X-Pack's role-based access control (RBAC) lets you restrict access to clusters, indexes, and fields by assigning privileges to roles and assigning roles to users. This topic walks you through creating a custom role, creating a user, assigning the role to the user, and verifying that the permissions work as expected.
How RBAC works
RBAC organizes access control around three core objects:
| Object | Description |
|---|---|
| Role | A named set of privileges. A role can grant cluster-level, index-level, and Kibana-level access. |
| Privilege | A specific action or group of actions a user can perform on a secured resource — for example, read on an index or monitor on a cluster. |
| User | An account that logs in to Kibana or calls Elasticsearch APIs. A user inherits all privileges from their assigned roles. |
For background, see User authorization and Identity authentication and authorization in Elasticsearch.
Before you begin
These instructions cover V6.7 and V7.X clusters. Steps may differ for other versions. When in doubt, follow the actual console interface.
Kibana privilege model by version:
| Kibana version | Supported privilege types |
|---|---|
| Earlier than V7.0 | Base privileges only. A base privilege grants access to all Kibana spaces. |
| V7.0 and later | Base privileges and feature privileges. A feature privilege grants access to a specific feature and requires a Kibana space. |
The Kibana privilege version differences described above apply to all scenarios in this topic. Each scenario's role configuration table lists the privilege value to use; refer to this table to determine whether that privilege is a base privilege or a feature privilege for your Kibana version.
Create a role and assign it to a user
Step 1: Create a role
