This topic describes how to connect to an Alibaba Cloud Elasticsearch cluster (ES) by using Java, Python, and Go.
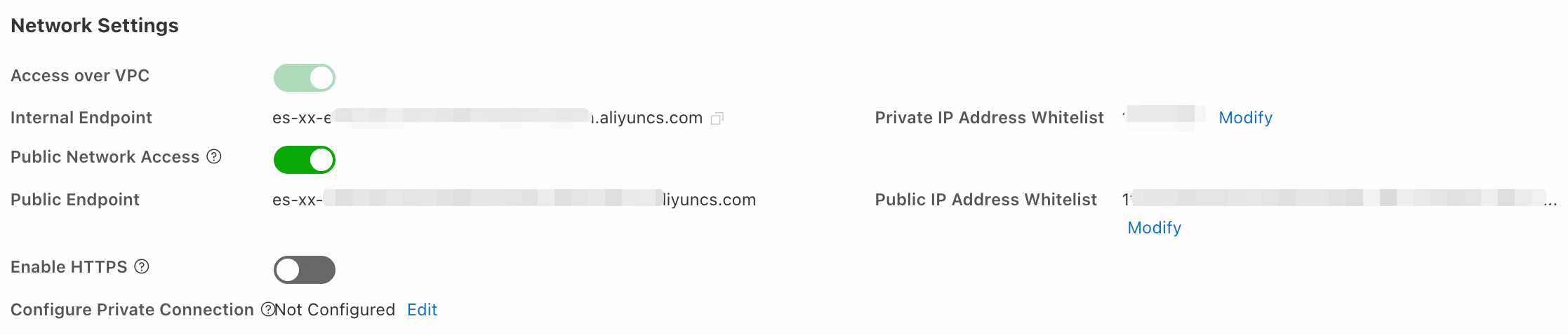
Configure the IP address whitelist
Only devices whose IP addresses are in the whitelist can connect to the cluster. Add the IP address of the connecting device to the VPC private whitelist or public access whitelist.
Step 1: Get the device IP address
| Scenario | IP address to add | How to get it |
|---|---|---|
| Connecting from an on-premises device | Public IP address of the device. If the device is on a LAN (home or corporate network), use the public egress IP of the LAN. | Run curl ipinfo.io/ip |
| Connecting from an ECS instance in a different VPC | Public IP address of the ECS instance | View in the ECS console instance list |
| Connecting from an ECS instance in the same VPC | Private IP address of the ECS instance | View in the ECS console instance list |
Step 2: Add the IP address to the whitelist
-
Log in to the ES console and go to the Basic Information page of the instance.
-
In the left navigation pane, choose Configuration and Management > Security Settings, then click Modify.
-
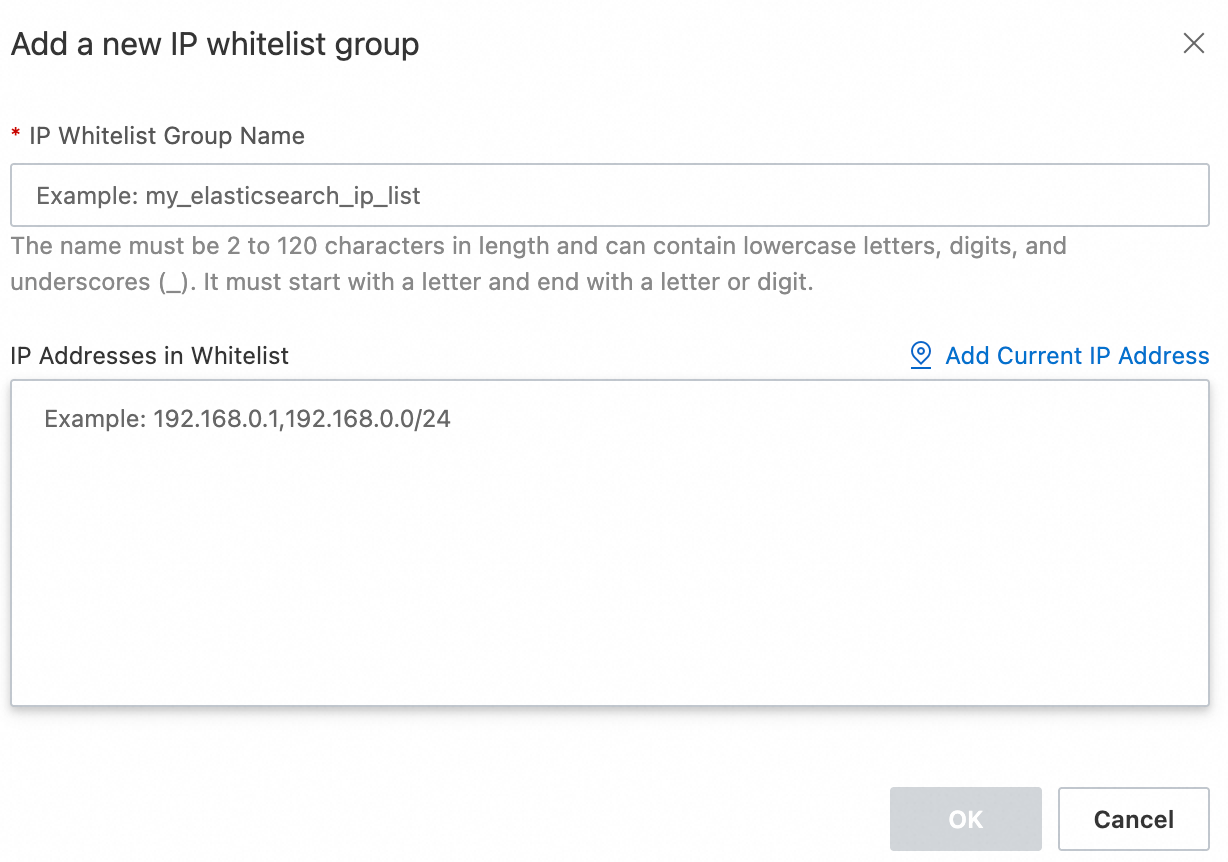
Click Configure to the right of the default group. In the dialog box that appears, add IP addresses to the VPC private whitelist or public access whitelist.
