ESA WAF offers four mitigation strategies of increasing complexity. Choose the right approach for your website, from one-click AI-powered rate limiting to fully custom rules.
Mitigation policies
The following table compares the four policies by use case, complexity, and key benefits. Start with the policy that matches your current needs. You can always layer additional policies as your requirements grow.
Policy | Use cases | Complexity | Key benefits |
Smart rate limiting | Individual developers and new, small-scale websites | Very Low | One-click, AI-powered protection with zero configuration. |
Create rules from security analytics | For proactively identifying and mitigating potential threats on stable websites. | Low | Data-driven insights to pinpoint and quickly respond to anomalous traffic. |
Create rules from a rule template | For combatting common attacks or addressing specific, general protection needs. | Medium | Pre-built templates cover common scenarios for efficient deployment. |
Create custom rules | For complex or unique security needs that require fine-grained control. | High | Offers the flexibility to meet complex protection requirement. |
Policy 1: Smart rate limiting
This is the simplest and fastest way to get started, especially for users new to web security.
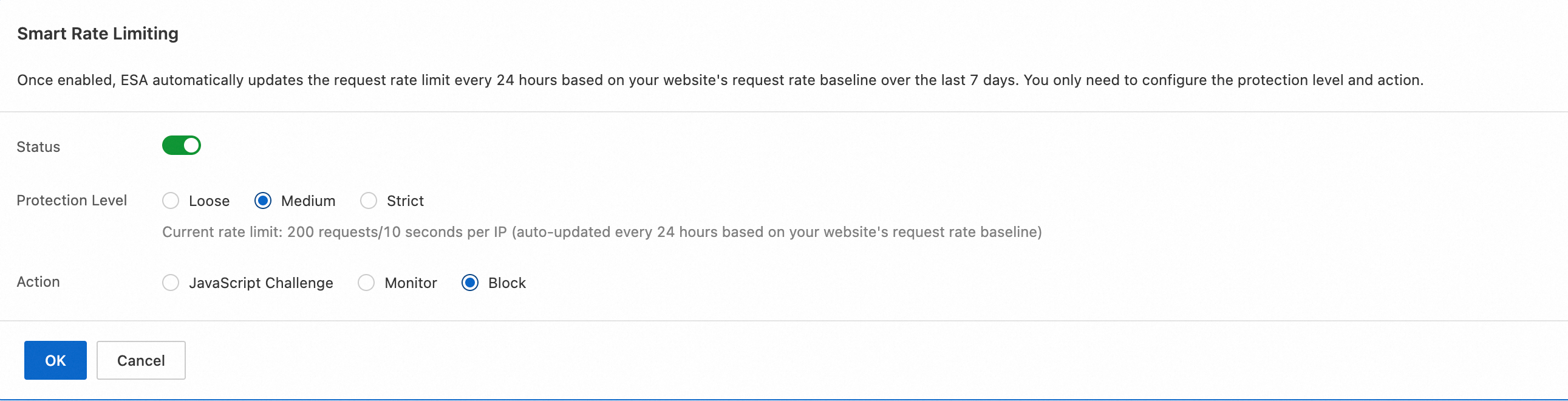
The smart rate limiting feature uses ESA's AI engine to automate rate limiting. You only need to enable the feature and select a protection level. The system learns a baseline from your website's past seven days of traffic data and automatically blocks requests that exceed normal frequency patterns. No manual rule configuration is required. This effectively protects against CC attacks (resource exhaustion) and malicious crawlers.
Use cases
Individual developers or startups: Low-traffic websites that need basic CC attack protection with minimal setup.
Security beginners: For users unfamiliar with WAF who need a simple, one-click solution.
Before you begin
Activation time: The feature takes effect about 10 seconds after you enable it.
Block duration: The system blocks IP addresses that trigger rate limiting for approximately 24 hours.
Handling false positives: If a legitimate IP address is blocked, add it to a whitelist under WAF > Whitelist Rules.
Steps
Policy 2: Security analytics
You may want to monitor traffic more proactively and respond to potential threats.
ESA provides Security Analytics and Events dashboards where you can inspect every request by IP address, path, and User-Agent. When you spot anomalous traffic, you can create a WAF rule directly from the dashboard with a single click. For example, you can:
Block an IP address that is sending repeated malicious requests.