Log on to the Kibana console. For details, see Log on to the Kibana console.
Go to the configuration management page:
V6.7: In the left-side navigation pane, click Management.
V7.X: Click the
 icon in the upper-left corner and choose Management > Stack Management.
icon in the upper-left corner and choose Management > Stack Management.
In the Security section, click Roles.
Click Create role and configure the following parameters.
Parameter Description Role name The name of the role. Cluster privileges Permissions on the cluster, such as viewing health status and settings, or creating snapshots. For available values, see Cluster privileges. Run As privileges (Optional) The user who assumes this role. If left blank, assign the role when you create the user. Index privileges — Indices The index pattern (full name, alias, wildcard, or regular expression). If no index patterns exist, go to Management > Kibana > Index Pattern to create one. For pattern syntax, see Indices privileges. Index privileges — Privileges The permissions to grant on the matched indexes. Index privileges — Granted fields (optional) The fields on which to grant permissions. Kibana privileges Permissions on Kibana. See the version table in Before you begin for the supported privilege types. 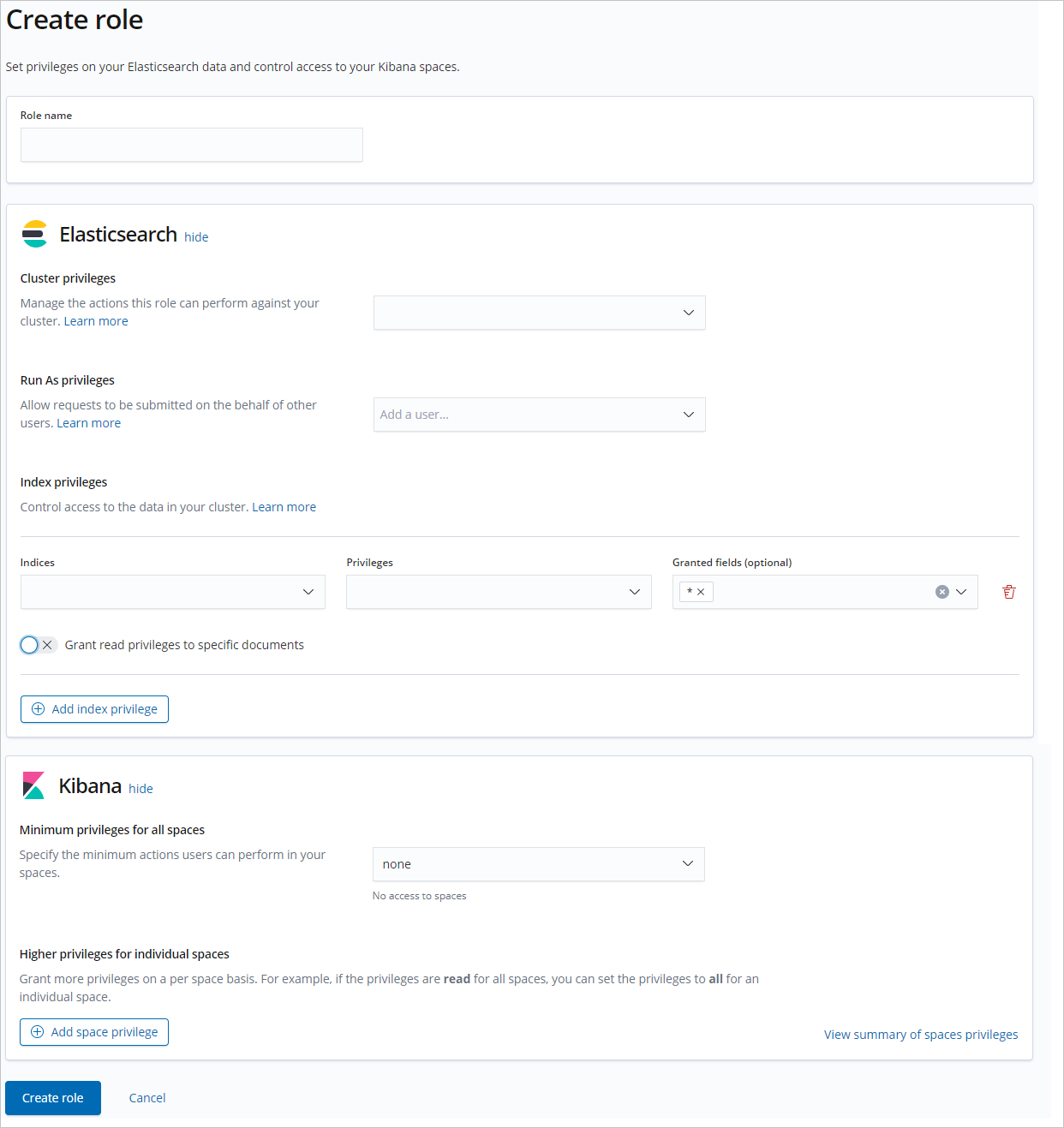
Click Create role.
Step 2: Create a user and assign the role
Go to the configuration management page (same path as Step 1).
In the Security section, click Users.
In the upper-right corner, click Create new user and configure the following parameters.
