This document covers the causes and solutions for HTTP 403 errors returned by OSS.
Quick reference
| Error code | Error message | Description |
|---|---|---|
| AbnormalBucketOwnerStatus | The status of the bucket owner is abnormal | The bucket owner's account is unavailable |
| AccessDenied | Multiple messages | Permission denied for the requested operation |
| AccessForbidden | CORSResponse: This CORS request is not allowed... | Cross-origin resource sharing (CORS) request blocked |
| AccessKeyIdAndSecurityTokenNotMatch | The OSS access key id and security token you provided does not match | AccessKey ID and STS token mismatch |
| BucketDisable | BucketDisable | Bucket disabled for security reasons |
| BucketNotBelongTo | The bucket you access does not belong to you | Current user is not the bucket owner |
| CnameDenied | The cname belongs to another user | Custom domain name already bound to another bucket |
| ImageDamage | The image file may be damaged | Image file is corrupted or missing data |
| InvalidAccessKeyId | Multiple messages | AccessKey ID invalid, nonexistent, or disabled |
| InvalidObjectState | The operation is not valid for the object's state | Archive object not ready for download |
| InvalidSecurityToken | The security token you provided is invalid | STS token is invalid |
| InDebt | Current user is indebted | OSS access blocked due to overdue payment |
| InDebtOverdue | Current user is indebted Overdue | OSS payment overdue |
| UbsmsInvalidBid | Your account partner does not have KMS Service | Key Management Service (KMS) not activated |
| NonStandardHostForbidden | Your host is invalid. Please use Open Storage Service standard host | Non-standard OSS host format |
| PermanentRedirect | The bucket you are attempting to access must be addressed using the specified endpoint... | Endpoint does not match the bucket's region |
| RequestTimeTooSkewed | The difference between the request time and the current time is too large | Request time differs from server time by more than 15 minutes |
| SecondLevelDomainForbidden | Multiple messages | Second-level or invalid domain used to access OSS |
| SecurityTokenExpired | The security token you provided has expired | STS token has expired |
| SecurityTokenNotSupported | Multiple messages | STS token used in unsupported region or operation |
| SignatureDoesNotMatch | The request signature we calculated does not match the signature you provided | Client and server signatures do not match |
| TransferAccelerationDisabled | Transfer acceleration is disabled | Transfer acceleration not supported in this region |
| UserDisable | UserDisable | User account disabled or OSS not activated |
| WORMConfigurationLocked | The WORM Configuration is locked | Retention policy is locked and cannot be deleted |
AbnormalBucketOwnerStatus
This error is returned when the bucket owner's account has an abnormal status.
The status of the bucket owner is abnormal
Cause: The service is unavailable to the owner of the target bucket.
Solution: Check whether the bucket owner's Alibaba Cloud account has been deleted or restricted for security reasons. Also confirm whether the service has been suspended due to overdue payments.
AccessDenied
This error is returned when a user does not have permission to perform the requested operation.
Not sure where to start? Use this checklist to narrow down the cause:
Identify the requester type. Check whether the request is anonymous, signed with an AccessKey pair, or signed with a Security Token Service (STS) token. Anonymous requests have no user policy attached.
Verify your credentials. Make sure the AccessKey ID and AccessKey secret are correct and active. You can verify them by logging in to ossbrowser.
Check whether the denial is explicit or implicit. An explicit denial means a
Denystatement in a policy blocked the request — find and update that policy. An implicit denial means noAllowstatement covers the action — add the required permission.Check all applicable policies. For RAM users, check Resource Access Management (RAM) policies. For STS tokens, check both the RAM role policy and the STS policy. For bucket access, check bucket policies. For VPC-based access, check Virtual Private Cloud (VPC) endpoint policies.
Access denied by authorizer's policy
Cause: You do not have the required permissions to perform the operation.
Solution: The final permissions of an STS token are the intersection of the RAM role's permissions (configured in Step 4) and the permissions in the STS policy (configured in Step 5). Use the following examples to check the intersection.
Example 1: A represents the RAM role permissions, B represents the STS policy permissions, and C (the overlap) represents the final effective permissions.
