Microservices Engine (MSE) cloud-native gateways use Resource Access Management (RAM) for access control. Instead of sharing your Alibaba Cloud account credentials, create RAM users for team members and grant each user only the permissions they need.
This topic describes how to create a RAM user and assign gateway permissions through system or custom policies.
Permission model
MSE cloud-native gateways support two authorization levels:
| Level | Scope | Use case |
|---|---|---|
| Coarse-grained | Full access or read-only access to all MSE resources | Quick setup for small teams |
| Fine-grained | Specific actions on specific gateway instances | Production environments that require least-privilege access |
A typical team maps these levels to two roles:
| Role | Responsibilities | Recommended policy |
|---|---|---|
| O&M engineer | Cluster management, permission management, resource provisioning | AliyunMSEFullAccess (system policy) |
| Developer | Configuration and service management | AliyunMSEReadOnlyAccess (system policy), or a custom policy for fine-grained control |
Resource usage and costs are billed to the Alibaba Cloud account, not to individual RAM users.
Prerequisites
Before you begin, make sure that you have:
An Alibaba Cloud account or a RAM user who has administrative rights
Access to the RAM console
Step 1: Create a RAM user
Log on to the RAM console by using an Alibaba Cloud account or a RAM user who has administrative rights.
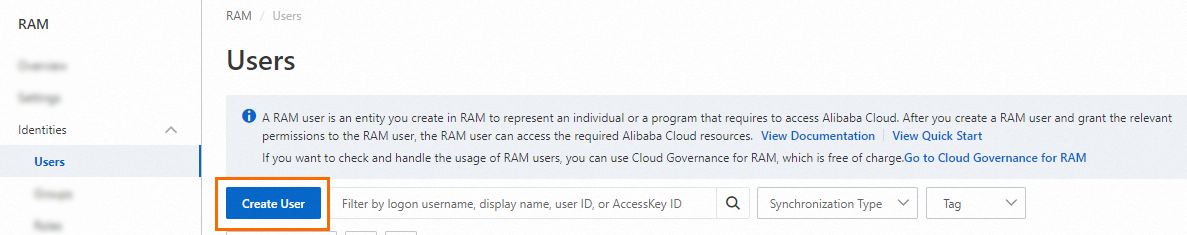
In the left-side navigation pane, choose Identities > Users.
On the Users page, click Create User.
In the User Account Information section, configure the following parameters:
NoteClick Add User to create multiple RAM users at a time.
Parameter Description Logon Name Up to 64 characters. Supports letters, digits, periods (.), hyphens (-), and underscores (_). Display Name Up to 128 characters. Tag Click the  icon, then enter a tag key and value. Tags help you organize and manage RAM users.
icon, then enter a tag key and value. Tags help you organize and manage RAM users.In the Access Mode section, select an access mode:
Console Access -- The RAM user logs on to the Alibaba Cloud console. Configure the logon password, password reset policy, and multi-factor authentication (MFA) settings as needed.
NoteIf you set the logon password to a custom password, it must meet the complexity requirements defined under Identities > Settings. For details, see Configure a password policy for RAM users.
Using permanent AccessKey to access -- An AccessKey pair is automatically created. The RAM user can call API operations or use development tools to access Alibaba Cloud resources.
NoteFor security, select only one access mode per RAM user. This way, when an employee leaves the organization, revoking console access also prevents programmatic access.
Click OK.
Step 2: Grant permissions to the RAM user
Log on to the RAM console as a RAM administrator.
In the left-side navigation pane, choose Identities > Users.
Find the target RAM user and click Add Permissions in the Actions column.
NoteTo grant permissions to multiple RAM users at once, select them and click Add Permissions at the bottom of the page.

In the Grant Permission panel, search for and select one or more policies, then click Grant permissions. Policies are classified into system policies and custom policies. See the following sections for details.
Confirm that authorization is successful and click Close.
System policies (coarse-grained authorization)
| Policy | Description |
|---|---|
AliyunMSEFullAccess | Full permissions to manage MSE. The RAM user can perform all operations in the MSE console, equivalent to using the Alibaba Cloud account. |
AliyunMSEReadOnlyAccess | Read-only permissions for MSE. The RAM user can read all resources of the Alibaba Cloud account. |
Custom policies (fine-grained authorization)
Custom policies restrict access to specific gateway instances and actions. To create a custom policy, see Create a custom policy.
Resource format
Custom policies use the following Alibaba Cloud Resource Name (ARN) format to identify gateway instances:
acs:mse:<region>:<account-id>:instance/<gateway-id>| Field | Description | Example |
|---|---|---|
<region> | Region ID, or * for all regions | cn-hangzhou, * |
<account-id> | Alibaba Cloud account ID, or * for any account | * |
<gateway-id> | Gateway instance ID | gw-8090caa2a3ab447a8bc5fdf3******** |
Use acs:mse:*:*:* to match all MSE resources across all regions.