Parameter Description Username The username for logging on to the Kibana console. Password The password for logging on to the Kibana console. Confirm password Must match the Password value. Full name The full name of the user. Email address The email address of the user. Roles One or more roles (built-in or custom) to assign. ImportantAlways fill in this field, even if you specified a user when creating the role. Omitting it causes a login error.
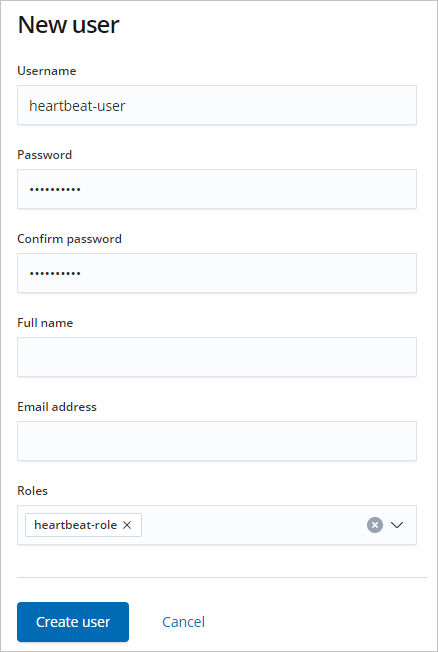
Click Create user.
Step 3: Verify
Log on to the Kibana console as the new user and perform operations to confirm the permissions are in effect.
Permission scenarios
The following sections show five common permission configurations. Each section describes the goal, the role settings, and how to verify the result.
Read-only access to an index
Goal: The user can query data from a specific index in Kibana but cannot write to it or access cluster-level APIs.
Role configuration:
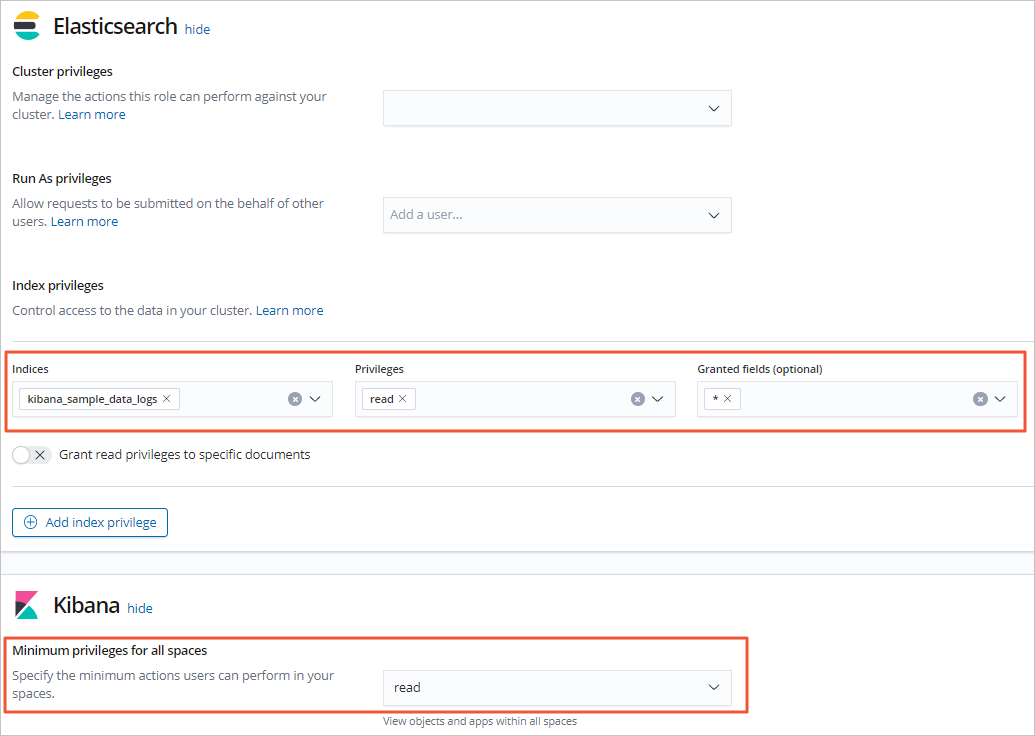
| Permission type | Key | Value | Description |
|---|---|---|---|
| Index privileges | Indices | kibana_sample_data_logs | The target index. Accepts full name, alias, wildcard, or regular expression. |
| Privileges | read | Grants access to the count, explain, get, mget, scripts, search, and scroll APIs. See privileges-list-indices. | |
| Granted fields (optional) | * | All fields. | |
| Kibana privileges | Privileges | read | Read-only access to all Kibana spaces. Default is none (no Kibana access). |
Verify:
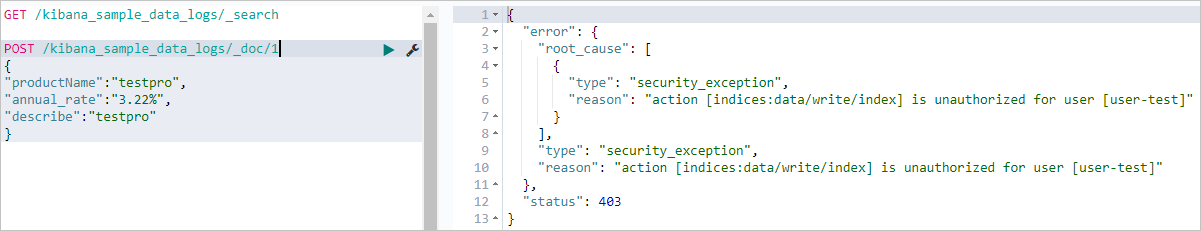
Run a read command — the request succeeds:
GET /kibana_sample_data_logs/_searchRun a write command — the request fails with a permissions error:
POST /kibana_sample_data_logs/_doc/1
{
"productName": "testpro",
"annual_rate": "3.22%",
"describe": "testpro"
}
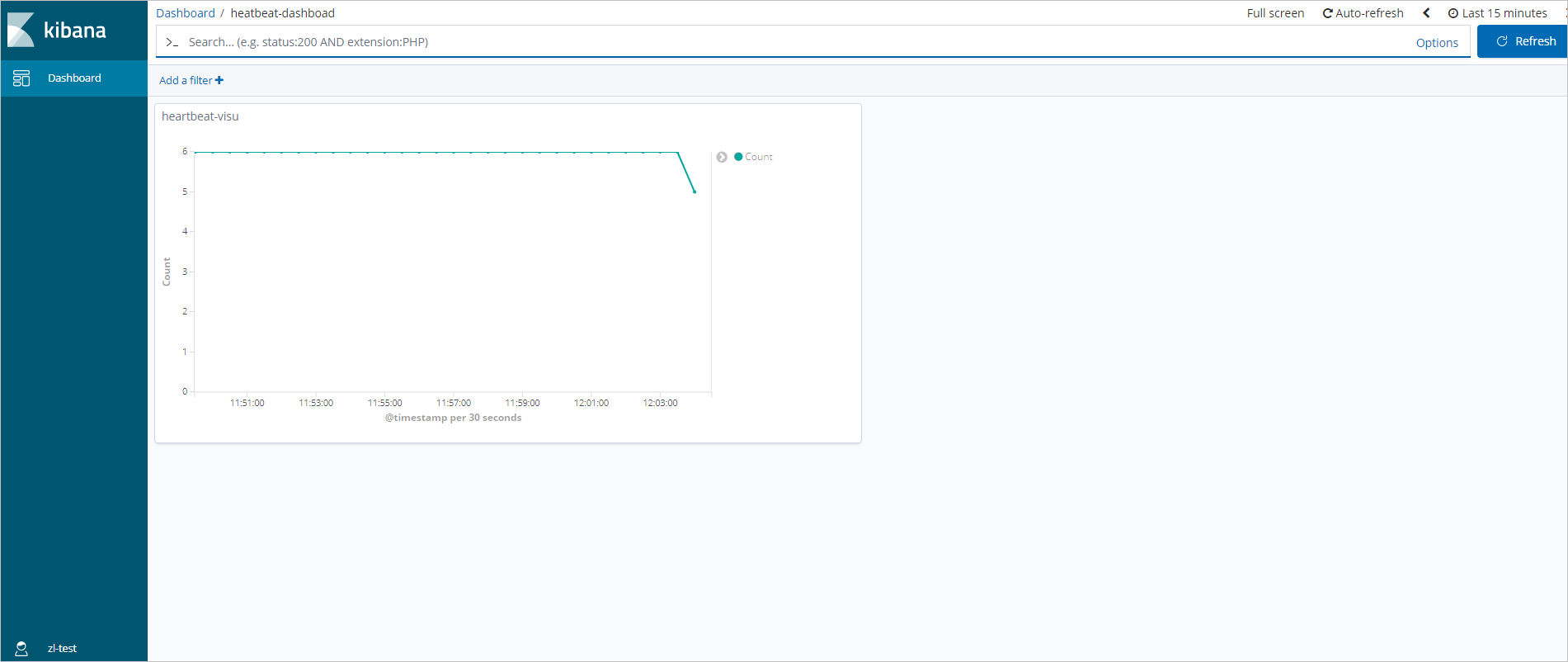
Dashboard view access
Goal: The user can view dashboards for a specific index but cannot access other Kibana features.
