Problem description
The request is denied by the policy configured for the Security Token Service (STS) token.
Causes
The effective permissions of an STS token equal the intersection of two permission sets — not the union:
Role permissions — the permissions granted to the RAM role in Step 4 of the STS setup guide
Policy parameter permissions — the permissions specified in the
policyparameter when your code calls STS to obtain the token
If a permission exists in the role but not in the policy parameter, or vice versa, the token does not have that permission. The policy parameter can only restrict role permissions, not expand them.
Examples
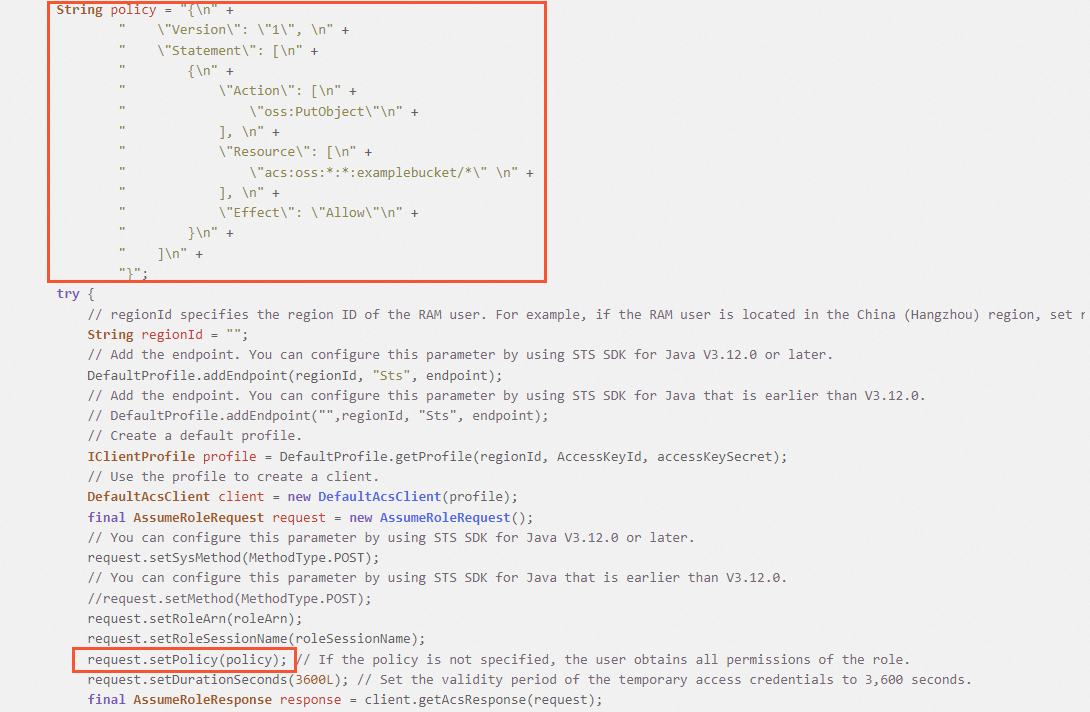
The following Java sample code shows where the policy parameter is set when calling STS.
Example 1 — token gets the expected permission
The role in Step 4 has AliyunOSSFullAccess. The policy parameter in Step 5 specifies oss:PutObject. Because oss:PutObject is within AliyunOSSFullAccess, the intersection is oss:PutObject. The temporary access credentials can upload objects to the specified bucket.
Example 2 — token gets no permissions
The role in Step 4 has only oss:PutObject. The policy parameter in Step 5 specifies oss:GetObject. The two sets do not overlap, so the intersection is empty. The temporary access credentials have no permissions and cannot perform any operations on the specified bucket.
Solutions
Check the permissions in both steps and make sure the permission you need appears in both.
Refer to Use temporary credentials provided by STS to access OSS:
Step 4: Grant the role permissions to upload objects to OSS — the role must include the permission your application needs.
Step 5: Obtain temporary access credentials — the
policyparameter must also include that same permission.