MaxCompute allows you to grant permissions to RAM accounts (RAM users and RAM roles) by assigning roles in the console. This topic describes how to grant different types of permissions and provides examples.
Grant project-level administrative permissions
Project-level administrative permissions in MaxCompute include managing project security settings, project-level users and roles, packages, label-based access control, and revoking expired permissions. For more information, see Project management permissions.
Procedure
Log on to the MaxCompute console, and select a region in the upper-left corner.
In the navigation pane on the left, choose .
On the Projects page, find the target project and click Manage in the Actions column.
On the Project Settings page, select the Role Permissions tab.
On the Role Permissions tab, you can create an administrator (Admin) role or modify the permissions of an existing administrator (Admin) role.
NoteBy default, only an Alibaba Cloud account has the permissions to manage roles in a project. To grant permissions by using a RAM account (a RAM user or RAM role), it must have administrative permissions for the project.
Create an administrator (Admin) role
Click Create Project-level Role to create a project-level role with MaxCompute permissions.
In the Create Role dialog box, configure the role information as prompted and click OK.
For Role Type, select Admin and specify a policy.
Modify the permissions of an existing administrator (Admin) role
On the Role Permissions tab, find the target role and click Modify Authorization in the Actions column. After you modify the policy, click Confirm to save the changes.
For more information about the values of Action and Resource, see Project management permissions. This topic provides policy examples for different management modules.
Find the target project-level role and click Manage Members in the Actions column. In the Manage Members dialog box, you can view role members, assign the role to users, or remove users from the role.
Policy examples
Administrative permissions for a module typically involve various actions and permissions on different resources. The examples use a wildcard (
*) to grant permissions to multiple objects in a single statement.For more information about Action and Resource, see Project management permissions.
Replace
project_namein the examples with the name of your MaxCompute project.
Role management
The following policy grants permissions to manage roles.
{
"Statement": [
{
"Action": [
"odps:*"
],
"Effect": "Allow",
"Resource": [
"acs:odps:*:projects/project_name/authorization/roles",
"acs:odps:*:projects/project_name/authorization/roles/*/*"
]
}
],
"Version": "1"
}Package management
The following policy grants permissions to manage packages.
{
"Statement": [
{
"Action": [
"odps:*"
],
"Effect": "Allow",
"Resource": [
"acs:odps:*:projects/project_name/authorization/packages",
"acs:odps:*:projects/project_name/authorization/packages/*",
"acs:odps:*:projects/project_name/authorization/packages/*/*/*"
]
}
],
"Version": "1"
}Managing Packages in the console requires the list permission for the Project. Therefore, you must first grant the user the list permission for the current Project. To grant this permission by using the console, see Granting project-level object operation permissions. To grant this permission by using the command line, see Managing user permissions by using commands.
Project security configurations
The following policy grants permissions to modify project security configurations.
{
"Statement":[
{
"Action":[
"odps:*"
],
"Effect":"Allow",
"Resource":[
"acs:odps:*:projects/project_name/authorization/configurations/*"
]
}
],
"Version":"1"
}Project user management
The following policy grants permissions to manage project users.
{
"Statement":[
{
"Action":[
"odps:*"
],
"Effect":"Allow",
"Resource":[
"acs:odps:*:projects/project_name/authorization/users"
]
}
],
"Version":"1"
}All administrative permissions
The following policy grants all administrative permissions.
{
"Statement":[
{
"Action":[
"odps:*"
],
"Effect":"Allow",
"Resource":[
"acs:odps:*:projects/project_name/authorization/*"
]
}
],
"Version":"1"
}Grant project-level object operation permissions
Project-level object operation permissions apply to operations on projects and the objects within them, such as tables, functions, and resources. Examples of operations include CreateTable, CreateInstance, and SelectTable. For more information, see Permissions on projects and objects in projects.
Procedure
Log on to the MaxCompute console, and select a region in the upper-left corner.
In the navigation pane on the left, choose .
On the Projects page, find the target project and click Manage in the Actions column.
On the Project Settings page, select the Role Permissions tab.
You can create a Resource role or modify the permissions of an existing Resource role.
NoteBy default, only an Alibaba Cloud account has the permissions to manage roles in a project. To grant permissions by using a RAM account (a RAM user or RAM role), it must have administrative permissions for the project.