Role configuration:
Assign both roles to the user when you create the user:
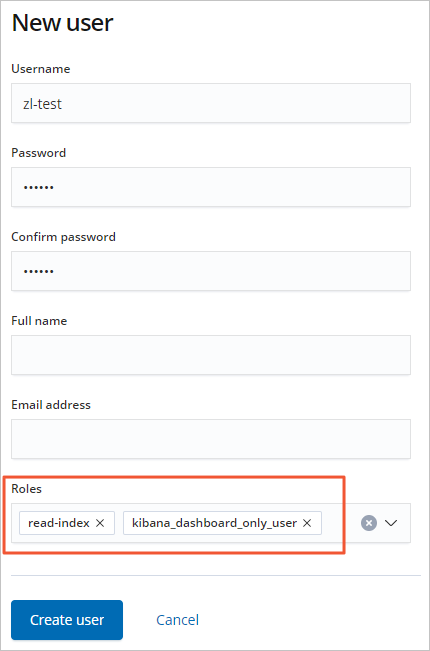
| Role | Type | Description |
|---|---|---|
read-index | Custom | Read-only access to the specific index. Create this role manually. |
kibana_dashboard_only_user | Built-in | Dashboard-only access in Kibana. |
In Kibana V7.0 and later, kibana_dashboard_only_user is deprecated. To restrict a user to dashboards, configure read-only index permissions only (see the Read-only access to an index scenario). To apply the Dashboards only restriction to a custom role in earlier versions: go to Management > Kibana > Advanced Settings > Dashboard, then set Dashboards only roles to your custom role.Verify:
Log on as the user and open the Dashboards section. The user can view dashboards for the index and cannot access other Kibana features.
Read and write access to indexes with cluster monitoring
Goal: The user can read, write, and delete documents in specific indexes, and can view cluster health and statistics, but cannot modify cluster settings.
Role configuration:
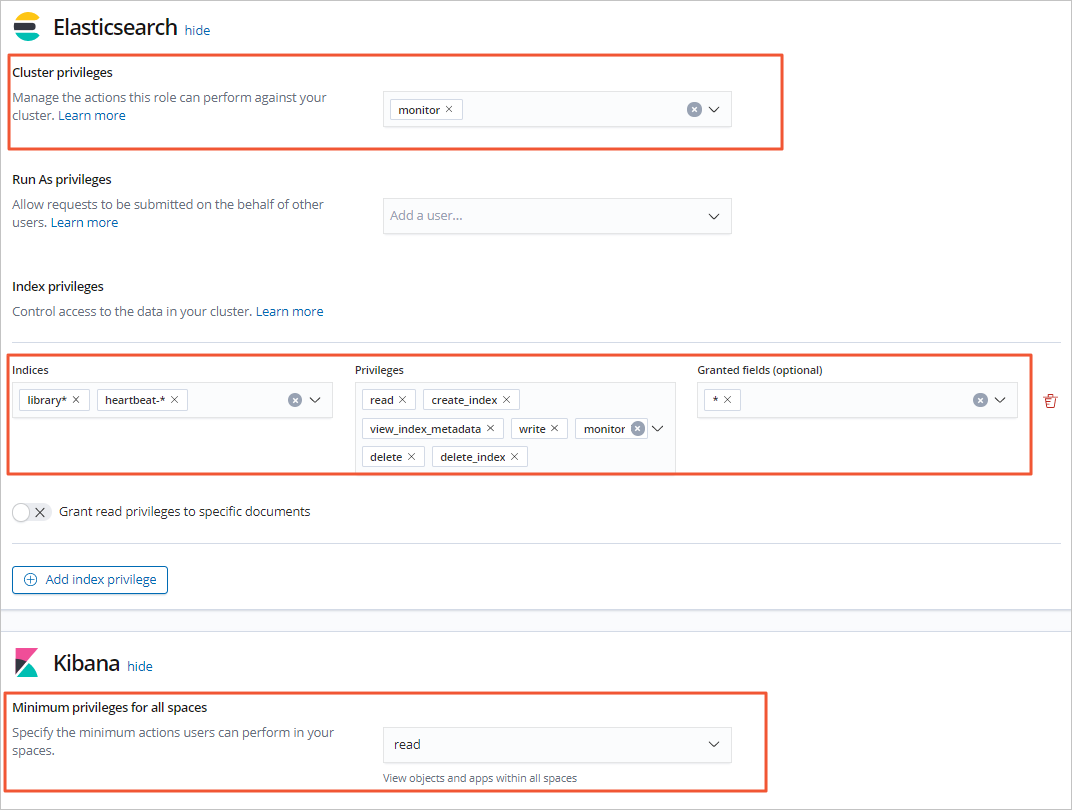
| Permission type | Key | Value | Description |
|---|---|---|---|
| Cluster privileges | cluster | monitor | View running status, health status, hot threads, node info, and blocked tasks. |
| Index privileges | Indices | heartbeat-*, library* | Target indexes. Accepts full name, alias, wildcard, or regular expression. |
