DAS Agent is an AI-powered database operations and maintenance (O&M) assistant built on Large Language Model (LLM) technology. Trained on over 100,000 Alibaba Cloud support tickets and expert knowledge, it provides end-to-end autonomous database O&M—from problem detection and diagnosis to optimization—using artificial intelligence for IT operations (AIOps).
What DAS Agent can do for you:
Diagnose faster: Identifies root causes of CPU spikes, slow SQL, lock contention, memory anomalies, and more across MySQL, PostgreSQL, Redis, MongoDB, SQL Server, and PolarDB-X.
Answer database questions: Draws on a knowledge base spanning general database knowledge and internal Alibaba Cloud expert documents, covering anomaly handling, upgrade and downgrade recommendations, and change impact analysis.
Deliver daily O&M reports: Generates a unified report across multiple instances and engines, covering metric trends, slow SQL, disk usage, invalid indexes, and CPU/memory/I/O usage.
All diagnostic recommendations currently require manual approval. Automatic execution by the LLM is not yet available.
Prerequisites
Before you begin, ensure that you have:
Connected your target database to DAS
DAS Agent supports the following database engines:
MySQL: RDS MySQL, PolarDB for MySQL, MySQL from other cloud vendors, and self-managed MySQL
PostgreSQL: RDS PostgreSQL, PolarDB for PostgreSQL, PostgreSQL from other cloud providers, and self-managed PostgreSQL
Redis: Tair (compatible with Redis), Redis from other cloud vendors, and self-managed Redis
MongoDB: ApsaraDB for MongoDB, MongoDB from other cloud vendors, and self-managed MongoDB
SQL Server: RDS SQL Server
Distributed: PolarDB-X
Usage notes
RAM users: RAM users must have management permissions for DAS and the database instance before using DAS Agent.
API integration: To integrate DAS Agent's AIOps capabilities into a non-DAS console or another business system, submit a ticket for consultation.
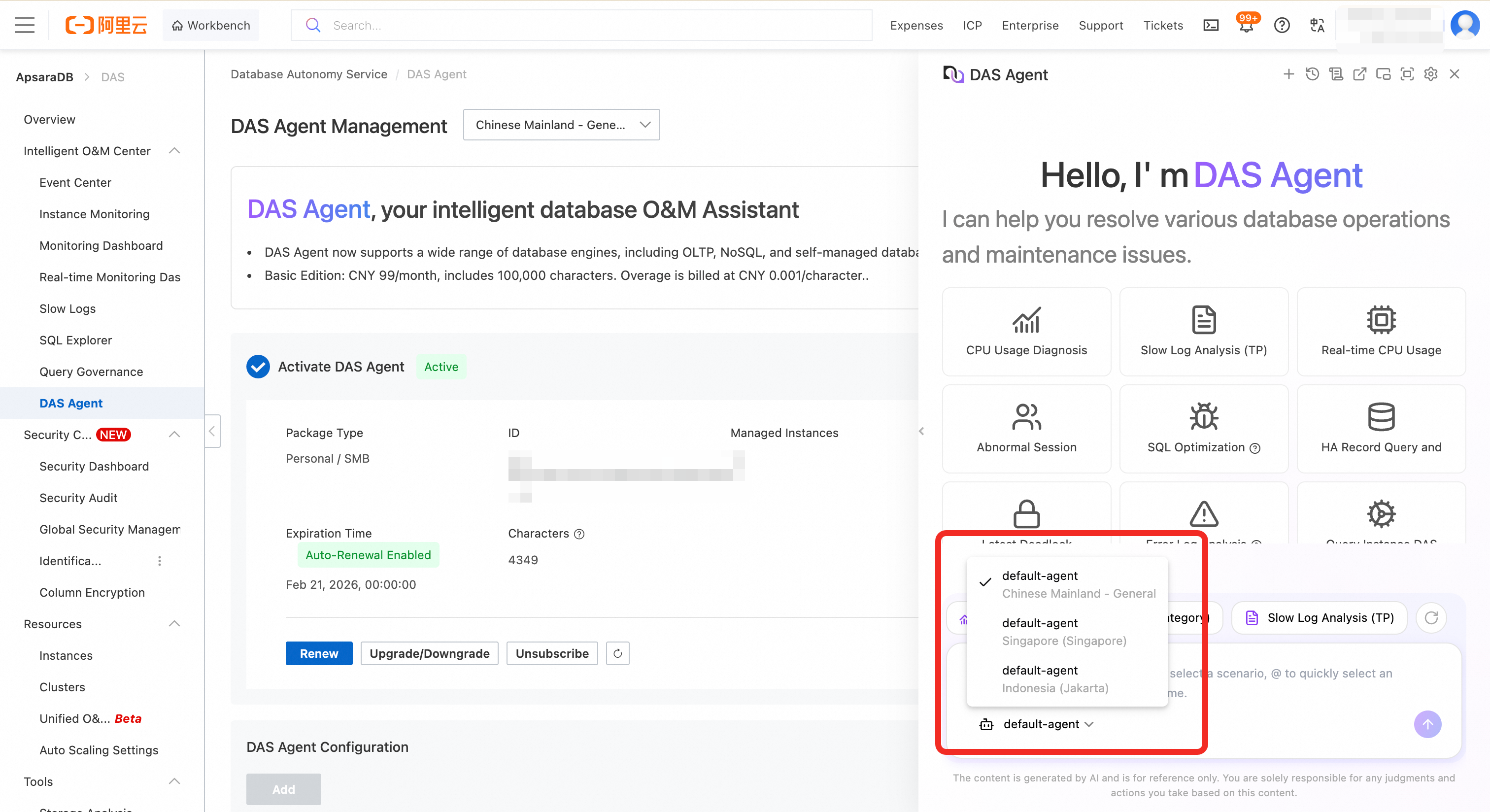
Regional isolation: Data security regulations prevent a single LLM service from managing instances across different countries and regions. If your instances span multiple regions, enable DAS Agent separately for each country or region. For example, instances in the Chinese mainland—such as Beijing, Shanghai, Hangzhou, and Guangzhou—share one DAS Agent. Instances in the United States, Singapore, and Indonesia each require separate activation.
Model routing outside the Chinese mainland: DAS Agent outside China relies on Alibaba Cloud Model Studio, which is currently deployed only in Singapore and the United States. Model calls are routed to the nearest of these two locations. As Model Studio expands to more countries and regions, DAS Agent will automatically migrate to the local service.
