After a sensitive data detection scan completes, Data Security Center (DSC) organizes results by asset type — database instances, OSS buckets, and Simple Log Service (SLS) projects. For each asset, you can drill down across three levels to find exactly where sensitive data was detected and which rules were triggered. Results are also available for specific data objects, such as data tables, files, or data stored within a 5-minute interval.
Drill-down levels:
| Level | What it shows |
|---|---|
| Instance | Overall sensitivity level for a database instance, OSS bucket, or SLS project |
| Object | Sensitive data statistics for individual tables, files, or Logstores within the instance |
| Hit | Detection rules that matched, the number of matches, and sample data from matched fields or files |
Sensitivity levels
DSC assigns one of the following sensitivity levels to each scanned asset:
| Sensitivity level | Description |
|---|---|
| N/A | No sensitive information included in the current identification template is detected. |
| S1 | Non-sensitive data. In most cases, the disclosure of this type of data does not cause harm. Examples: provinces, cities, and product names. |
| S2 | Moderately sensitive data. This type of data is not suitable for disclosure. The disclosure of this type of data causes low-level harm. Examples: names and addresses. |
| S3 | Highly sensitive data. This type of data has a high sensitivity level. The disclosure of a small amount of this type of data causes serious harm. Examples: identity documents, account passwords, and database information. |
