If the cloud-native gateway and the node where the backend service is deployed are in different security groups, you must add a security group authorization rule that grants the gateway access to the ports used by the backend services.
How it works
A security group is a virtual firewall that controls inbound and outbound traffic for Elastic Compute Service (ECS) instances and elastic network interfaces (ENIs). Security groups provide stateful inspection and packet filtering, allowing you to define security domains in the cloud.
When you create a cloud-native gateway, you select a VPC and a security group type. Based on your selection, the gateway creates a managed security group for its own nodes. Because the gateway nodes and the backend service nodes are in separate security groups, you must explicitly authorize the gateway to access the required ports in the backend service's security group.
Select the same security group type for the gateway as the one used by the backend service.
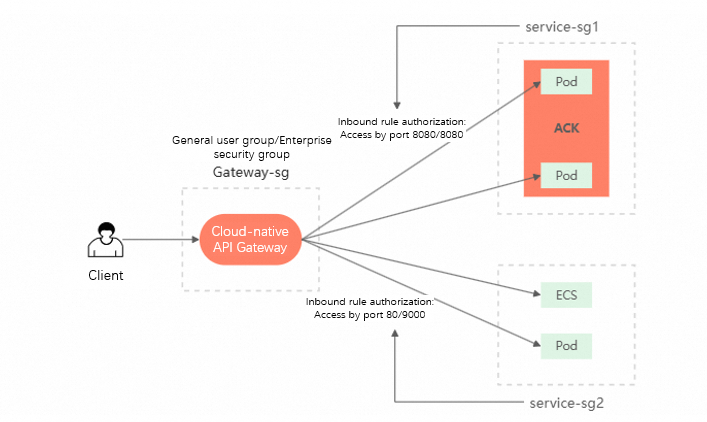
The authorization rule creates an inbound rule in the backend service's security group. This rule allows traffic from the gateway's security group on the specified port range.
| Rule property | Value |
|---|---|
| Direction | Inbound |
| Source | The gateway's managed security group |
| Port range | The ports you specify (for example, 8080/8080 or 1/65535) |
| Action | Allow |
| Purpose | Allow traffic from the cloud-native gateway to backend services |
Prerequisites
Before you begin, make sure that you have:
A cloud-native gateway in MSE
The security group ID of the node where the backend service runs (see Step 1)
Step 1: Find the security group ID of the backend service
Upstream services associated with a cloud-native gateway are typically deployed in containers or on ECS instances. Identify the security group of the node where the backend service runs. The procedure depends on the deployment type.
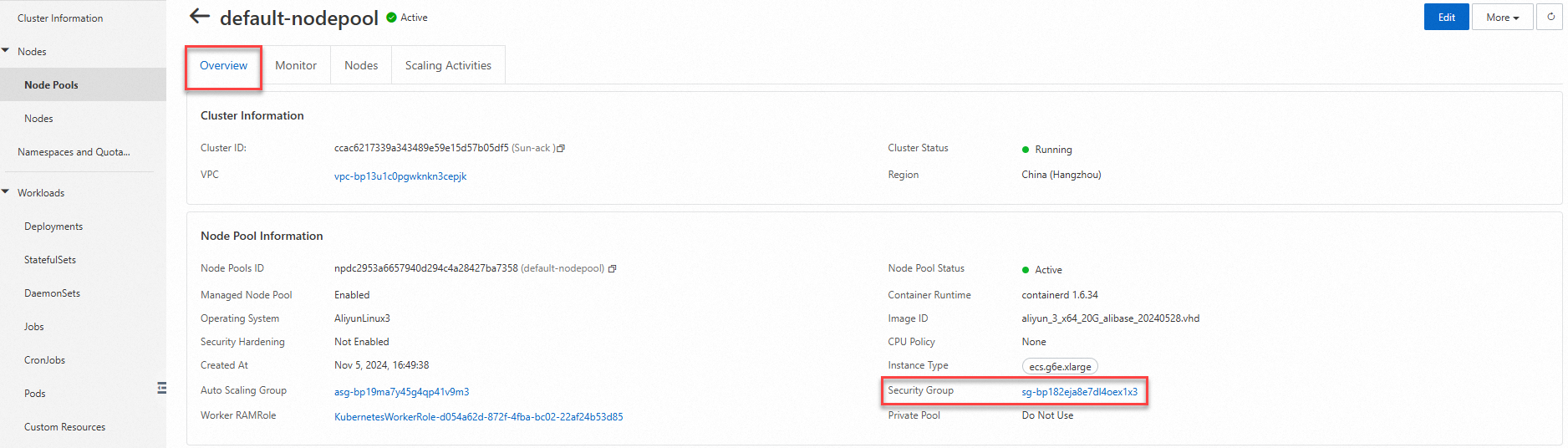
ACK managed cluster
Log on to the ACK console. In the left-side navigation pane, click Clusters.
On the Clusters page, click the name of the target cluster. In the left-side navigation pane, choose Nodes > Node Pools.
Click the target node pool and select the Basic Information tab. Note the security group ID.
ACK Serverless cluster
Log on to the ACK console. In the left-side navigation pane, click Clusters.
On the Clusters page, click the name of the target cluster. On the Basic Information tab, note the security group ID.