| Privileges | read | Read-only access: count, explain, get, mget, scripts, search, and scroll APIs. | |
create_index | Create indexes. To use an alias at creation time, also grant manage. The alias must match the Indices pattern. | ||
view_index_metadata | Read index metadata: aliases, aliases exists, get index, exists, field mappings, mappings, search shards, type exists, validate, warmers, settings, and ilm. | ||
write | All write operations, including mapping updates and the operations performed by calling the index, update, delete, and bulk APIs. Includes more permissions than create + index combined. | ||
monitor | Monitor index operations: recovery, segments info, stats, and status APIs. | ||
delete | Delete documents. | ||
delete_index | Delete indexes. | ||
| Granted fields (optional) | * | All fields. | |
| Kibana privileges | Privileges | read | Read-only access to all Kibana spaces. Default is none. |
Verify:
Log on as the user and run the following commands. All should succeed:
GET /_cat/indices?vGET /_cluster/statsGET /product_info/_searchGET /product_info1/_searchPOST /kibana_sample_data_logs/_doc/2
{
"productName": "testpro",
"annual_rate": "3.22%",
"describe": "testpro"
}PUT /product_info2/_doc/1
{
"productName": "testpro",
"annual_rate": "3.22%",
"describe": "testpro"
}DELETE product_info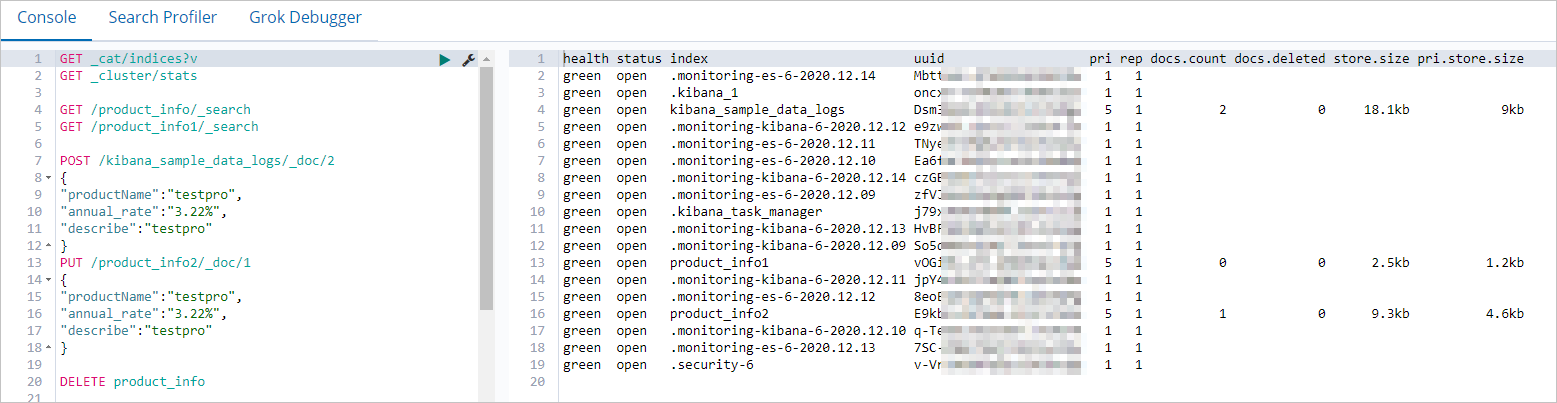
Read-only access to the Discover page and a specific index
Goal: The user can view data from a specific index on the Kibana Discover page but has no other Kibana access.
