Data Management (DMS) lets you manage database accounts for ApsaraDB for MongoDB through a graphical interface or the command-line interface (CLI). Use the graphical interface to create, edit, and delete accounts without writing commands. Use the CLI when you need scripted or shell-based account management.
Prerequisites
Before you begin, make sure that:
Your DMS account has the administrator, database administrator (DBA), or instance owner role. For more information, see System roles.
The database account name you plan to create is unique within the target database.
Use the user management feature
The user management feature in the DMS console lets you create, edit, and delete database accounts without writing any commands.
Create a database account
Log on to the DMS console V5.0.
Log on to the MongoDB database. For more information, see Log on to a database instance.
ImportantIf your instance is a replica set instance, log on to the primary node.
In the left-side navigation pane, right-click the instance and select Account Management.
Click Create a database account in the upper-left corner.
Configure the account parameters.
Parameter Required Description Example Destination database Yes The database for which you want to create the account. Setting this to admincreates a privileged account; any other value creates a regular account.adminDatabase account Yes The username. Cannot contain Chinese characters. Allowed characters: letters, digits, and ! # $ % ^ & * ( ) _ + - =.dbuser01Password Yes The login password. Use 8–32 characters with at least three of the following types: English letters (case-sensitive), digits, and special characters ( ! # $ % ^ & * ( ) _ + - =).MyP@ssw0rdConfirm password Yes Re-enter the password to confirm. 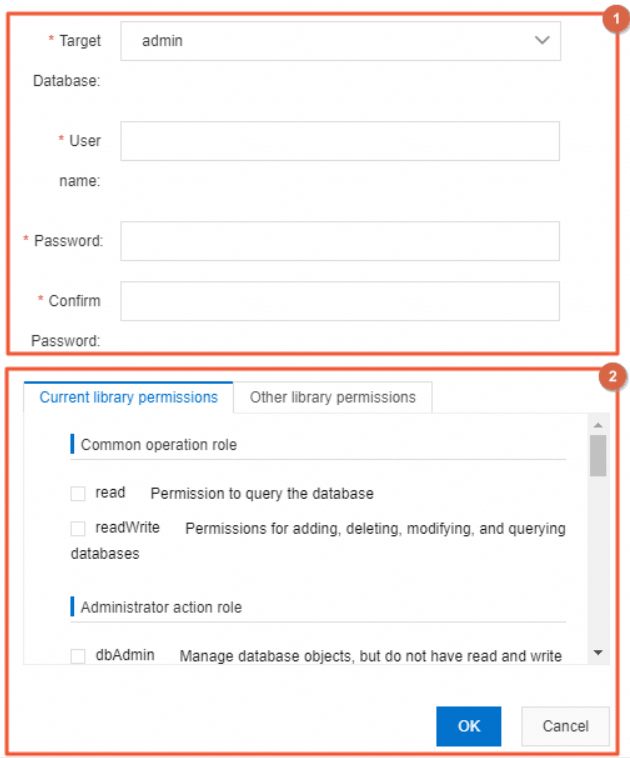
Grant permissions to the account. For a description of available roles and their permissions, see Role permissions.
Click OK.
DMS generates SQL statements from your configuration. In Security Collaboration mode, these statements may fail due to security rules. If that happens, follow the on-screen instructions or contact your DBA or DMS administrator.
Edit or delete an account
Log on to the DMS console V5.0.
In the left-side instance list, right-click the instance and select Database Accounts.
On the Database Accounts page, find the account you want to manage.
Click Edit or Delete in the Actions column.
Use the CLI
Connect to your instance through DMS. The connection method depends on your instance architecture:
After connecting, use the mongo shell to manage accounts:
Create an account: See Create a database account.
Query accounts: See Query database accounts.
Role permissions
The following table lists the built-in MongoDB roles available when granting permissions to a database account. For the full specification, see the MongoDB documentation.
Permissions apply at two levels:
Database-level roles (common operation, administrator action): apply to a specific database.
Instance-level and cluster roles: apply across all databases or the entire cluster.
| Role type | Role | Permissions |
|---|---|---|
| Common operation roles | read | Query data in the database. |
readWrite | Insert, delete, update, and query data in the database. | |
| Administrator action roles | dbAdmin | Manage data in the database, but not read or write data. |
userAdmin | Create users for the database. | |
dbOwner | Perform all operations on the database. | |
| Instance-level roles | readAnyDatabase | Query data in all databases of the instance. |
readWriteAnyDatabase | Insert, delete, update, and query data in all databases of the instance. | |
userAdminAnyDatabase | Create users for all databases of the instance. | |
dbAdminAnyDatabase | Manage data in all databases of the instance. | |
| Cluster administrator roles | hostManager | Manage data in the database, but not read or write data. |
clusterMonitor | Query clusters and replica sets. | |
clusterManager | Manage and monitor clusters and replica sets. | |
clusterAdmin | Perform all operations on clusters. | |
| Backup and recovery roles | backup | Query data in all databases of the instance. |
restore | Insert, delete, update, and query data in all databases of the instance. | |
| Super role | Root | Perform all operations on all resources in the instance. |
FAQ
Why is a newly created account not visible on the Database Accounts page?
The Database Accounts page shows accounts for the currently selected database only. Switch to the database you selected as the Destination database when creating the account — the account will appear there.