Policy statement structure
Each custom policy contains one or more statements. Each statement specifies which actions are allowed or denied on which resources.
| Field | Description |
|---|---|
Action | The MSE API actions to allow or deny. Wildcards are supported: mse:Get* matches all actions that start with Get. |
Resource | The gateway instances to which the statement applies. Use the ARN format above for instance-scoped actions, or acs:mse:*:*:* for actions that are not instance-scoped. |
Effect | Allow or Deny. |
Example: Read-only access to a specific gateway
The following policy grants a RAM user read-only access to the gateway gw-8090caa2a3ab447a8bc5fdf3********. The user can view gateway configurations, routes, and services but cannot make changes.
{
"Version": "1",
"Statement": [
{
"Action": [
"mse:Query*",
"mse:List*",
"mse:Get*",
"mse:Select*",
"mse:Pull*",
"mse:GatewayBlackWhite*",
"mse:GatewayHealthCheckList",
"mse:GatewayQueryMonitor",
"mse:UploadWasmFile"
],
"Resource": "acs:mse:*:*:instance/gw-8090caa2a3ab447a8bc5fdf3********",
"Effect": "Allow"
},
{
"Action": [
"mse:QueryDefaultAlertStatus",
"mse:ListGatewayZone",
"mse:ListUpgradableGatewayVersions",
"mse:ListTagResources",
"mse:ListGatewayIngressMigrateTask",
"mse:ListEventRecords",
"mse:GetEventFilterOptions",
"mse:GetEventDetail",
"mse:GetGatewaySelection",
"mse:GetGatewayAlarms",
"mse:GetGatewayMigrateNamespacedServices",
"mse:GetGatewayIngressMigrateTaskDetail",
"mse:GetPluginGuide",
"mse:GetRegExpCheck",
"mse:GetRegExpTest",
"mse:CheckPluginLua"
],
"Resource": "acs:mse:*:*:*",
"Effect": "Allow"
},
{
"Action": [
"log:DescribeService",
"log:ListProject",
"log:GetProductDataCollection"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"arms:SearchContactGroup"
],
"Resource": "*",
"Effect": "Allow"
}
]
}How this policy works:
| Statement | Scope | Purpose |
|---|---|---|
| 1st | Specific gateway instance | Grants read actions (Query, List, Get, Select, Pull) on the target gateway only. |
| 2nd | All MSE resources (acs:mse:*:*:*) | Grants global read actions that are not instance-scoped, such as listing zones and checking upgrade versions. |
| 3rd | All resources (*) | Grants read access to Simple Log Service for monitoring features. |
| 4th | All resources (*) | Grants read access to Application Real-Time Monitoring Service (ARMS) for alerting features. |
Example: Read-write access to a specific gateway
The following policy grants a RAM user full management access to the gateway gw-8090caa2a3ab447a8bc5fdf3********. The user can create, modify, and delete routes, services, and configurations on this gateway.
{
"Version": "1",
"Statement": [
{
"Action": [
"mse:*"
],
"Resource": "acs:mse:*:*:instance/gw-8090caa2a3ab447a8bc5fdf3********",
"Effect": "Allow"
},
{
"Action": [
"mse:QueryDefaultAlertStatus",
"mse:CreateDefaultAlert",
"mse:ListGatewayZone",
"mse:ListUpgradableGatewayVersions",
"mse:ListEventRecords",
"mse:GetEventFilterOptions",
"mse:GetEventDetail",
"mse:GetGatewaySelection",
"mse:GetGatewayAlarms",
"mse:GetGatewayMigrateNamespacedServices",
"mse:GetPluginGuide",
"mse:GetRegExpCheck",
"mse:GetRegExpTest",
"mse:CheckPluginLua",
"mse:*TagResources",
"mse:*CustomPlugin",
"mse:*GatewayIngressMigrateTask*"
],
"Resource": "acs:mse:*:*:*",
"Effect": "Allow"
},
{
"Action": [
"log:DescribeService",
"log:ListProject",
"log:GetProductDataCollection",
"log:OpenProductDataCollection"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"arms:SearchContactGroup"
],
"Resource": "*",
"Effect": "Allow"
}
]
}Differences from the read-only policy:
| Difference | Read-only | Read-write |
|---|---|---|
| Gateway instance actions | mse:Query*, mse:List*, mse:Get*, and other read actions | mse:* (all actions, including create, update, and delete) |
| Global actions | Read-only global actions | Adds mse:CreateDefaultAlert, tag management (mse:*TagResources), custom plugin management (mse:*CustomPlugin), and ingress migration tasks (mse:*GatewayIngressMigrateTask*) |
| Log service | Read-only (log:DescribeService, log:ListProject, log:GetProductDataCollection) | Adds log:OpenProductDataCollection to enable log collection |
What to do next
Share the RAM user credentials with team members. They can access MSE in two ways:
Log on to the console
Go to the RAM User Logon page.
