DDoS attacks can slow down domain name resolution or cause service interruptions. The Anti-DDoS Protection feature of Alibaba Cloud DNS protects your domain names and ensures the availability of the domain name resolution service.
Protection levels
Alibaba Cloud DNS offers two protection levels. You can choose a protection level that meets your business needs.
Protection level | Mitigation capabilities | Scenarios |
DNS Anti-DDoS Basic | Protects all domain names in the instance from DNS attacks, with a mitigation capacity of up to 10 million queries per second (QPS). | Suitable for services that experience moderate-intensity DNS attacks. |
DNS Anti-DDoS Advanced | Protects all domain names in the instance from DNS attacks and can mitigate large-scale DNS query attacks that exceed 100 million QPS. | Suitable for core services that require high business continuity, such as finance, gaming, and e-commerce, or services that frequently face large-scale attacks. |
Scope
This feature is available only for paid instances of Alibaba Cloud DNS. If your domain name currently uses the Free Edition, you must upgrade to a paid edition to enable this protection.
Enable Anti-DDoS Protection
Go to Public Zone DNS Firewall.
The Anti-DDoS Protection tab is selected by default. This tab displays a list of domain names that are managed by Public Zone.
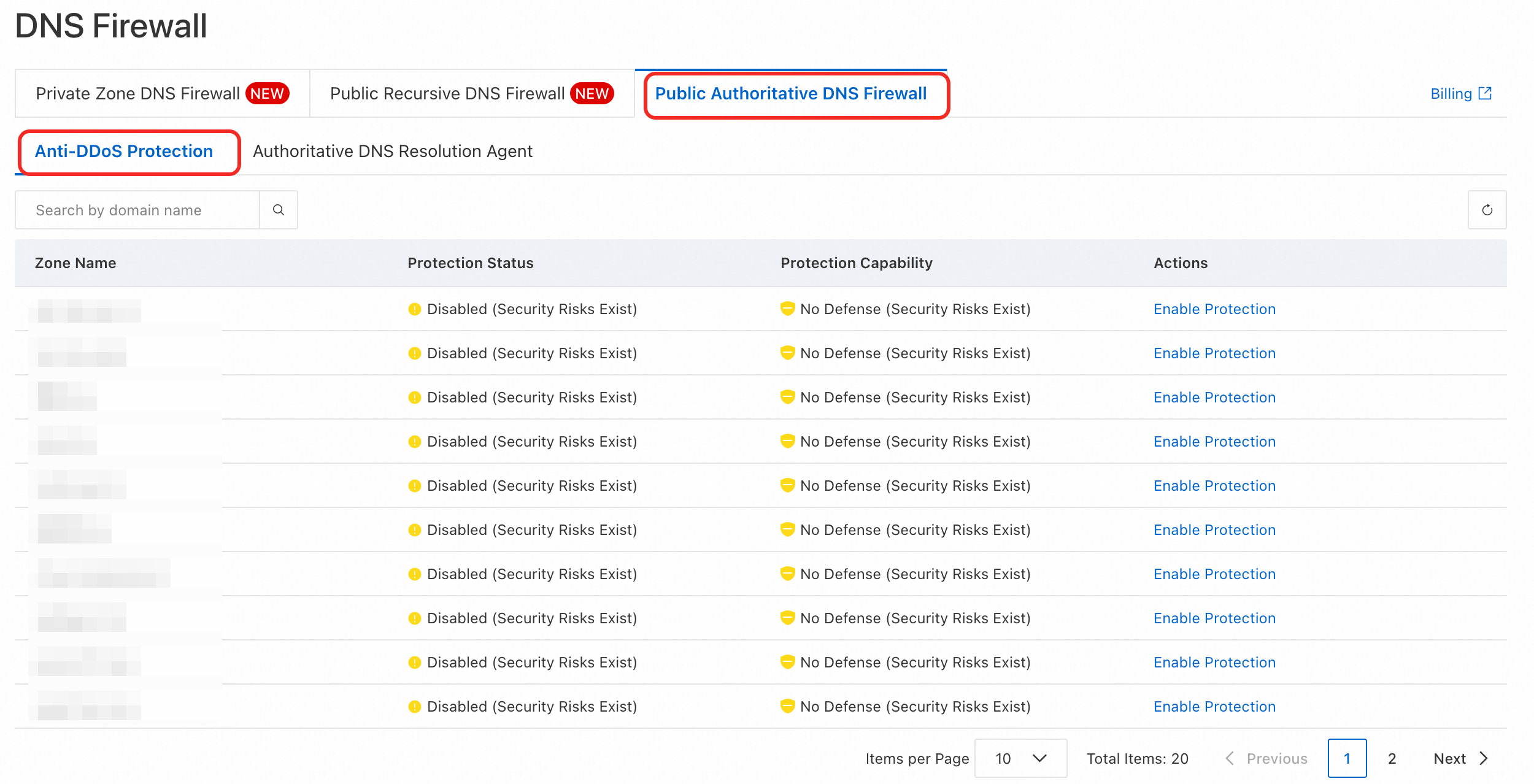
Find the domain name that you want to protect and click Enable Protection in the Actions column. In the panel that appears, select the required specifications and complete the purchase.
