeQuery("SELECT VERSION()")) {
// Check if the query returned a result
if (rs.next()) {
// Get the result from the first column and print it
String dbVersion = rs.getString(1);
System.out.println("Database version: " + dbVersion);
} else {
System.out.println("Failed to retrieve database version information.");
}
}
}catch(Exception e){
e.printStackTrace();
} finally {
try {
if (conn != null)
conn.close();
} catch (SQLException e) {
e.printStackTrace();
}
}
}
}Python
# Install pymysql
# pip install pymysql
import pymysql
# --- Configure your database information ---
db_config = {
'host': 'your_polardb_host', # Your cluster endpoint
'user': 'your_username', # Your username
'password': 'your_password', # Your password
'database': 'your_database', # The database you want to connect to
'port': 3306
}
# --- Configure SSL information ---
ssl_args = {
'ca': '{path_to_CA_certificate}/ApsaraDB-CA-Chain.pem',
'mode': 'VERIFY_CA'
}
try:
# Establish a connection and pass the ssl parameter
print("Attempting to connect to MySQL using SSL...")
connection = pymysql.connect(**db_config, ssl=ssl_args)
print("SSL connection successful!")
with connection.cursor() as cursor:
# Execute a simple query to verify the connection
cursor.execute("SELECT VERSION()")
version = cursor.fetchone()
print(f"Database version: {version[0]}")
except pymysql.MySQLError as e:
# Printing SSL-related errors can be helpful
print(f"Connection failed: {e}")
finally:
if 'connection' in locals() and connection.open:
connection.close()
print("Database connection closed.")Verify the encrypted connection
PolarDB supports TLSv1.2 and later versions. During the SSL handshake, the client and PolarDB negotiate connection parameters such as the TLS version, cipher suite, and session key. For a detailed list of cipher suites, see the OpenSSL official website.
Connect to the PolarDB cluster using an SSL-configured client.
Run the following SQL statement:
SHOW STATUS LIKE 'ssl_cipher';
+---------------+---------------------------+
| Variable_name | Value |
+---------------+---------------------------+
| Ssl_cipher | DHE-RSA-AES256-GCM-SHA384 |
+---------------+---------------------------+Interpret the result:
A non-empty
Value(such asDHE-RSA-AES256-GCM-SHA384) confirms that the connection is encrypted.An empty
Valuemeans the connection is not encrypted. Check your client configuration.
Manage SSL certificates
Modify the protected endpoint
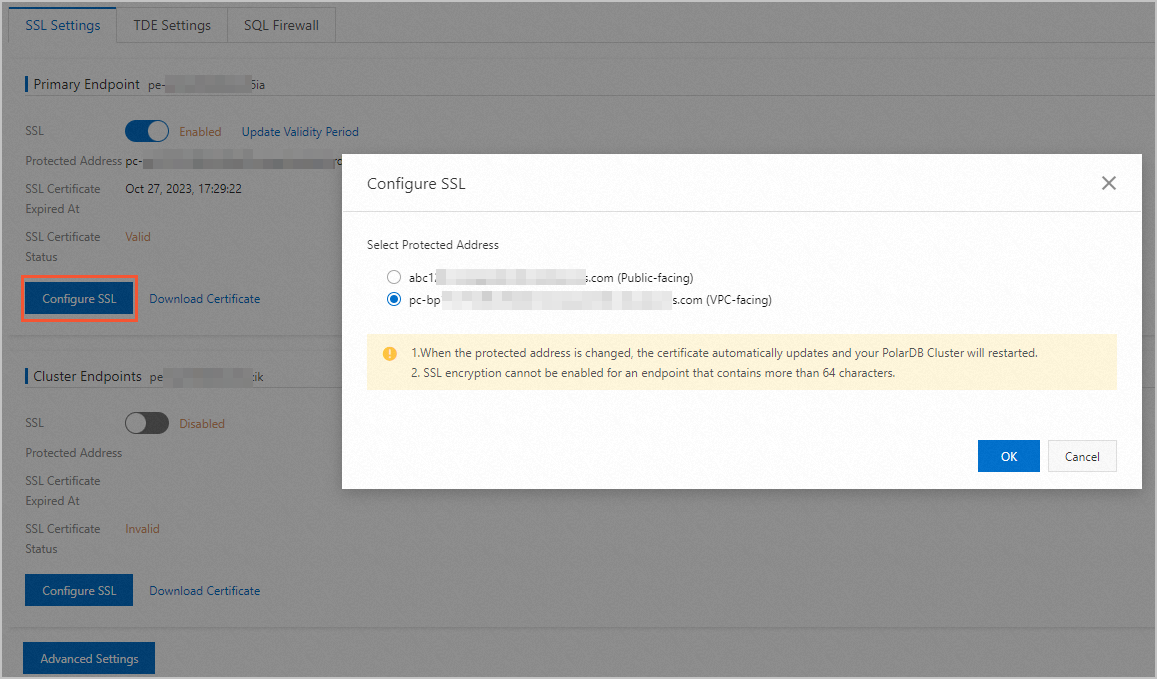
To change the SSL-protected endpoint, click Configure SSL in the corresponding endpoint section on the SSL Settings tab.