Role configuration:
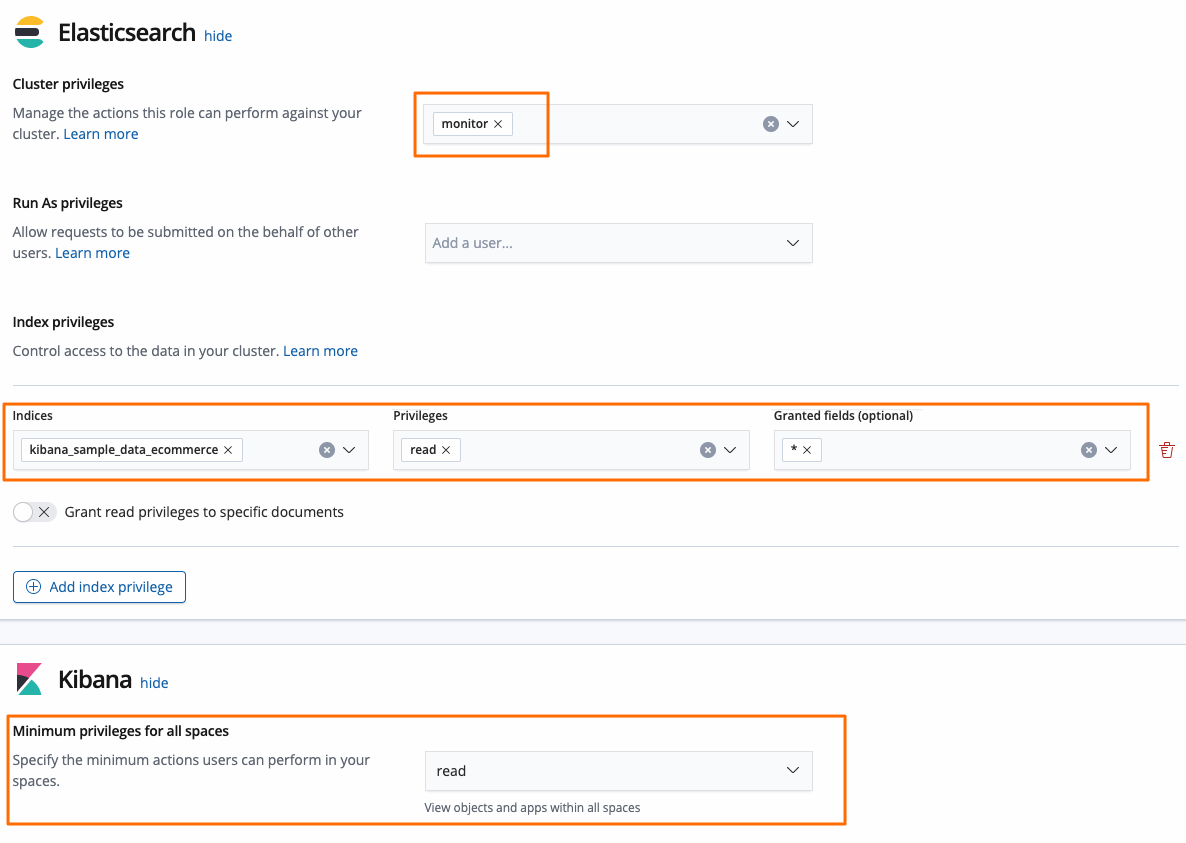
| Permission type | Key | Value | Description |
|---|---|---|---|
| Cluster privileges | Privileges | monitor | View running status, health status, hot threads, node information, node and cluster statistics, and blocked tasks. |
| Index privileges | Indices | kibana_sample_data_ecommerce | The target index. Accepts full name, alias, wildcard, or regular expression. |
| Privileges | read | Read-only access: count, explain, get, mget, scripts, search, and scroll APIs. | |
| Granted fields (optional) | * | All fields. | |
| Kibana privileges | Privileges | read | Read-only access to all Kibana spaces. Default is none. When assigning access to a specific Kibana feature (such as Discover), specify a Kibana space. |
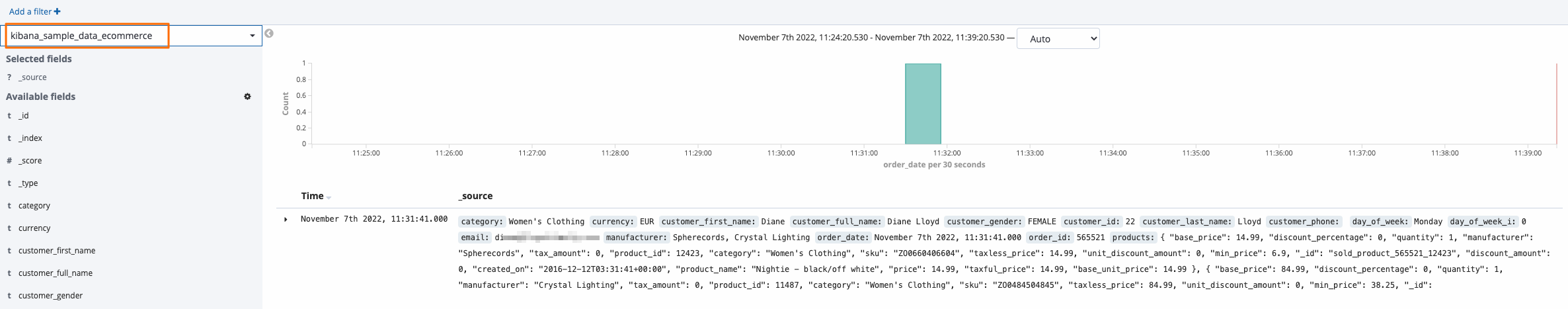
Verify:
Log on as the user and open the Discover page. The user can view index data on Discover and cannot access other Kibana sections.