Scenario 1: The domain name uses the Free Edition of Public Zone
You must upgrade the resolution service to a paid edition and then select a DNS protection level.
In the edition selection panel, select a paid edition of Public Zone.
In the DNS Security section, select DNS Anti-DDoS Basic or DNS Anti-DDoS Advanced.
Confirm the order information and complete the purchase.
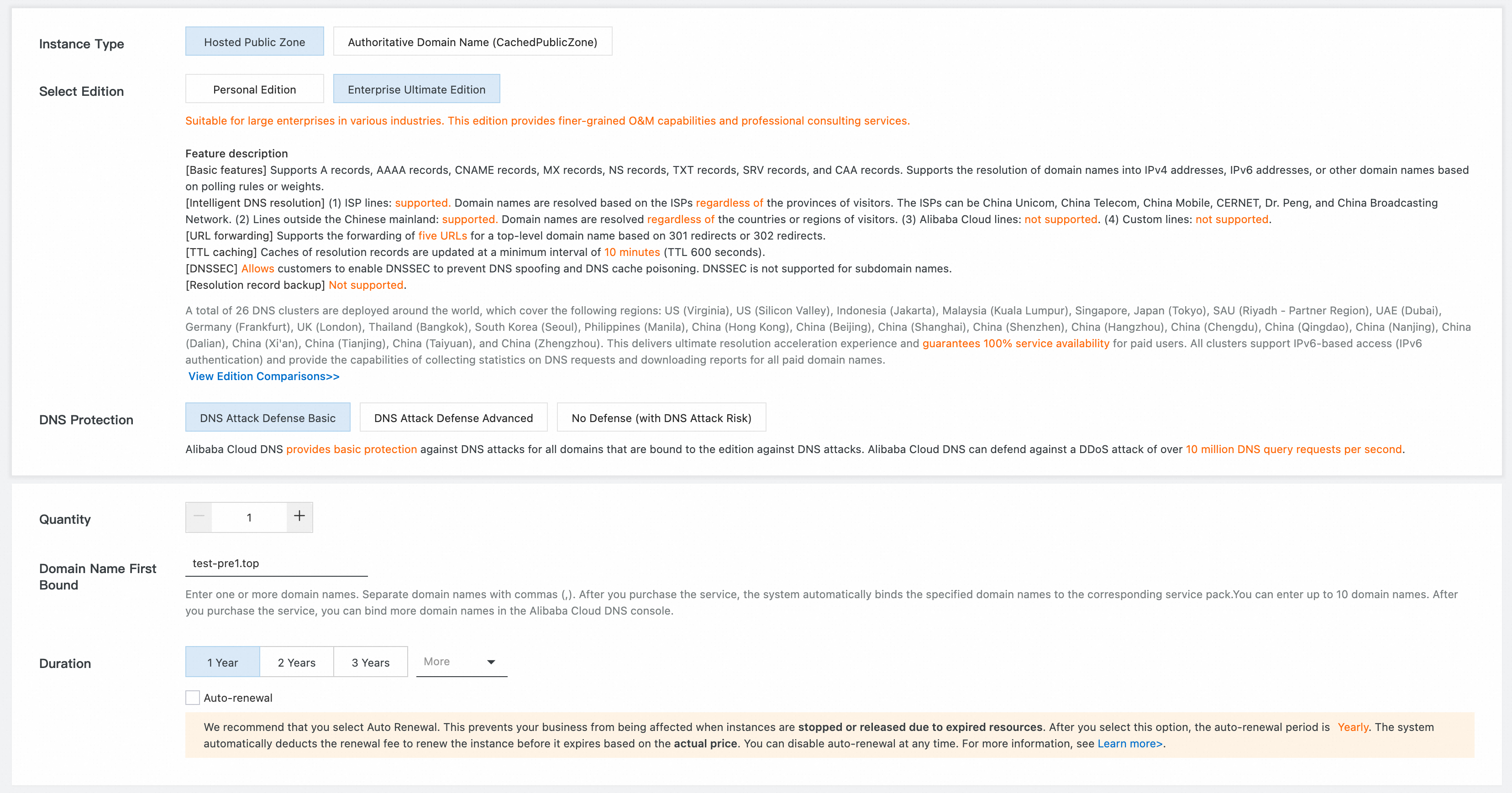
Scenario 2: The domain name already uses a paid edition of Public Zone
You can purchase and add the DNS protection feature directly. Note: The subscription duration of the protection feature is aligned with the remaining subscription duration of your Public Zone instance. The cost is prorated based on the remaining duration.In the DNS Security section of the edition selection panel, select DNS Anti-DDoS Basic or DNS Anti-DDoS Advanced.