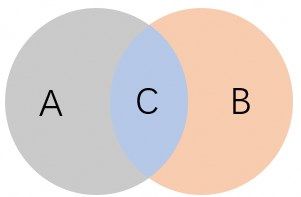
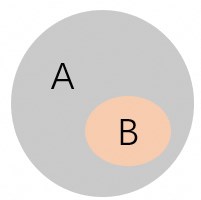
Example 2: The STS policy permissions (B) are a subset of the RAM role permissions (A). Therefore, B represents the final effective permissions.
Access denied by bucket policy
Cause: Access is denied by the bucket policy.
Solution: Update the bucket policy to grant the required permissions. For more information, see Configure bucket policies to authorize other users to access specified resources.
Access denied by VPC endpoint policy
Cause: A VPC endpoint policy configured for the client's VPC is blocking the request.
Solution: Check and update the endpoint policy for the VPC where the client resides.
AccessDenied
Cause: The credentials used do not have the required permissions.
Solution:
Verify that the AccessKey ID and AccessKey secret are correct. For more information, see Create an AccessKey pair.
Verify that the RAM user has the required permissions on the bucket or object.
Anonymous access is forbidden for this operation
Cause: The operation requires authentication, but the request was sent without credentials.
Solution: Configure a bucket policy to grant anonymous users access to the specific resources they need. For more information, see Configure bucket policies to authorize other users to access specified resources.
Anonymous user has no right to access this bucket
Cause: Anonymous users are not permitted to access this bucket.
Solution: Configure a bucket policy to grant anonymous users the required access. For more information, see Configure bucket policies to authorize other users to access specified resources.
Anonymous user has no right to access this object
Cause: Anonymous users are not permitted to access this object.
Solution: Configure a bucket policy to grant anonymous users access to the specific resources they need. For more information, see Configure bucket policies to authorize other users to access specified resources.
Hierarchical namespace is disabled
Cause: The hierarchical namespace feature is not enabled for the bucket. Renaming directories and files requires this feature.
Solution: Enable hierarchical namespace when creating the bucket. For supported regions and applicable scenarios, see Enable the hierarchical namespace feature.
Invalid according to Policy: Policy Condition failed: " + RelatedUnit; //XXX
Cause: The conditions in the
policyform field are invalid.Solution: Specify valid conditions in the
policyform field. For supported conditions and matching methods, see Appendix: Post Policy.
Invalid according to Policy: Policy Condition failed: ["eq", "$Content-Type", "image/png"]
Cause: The file type does not match the
Content-Typevalue specified in the policy.Solution: The
Content-Typefield in a PostObject policy restricts which file types can be uploaded. If the policy limits uploads toimage/png, only files of that type are accepted. To allow other types, add the correspondingContent-Typevalues to the policy. For a list of common Content-Type values, see How do I set Content-Type (MIME)?.
Invalid according to Policy: Policy expired
Cause: The policy in the PostObject request has expired.
Solution: The
policyform field contains a Base64-encoded, UTF-8 JSON object that declares the conditions the request must satisfy, including an expiration time. Make sure theexpirationvalue has not passed. The format is:{ "expiration": "2014-12-01T12:00:00.000Z", "conditions": [ {"bucket": "johnsmith"}, ["starts-with", "$key", "user/eric/"] ] }For more information about supported conditions, see Appendix: Post Policy.
Invalid date (should be seconds since epoch)
Cause: The
Expiresparameter value is not a valid Unix timestamp.Solution: Set
Expiresto a Unix timestamp — the number of seconds elapsed since 00:00:00 UTC on January 1, 1970. This value specifies when the URL expires.
Query string authentication requires the Signature, Expires and OSSAccessKeyId parameters
Cause: The signed URL is missing one or more required parameters.
Solution: A signed URL must include at least
Signature,Expires, andOSSAccessKeyId. Example:http://oss-example.oss-cn-hangzhou.aliyuncs.com/oss-api.pdf?OSSAccessKeyId=nz2pc56s936**9l&Expires=1141889120&Signature=vjbyPxybdZaNmGa%2ByT272YEAiv****For more information, see Include a signature in a URL.