Create a Resource role
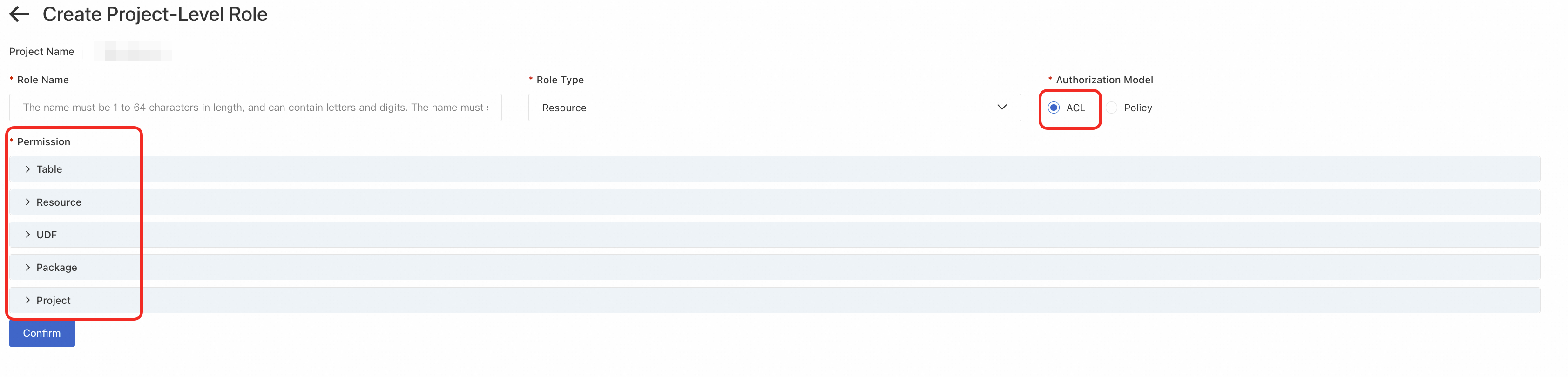
Click Create Project-level Role to create a project-level role with MaxCompute permissions.
In the Create Role dialog box, configure the role information as prompted and click OK.
For Role Type, select Resource, and then configure permissions by using an ACL or a policy.
Modify the permissions of an existing Resource role
On the Role Permissions tab, find the target role and click Modify Authorization in the Actions column. Then, modify the ACL or policy permissions.
For more information about the permissions, see Permissions on projects and objects in projects. This topic provides examples of granting permissions by using an ACL and a policy in the console. For more information, see Grant project-level administrative permissions.
Find the target project-level role and click Manage Members in the Actions column. In the Manage Members dialog box, you can view the members of the role, assign the role to users, or remove users from the role.
Authorization examples
For more information about the Actions and Objects for project-level object operation permissions, see Permissions on projects and objects in projects.
Replace
project_namein the examples with the name of your MaxCompute project.
Authorization by ACL
You can use an ACL to grant a Resource role the permissions to create tables (CreateTable), create instances (CreateInstance), view a list of all object types in a project (List), read the metadata of all tables (Describe), and read table data (Select). The following figure shows an example.
Do not close the progress bar or the page while granting permissions, or the process may be interrupted.
Authorization by policy
The following policy grants a Resource role the permissions to create tables (CreateTable), create instances (CreateInstance), and view a list of all object types in a project (List), as well as the permissions to read the metadata of all tables (Describe) and read table data (Select).
{ "Statement": [{ "Action": ["odps:CreateTable","odps:CreateInstance","odps:List"], "Effect": "Allow", "Resource": ["acs:odps:*:projects/project_name"]}, { "Action": ["odps:Describe","odps:Select"], "Effect": "Allow", "Resource": ["acs:odps:*:projects/project_name/tables/*"]}], "Version": "1"}The following policy grants a Resource role the permissions to read metadata (Describe) and query data (Select) for all tables whose names start with tmp. It also grants the permissions to read and update all resources and functions, but denies the permission to delete any table.
{ "Statement": [{ "Action": ["odps:Describe","odps:Select"], "Effect": "Allow", "Resource": ["acs:odps:*:projects/project_name/tables/tmp_*"]}, { "Action": ["odps:Read","odps:Write"], "Effect": "Allow", "Resource": ["acs:odps:*:projects/project_name/resources/*"]}, { "Action": ["odps:Read","odps:Write"], "Effect": "Allow", "Resource": ["acs:odps:*:projects/project_name/functions/*"]}, { "Action": ["odps:Drop"], "Effect": "Deny", "Resource": ["acs:odps:*:projects/project_name/tables/*"]}], "Version": "1"}If data storage by schema is enabled for the project (Schema operations), you must modify the policy as follows:
{ "Statement": [{ "Action": ["odps:Describe","odps:Select"], "Effect": "Allow", "Resource": ["acs:odps:*:projects/project_name/schemas/*/tables/tmp_*"]}, { "Action": ["odps:Read","odps:Write"], "Effect": "Allow", "Resource": ["acs:odps:*:projects/project_name/schemas/*/resources/*"]}, { "Action": ["odps:Read","odps:Write"], "Effect": "Allow", "Resource": ["acs:odps:*:projects/project_name/schemas/*/functions/*"]}, { "Action": ["odps:Drop"], "Effect": "Deny", "Resource": ["acs:odps:*:projects/project_name/schemas/*/tables/*"]}], "Version": "1"}
Grant tenant-level administrative permissions
Tenant-level administrative permissions are for managing tenant-level users and role permissions. These permissions include adding or removing tenant users, creating or deleting tenant-level roles, viewing tenant-level users and roles and their permissions, assigning tenant-level roles to users, revoking tenant-level roles from users, adding tenant-level roles to projects, and removing tenant-level roles from projects.