Enter the RAM user logon name and click Next, then enter the password and click Log On.
NoteThe logon name follows the format
<$username>@<$AccountAlias>or<$username>@<$AccountAlias>.onaliyun.com. If no account alias is set, the Alibaba Cloud account ID is used by default.On the RAM user center page, click the target service to open its console.
Call API operations
Use the RAM user's AccessKey pair (AccessKey ID and AccessKey secret) in your code to authenticate API requests.
API-to-policy action reference
Use the following tables to identify the actions to include in custom policies.
Gateway management
| Action | Description | Read-only |
|---|---|---|
| AddGateway | Create a pay-as-you-go cloud-native gateway | No |
| ListGateway | List gateway clusters | Yes |
| GetGatewayDetail | Get cloud-native gateway details | Yes |
| GetGateway | Get cloud-native gateway information | Yes |
| ListGatewaySlb | List Server Load Balancer (SLB) instances of a gateway | Yes |
| SelectGatewaySlb | Query existing SLB instances | No |
| AddGatewaySlb | Associate an SLB instance with a gateway | No |
| DeleteGatewaySlb | Disassociate an SLB instance from a gateway | No |
| DeleteGateway | Delete a pay-as-you-go cloud-native gateway | No |
Service source management
| Action | Description | Read-only |
|---|---|---|
| ListServiceSource | List service sources | Yes |
| GetKubernetesSource | Query existing Container Service for Kubernetes (ACK) clusters | Yes |
| GetMseSource | Query existing MSE registries | Yes |
| AddServiceSource | Add a service source | No |
| DeleteServiceSource | Remove a service source | No |
| PullServices | List existing services | Yes |
| ImportServices | Create or import services | No |
| ListGatewayService | List subscribed services | Yes |
| GetGatewayServiceDetail | Get service details | Yes |
| AddGatewayServiceVersion | Add a service version | No |
| UpdateGatewayServiceVersion | Update a service version | No |
| DeleteGatewayServiceVersion | Remove a service version | No |
| UpdateGatewayServiceTrafficPolicy | Update the load balancing policy of a service | No |
Route management
| Action | Description | Read-only |
|---|---|---|
| ListGatewayRoute | List routes | Yes |
| AddGatewayRoute | Create a route | No |
| ApplyGatewayRoute | Publish a route | No |
| OfflineGatewayRoute | Disable a route | No |
| DeleteGatewayRoute | Delete a route | No |
| GetGatewayRouteDetail | Get route details | Yes |
| GetRateLimit | Get throttling rules for a route | Yes |
| AddRateLimit | Add a throttling rule to a route | No |
| UpdateRateLimit | Delete a throttling rule from a route | No |
| UpdateGatewayRouteHTTPRewrite | Update the rewrite policy of a route | No |
| UpdateGatewayRouteHeaderOp | Update the header settings of a route | No |
| UpdateGatewayRouteCORS | Update the cross-origin resource sharing (CORS) policy of a route | No |
| UpdateGatewayRouteTimeout | Update the timeout policy of a route | No |
| UpdateGatewayRouteRetry | Update the retry policy of a route | No |
Certificate and domain name management
| Action | Description | Read-only |
|---|---|---|
| ListGatewayDomain | List associated domain names | Yes |
| AddGatewayDomain | Associate a domain name | No |
| GetGatewayDomainDetail | Get domain name details | Yes |
| UpdateGatewayDomain | Update associated domain name information | No |
| DeleteGatewayDomain | Disassociate a domain name | No |
| ListSSLCert | List existing certificates | Yes |
| AddSSLCert | Associate a certificate with a domain name | No |
| UpdateSSLCert | Update the certificate of a domain name | Yes |
Other operations
| Action | Description | Read-only |
|---|---|---|
| GetBlackWhiteList | Get IP addresses in the blacklist and whitelist | Yes |
| AddBlackWhiteList | Add an IP address to the blacklist or whitelist | No |
| UpdateBlackWhiteList | Update the blacklist and whitelist | No |
| AddGatewayAuth | Add an authentication method | No |
| ListGatewayAuth | List authentication methods | Yes |
| UpdateGatewayAuth | Update an authentication method | No |
| DeleteGatewayAuth | Remove an authentication method | No |
| AddAuthResource | Add an authentication URL | No |
| DeleteAuthResource | Delete an authentication URL | No |