| S4 | Core confidential data. This type of data must not be disclosed under any circumstances. Examples: genes, fingerprints, and iris information. |
View detection results for a database instance
Log on to the Data Security Center console.
In the left navigation pane, choose Classification and Grading > Asset Insight.
On the Asset Type tab, click a data type to view detection results for all database instances connected to DSC.
The Asset Type and Data Domain tabs provide different views of the same results. This topic uses the Asset Type tab. On the Data Domain tab, select a data domain to view results for all assets within that domain.

In the Actions column, click the appropriate option for the asset type:
Table Details — for structured data and big data
Details — for unstructured data in SLS
File Details — for unstructured data in OSS
In the details panel that appears on the right, review the sensitive data statistics.
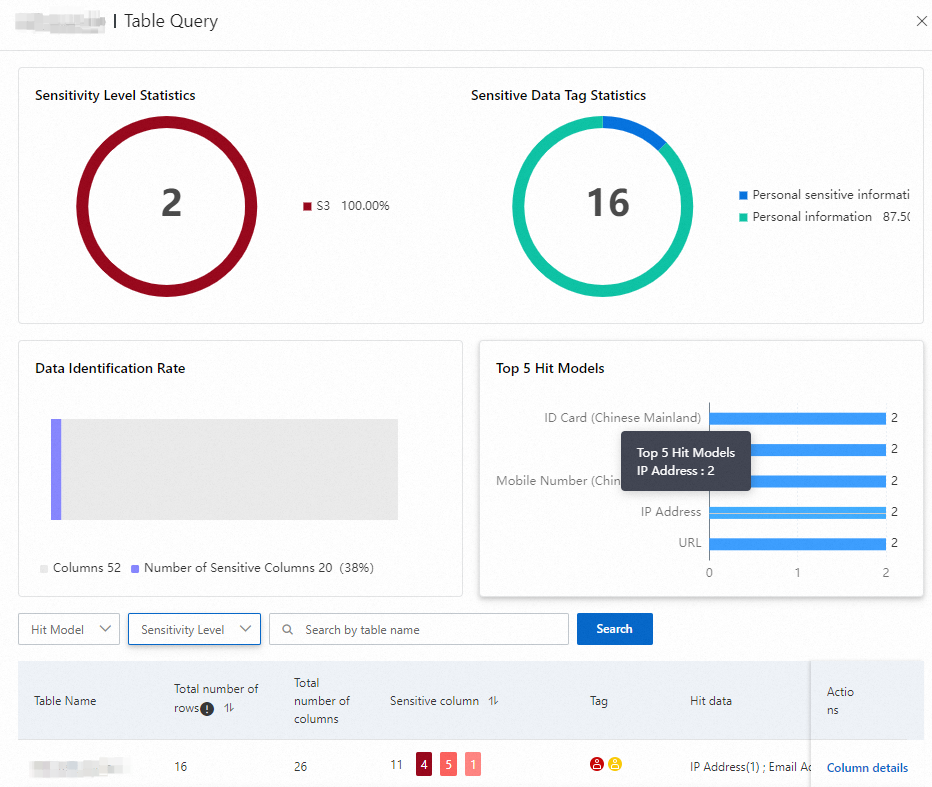
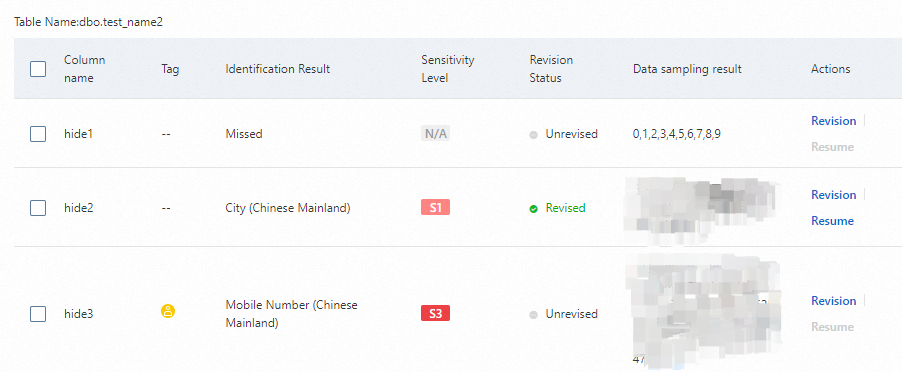
In the sensitive data list, click the appropriate option in the Actions column to view which detection rules were triggered for each data column: If Revision appears in the Actions column, click it to correct the detection results.
Column details — for structured data and big data
Hit details — for unstructured data
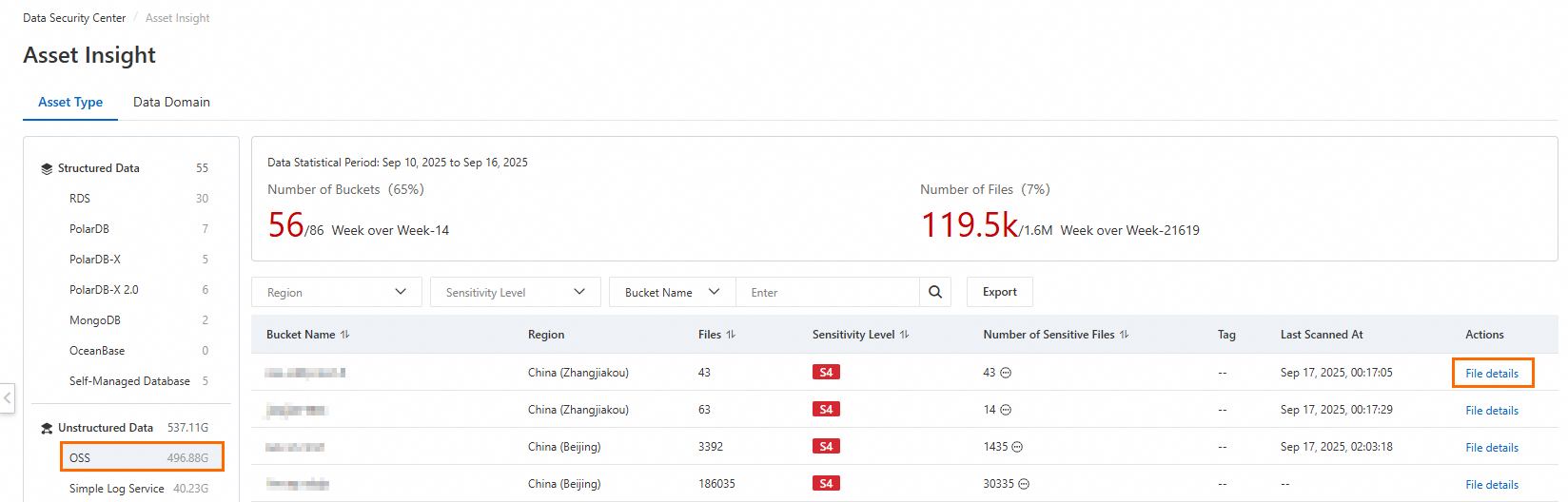
View detection results for an OSS bucket
Log on to the Data Security Center console.
In the left navigation pane, choose Classification and Grading > Asset Insight.
