To let team members collaborate on a Flink project — developing jobs, running Operations and Maintenance (O&M), or viewing results — add them as members and assign a role. This topic explains the role types, common permission issues, and the authorization procedure.
How to use this topic
| You are... | Go to... |
|---|---|
| A project owner or admin who needs to add team members | Authorization procedure |
| A member who cannot access a project | Authorization scenarios |
| Someone deciding which role to assign | Role types |
| Looking up what a role can do | Fine-grained permission list |
Authorization scenarios
If you encounter a permission error in the development console, identify which scenario applies:
| Scenario | Interface | What it means and what to do |
|---|---|---|
| Cannot access the current project |  |
Your account has no access to this project. Ask a member with the owner role or a user with member management permissions to assign you the viewer role or higher. After the permission is granted, refresh the page or access it again. |
| Cannot use a specific feature or operation | Your role lacks the permission for this action. Ask a member with the owner role or a user with role management permissions to update your custom role's permissions. |
Role types
A role is a collection of permissions. The development console provides two types: system roles and custom roles.
| Role type | Description | Constraints |
|---|---|---|
| System role | Three built-in roles: owner, editor, and viewer. For a full comparison, see Fine-grained permission list. | Cannot be modified or deleted. For permissions outside the fine-grained list — such as metadata management or UDF management in SQL development — assign the editor or owner role. |
| Custom role | Create when system roles do not meet your fine-grained authorization needs. Extend permissions from the viewer or editor baseline. | Must include all viewer permissions. Only owner-role members or users with role management permissions can create, edit, or delete custom roles. Maximum 10 custom roles per project. Some permissions have dependencies — the system selects these automatically. |
Prerequisites
Before you begin, ensure that you have read the Authorization instructions.
Authorization procedure
Step 1 (optional): Create a custom role
Skip this step if a system role (owner, editor, or viewer) meets your needs.
-
Log in to the development console as a member with the owner role or role management permissions.
-
At the top of the page, select the target project.
-
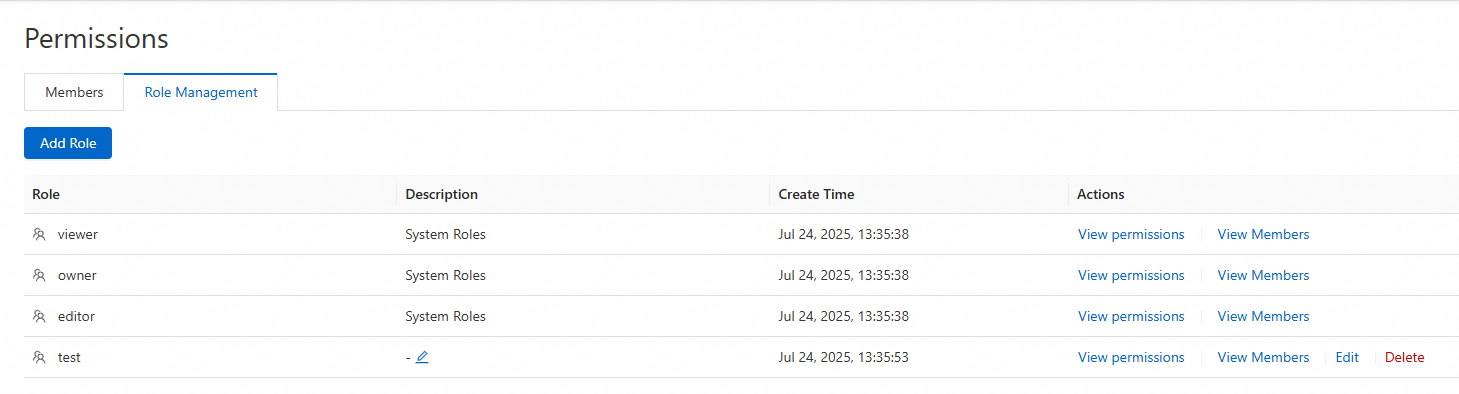
In the left navigation pane, go to Security > Permission Management, then click the Role Management tab.
-
Click Add Role and fill in the fields.
