Associating a RAM role with an individual development environment lets you access other Alibaba Cloud services using short-lived credentials issued by Security Token Service (STS), instead of hardcoding a long-term AccessKey pair. The credentials rotate automatically, which reduces the risk of credential leaks.
Limitations
Each individual development environment supports only one associated RAM role.
Before you begin
Review the following scenarios to determine the right approach for your environment:
| Scenario | Recommended approach | Notes |
|---|---|---|
| Using Notebook or Python in DataWorks to access MaxCompute, Hologres, EMR Serverless Spark, Realtime Compute for Apache Flink, or Platform for AI (PAI) | Associate the DataWorks default role | No RAM role creation required |
| Individual development environment is set to public in the workspace | Do not associate a RAM role | Prevents unintended permission leaks; use an AccessKey pair in your code instead |
| Accessing services beyond the default role's scope | Associate a custom RAM role | Create a RAM role whose trusted entity is an Alibaba Cloud service |
Step 1: Associate a RAM role with an individual development environment
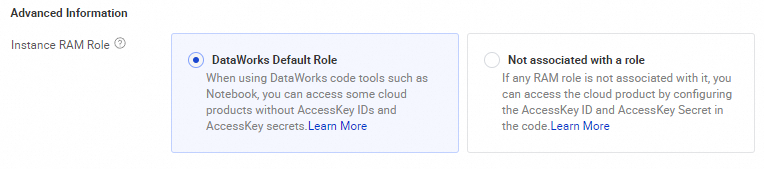
Scenario 1: Associate the DataWorks default role
The DataWorks default role grants the permissions of the individual development environment owner to access the following services: MaxCompute, Hologres, EMR Serverless Spark, Realtime Compute for Apache Flink, and Platform for AI (PAI). No role creation is required.
After associating the default role, you can perform the following operations without configuring an AccessKey pair:
-
Use an SQL cell of Notebook to access MaxCompute, Hologres, EMR Serverless Spark, Realtime Compute for Apache Flink, or PAI.
-
Use MaxCompute SDK to submit a task to a MaxCompute project on which the owner of the individual development environment has execution permissions.
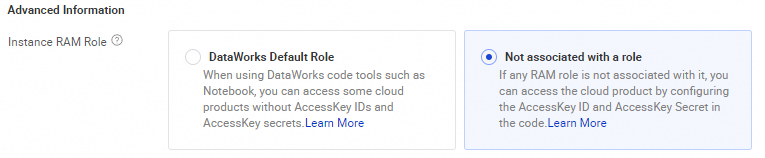
Scenario 2: Do not associate a RAM role
If the individual development environment is set to public in the workspace, do not associate a RAM role. This prevents unintended permission leaks. When creating or reconfiguring the environment, set RAM Role in the Advanced Information section to Do Not Associate Role, then configure an AccessKey pair directly in your code.
Step 2: Get a temporary access credential
Note: All three methods below rely on a local service that is automatically injected when the individual development environment is created. They only work inside the individual development environment. Running this code locally or in another environment will fail.
Choose one of the following methods to get a temporary access credential from the RAM role associated with your individual development environment.
Method 1: Use the Alibaba Cloud Credentials tool (recommended)
The Credentials tool calls the injected local service to fetch a temporary access credential and rotates it automatically.
Install the Credentials tool:
pip install alibabacloud_credentialsUse the Credentials tool to get credentials:
from alibabacloud_credentials.client import Client as CredClient
from alibabacloud_credentials.models import Config as CredConfig
credentialsConfig = CredConfig(
type='credentials_uri' # Fetches a temporary access credential via the injected URI.
# If no other credential source is configured in the default
# credential chain, omit this parameter.
)
credentialsClient = CredClient(credentialsConfig)For SDK examples in other languages, see Best practices for using an access credential to call API operations.
Method 2: Query the local service endpoint
Run the following command in the terminal of your individual development environment:
# Retrieve a temporary access credential for the RAM role.
curl $ALIBABA_CLOUD_CREDENTIALS_URIA successful response looks like this:
{
"Code": "Success",
"AccessKeyId": "STS.N*********7",
"AccessKeySecret": "3***************d",
"SecurityToken": "DFE32G*******",
"Expiration": "2024-05-21T10:39:29Z"
}| Field | Description |
|---|---|
SecurityToken |
Temporary token for the RAM role |
Expiration |
UTC expiration time of the credential |
Method 3: Read the local credentials file
Read the credentials file at /mnt/.alibabacloud/credentials. The file contains the same fields as the response in Method 2:
{
"AccessKeyId": "STS.N*********7",
"AccessKeySecret": "3***************d",
"SecurityToken": "DFE32G*******",
"Expiration": "2024-05-21T10:39:29Z"
}Step 3: Access MaxCompute using the RAM role
-
Install the Credentials tool and MaxCompute SDK:
# Install the Credentials tool. pip install alibabacloud_credentials # Install MaxCompute SDK. pip install odps -
Use the RAM role's temporary access credential to list tables in a MaxCompute project:
from alibabacloud_credentials import providers from odps.accounts import CredentialProviderAccount from odps import ODPS if __name__ == '__main__': account = CredentialProviderAccount(providers.DefaultCredentialsProvider()) o = ODPS( account=account, project="<odps_project>", # Replace with the name of the MaxCompute project to access. endpoint="<odps_endpoint>" # Replace with the endpoint of the region where the project resides. ) for t in o.list_tables(): print(t)Replace the following placeholders:
Placeholder Description <odps_project>Name of the MaxCompute project to access <odps_endpoint>Endpoint of the region where the project resides
What's next
-
To learn more about RAM roles and trusted entities, see RAM role overview.
-
To explore credential usage patterns in other languages, see Best practices for using an access credential to call API operations.