Confirm the order information and complete the purchase.
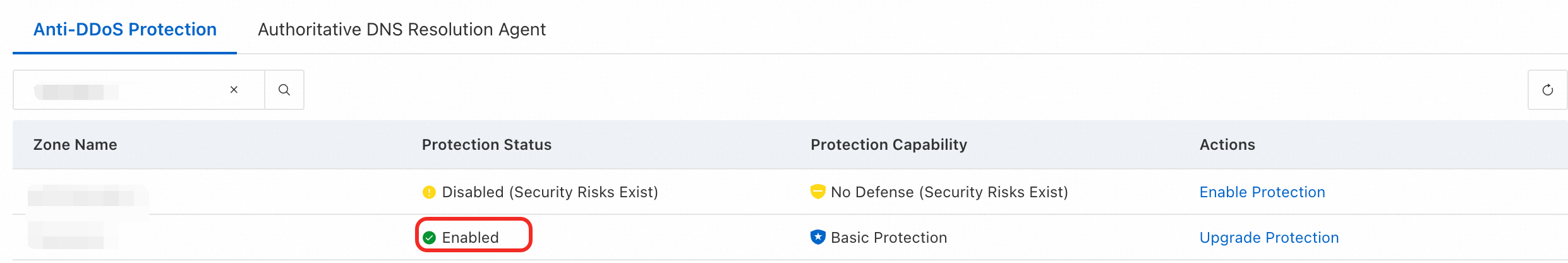
Return to the Anti-DDoS Protection page. The Protection Status for the domain name is now Enabled.
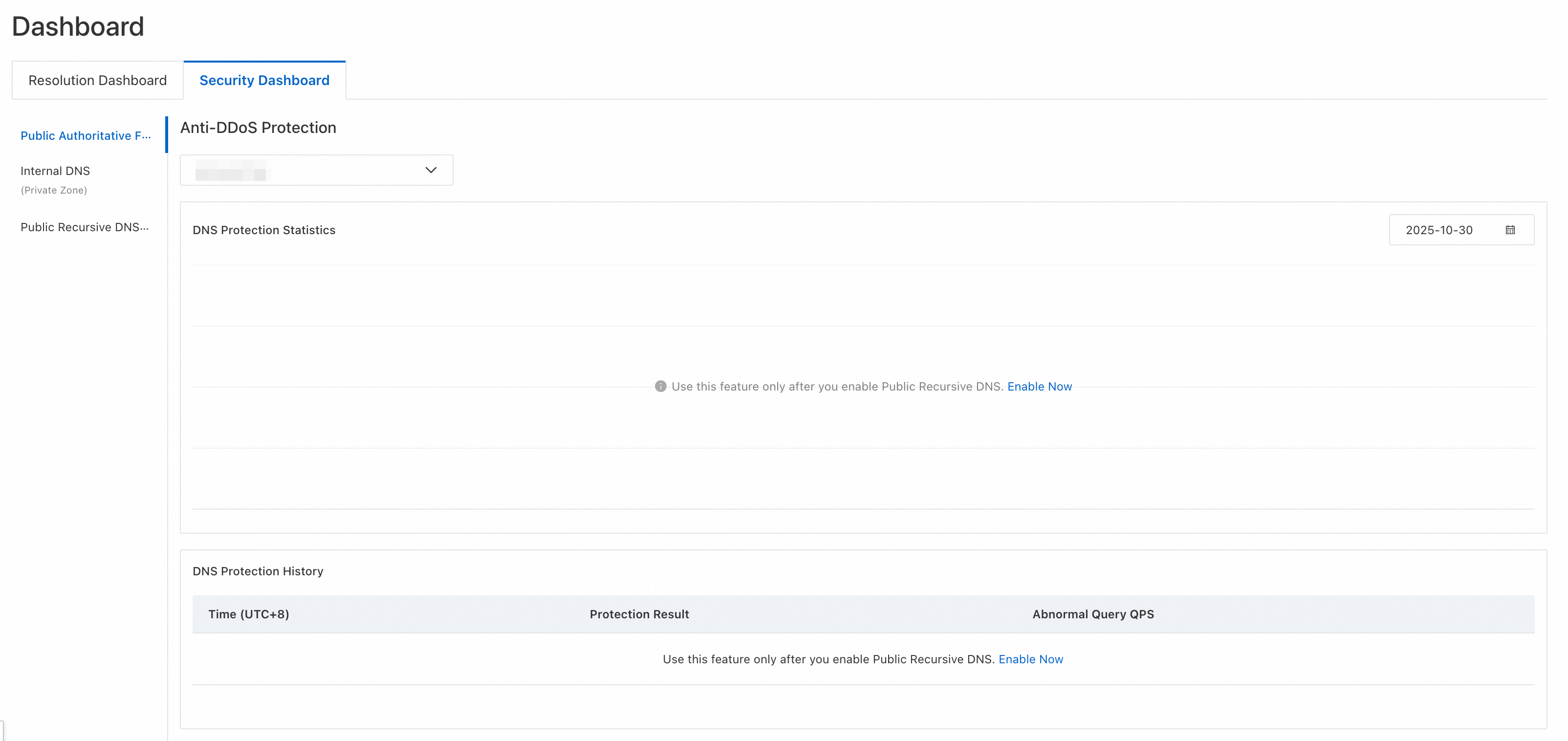
View the security dashboard
After you enable protection, you can monitor the security status of your domain names and view attack data and history on the Security Dashboard page.
Click Public Zone DNS Firewall and select the target domain name. You can view information such as the domain name resolution status, the DNS Protection Statistics graph, which shows data for the last 7 days, and the DNS Protection History log.
Domain Name Resolution Status: If the domain name is under a DNS attack, this section displays alert information. You will also receive a notification by text message or email.
DNS Protection Statistics: If the domain name is under a DNS attack, this section displays a trend graph of the queries per second (QPS) for abnormal requests.
DNS Protection History: In the history log, you can view the Time (UTC+8), Protection Result, and Abnormal Query QPS.
Billing
Anti-DDoS Protection is a value-added service that requires a separate purchase. For more information, see Product Billing.
If you purchase the protection feature for a domain name that is already attached to a paid Public Zone instance, the subscription duration of the new feature is aligned with the remaining subscription duration of the instance. The cost is prorated to ensure that both services expire at the same time.
If you also need to purchase a paid edition of the Public Zone service, see Product Billing.
Protection statuses
During a DNS query attack, the protection status of a domain name can be one of the following: Traffic Scrubbing Started, Traffic Scrubbing Ended, Blackhole Filtering Started, or Blackhole Filtering Ended.
Traffic Scrubbing Started: If the DNS security system detects that a custom domain name is subject to a sustained, high volume of abnormal requests, it enables the traffic scrubbing policy. This policy blocks abnormal DNS queries.
Traffic Scrubbing Ended: If the DNS security system detects a decrease in abnormal requests to the custom domain name, it disables the traffic scrubbing policy.
Blackhole Filtering Started: If the DNS security system detects that a custom domain name is under a sustained, high volume of abnormal requests that exceeds the mitigation capacity of the current edition, it stops the resolution service for that domain name.
Blackhole Filtering Ended: During blackhole filtering, if the DNS security system detects that the abnormal requests to the custom domain name have dropped to a level within the mitigation capacity, it automatically resumes the resolution service. After the service resumes, the changes take effect after the TTL expires.