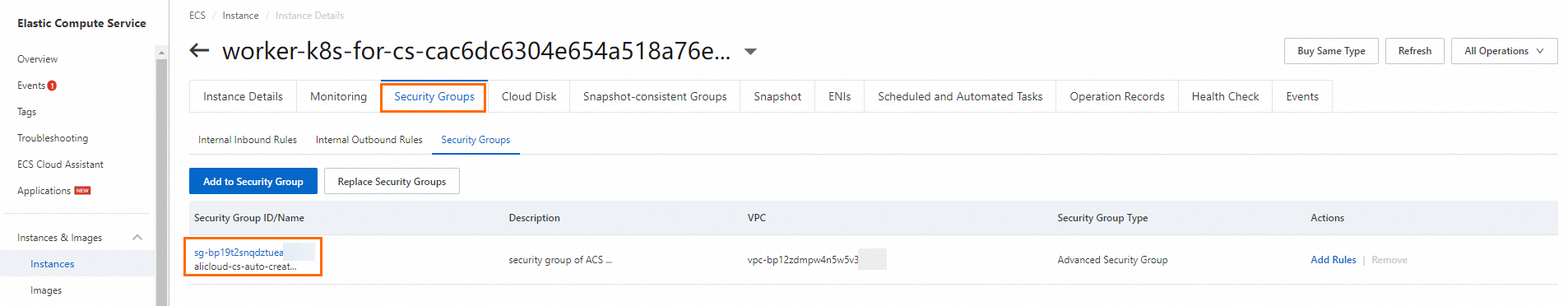
ECS instance
Log on to the ECS console. In the left-side navigation pane, choose Instances & Images > Instances.
Click the target ECS instance, then click the Security Groups tab. Note the security group ID.
Step 2: Add a security group authorization rule
Log on to the MSE console. In the left-side navigation pane, choose Cloud-native Gateway > Gateways. In the top navigation bar, select a region.
On the Gateways page, click the name of the target gateway. In the left-side navigation pane, click Overview, then select the Security Group Authorization tab.
Click Add Security Group Rule. In the Security Group ID field, paste the security group ID from Step 1 and select the security group.

In the Port Range field, enter the port range in the
Start Port/End Portformat. To add multiple port ranges, press Enter after each entry.
Click Save.
The gateway generates a corresponding inbound rule. This rule also appears in the security group of the backend service node.

Delete a security group authorization rule
Log on to the MSE console. In the left-side navigation pane, choose Cloud-native Gateway > Gateways. In the top navigation bar, select a region.
On the Gateways page, click the gateway ID.
In the left-side navigation pane, click Overview. On the Add Security Group Rule tab, find the target rule, click Delete in the Actions column, then click OK.
By default, only the security group rule for the cloud-native gateway is deleted. To also remove the corresponding inbound rule from the backend service's security group, select Cascade Delete The Preceding Inbound Rules In This Security Group.
FAQ
Why can't I access the service after adding a security group rule?
Two common causes:
Wrong node: The service runs on Node A, but you authorized Node B's security group. Verify that the service is deployed on the node whose security group you authorized.
Multiple security groups on one node: If the target node belongs to more than one security group, add an authorization rule for each security group.
Why did access stop working after it was previously successful?
Service health: Confirm the backend service is still running. Run
curlfrom another node in the same security group to test connectivity.Port change: If the service port changed (for example, from
8080to8081), update the port range in the security group authorization rule. To avoid this issue, specify a broad port range such as1/65535when you create the rule.