Data Security Center (DSC) assesses the security configuration compliance of your Object Storage Service (OSS) buckets. It checks whether configurations such as access control list (ACL) and encryption policies are in place, and flags any detected risks with remediation guidance.
How it works
DSC runs a security baseline check against the Alibaba Cloud Data Security Best Practices policy. The policy covers seven security domains for OSS buckets. When a check item fails, DSC surfaces the risk and links directly to the relevant OSS configuration page so you can remediate it.
The end-to-end workflow has four steps:
Create an OSS bucket.
Add the bucket to DSC and enable configuration risk checks.
Run a baseline check manually.
Review the results and fix any configuration risks.
Security baseline check items
The following table lists all OSS baseline check items, grouped by security domain.
| Security domain | Check item | Fails when |
|---|---|---|
| Data storage security | OSS-enable Bucket server-side encryption | Server-side encryption is not enabled for the bucket. |
| Data backup and recovery | OSS-enable Bucket version control | Versioning is not enabled for the bucket. |
| Access control management | OSS-configure an access source IP address whitelist | The bucket is publicly exposed. |
| Data transmission encryption | OSS-enable secure encrypted transmission | Encrypted transmission is not enforced for objects during transfer. |
| Log monitoring audit | OSS-enable log storage | Log storage is not enabled for the bucket. |
| Identity rights management | OSS-anonymous account "read/write/full control" permission configuration | The bucket is configured with public-read-write permissions, violating the principle of least privilege. |
| Sensitive data protection | OSS-log file public read (write) access permission settings; OSS-sensitive data Bucket public read (write) Access Check | Log files have public read/write access, or a bucket containing sensitive data lacks access control. |
If sensitive data detection has not been run on a bucket, the OSS-sensitive data Bucket public read (write) Access Check item passes by default.
Prerequisites
Before you begin, ensure that you have:
Activated the Free Edition of Data Security Center and granted DSC the permissions to access other Alibaba Cloud resources
Activated Object Storage Service (OSS) for your account
The Free Edition of DSC includes the baseline check feature and supports check items in the Alibaba Cloud Data Security Best Practices policy. It provides 500 TB of free OSS protection per month. The PIPL Security Baseline policy requires an Enterprise instance of DSC.
Step 1: Create an OSS bucket
In the OSS console, go to the Buckets page and click Create Bucket.
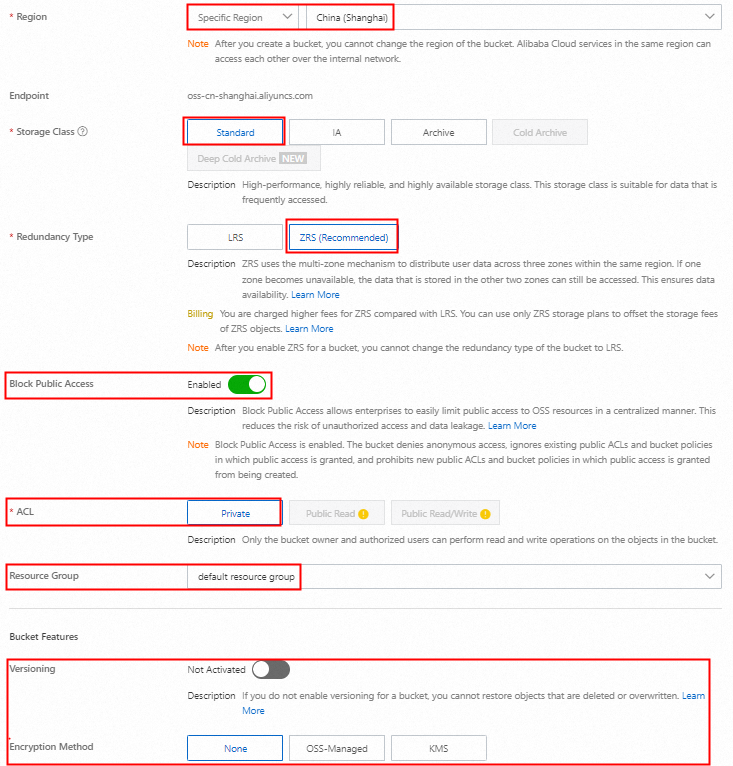
In the Create Bucket panel, configure the required parameters, leave the other parameters at their defaults, and click Create.
Step 2: Add the OSS bucket to DSC
Log on to the Data Security Center console.
In the left navigation pane, click Asset Center.
In the Unstructured Data area, click OSS, and then click Asset synchronization.