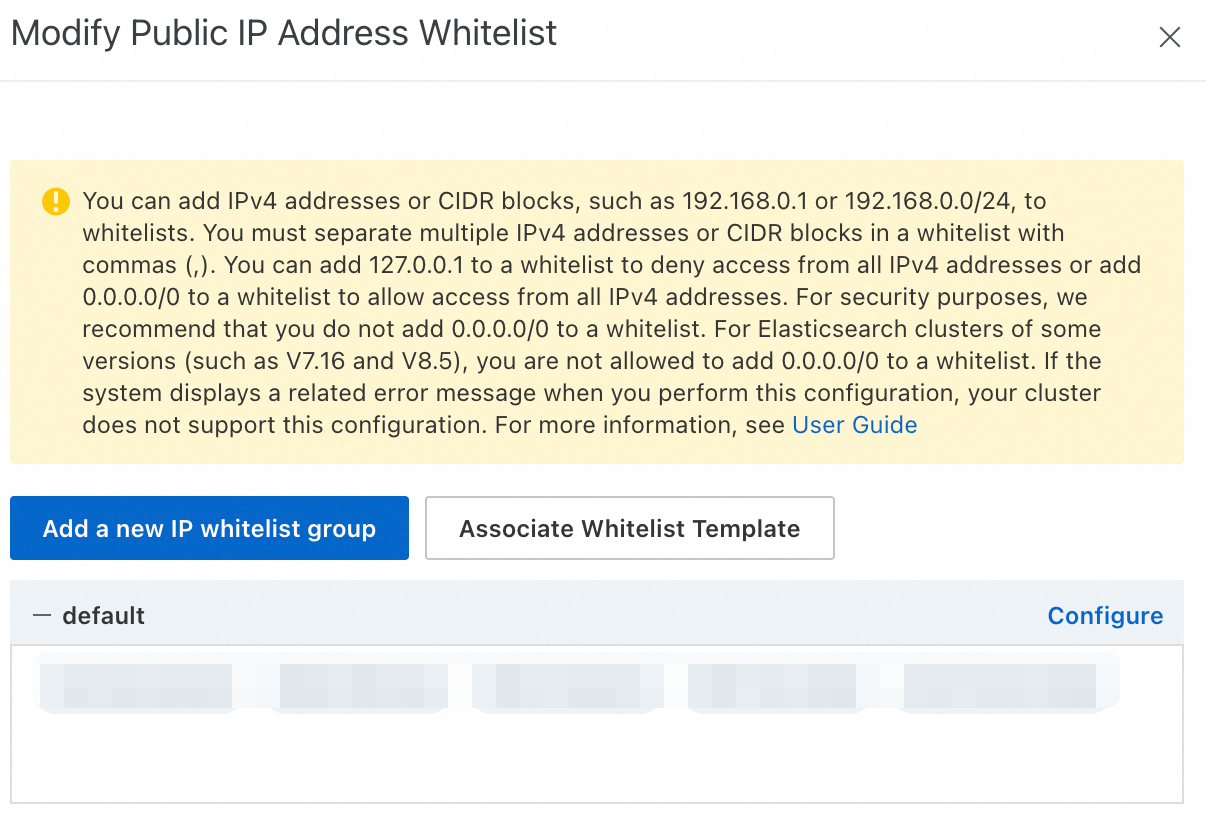
Supported IP address formats:
Format Examples Notes IPv4 address 192.168.0.1(single),192.168.0.0/24(CIDR block)Use 127.0.0.1to deny access.0.0.0.0/0allows all IP addresses — high risk, not recommended. Some versions (7.16, 8.5) and regions do not support0.0.0.0/0.IPv6 address 2401:XXXX:1000:24::5(single),2401:XXXX:1000::/48(CIDR block)Supported only on clusters using the v2 deployment architecture in the China (Hangzhou) region. Use ::1to deny all.::/0allows all — high risk, not recommended.-
A single cluster supports up to 300 IP addresses or CIDR blocks.
