The DDoS protection features leverage general rules developed by the Alibaba Cloud anti-DDoS engine based on extensive historical attack and defense data. These rules are always-on. During an HTTP DDoS attack, the rules detect and block malicious requests in real-time. This action prevents attack traffic from reaching the origin server, which protects the server's resources from abnormal consumption.
View and adjust rules
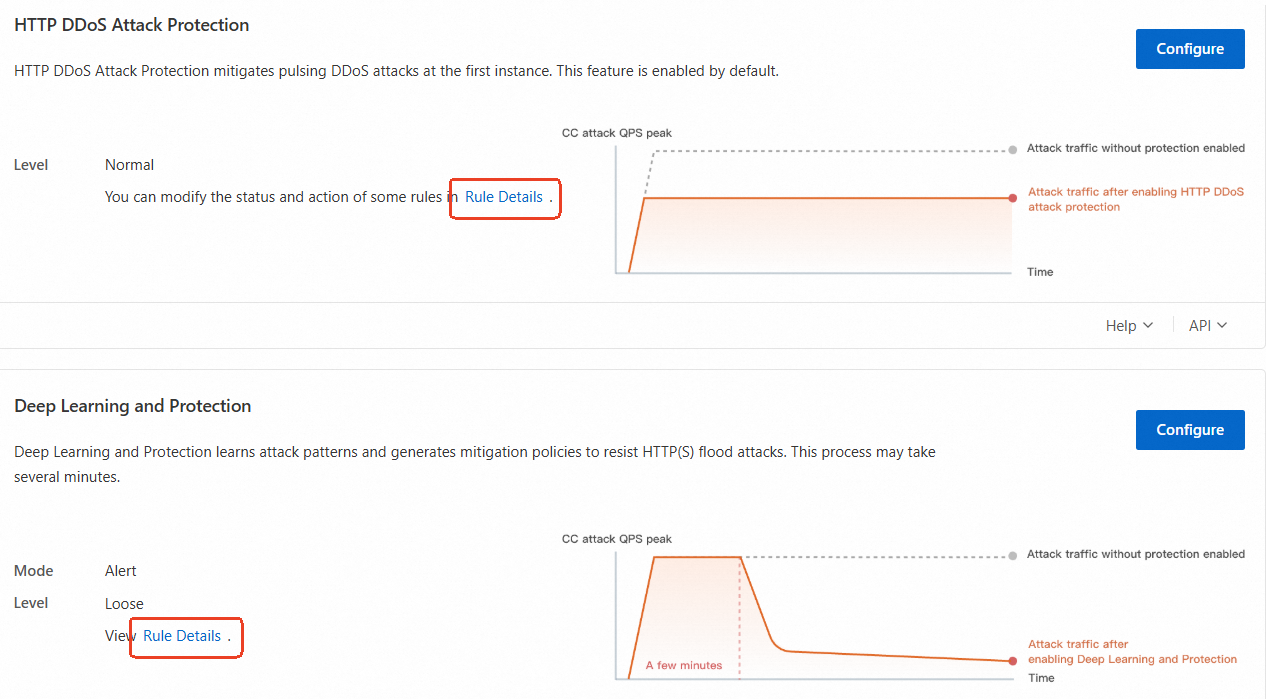
The details, status, and actions for mitigation rules are configured by default. Adjust the rules as needed.
In the ESA console, choose Websites and click your target website.
In the navigation pane on the left, choose .
On the Protection Settings tab, click Rule Details in the HTTP DDoS Attack Protection or Deep Learning and Protection sections to modify the status and action of the rule.
Action descriptions
Block: When a request matches a rule, it is blocked and a response page indicating the action is sent back to the requesting client.
NoteTo configure a custom error page for block actions, see Configure custom pages.
Monitor: Requests that match the rule are not blocked but are logged instead. You can query logs about requests that match the rule and analyze the protection performance. For example, you can check whether normal requests are blocked based on logs. The first time you configure a rule, you can set the Action parameter to Monitor to check the protection performance of the rule and whether legitimate requests are blocked. Then, you can determine whether to change the action for these requests.
NoteYou can query logs only when the Simple Log Service for WAF feature is enabled.
JavaScript Challenge: This indicates that WAF issues a JavaScript code snippet to the client, which a standard browser can execute automatically. If the client passes JavaScript verification, WAF allows requests from the client within a specific time range. During this time range, the client can bypass the verification. By default, the time range is 30 minutes. If the client fails JavaScript verification, WAF blocks requests from the client.