Block a crawler disguised as a browser, identified by its User-Agent string.
Use cases
Growing websites: Monitor increasing website traffic to detect anomalies early.
Proactive security operations: Detect and stop suspicious behavior, such as rapid directory scanning, before it escalates into a full attack.
Note
Data in the Security Analytics and Events dashboards has a latency of approximately 5 minutes.
Steps
Policy 3: Rule templates
Using a rule template to combat common, known attack types.
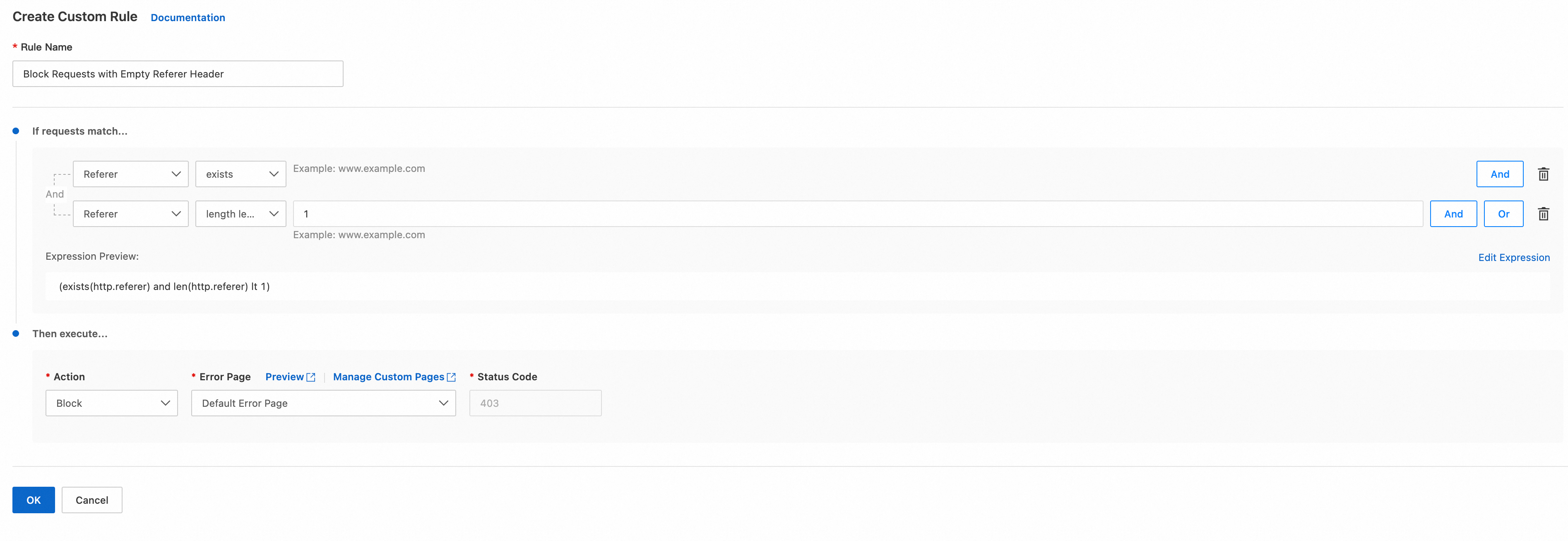
ESA provides pre-configured rule templates based on real-world attack data, covering scenarios like blocking empty-Referer requests, protecting backend login pages from brute-force attacks, and allowlisting specific IPs. Select a template, fill in the required parameters (such as your backend login URL), and the rule is deployed immediately.
Use cases
Common attacks: Your website is experiencing password brute-forcing, SQL injection, or similar known attack types.
Clear protection goals: You know exactly what you need, such as "allow only search engine crawlers".
Note
Read each template's description carefully before use. Misconfigured parameters may block legitimate traffic.
Steps
Policy 4: Custom rules
When the preceding policies cannot meet your needs, use WAF Configuration Rules for fully customized protection.