-
Separate multiple entries with commas (,) and no spaces.
-
To create additional groups, click Add IP Whitelist Group. Groups are for organizational purposes only — all IP addresses across groups share the same access permissions.
-
-
Click Confirm.
Protocols and certificates
For optimal compatibility, ensure your client's language version (Java, Python, or Go) matches the ES cluster's underlying runtime.
Public HTTPS: Uses a certificate issued by a trusted Certificate Authority (CA). No special client configuration is required. Connect directly by using the
https://protocol.Private HTTPS: Uses a self-signed certificate for encrypted data transmission. You must configure your client to skip certificate verification. For details, see the private HTTPS connection examples for each language.
Connect to the cluster
Java
Install Java Development Kit (JDK) 1.8 or later.
Configure Maven dependencies.
ImportantSet
versionto the correct ES version number. The relevant dependencies can be pulled only ifversionis set correctly. The ES version in this example is 8.17.0.<dependency> <groupId>co.elastic.clients</groupId> <artifactId>elasticsearch-java</artifactId> <version>8.17.0</version> </dependency> <dependency> <groupId>com.fasterxml.jackson.core</groupId> <artifactId>jackson-databind</artifactId> <version>2.12.3</version> </dependency>Configure YML parameters to enable automatic index creation:
action.auto_create_index: true. The following example connects to the ES cluster and creates an index named hr_test.
Basic connection example
The following example applies to public HTTPS or private HTTP scenarios:
package org.example;
import co.elastic.clients.elasticsearch.ElasticsearchClient;
import co.elastic.clients.elasticsearch.cat.IndicesResponse;
import co.elastic.clients.elasticsearch.indices.*;
import co.elastic.clients.json.jackson.JacksonJsonpMapper;
import co.elastic.clients.transport.ElasticsearchTransport;
import co.elastic.clients.transport.rest_client.RestClientTransport;
import org.apache.http.HttpHost;
import org.apache.http.auth.AuthScope;
import org.apache.http.auth.UsernamePasswordCredentials;
import org.apache.http.client.CredentialsProvider;
import org.apache.http.impl.client.BasicCredentialsProvider;
import org.apache.http.impl.nio.client.HttpAsyncClientBuilder;
import org.elasticsearch.client.*;
import java.io.IOException;
public class RestClientTest {
public static void main(String[] args) {
final CredentialsProvider credentialsProvider = new BasicCredentialsProvider();
credentialsProvider.setCredentials(AuthScope.ANY, new UsernamePasswordCredentials("{UserName}", "{YourPassword}"));
// Use "https" for public HTTPS access or "http" for private HTTP access.
RestClient restClient = RestClient.builder(new HttpHost("{YourEsHost}", 9200, "https"))
.setHttpClientConfigCallback(new RestClientBuilder.HttpClientConfigCallback() {
@Override
public HttpAsyncClientBuilder customizeHttpClient(HttpAsyncClientBuilder httpClientBuilder) {
return httpClientBuilder.setDefaultCredentialsProvider(credentialsProvider);
}
}).build();
ElasticsearchTransport transport = new RestClientTransport(restClient, new JacksonJsonpMapper());
ElasticsearchClient elasticsearchClient = new ElasticsearchClient(transport);
try {
CreateIndexResponse indexRequest = elasticsearchClient.indices().create(createIndexBuilder -> createIndexBuilder
.index("hr_test")
.aliases("foo", aliasBuilder -> aliasBuilder.isWriteIndex(true))
);
System.out.println("Index document successfully! " + indexRequest.acknowledged());
transport.close();
restClient.close();
} catch (IOException ioException) {
// Handle exceptions.
