When requests pass through a cloud-native gateway, you may need to inject, rewrite, or strip HTTP headers before they reach backend services or before responses return to clients. A header setting policy in Microservices Engine (MSE) lets you add, modify, or delete headers on both requests and responses at the route level -- without changing application code.
Prerequisites
Before you begin, make sure that you have:
An MSE cloud-native gateway with at least one routing rule
Action type behavior
Each action type handles existing headers differently. Choose the action type based on your use case:
| Action type | Behavior | Use case |
|---|---|---|
| Add | Appends a value to the header. If a header with the same key already exists, the new value is concatenated to the existing value, separated by a comma (,). | Add a custom tracking header alongside any existing values. |
| Modify | Sets the header to the specified value. If the header does not exist, it is created. If the header already exists, the existing value is overwritten. | Force a specific Content-Type or inject a trace ID, regardless of whether the header already exists. |
| Delete | Removes the specified header from the request or response. | Strip internal authentication tokens or debug headers before forwarding to upstream services. |
Create a header setting policy
Log on to the MSE console. In the top navigation bar, select a region.
In the left-side navigation pane, choose Cloud-native Gateway > Gateways. Click the name of the gateway.
In the left-side navigation pane, click Routes, and then click the Routes tab.
Find the target routing rule and click Policies in the Actions column.
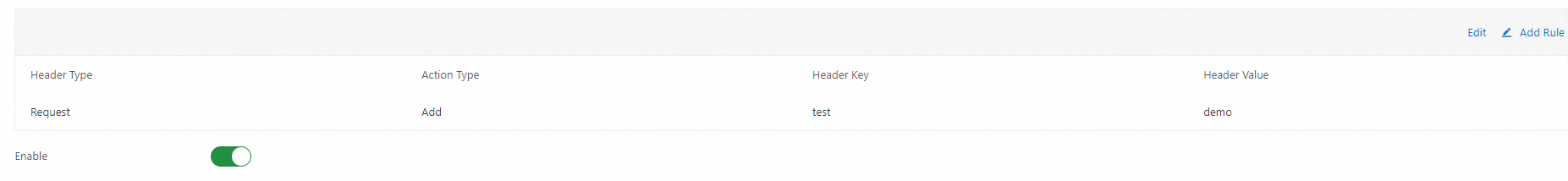
In the left-side navigation pane of the Policies tab, click Headers. On the Edit Header tab, click
 or Add Rule.
or Add Rule.Configure the following parameters and click Save in the upper-right corner.
Parameter Description Header Type Select Request to modify request headers, or Response to modify response headers. Action Type Select Add, Modify, or Delete. For detailed behavior of each action type, see Action type behavior. Header Key The header name (for example, X-Request-IDorCache-Control).Header Value The value of the header in requests or responses. Turn on the Enable toggle to activate the policy.
NoteWhen the toggle is off, the gateway does not apply any header modifications defined in this policy.
Verify the result
The following example demonstrates adding a test: demo response header.
Send a request to the gateway ingress IP address: Replace
<gateway-ingress-ip>with the actual ingress IP address of your gateway.curl -I http://<gateway-ingress-ip>/demo/item/listConfirm that the response includes the
test: demoheader: Thetest: demoline confirms that the header setting policy is working.HTTP/1.1 200 OK x-content-type-options: nosniff x-xss-protection: 1; mode=block cache-control: no-cache, no-store, max-age=0, must-revalidate pragma: no-cache expires: 0 x-frame-options: DENY content-type: application/json content-length: 86 date: Tue, 30 Nov 2021 03:03:04 GMT x-envoy-upstream-service-time: 4 test: demo server: istio-envoy
Common scenarios
The following table lists typical header manipulation scenarios and the recommended configuration for each:
| Scenario | Header Type | Action Type | Header Key | Header Value |
|---|---|---|---|---|
| Add a CORS header to responses | Response | Modify | Access-Control-Allow-Origin | * |
| Inject a trace ID into requests | Request | Modify | X-Request-ID | <trace-id> |
| Strip an internal header before forwarding | Request | Delete | X-Internal-Debug | -- |
| Append a routing tag to requests | Request | Add | X-Route-Tag | canary |