Request has expired
Cause: The
Expiresvalue in the request has already passed.Solution: Set a valid
Expiresvalue for the request. For details on settingExpiresin upload requests, see PutObject, PostObject, AppendObject, and InitiateMultipartUpload.
Target object does not reside in the same data center as source object
Cause: Cross-region object copy is not supported.
Solution: Objects can only be copied between buckets in the same region. The source and destination buckets can be the same or different. For more information, see CopyObject.
The bucket you are attempting to access must be addressed using the specified endpoint. Please send all future requests to this endpoint
Cause: The endpoint used in the request does not match the bucket's region.
Solution: Use the correct endpoint for the bucket's region. For example, a bucket in the
oss-cn-hangzhouregion has the public endpointoss-cn-hangzhou.aliyuncs.com. For a full list of endpoints, see Access OSS over IPv6.
This request is forbidden by kms
Cause: The credentials used do not have permission to use the specified Key Management Service (KMS) customer master key (CMK).
Solution: Make sure the credentials have the required permissions for the CMK ID. For more information, see Server-side encryption.
You are denied by bucket referer policy
Cause: The request's
Refererheader did not pass the bucket's hotlink protection check.Solution: Hotlink protection restricts access by validating the
Refererheader against a whitelist of allowed domain names, and optionally blocking requests with an emptyReferer. Add the required domain to the Referer whitelist. For more information, see Configure hotlink protection.
You do not have read acl permission on this object
Cause: The credentials used do not have permission to read the object's access control list (ACL).
Solution: Contact the object owner to grant the
GetObjectACLpermission.
You do not have read permission on this object
Cause: The credentials used do not have read permission on the object.
Solution: Contact the object owner to grant read permission.
You do not have write acl permission on this object
Cause: The credentials used do not have permission to update the object's ACL.
Solution: Contact the object owner to grant the
PutObjectACLpermission.
You do not have write permission on this object
Cause: The credentials used do not have write permission on the object.
Solution: Contact the object owner to grant write permission.
You have no right to access this object
Cause: The RAM user does not have permission to access this object.
Solution: Grant the RAM user the required permissions for the object. For examples of common RAM policies for different access scenarios, see Tutorial: Use RAM policies to control access to OSS.
You have no right to access this object because of bucket acl
Cause: The bucket ACL does not allow the requested operation on this object.
Solution: Grant the required OSS permissions, such as
PutObject,GetObject, andAppendObject. For common RAM policy examples, see Common examples of RAM policies.
AccessForbidden
This error is returned when a CORS request is blocked or other access restrictions are in place.
CORSResponse: This CORS request is not allowed. This is usually because the evaluation of Origin, request method / Access-Control-Request-Method or Access-Control-Requet-Headers are not whitelisted by the resource's CORS spec
Cause: CORS is not configured for the bucket, or the existing CORS configuration does not allow this request's origin, method, or headers.
Solution: Configure CORS rules for the bucket. For more information, see Configure cross-origin resource sharing.
AccessKeyIdAndSecurityTokenNotMatch
This error is returned when the provided AccessKey ID and STS token do not match.
The OSS access key id and security token you provided does not match
Cause: The AccessKey pair provided by the user does not match the STS token.
Solution: For more information, see Use an STS token to access OSS.
BucketDisable
This error is returned when the bucket is disabled for security reasons.
BucketDisable
Cause: The bucket is disabled for security reasons.
Solution: Check whether your account has overdue payments, or contact technical support for a security review.
BucketNotBelongTo
This error is returned when a user attempts to access a bucket that does not belong to them.
The bucket you access does not belong to you
Cause: The current user is not the owner of the target bucket.
Solution: Only the bucket owner can perform this operation.
CnameDenied
This error is returned when a domain name binding operation is denied.
The cname belongs to another user
Cause: The domain name is already bound to another bucket.
Solution: Either use a different domain name, or verify ownership of the domain name to reassign it to your bucket. Verifying ownership unbinds it from the other bucket. For more information, see Bind a custom domain name.
ImageDamage
This error is returned when an image file is damaged and cannot be identified or processed.
The image file may be damaged
Cause: The image file is missing data or is corrupted.
Solution: Verify the integrity of the source file. If damaged, re-upload the original file from your local storage.