Full index management without Kibana access
Goal: The user can create and delete indexes, modify index configurations, and add, update, delete, and query documents, but cannot log on to the Kibana console.
Role configuration:
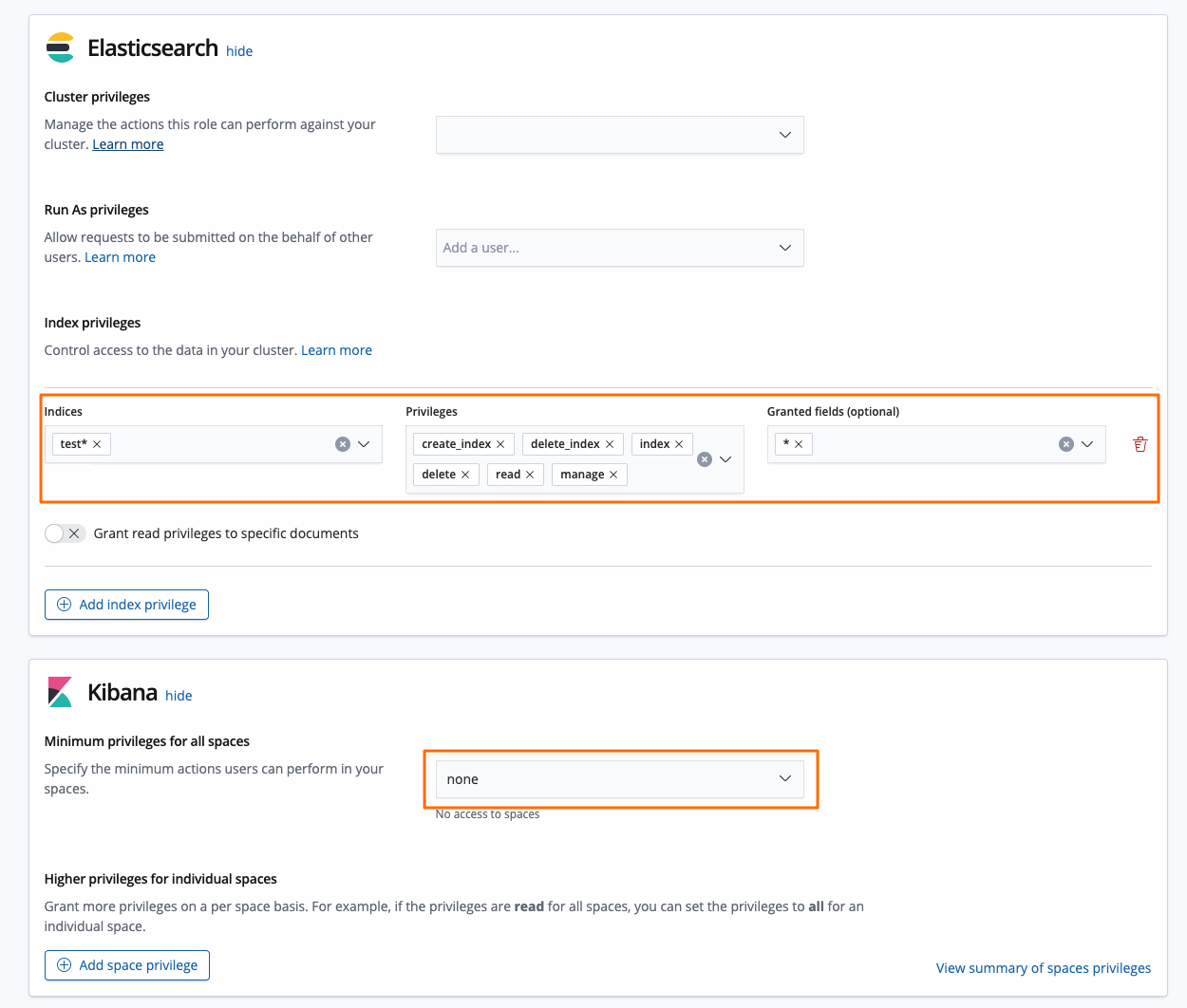
| Permission type | Key | Value | Description |
|---|---|---|---|
| Index privileges | Indices | test* | Target indexes. Accepts full name, alias, wildcard, or regular expression. |
| Privileges | create_index | Create indexes. To use an alias at creation time, also grant manage. | |
delete_index | Delete indexes. | ||
index | Index documents, update documents, and update index mappings. | ||
delete | Delete documents. | ||
read | Read-only access: count, explain, get, mget, scripts, search, and scroll APIs. | ||