Parameter Description Role Name Must start with a letter. Can contain letters, digits, and hyphens (-). Maximum 64 characters. Role Description Describes the role's purpose and permission scope. Maximum 256 characters. Role Permissions Select the permissions for this role. Some permissions have dependencies — the system automatically selects required dependencies. For details, see Fine-grained permission list. -
Click OK. The new role appears in the list. From the Actions column, you can:
-
View Permissions — see all permissions assigned to the role.
-
View Members — see which members have this role.
-
Edit Permissions — add or remove permissions (requires role editing permissions).
-
Delete Custom Role — remove all members from the role or reassign them first, then delete it (requires role deletion permissions).
-
Step 2: Attach a role to a member
-
Log in to the development console as a member with the owner role or member creation permissions.
-
At the top of the page, select the target project.
-
In the left navigation pane, go to Security > Permission Management, then click the Member Management tab.
-
Click Add Member, select an account, and assign a Role.
Field Details Select RAM account Lists the Resource Access Management (RAM) users and RAM roles under the Alibaba Cloud account for this project. Select one or more. Add account manually Enter an Alibaba Cloud account ID, RAM user ID (UID), or RAM role ID directly. To find these IDs: Account ID — click your profile picture in the upper-right corner, then go to Account Center > Security Settings > Account ID. RAM user UID — see View the information about a RAM user. RAM role ID — see View the information about a RAM role. Role Select a system role or a custom role. To preview a role's permissions, go to Role Management and click View Permissions in the Actions column. 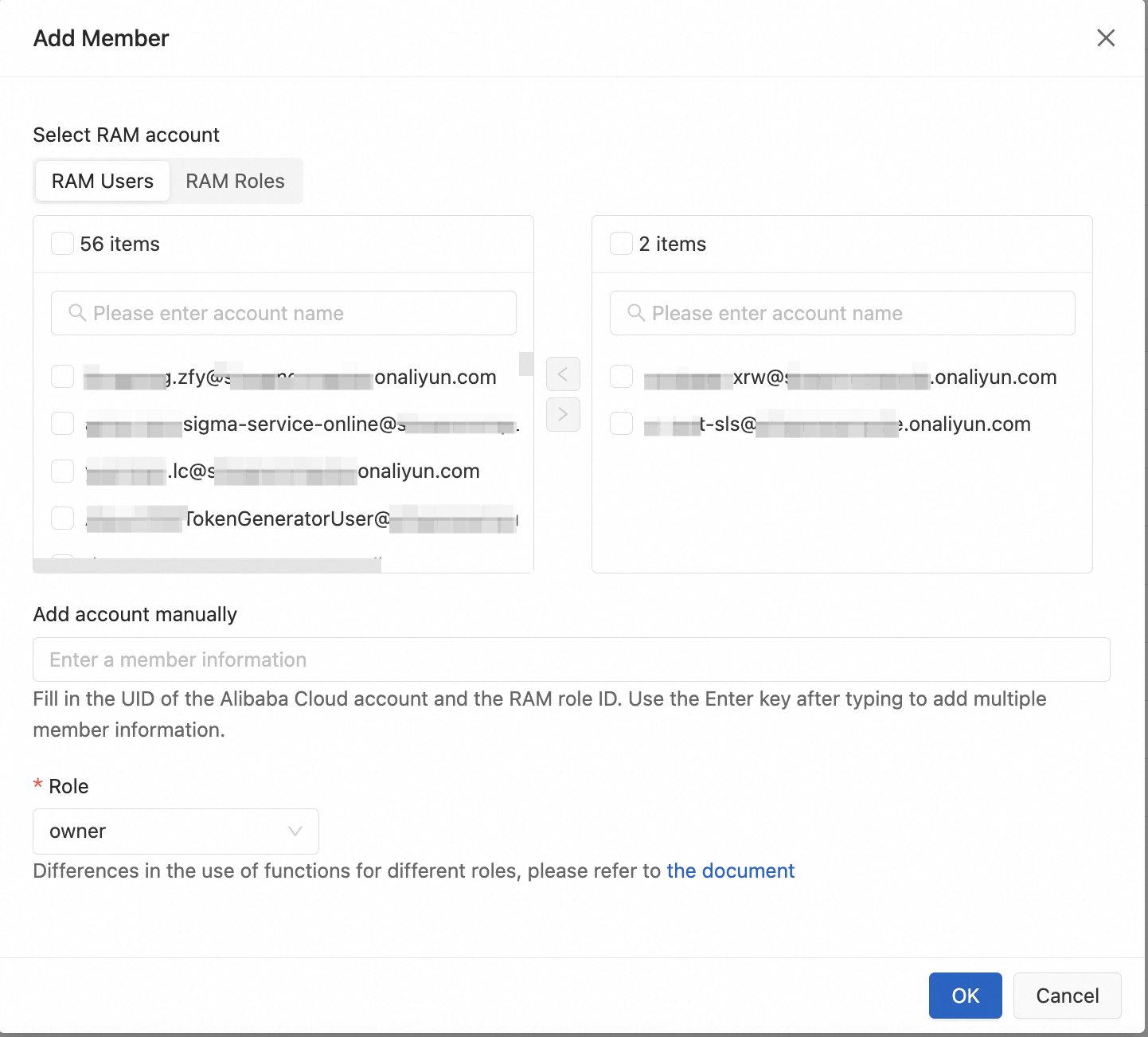
-
Click OK.