After you modify the protected endpoint, PolarDB automatically updates the SSL certificate and restarts the cluster. Perform this operation during off-peak hours.
Update the certificate validity period
If you modified the SSL endpoint or the certificate is about to expire, manually update the certificate.
Updating the certificate validity period restarts the cluster. Perform this operation during off-peak hours.
On the SSL Settings tab, click Update Validity Period.
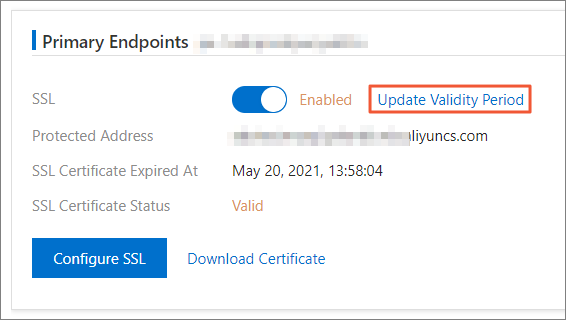
In the dialog box that appears, click OK.
After the update, download and configure the new certificate on all clients that use CA certificate verification (VERIFY_CA or VERIFY_IDENTITY mode).
Enable automatic certificate rotation
After you enable automatic certificate rotation, PolarDB automatically renews the certificate within the cluster's maintenance window in the 10 days before the certificate expires.
Automatic certificate renewal restarts the cluster. Perform this operation during off-peak hours.
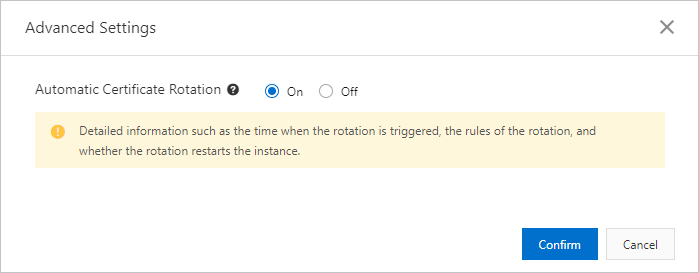
On the SSL Settings tab, click Advanced Settings.
In the Advanced Settings dialog box, enable automatic certificate rotation and click OK.
Disable SSL encryption
Disabling SSL encryption restarts the cluster. Perform this operation during off-peak hours.
On the SSL Settings tab, click the slider next to SSL Status to disable SSL encryption.
In the dialog box that appears, click OK.
Sysbench stress testing
To run Sysbench benchmarks over an SSL-encrypted connection:
Download and decompress the certificate.
Configure Sysbench:
Add
--mysql-ssl=onto thesysbenchcommand line.For Sysbench 1.0.x, rename the .pem file to
cacert.pemand place it in the directory from which you run thesysbenchcommand. The SSL certificate name is hard-coded ascacert.pemin this version.For Sysbench 1.1.x, use the same method as 1.0.x, or pass the path of the PEM file using the
--mysql-ssl-caparameter.
For more information about the stress testing method, see Performance test method (OLTP).
During stress testing, make sure the MySQL client version is consistent with the MySQL version of PolarDB.
API reference
| API | Description |
|---|---|
| DescribeDBClusterSSL | Queries the SSL settings of a PolarDB cluster. |
| ModifyDBClusterSSL | Enables or disables SSL encryption, or updates the CA certificate for a PolarDB cluster. |