On the Asset Type tab, click Unstructured Data > OSS in the left-side pane to view detection results for all OSS buckets connected to DSC.
In the Actions column of the target bucket, click File details.
In the OSS object query panel, review the sensitive data statistics.
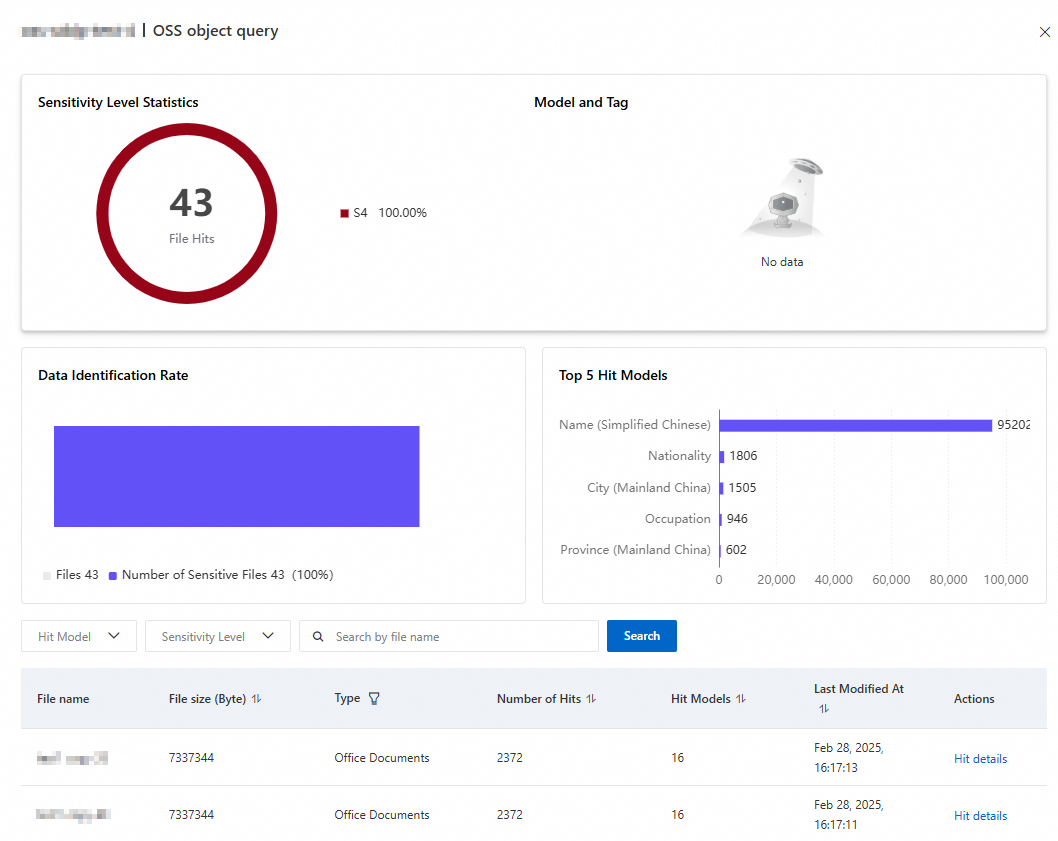
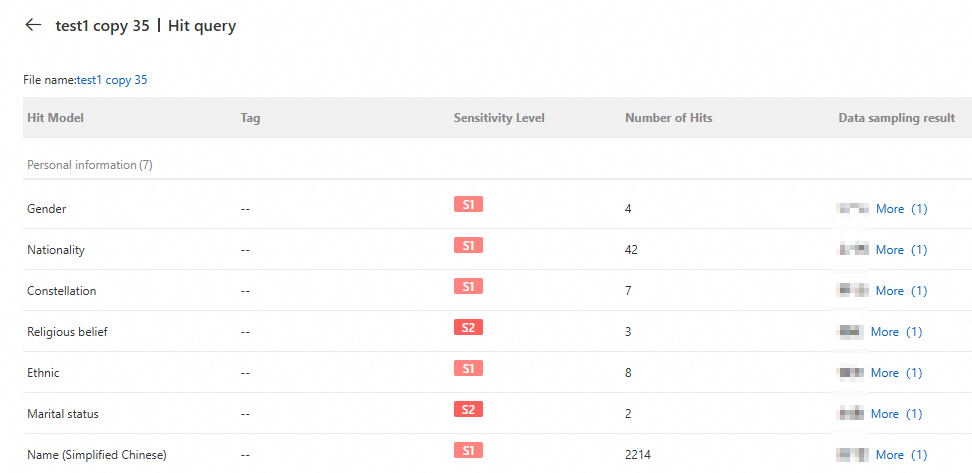
In the Actions column of a sensitive file, click Hit details. The Hit query panel displays the Hit Model, Sensitivity Level, Number of Hits, and Data sampling result for that file.
