Instead of sharing your Alibaba Cloud account credentials, create Resource Access Management (RAM) users and grant them specific permissions on Microservices Engine (MSE) resources. This approach eliminates the security risk of exposing your AccessKey pair while giving each team member only the access they need.
When to use RAM for MSE
RAM-based access control applies when your organization needs to:
Keep the Alibaba Cloud account credentials confidential and avoid sharing them across teams
Assign different permission levels to different roles, such as developers and O&M personnel
Revoke permissions or delete RAM users when team members change roles or leave the organization
All resource usage and costs are billed to the Alibaba Cloud account, regardless of which RAM user performs the operations.
MSE is a managed service that provides two roles: developer and O&M. Developers are responsible for configuration and service management. O&M personnel are responsible for instance, namespace, and permission management.
Access paths
MSE provides two access paths, as shown in the following figure.
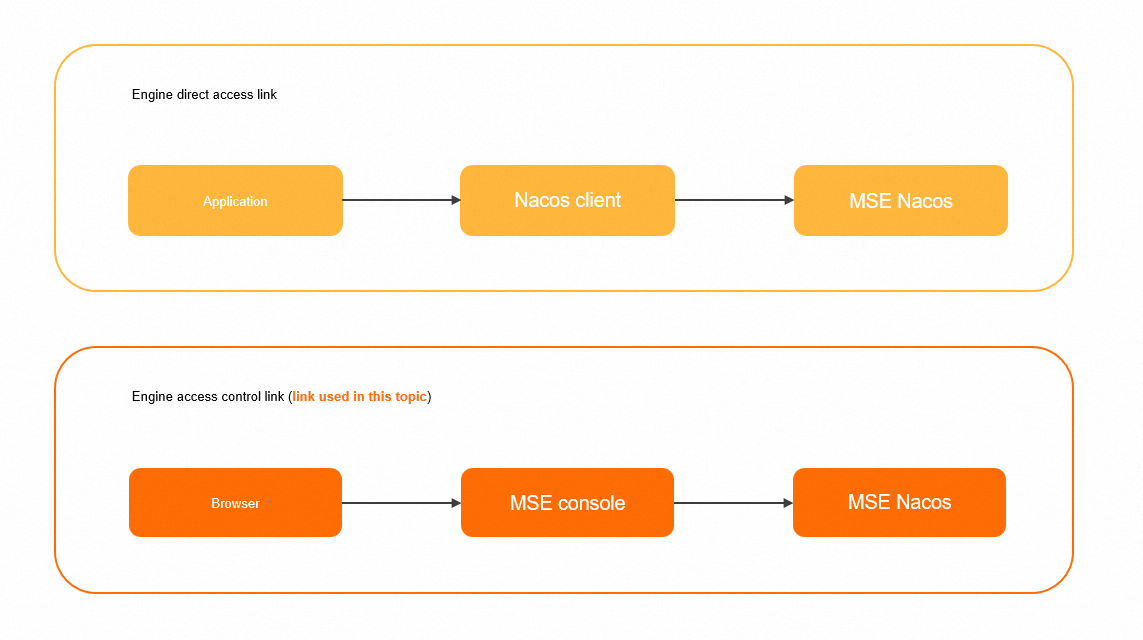
Engine access control link: Access MSE in Console Access mode or OpenAPI Access mode. The rest of this document covers permissions for this path.
Engine direct access link: Access an MSE Nacos instance directly through the Nacos client. For details, see Access authentication by the Nacos client.
Prerequisites
Before you begin, make sure that you have:
An Alibaba Cloud account or a RAM user with administrative rights
MSE activated for your account
Step 1: Create a RAM user
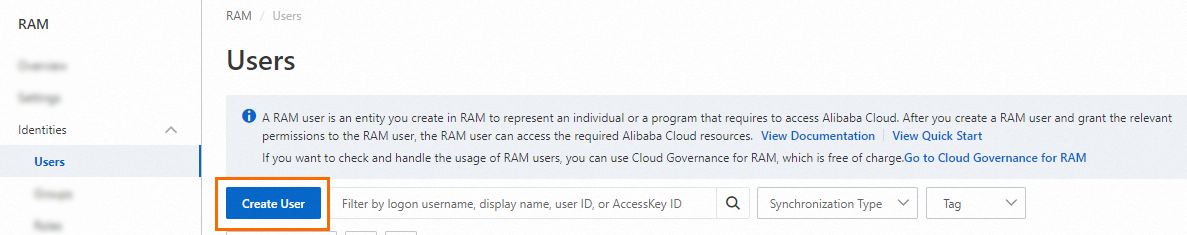
Log on to the RAM console.
In the left-side navigation pane, choose Identities > Users.
On the Users page, click Create User.