NoteThis routing applies only to Model Studio model calls. Database data—such as audit logs—always stays within the region where the instance is deployed.
Billing
For pricing details, see DAS Agent pricing.
Starting March 17, 2026, DAS Agent includes a daily free trial plan:
Basic quota:Each user gets 5,000 free characters per day. After the quota is used, upgrade to a commercial edition to continue.
Check-in bonus:Complete a daily check-in by viewing or querying the O&M Daily Report in the console. Each check-in grants 700 additional characters. Seven consecutive check-ins provide 4,900 extra characters total.
Quota tracking:Check your remaining daily quota and usage at any time on the console. The free quota policy is subject to change, including increases, decreases, or cancellation.
The free quota policy is subject to change, including increases, decreases, or cancellation.
Features
| Feature | Status | Description |
|---|---|---|
| Database Q&A | Supported | Answers questions using a knowledge base that spans general database knowledge and internal documents accumulated by senior Alibaba Cloud experts. Covers major OLTP and NoSQL engines, including anomaly handling, upgrade and downgrade recommendations, and change impact analysis. |
| Database anomaly diagnosis | Supported | Diagnoses anomalies across OLTP and NoSQL scenarios: metric and anomaly queries, real-time CPU and memory diagnosis, session analysis, lock analysis, latency insight (Tair), large key analysis (Tair), slow SQL analysis (OLTP and MongoDB), SQL optimization (executed and unexecuted), and security risk detection. DAS Agent identifies root causes and provides optimization and immediate remediation suggestions. Note Recommendations currently require manual approval. Automatic LLM execution is not yet available. |
| Intelligent O&M report | Supported | Generates a unified O&M report covering multiple instances across engines. Includes metric trend comparison, optimization suggestions, and monitoring recommendations. Note Only daily reports are currently available. Weekly and monthly reports and custom templates are planned for a future release. |
| Anomaly detection and alerting | Not supported | Planned: proactive anomaly detection based on performance trend metrics. |
Supported skills
DAS Agent provides skills across three categories: performance and diagnosis, instance management, and security.
Self-managed and other-cloud instances:For MySQL, PostgreSQL, Redis, or MongoDB engines from other cloud vendors or self-managed environments, DAS Agent supports diagnosis and optimization based on standard protocols. Vendor-specific custom features and non-standard modifications are not supported.