manage | Manage index operations: aliases, analyze, cache clear, close, delete, exists, flush, mapping, open, force merge, refresh, settings, search shards, templates, and validate. | ||
| Granted fields (optional) | * | All fields. | |
| Kibana privileges | Privileges | none | Default value. No Kibana spaces are authorized. |
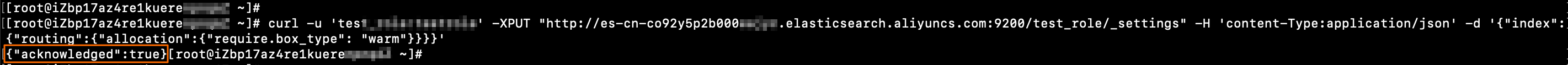
Verify:
Access the cluster directly and run the following tests:
Create and delete an index. Both operations succeed.
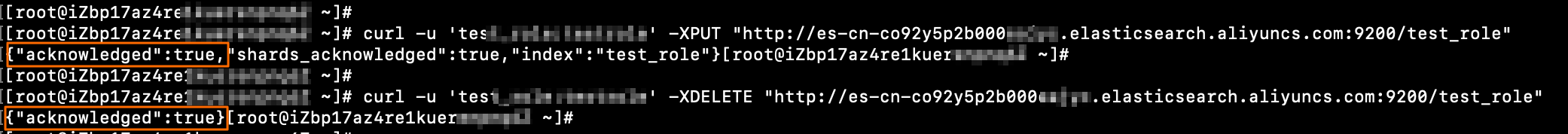
Modify index configurations (for example, mark data as cold). The operation succeeds.
Add, update, delete, and query documents. All operations succeed.
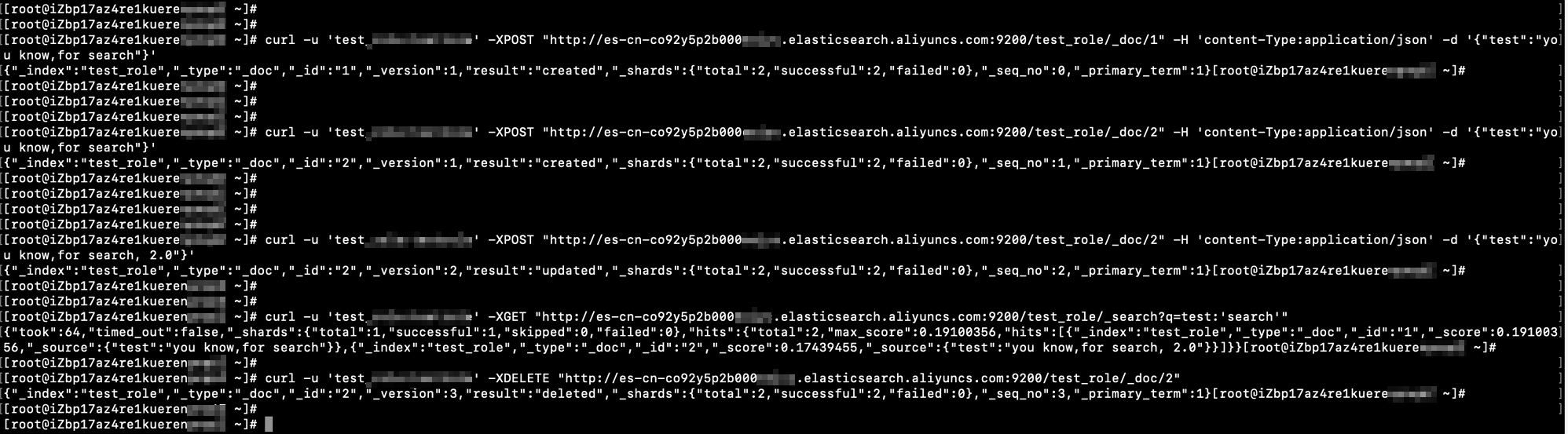
Attempt to log on to the Kibana console. The login fails with a permissions error.