In the User Account Information section, configure the following parameters:
Logon Name: Up to 64 characters. Supports letters, digits, periods (.), hyphens (-), and underscores (_).
Display Name: Up to 128 characters.
Tag: Click the
 icon to add one or more tags (key-value pairs) for managing the RAM user.
icon to add one or more tags (key-value pairs) for managing the RAM user.
NoteClick Add User to create multiple RAM users at a time.
In the Access Mode section, select an access mode:
Console Access: The RAM user logs on to the Alibaba Cloud console. Configure a logon password (system-generated or custom), and optionally require a password reset on first logon or enable multi-factor authentication (MFA).
NoteCustom passwords must meet the complexity requirements configured under Identities > Settings. For details, see Configure a password policy for RAM users.
Using permanent AccessKey to access: Automatically creates an AccessKey pair for the RAM user to call API operations or use development tools.
NoteFor better security, select Console Access. This way, the RAM user can no longer use an AccessKey pair to access Alibaba Cloud resources after the RAM user leaves the organization.
Click OK.
Step 2: Grant permissions to the RAM user
Log on to the RAM console as a RAM administrator.
In the left-side navigation pane, choose Identities > Users.
Find the target RAM user and click Add Permissions in the Actions column. To grant permissions to multiple RAM users at once, select the users and click Add Permissions at the bottom of the page.

In the Grant Permission panel, search for and select a policy based on your requirements, then click Grant permissions. See the following sections for policy options.
System policies for coarse-grained authorization
Start with system policies for quick setup, then move to custom policies as your access control requirements become more specific.
MSE provides two system policies:
| Policy | Description |
|---|---|
| AliyunMSEFullAccess | Full access to all MSE features. Attach this policy to O&M personnel who need to create, modify, and delete resources. |
| AliyunMSEReadOnlyAccess | Read-only access to all MSE resources. Attach this policy to developers who need to view resources but should not create or delete them. |
For finer control over developer permissions, create a custom policy.
Custom policies for fine-grained authorization
Create custom RAM policies to control access at the instance, namespace, group, or individual resource level.
For more information about fine-grained authorization for Nacos registries and configuration centers, see:
Available actions
The following tables list all MSE actions that you can use in custom policies.
Instance-level actions (can be scoped to specific instances):
| Action | Description | Read-only |
|---|---|---|
| CreateCluster | Create an instance | No |
| DeleteCluster | Delete an instance | No |
| QueryClusterDetail | Query instance details | Yes |
| RestartCluster | Restart an instance | No |
| RetryCluster | Retry an instance | No |
| UpdateCluster | Update an instance | No |
| CreateNacosConfig | Create a Nacos configuration | No |
| DeleteNacosConfig | Delete a Nacos configuration | No |
| DeleteNacosConfigs | Batch delete Nacos configurations | No |
| GetNacosConfig | View a Nacos configuration | Yes |
| GetNacosHistoryConfig | View Nacos configuration history | Yes |
| UpdateNacosConfig | Update a Nacos configuration | No |
| UpdateNacosInstance | Update a Nacos instance | No |
| DeleteNacosService | Delete a Nacos service | No |
| CreateNacosService | Create a Nacos service | No |
| UpdateNacosService | Update a Nacos service | No |
| CreateNacosInstance | Create a Nacos instance | No |
| UpdateNacosCluster | Update a Nacos cluster | No |
Account-level actions (cannot be scoped to specific instances):
| Action | Description | Read-only |
|---|---|---|
| ListClusters | List all instances | Yes |
| ListServiceQuotas | Query quotas (recommended to grant) | Yes |
Instance-level actions (no fine-grained display support):
| Action | Description | Read-only |
|---|---|---|
| ListNacosConfigs | List Nacos configurations | Yes |
| ListNacosHistoryConfigs | List Nacos configuration history | Yes |
| ListAnsServices | List all services | Yes |
| ListAnsServiceClusters | List clusters of a service | Yes |
| ListAnsInstances | List instances of a service | Yes |
Resource ARN format
All custom policies use the following resource ARN format:
acs:mse:*:*:instance/${instanceId}/${namespaceId}/${groupId}/${dataId|serviceName}The ARN supports hierarchical scoping. You can scope permissions at different granularity levels:
| Scope level | ARN example |
|---|---|
| All resources | acs:mse:*:*:* |
| Specific instance | acs:mse:*:*:instance/mse-cn-0pp1j8om80a |
| Specific namespace | acs:mse:*:*:instance/mse-cn-0pp1j8om80a/3fd98c48-... |
| Specific group + DataId | acs:mse:*:*:instance/mse-cn-0pp1j8om80a/3fd98c48-.../DEFAULT_GROUP/prod.yaml |
| Specific group + service | acs:mse:*:*:instance/mse-cn-0pp1j8om80a/3fd98c48-.../DEFAULT_GROUP/test-service |
Use the InstanceId (not ClusterId) as the instance identifier in the ARN.
