A service-linked role (SLR) is a RAM role whose trusted entity is an Alibaba Cloud service. SLRs are used for cross-service authorization. If you need Hologres to access other services, such as MaxCompute or DLF, you must create the AliyunServiceRoleForHologresIdentityMgmt service-linked role. This topic describes how to create, authorize, view, and delete the AliyunServiceRoleForHologresIdentityMgmt role.
For more information about service-linked roles, see Service-linked Role.
AliyunServiceRoleForHologresIdentityMgmt overview
Role description
-
Service name: identity.hologres.aliyuncs.com.
-
Role name: AliyunServiceRoleForHologresIdentityMgmt.
-
Role purpose: Hologres uses this role to access your MaxCompute resources.
Create and authorize the AliyunServiceRoleForHologresIdentityMgmt role
You can create and authorize the AliyunServiceRoleForHologresIdentityMgmt role using different methods for new and existing instances.
To create the AliyunServiceRoleForHologresIdentityMgmt role using a RAM user, the RAM user must have the CreateServiceLinkedRole permission. For more information, see Permissions required to create a service-linked role.
New instance
On the Hologres instance purchase page, click Create Service-linked Role to grant permissions.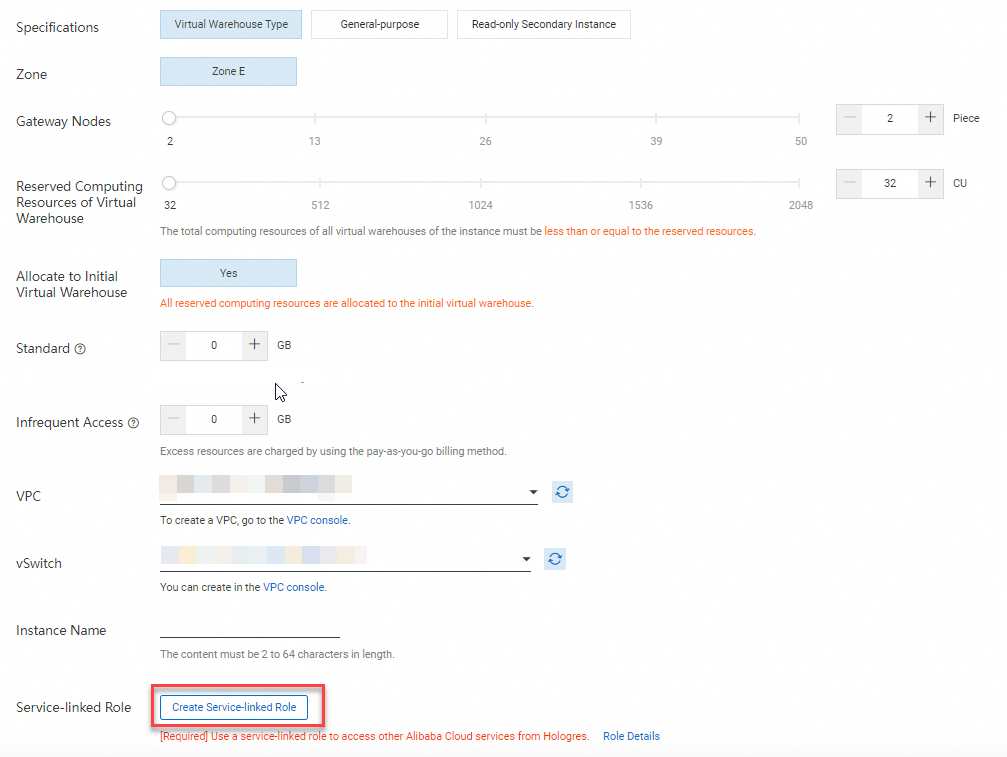
Existing instance
If you do not need to purchase or upgrade an instance, you can create and authorize the service-linked role using the Resource Access Management console or OpenAPI.
-
After you log on to the Hologres Management Console, click Authorize Service-linked Role to complete the authorization.
-
Create and authorize using OpenAPI
-
Go to OpenAPI.