Only an Alibaba Cloud account or a user with the tenant-level Super_Administrator or Admin role can manage tenant-level permissions.
To grant administrative permissions to a RAM account (a RAM user or RAM role), an Alibaba Cloud account must assign the Super_Administrator or Admin role to the RAM account. The tenant-level Super_Administrator and Admin roles have extensive management permissions. Use them with caution. For more information about these permissions, see Role planning. For more information about tenant-level roles, see Grant permissions to tenant-level roles.
Log on to the MaxCompute console, and select a region in the upper-left corner.
In the navigation pane on the left, choose .
On the Tenants page, click the Users tab.
On the Users tab, click Modify Role in the Actions column for the target Resource Access Management (RAM) user.
In the Edit Role dialog box, select the roles to assign to the user from the Available Roles area, move them to the Added Roles area, and then click OK.
Grant tenant-level object operation permissions
Tenant-level object operation permissions include permissions to operate on tenant-level objects such as quotas and network connections (Networklink). Examples include use quota and CreateNetworkLink. These permissions also allow a single account to manage objects across multiple projects, which simplifies permission management. For more information about tenant-level roles, see Grant permissions to tenant-level roles.
Procedure
Log on to the MaxCompute console, and select a region in the upper-left corner.
In the navigation pane on the left, choose .
On the Tenants page, click the Roles tab.
On the Roles page, you can create a new tenant-level role or manage the permissions of an existing custom role.
NoteOnly an Alibaba Cloud account or a user with the tenant-level Super_Administrator or Admin role can manage tenant-level permissions.
Add a tenant-level role
On the Roles tab, click Add Role. In the Add Role dialog box, enter a Role Name and Policy Content, and then click OK to create the role.
Parameter
Description
Role Name
The name of the tenant-level role. The name must be unique within your Alibaba Cloud account. It must be 6 to 64 characters long, start with a letter, and contain only letters, digits, and underscores (_).
Policy Content
The permission policy for the role. You can edit the policy code directly in the UI based on a policy template.
Modify the permissions of an existing tenant-level role
On the Roles tab, find the target role and click Manage Permissions in the Actions column. Modify the policy document and click OK to save the changes.
On the Users tab, find the user to whom you want to grant permissions and click Modify Role in the Actions column.
In the Edit Role dialog box, select the roles to assign to the user from the Available Roles area, move them to the Added Roles area, and then click OK.
Policy examples
The examples use a wildcard (
*) to grant permissions to a group of objects with a single statement.For more information about the specific Actions and Resources, see Permissions on objects in a tenant.
Example 1: Grant a tenant-level role the
Usagepermission on all quotas in all regions, and theCreateNetworkLink,List, andExecutepermissions on all networklinks.{ "Statement":[ { "Action":[ "odps:Usage" ], "Effect":"Allow", "Resource":[ "acs:odps:*:regions/*/quotas/*" ] }, { "Action":[ "odps:CreateNetworkLink", "odps:List", "odps:Execute" ], "Effect":"Allow", "Resource":[ "acs:odps:*:networklinks/*" ] } ], "Version":"1" }Example 2: Grant a tenant-level role all operation permissions on MaxCompute projects
project_1andproject_2.{ "Statement":[ { "Action":[ "odps:*" ], "Effect":"Allow", "Resource":[ "acs:odps:*:projects/project_1", "acs:odps:*:projects/project_1/*", "acs:odps:*:projects/project_2", "acs:odps:*:projects/project_2/*" ] } ], "Version":"1" }NoteAfter you grant permissions on project objects by using a tenant-level role, you must add the role to the project for the permissions to take effect. The project owner or a user with the project-level Super_Administrator or Admin role can perform this action. On the Role Permissions tab, for Role Level, select Tenant. Find the target role and click Enable in the Actions column.