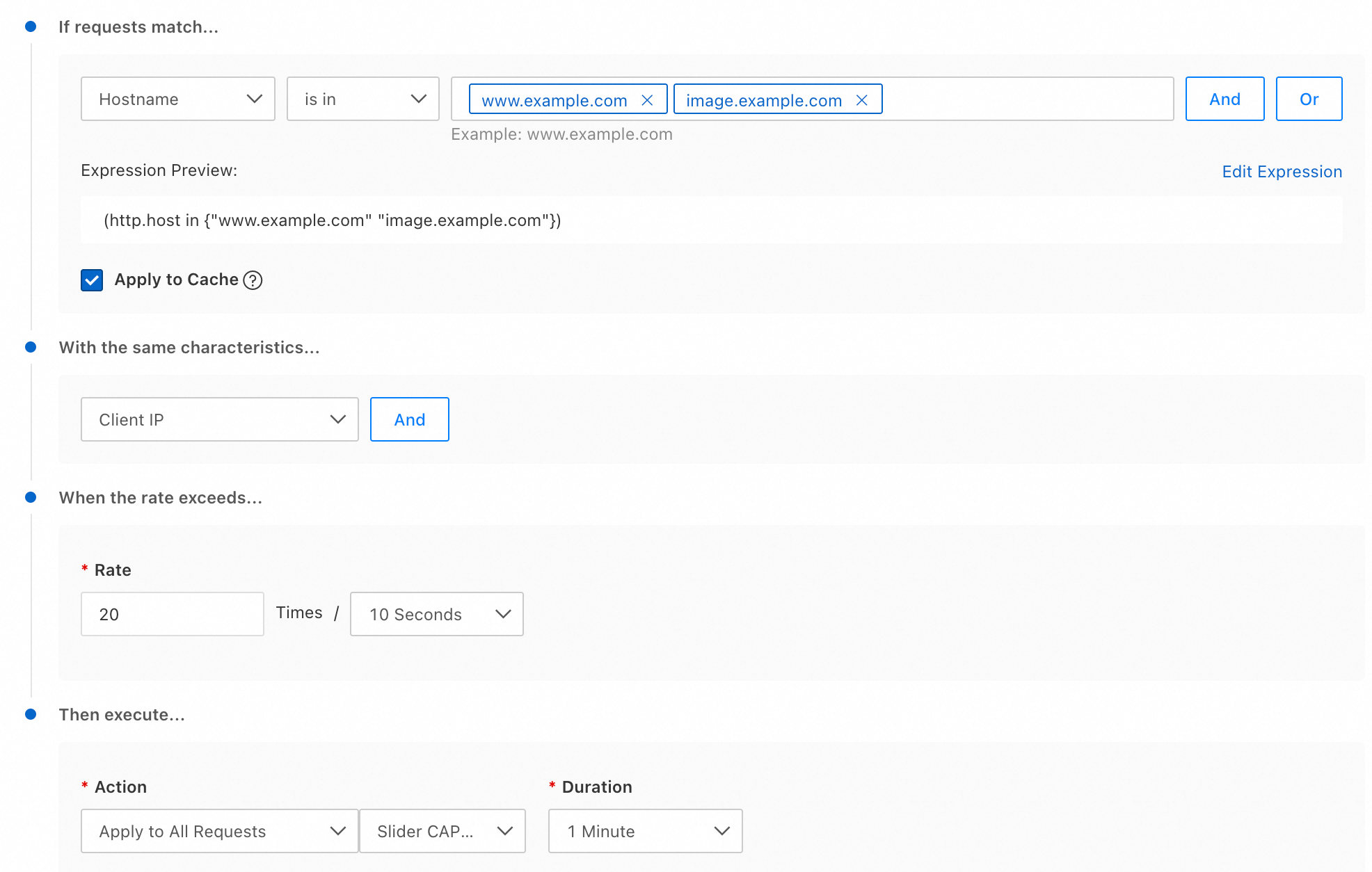
Custom rules let you build match conditions by combining request attributes such as IP address, URL path, headers, cookies, and body content. You then assign an action: block, observe, or allow. This gives you full control over how traffic is filtered and handled.
Use cases
Advanced security operations: You need fine-grained, multi-condition protection logic built by experienced security engineers.
Special business scenarios: Your application has unique logic that requires tightly integrated rules, such as allowing only users with a specific cookie to access an API.
Responding to complex attacks: You face advanced persistent threats (APTs) where attackers constantly change methods, requiring flexible and adaptive rules.