InvalidAccessKeyId
This error is returned when the AccessKey ID is in an incorrect format, does not exist, or is disabled.
The OSS Access Key Id contains non-acceptable characters, which accepts only alphanumeric characters[0-9a-zA-Z] and several special characters[._=]
Cause: The AccessKey ID contains unsupported characters.
Solution: Re-enter the correct AccessKey ID. Valid characters are alphanumeric
[0-9a-zA-Z]and the special characters[._=]. For more information, see Create an AccessKey pair.
The OSS Access Key Id you provided does not exist in our records
Cause: The temporary access credential (STS token) has expired, making the associated AccessKey ID invalid.
Solution: Request a new temporary access credential from the app server using a valid AccessKey pair. For more information, see Obtain a temporary access credential.
The OSS Access Key Id you provided is disabled
Cause: The AccessKey ID has been disabled.
Solution: Re-enable the AccessKey pair.
InvalidObjectState
This error is returned when an operation is not valid for the object's current state.
The operation is not valid for the object's state
Cause: Downloading an Archive object failed because of one of the following reasons:
A RestoreObject request was never submitted, or the previous RestoreObject request timed out.
A RestoreObject request was submitted, but the restore operation is not yet complete.
Solution: Submit a RestoreObject request and wait for the restore to complete before attempting the download. For more information, see RestoreObject.
InvalidSecurityToken
This error is returned when the provided STS token is invalid.
The security token you provided is invalid
Cause: The STS token is invalid.
Solution: For more information, see Use an STS token to access OSS.
InDebt
This error is returned when OSS access is blocked because the Alibaba Cloud account has an overdue payment.
Current user is indebted
Cause: OSS access is suspended because the account has an outstanding balance.
Solution: Pay the outstanding balance on your Alibaba Cloud account to restore access.
InDebtOverdue
This error is returned when an OSS payment is overdue.
Current user is indebted Overdue
Cause: An OSS payment is overdue.
Solution: Pay the overdue amount to restore access.
UbsmsInvalidBid
This error is returned when KMS is not activated on the account.
Your account partner does not have KMS Service
Cause: KMS is not activated. Server-side encryption with KMS-managed keys (SSE-KMS) requires KMS to be active.
Solution: Activate KMS before using SSE-KMS to encrypt OSS data. For more information, see Activate KMS.
NonStandardHostForbidden
This error is returned when the host used does not follow the standard OSS domain name format.
Your host is invalid. Please use Open Storage Service standard host
Cause: The request host does not match the standard OSS domain name format.
Solution: Use the standard OSS domain name format. For more information, see Access OSS over IPv6.
PermanentRedirect
This error is returned when the endpoint used to access a bucket does not match the actual endpoint of the bucket's region.
The bucket you are attempting to access must be addressed using the specified endpoint. Please send all future requests to this endpoint
Cause: The SDK request uses no endpoint or an incorrect endpoint. For example, the bucket is in the China (Qingdao) region but the request uses the default endpoint
oss-cn-hangzhou.aliyuncs.com.Solution: Use the endpoint that matches the bucket's region. For buckets in different regions, create a separate OSS client for each region with the correct endpoint. For example, use
oss-cn-hangzhou.aliyuncs.comfor China (Hangzhou) andoss-cn-qingdao.aliyuncs.comfor China (Qingdao).
RequestTimeTooSkewed
This error is returned when the request time differs from the OSS server time by more than 15 minutes.
The difference between the request time and the current time is too large
Cause: The request was sent more than 15 minutes before or after the current time on the OSS server.
Solution: Check and correct the system time on the device that sends the request. OSS uses Greenwich Mean Time (GMT), also known as Coordinated Universal Time (UTC). Make sure the device clock is synchronized with a reliable time source.
Windows: Go to Control Panel > Clock, Language, and Region > Set the time and date. The time zone displayed (for example,
+08:00) indicates the offset from UTC.Linux or Unix: Run
date -Rto view the current time and time zone. In the following example,+0800indicates UTC+8.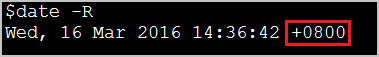
SecondLevelDomainForbidden
This error is returned when you use a second-level domain name to access OSS or the domain name format is incorrect.