Policy examples
Example 1: Full access to a specific instance
Grant read and write access to instance mse-cn-0pp1j8om80a:
{
"Statement": [
{
"Action": "mse:ListClusters",
"Resource": "acs:mse:*:*:*",
"Effect": "Allow"
},
{
"Action": "mse:*",
"Resource": "acs:mse:*:*:instance/mse-cn-0pp1j8om80a",
"Effect": "Allow"
}
],
"Version": "1"
}Example 2: Read-only access to all instances
{
"Statement": [
{
"Action": [
"mse:List*",
"mse:Query*",
"mse:Get*"
],
"Resource": "acs:mse:*:*:*",
"Effect": "Allow"
}
],
"Version": "1"
}Example 3: Read and write access to a specific namespace
Grant read and write access to configurations in namespace 3fd98c48-a709-4061-bba1-e341d79d681b within instance mse-cn-0pp1j8om80a. This requires three levels of permissions:
List instances (account-level) -- so the RAM user can see the instance list.
Read all resources in the instance -- so the RAM user can access the instance and browse its resources.
Create and modify configurations in the target namespace.
{
"Version": "1",
"Statement": [
{
"Action": ["mse:ListClusters"],
"Resource": ["acs:mse:*:*:*"],
"Effect": "Allow"
},
{
"Action": [
"mse:List*",
"mse:Query*",
"mse:Get*"
],
"Resource": ["acs:mse:*:*:instance/mse-cn-0pp1j8om8"],
"Effect": "Allow"
},
{
"Action": [
"mse:CreateNacosConfig",
"mse:UpdateNacosConfig"
],
"Resource": ["acs:mse:*:*:instance/mse-cn-0pp1j8om8/3fd98c48-a709-4061-bba1-e341d79d681b"],
"Effect": "Allow"
}
]
}Example 4: Read and write access to a specific DataId
Grant read and write access to the configuration prod.yaml in group DEFAULT_GROUP under namespace 3fd98c48-a709-4061-bba1-e341d79d681b in instance mse-cn-0pp1j8om80a.
Resource ARN format: acs:mse:*:*:instance/${instanceId}/${namespaceId}/${groupId}/${dataId}
{
"Version": "1",
"Statement": [
{
"Action": ["mse:ListClusters"],
"Resource": ["acs:mse:*:*:*"],
"Effect": "Allow"
},
{
"Action": [
"mse:List*",
"mse:Query*",
"mse:Get*"
],
"Resource": ["acs:mse:*:*:instance/mse-cn-0pp1j8om8"],
"Effect": "Allow"
},
{
"Action": [
"mse:CreateNacosConfig",
"mse:UpdateNacosConfig"
],
"Resource": ["acs:mse:*:*:instance/mse-cn-0pp1j8om8/3fd98c48-a709-4061-bba1-e341d79d681b/DEFAULT_GROUP/prod.yaml"],
"Effect": "Allow"
}
]
}Example 5: Read and write access to a specific service
Grant read and write access to service test-service in group DEFAULT_GROUP under namespace 3fd98c48-a709-4061-bba1-e341d79d681b in instance mse-cn-0pp1j8om80a.
Resource ARN format: acs:mse:*:*:instance/${instanceId}/${namespaceId}/${groupId}/${serviceName}
{
"Version": "1",
"Statement": [
{
"Action": ["mse:ListClusters"],
"Resource": ["acs:mse:*:*:*"],
"Effect": "Allow"
},
{
"Action": [
"mse:List*",
"mse:Query*",
"mse:Get*"
],
"Resource": ["acs:mse:*:*:instance/mse-cn-0pp1j8om8"],
"Effect": "Allow"
},
{
"Action": [
"mse:CreateNacosConfig",
"mse:UpdateNacosConfig"
],
"Resource": ["acs:mse:*:*:instance/mse-cn-0pp1j8om8/3fd98c48-a709-4061-bba1-e341d79d681b/DEFAULT_GROUP/test-service"],
"Effect": "Allow"
}
]
}In the Grant Permission panel, confirm that the authorization is successful and click Close.
What to do next
Share the logon credentials or AccessKey pair with the team member who will use the RAM user account.
Log on to the MSE console
Go to the RAM User Logon page.
Enter the RAM user logon name and click Next, then enter the password and click Log On.
NoteThe logon name follows the format
<$username>@<$AccountAlias>or<$username>@<$AccountAlias>.onaliyun.com. If no account alias is set, the Alibaba Cloud account ID is used by default.From the RAM user center page, navigate to the MSE console.
Call API operations
Use the RAM user's AccessKey ID and AccessKey secret in your code to authenticate API calls.