Step 3: Access the console after authorization
After authorization is complete, the new member can use the development console.
-
Already logged in: Refresh the page to access the project.
-
Not yet logged in: Access the project directly using the project URL.
Fine-grained permission list
The table below shows what each system role can do. Use this as a reference when choosing between system roles or designing custom roles.
| Category | Permission | owner | editor | viewer |
|---|---|---|---|---|
| ETL/Data ingestion | View list of SQL/YAML job drafts | √ | √ | √ |
| Develop SQL/YAML job drafts (create, edit) | √ | √ | ||
| Debug SQL job drafts | √ | √ | ||
| Deep check SQL/YAML job drafts | √ | √ | ||
| Delete SQL/YAML job drafts | √ | √ | ||
| Deploy SQL/YAML job drafts | √ | √ | ||
| Data query | View data query scripts | √ | √ | √ |
| Edit data query scripts (create, edit, delete) | √ | √ | ||
| Execute data query scripts | √ | √ | ||
| Job O&M | View list of O&M deployments | √ | √ | √ |
| Deploy JAR and Python jobs | √ | √ | ||
| Update O&M deployment configuration | √ | √ | ||
| Delete O&M deployments | √ | √ | ||
| Start/Stop job instances | √ | √ | ||
| Data management | View materialized tables | √ | √ | √ |
| View metadata | √ | √ | √ | |
| View tables | √ | √ | √ | |
| Create materialized tables | √ | √ | ||
| Create catalogs | √ | √ | ||
| Create tables | √ | √ | ||
| Delete materialized tables | √ | √ | ||
| Delete catalogs | √ | √ | ||
| Delete tables | √ | √ | ||
| Edit materialized tables | √ | √ | ||
| File management | View resources | √ | √ | √ |
| Upload resources | √ | √ | ||
| Delete resources | √ | √ | ||
| Download resources | √ | √ | ||
| Session management | View session clusters | √ | √ | √ |
| Create session clusters | √ | √ | ||
| Update session cluster configuration | √ | √ | ||
| Start/Stop session clusters | √ | √ | ||
| Delete session clusters | √ | √ | ||
| Security Center | View member list | √ | √ | √ |
| View role list | √ | √ | √ | |
| View variable list | √ | √ | √ | |
| Create members | √ | √ | ||
| Create variables | √ | √ | ||
| Delete variables | √ | √ | ||
| Edit members | √ | |||
| Delete members | √ | |||
| Create roles | √ | |||
| Edit roles | √ | |||
| Delete roles | √ | |||
| Configuration management | View job templates | √ | √ | √ |
| Edit job templates | √ | √ | ||
| Git configuration | Pull code changes | √ | √ | |
| Push code changes | √ | √ | ||
| Attach Git repository | √ | |||
| Detach Git repository | √ |
What's next
If you use a RAM user or RAM role to access the Realtime Compute for Apache Flink management console for operations such as purchasing, viewing, or deleting workspaces, grant the required management console permissions. For details, see Management Console Authorization.