Please use virtual hosted style to access
Cause: The request uses an incorrect host format instead of the required virtual-hosted style.
Solution: Use the virtual-hosted style URL format:
<Schema>://<Bucket>.<Public Endpoint>/<Object>, whereSchemaisHTTPorHTTPS,Bucketis your bucket name,Public Endpointis the endpoint for the region, andObjectis the path of the file in OSS. Example:https://examplebucket.oss-cn-hangzhou.aliyuncs.com/destfolder/example.txt
The bucket you are attempting to access must be addressed using OSS third level domain
Cause: The request domain name is not a third-level domain name containing the bucket name.
Solution: All OSS requests (except
GetService/ListBuckets) must use third-level domain names in the formatBucketName.Endpoint. Example:https://examplebucket.oss-cn-hangzhou.aliyuncs.com
SecurityTokenExpired
This error is returned when the STS token has expired.
The security token you provided has expired
Cause: The STS token's validity period has passed.
Solution: Request a new STS token from the STS service and retry the operation.
SecurityTokenNotSupported
This error is returned when an STS token is used in a region or for an operation that does not support it.
Security token is not supported in this region
Cause: The region does not support STS token authentication.
Solution: Check which regions support STS tokens. For more information, see Endpoints.
This interface does not support security token
Cause: The API operation cannot be called with STS token credentials.
Solution: STS tokens are intended for temporarily granting specific users access to OSS resources. For other authorization scenarios, see Access control overview to select an appropriate authorization method.
SignatureDoesNotMatch
This error is returned when the client's request signature does not match the signature calculated by the OSS server.
The request signature we calculated does not match the signature you provided
Cause: The signature in the request header or URL does not match the server's calculation. The request is rejected.
Solution: Follow these steps to identify the mismatch.
Verify the AccessKey ID and AccessKey secret. Log in to ossbrowser with the same credentials to confirm they are valid.
Check the signature algorithm. OSS supports two signing methods: To avoid manual signature calculation, use an Alibaba Cloud SDK. For more information, see Use an Alibaba Cloud SDK to initiate a request.
Signature in the request header:
StringToSign = VERB + "\n" + Content-MD5 + "\n" + Content-Type + "\n" + Date + "\n" + CanonicalizedOSSHeaders + CanonicalizedResource Signature = base64(hmac-sha1(AccessKeySecret, StringToSign))Signature in the URL:
StringToSign = VERB + "\n" + CONTENT-MD5 + "\n" + CONTENT-TYPE + "\n" + EXPIRES + "\n" + CanonicalizedOSSHeaders + CanonicalizedResource Signature = urlencode(base64(hmac-sha1(AccessKeySecret, StringToSign)))
Compare the
StringToSignvalues. TheStringToSignfield indicates the string-to-sign — the content that needs to be encrypted using the AccessKey secret in the signature algorithm. Compare it with the string-to-sign your client computed to find the discrepancy.Example request:
PUT /bucket/abc?acl Date: Wed, 24 May 2023 02:12:30 GMT Authorization: OSS qn6q**************:77Dv**************** x-oss-abc: mymetaExpected string-to-sign for this request:
PUT\n\n\nWed, 24 May 2023 02:12:30 GMT\nx-oss-abc:mymeta\n/bucket/abc?acl
TransferAccelerationDisabled
This error is returned when transfer acceleration is used in a region that does not support it.
Transfer acceleration is disabled
Cause: The region where the bucket is located does not support the transfer acceleration feature.
Solution: Contact technical support to resolve this issue.
UserDisable
This error is returned when the user account is disabled or the OSS service is not activated.
UserDisable
Causes:
The account has an overdue payment or is disabled for security reasons.
The OSS service is not activated on the account.
Solutions:
Check whether the account has overdue payments, or contact technical support for a security review.
Activate the OSS service.
WORMConfigurationLocked
This error is returned when attempting to delete a retention policy after it has been locked.
The WORM Configuration is locked
Cause: An attempt is made to delete a retention policy after it is locked.
Solution: After a retention policy is locked, it cannot be deleted and its retention period cannot be shortened. You can only extend the retention period. For more information, see Retention policies.