-
In Parameter Settings, set ServiceName to identity.hologres.aliyuncs.com.
-
Click Invoke.
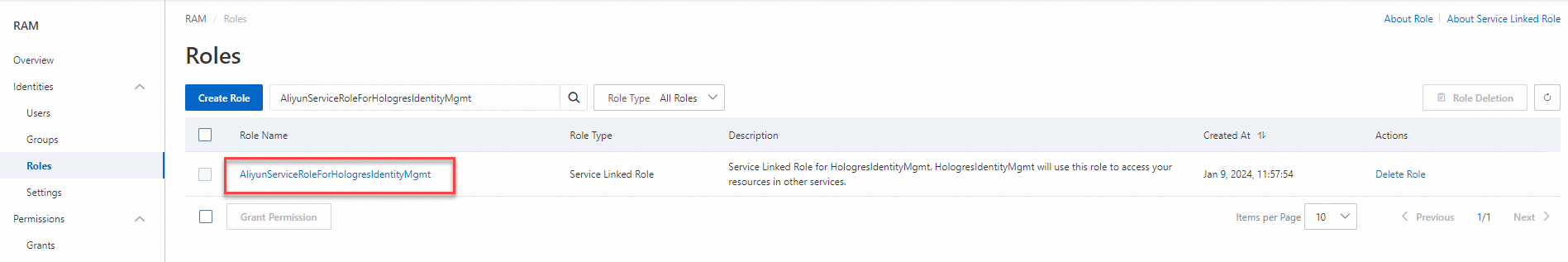
After the call is successful, you can view the role in the RAM console.
-
View the service-linked role
To view the permission details of an existing AliyunServiceRoleForHologresIdentityMgmt service-linked role, perform the following steps.
-
Log on to the Resource Access Management (RAM) console using your Alibaba Cloud account (root account) or as a RAM administrator.
-
In the navigation pane on the left, choose Identity Management > Role.
-
On the Role page, search for AliyunServiceRoleForHologresIdentityMgmt and click the role name.
-
On the Access Control tab, click the access policy that is attached to the role.
-
On the Policy Content tab, view the permission description.
NoteYou can only view the access policy of the AliyunServiceRoleForHologresIdentityMgmt service-linked role. You cannot modify it.
Delete the service-linked role
To prevent Hologres from accessing MaxCompute, you can manually delete the AliyunServiceRoleForHologresIdentityMgmt role in the Resource Access Management (RAM) console. This action stops cross-service access by Hologres. For the specific steps, see Delete a RAM role.
-
Deleting the AliyunServiceRoleForHologresIdentityMgmt service-linked role also revokes its authorization.
-
To delete the AliyunServiceRoleForHologresIdentityMgmt role using a RAM user, the RAM user must have the DeleteServiceLinkedRole permission. For more information, see Permissions required to delete a service-linked role.
FAQ
-
Issue 1: When you click Create Service-linked Role on the Hologres new instance purchase page, the following message is displayed: "The current logged-on user does not have permission to create a service-linked role. Contact the root account or permission administrator to grant permissions to the current user."
Solution: Use your Alibaba Cloud account (root account) to grant the CreateServiceLinkedRole permission to the RAM user. For more information, see Service-linked Role.
-
Issue 2: When you access a MaxCompute foreign table in Hologres, you might encounter one of the following errors:
-
Error 1:
ERROR: Fail to access foreign data as user 1063806044629636, AliyunServiceRoleForHologresIdentityMgmt does not exist. -
Error 2:
ErrorMessage=ODPS-0420095: Access Denied - Authorization Failed [4111], You have NO privilege 'odps:ActOnBehalfOfAnotherUser' on {acs:odps:regions_id:xxxxxx:users/default/aliyun/xxxxxx. Not pass by ram permission check.
Solution: Re-authorize the AliyunServiceRoleForHologresIdentityMgmt service-linked role. For more information, see the authorization method for existing instances in Create and authorize the AliyunServiceRoleForHologresIdentityMgmt role.
-