Click the File name above the list to open the file in the OSS console.
Limitation
The file path shown is the path DSC recorded during the scan. If the file was moved after the scan, the path may be outdated. To get an accurate result, rerun the detection task under Classification and Grading > Tasks > Identification Tasks.
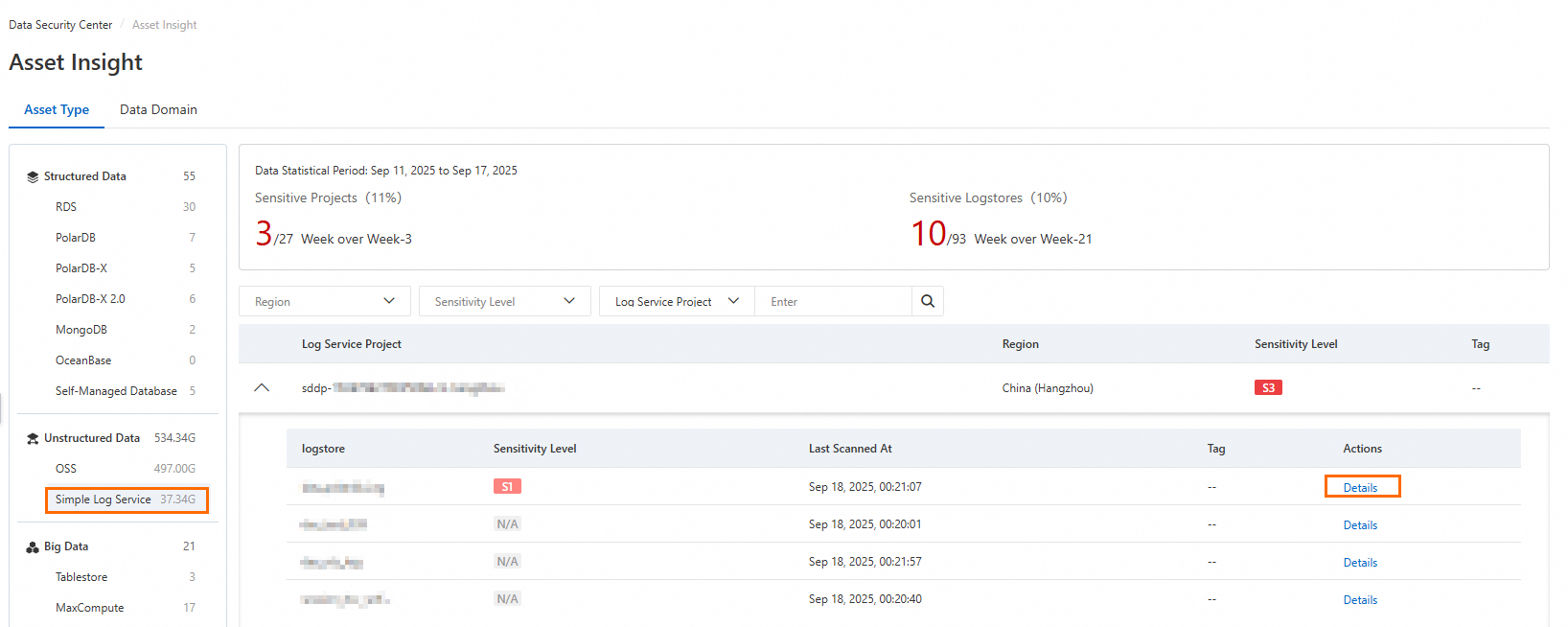
View detection results for SLS
Log on to the Data Security Center console.
In the left navigation pane, choose Classification and Grading > Asset Insight.
On the Asset Type tab, click Unstructured Data > SLS in the left-side pane to view detection results for all SLS projects connected to DSC.
In the Actions column of the target Logstore, click Details.
In the Simple Log Service Object Query panel, review the sensitive data statistics.
