This page answers common questions about access control for Alibaba Cloud Elasticsearch clusters.
- No VPCs appear on the buy page when a RAM user tries to purchase a cluster
- If a temporary user is deleted, are the clusters or data created by that user also deleted?
- The error "The specified RAM user is not authorized. Check the permission of the RAM user and try again." appears. What should I do?
- How do I create a user with read-only access to Elasticsearch cluster resources such as indexes?
- After logging into the Kibana console with a role-assigned user, no indexes are visible. Only the elastic account can view indexes. What should I do?
No VPCs appear on the buy page when a RAM user tries to purchase a cluster
The RAM user likely lacks permission to list virtual private clouds (VPCs). Check the RAM user's permissions, and if the required permissions are missing, create a custom policy to grant them.
If a temporary user is deleted, are the clusters or data created by that user also deleted?
No. Deleting a temporary user does not delete the Elasticsearch clusters that user created, and any changes the user made to those clusters are not rolled back. Operations performed by a temporary user are equivalent to those performed by an Alibaba Cloud account.
The error "The specified RAM user is not authorized. Check the permission of the RAM user and try again." appears. What should I do?
Grant the required permissions to the RAM user. For details, see Create a custom policy.
You can also attach one of the following system policies directly:
| Policy | Scope | Attach to |
|---|---|---|
AliyunElasticsearchReadOnlyAccess | Read-only access to Elasticsearch and Logstash clusters | Read-only users |
AliyunElasticsearchFullAccess | Management access to Elasticsearch and Logstash clusters | Administrators |
How do I create a user with read-only access to Elasticsearch cluster resources such as indexes?
Create a role with the required permissions in the Kibana console, then assign the role to the user. For details, see Use the RBAC mechanism provided by Elasticsearch X-Pack to implement access control.
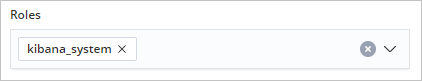
After logging into the Kibana console with a role-assigned user, no indexes are visible. Only the elastic account can view indexes. What should I do?
Grant the kibana_system permission to the user when creating it. For details, see Use the RBAC mechanism provided by Elasticsearch X-Pack to implement access control.