After synchronization completes, find the bucket and turn on the Configuration Risks switch. Wait until the Connection Status changes to Connected.

Step 3: Run a baseline check manually
By default, DSC runs a baseline check on connected assets at approximately 01:00 every day. To view results immediately, trigger the check manually.
Confirm that the check policy is enabled
In the left navigation pane, choose Risk Governance > Configuration Risks.
On the Policies > Alibaba Cloud Data Security Best Practices tab, review the OSS-related check items and their status. By default, DSC enables all check items in the policy.

Confirm that the status column for each OSS check item shows the enabled icon
 .
.
Trigger checks for each item
Go to Risk Trends > Alerts, find the target policy, and click Details in the Actions column.
On the Risk Situation tab, click Check for each OSS-related check item. The check is complete when the Check button becomes active again. Close the panel when done.

Repeat for any remaining check items under different policies.
Step 4: Review and fix security risks
View check results
On the Asset Risks tab, search for the bucket to view its check results. The detection time shows when the last check ran.
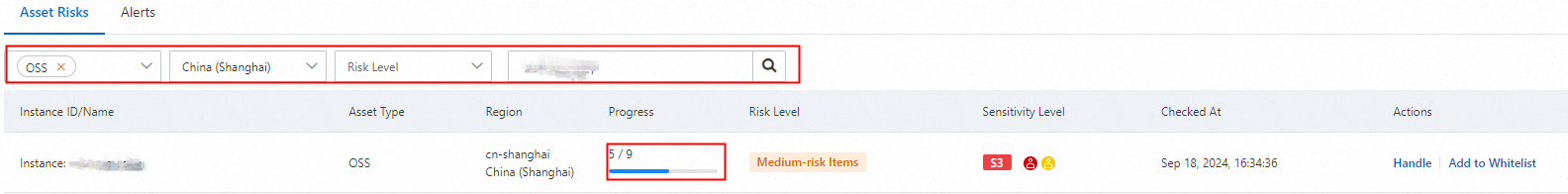
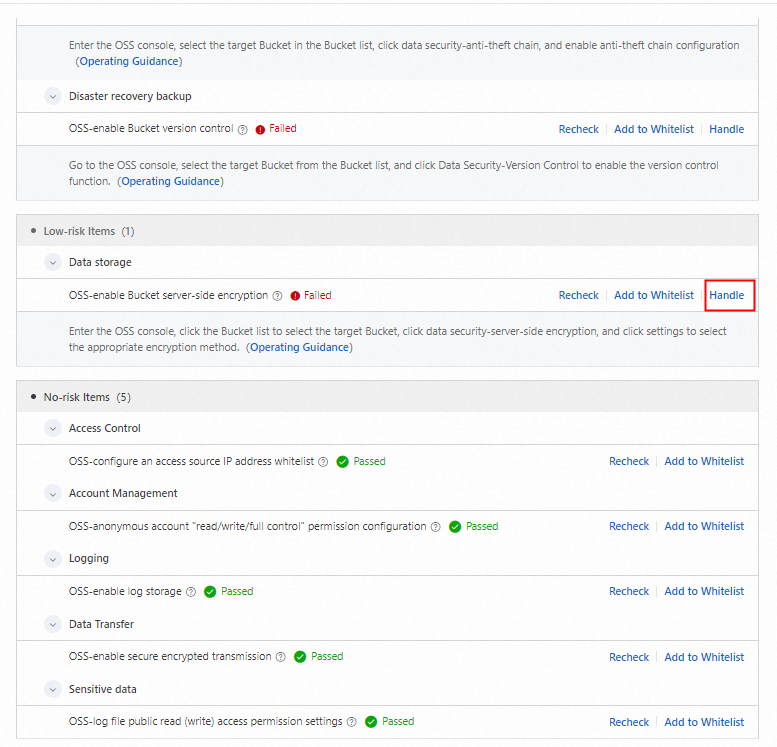
Click Handle in the Actions column to see which check items failed and the recommended fixes.
Fix a risk item
In the Risk Details area, click Handle. DSC navigates to the relevant OSS configuration page. For example, to fix OSS-enable Bucket server-side encryption: on the Server-side Encryption page, click Settings, set the encryption method to OSS-Managed, and click Save. For configuration details, see Server-side encryption.