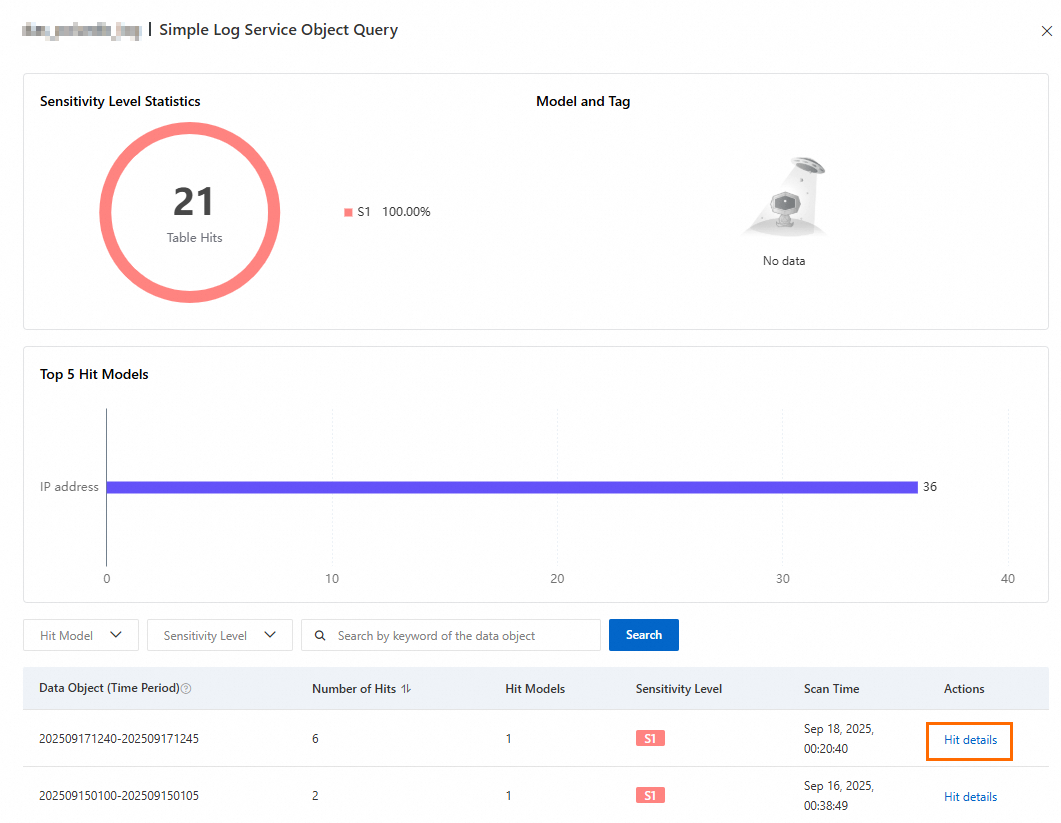
In the Actions column of the data object, click Hit details to view the Hit Model, Sensitivity Level, Number of Hits, and Data sampling result.
Click a result in the Data sampling result column to open the corresponding Logstore in SLS and filter logs based on that result.
Limitations
The following limitations apply when querying logs in SLS based on sampling results.
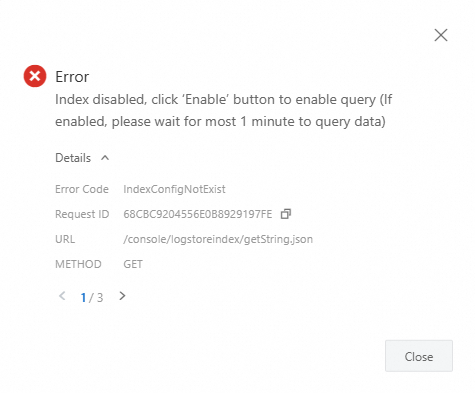
Field index
Index not created: An error is reported when you filter logs based on sampling results. Click Enable Index in the upper-right corner of the page, then configure the index, tokenizers, and other settings in the Query and Analysis panel. For more information, see Create an index.
Index created but missing required fields: The query may return no results. Adjust the field configuration of the index to include the required fields.
Account permissions
If you use a Resource Access Management (RAM) user, the RAM user must have the AliyunLogReadOnlyAccess policy (read-only permission for Simple Log Service).