}
}
}
Private HTTPS connection example
For private HTTPS connections, you must add a configuration to skip certificate verification:
package org.example;
import co.elastic.clients.elasticsearch.ElasticsearchClient;
import co.elastic.clients.json.jackson.JacksonJsonpMapper;
import co.elastic.clients.transport.ElasticsearchTransport;
import co.elastic.clients.transport.rest_client.RestClientTransport;
import org.apache.http.HttpHost;
import org.apache.http.auth.AuthScope;
import org.apache.http.auth.UsernamePasswordCredentials;
import org.apache.http.client.CredentialsProvider;
import org.apache.http.conn.ssl.NoopHostnameVerifier;
import org.apache.http.impl.client.BasicCredentialsProvider;
import org.apache.http.impl.nio.client.HttpAsyncClientBuilder;
import org.apache.http.ssl.SSLContexts;
import org.elasticsearch.client.*;
import javax.net.ssl.SSLContext;
public class RestClientTestPrivateHttps {
public static void main(String[] args) throws Exception {
final CredentialsProvider credentialsProvider = new BasicCredentialsProvider();
credentialsProvider.setCredentials(AuthScope.ANY, new UsernamePasswordCredentials("{UserName}", "{YourPassword}"));
// Create an SSLContext that trusts all certificates.
SSLContext sslContext = SSLContexts.custom()
.loadTrustMaterial(null, (chain, authType) -> true) // Trust all certificates.
.build();
RestClient restClient = RestClient.builder(new HttpHost("{YourEsHost}", 9200, "https"))
.setHttpClientConfigCallback(new RestClientBuilder.HttpClientConfigCallback() {
@Override
public HttpAsyncClientBuilder customizeHttpClient(HttpAsyncClientBuilder httpClientBuilder) {
return httpClientBuilder
.setDefaultCredentialsProvider(credentialsProvider)
.setSSLContext(sslContext) // Set the SSLContext.
.setSSLHostnameVerifier(NoopHostnameVerifier.INSTANCE); // Skip hostname verification.
}
}).build();
ElasticsearchTransport transport = new RestClientTransport(restClient, new JacksonJsonpMapper());
ElasticsearchClient elasticsearchClient = new ElasticsearchClient(transport);
// Perform operations.
System.out.println(elasticsearchClient.info());
transport.close();
restClient.close();
}
}Python
The following code uses ES version 8.17.0 as an example. Replace the version number with your actual ES version.
Basic connection example
The following example applies to public HTTPS or private HTTP scenarios:
pip install elasticsearch==8.17.0from elasticsearch import Elasticsearch
es = Elasticsearch(
hosts=['https://<YourEsHost>:9200'], # Use 'https://' for public HTTPS access or 'http://' for private HTTP access.
basic_auth=('<UserName>', '<YourPassword>'),
)
print(es.info())
Private HTTPS connection example
from elasticsearch import Elasticsearch
import urllib3
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning) # Disable SSL warnings (optional).
es = Elasticsearch(
hosts=['https://<YourEsHost>:9200'],
basic_auth=('<UserName>', '<YourPassword>'),
verify_certs=False, # Skip certificate verification.
ssl_show_warn=False, # Disable SSL warnings.
)
print(es.info())
Go
The following example shows how to connect to an ES 8.x cluster by using Go. For more information about the features of the Go client, see Elasticsearch Go Client.
Basic connection example
The following example applies to public HTTPS or private HTTP scenarios:
go get github.com/elastic/go-elasticsearch/v8
package main
import (
"github.com/elastic/go-elasticsearch/v8""log"
)
func main() {
cfg := elasticsearch.Config{
Addresses: []string{"https://<YourEsHost>:9200"}, // Use "https://" for public HTTPS access or "http://" for private HTTP access.
Username: "<UserName>",
Password: "<YourPassword>",
}
es, _ := elasticsearch.NewClient(cfg)
res, _ := es.Info()
defer res.Body.Close()
log.Println(res)
}
Private HTTPS connection example
package main
import (
"crypto/tls""net/http""github.com/elastic/go-elasticsearch/v8""log"
)
func main() {
cfg := elasticsearch.Config{
Addresses: []string{"https://<YourEsHost>:9200"},
Username: "<UserName>",
Password: "<YourPassword>",
Transport: &http.Transport{
TLSClientConfig: &tls.Config{InsecureSkipVerify: true}, // Skip certificate verification.
},
}
es, _ := elasticsearch.NewClient(cfg)
res, _ := es.Info()
defer res.Body.Close()
log.Println(res)
}Parameters
Parameter | Description |
UserName | The default username is For security reasons, you should not use this default administrator account directly in a production environment. You can use the Role-based Access Control (RBAC) mechanism of Elasticsearch X-Pack to customize roles, assign permissions, and then assign the roles to users to implement fine-grained permission control. For more information, see Manage user permissions by using Elasticsearch X-Pack roles. |
YourPassword | The password for the specified |
https | Specifies the access protocol. HTTP is enabled by default. For security, we recommend using the HTTPS protocol, which you must enable manually. To do this, log on to the Elasticsearch console, go to the Basic Information page of your instance, and in the left-side navigation pane, choose Configuration and Management > Security Settings to enable the HTTPS protocol. Important
|
YourEsHost | The cluster endpoint that you obtained in the "Prerequisites" section:
|
9200 | Specifies the cluster's access port. The default is 9200 for both VPC private network and public access. |