Verify the fix
Return to the risk details panel in DSC and click Recheck.
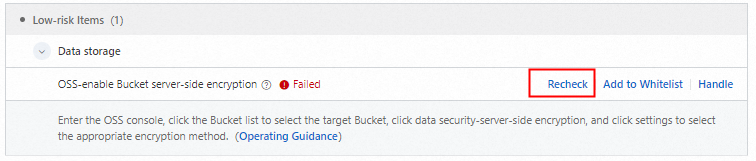
A passed result confirms the risk item is resolved.
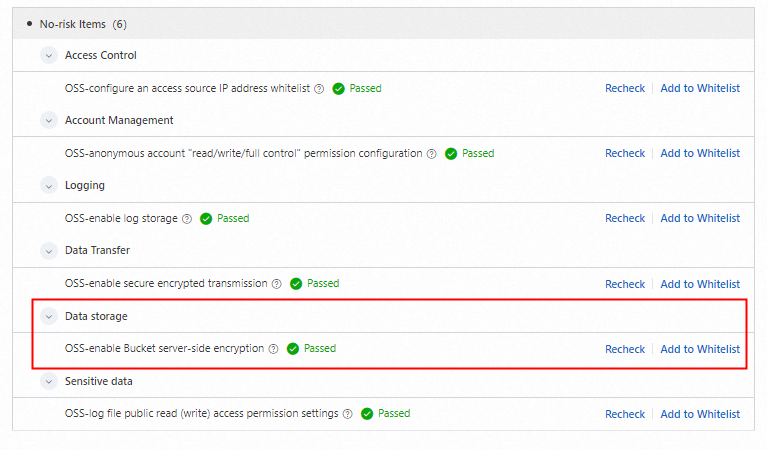
Repeat this process for all remaining risk items.
After you store data in the bucket
Complete the security configuration compliance check above before storing data in a bucket. Once you have data in the bucket, take these additional steps to stay compliant.
Set up sensitive data detection
The OSS-sensitive data Bucket public read (write) Access Check item passes by default for buckets where sensitive data has not been detected. After storing data, create a sensitive data detection task to periodically scan the bucket. If DSC finds sensitive data, it runs the OSS-sensitive data Bucket public read (write) Access Check baseline check, letting you catch and fix any related risks promptly.
For details on creating a detection task, see Scan for sensitive data using a detection task.
The Free Edition of DSC provides 5 GB of free OSS data detection per month. If this quota does not meet your needs, purchase a paid instance of DSC. For pricing information, see Purchase DSC.
Add assets to the whitelist
If a failed check for a specific asset is acceptable for your use case, go to the Asset Risks tab, find the asset, and click Add to Whitelist in the Actions column. This excludes the asset from that check item.
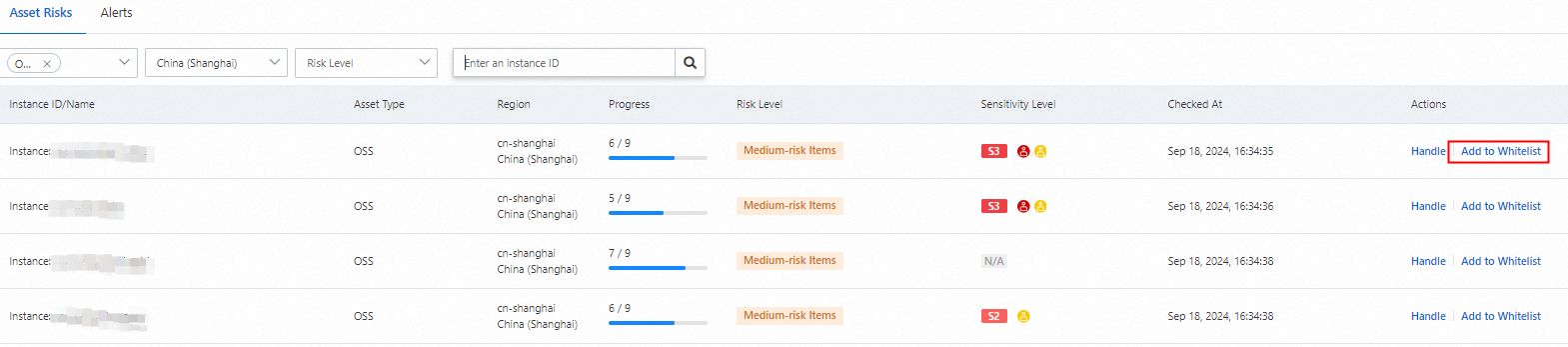
Whitelist management requires an Enterprise instance of DSC. The Free Edition does not support this feature.