Sample API call format:The JSON samples below use a structured request body to trigger a specific skill directly when calling the API. Compared to natural language queries, this mode ensures stable and predictable execution of the target diagnostic task.
Performance and diagnosis
| Skill | Description | Supported cloud instances | Self-managed/other cloud | Required parameters | Sample API call |
|---|---|---|---|---|---|
| Real-time CPU diagnosis (MySQL) | Diagnoses abnormal CPU usage using real-time data. | RDS MySQL, PolarDB for MySQL | Not supported | Instance ID; Node ID (required for PolarDB for MySQL; primary node used by default) | {"operation_id":"high_cpu_usage_real_time_diagnose_mysql","input_parameters":{"instance_id":"xxxxxx","node_id":"xxxxxxxx"},"direct_mode":true} |
| Real-time CPU diagnosis (Tair/Redis) | Diagnoses abnormal CPU usage for Tair (compatible with Redis) instances, analyzing root causes from real-time session, large key, and hot key data. | Tair (compatible with Redis) | Not supported | Instance ID; Node ID (optional) | {"operation_id":"redis_cpu_diagnose_history_time","input_parameters":{"instance_id":"xxxxxxx","start_time":"2026-02-05T20:33:01+08:00","end_time":"2026-02-06T20:33:01+08:00"},"direct_mode":true} |
| CPU usage diagnosis (MySQL) | Diagnoses abnormal CPU usage for a specified time period using sessions, slow query logs, and SQL Explorer data. | RDS MySQL, PolarDB for MySQL | Not supported | Instance ID; Node ID (required for PolarDB for MySQL; primary node used by default); Time range (start_time and end_time) | {"operation_id":"performance_diagnose_mysql","input_parameters":{"instance_id":"xxxxxx","node_id":"xxxxxxxx","start_time":"2026-02-05T20:32:07+08:00","end_time":"2026-02-06T20:32:07+08:00"},"direct_mode":true} |
| SQL diagnosis and optimization | Analyzes SQL statements for performance issues based on the database engine version, table schema, indexes, execution plan, and SQL script. Also supports pre-checks for unreleased SQL statements. | RDS MySQL, RDS PostgreSQL, PolarDB for MySQL, PolarDB for PostgreSQL | MySQL and PostgreSQL engines | Instance ID; Database; SQL script; Search_path (optional, for PostgreSQL) | {"operation_id":"mysql_query_optimization_advisor","input_parameters":{"instance_id":"xxxxxxx","database":"xxxxxxx","sql":"xxxxxxxxxx"},"direct_mode":true} |
| Slow log analysis (TP) | Identifies problematic SQL statements from slow query log statistics and provides optimization suggestions. | RDS MySQL, RDS SQL Server, RDS PostgreSQL, PolarDB for MySQL, PolarDB for PostgreSQL, PolarDB-X | Not supported | Instance ID; Node ID (required for PolarDB for MySQL; primary node used by default); Time range (start_time and end_time); Top N records | {"operation_id":"sql_slowlog_summary","input_parameters":{"instance_id":"xxxxxxx","node_id":"xxxxxxxx","start_time":"2026-02-05T20:34:16+08:00","end_time":"2026-02-06T20:34:16+08:00","top_n":"x"},"direct_mode":true} |
| Slow log analysis (MongoDB) | Identifies problematic query templates from MongoDB slow query log statistics and recommends QueryIDs that require attention. | ApsaraDB for MongoDB | Not supported | Instance ID; Node ID (optional); Time range (start_time and end_time); Top N records | {"operation_id":"mongodb_slowlog_summary","input_parameters":{"instance_id":"xxxxx","node_id":"xxxxxxx","start_time":"2026-02-05T20:33:28+08:00","end_time":"2026-02-06T20:33:28+08:00","top_n":"x"},"direct_mode":true} |
| Monitoring metric query | Queries instance metrics such as CPU usage, memory usage, and storage space usage. | RDS MySQL, RDS PostgreSQL, PolarDB for MySQL, PolarDB for PostgreSQL | Not supported | Instance ID; Node ID (required for PolarDB for MySQL; primary node used by default) | {"operation_id":"monitoring_indicator_query_tool","input_parameters":{"instance_id":"xxxxx","node_id":"xxxxxxx"},"direct_mode":true} |
| Key performance metric summary | Queries and summarizes key performance metrics for an instance within a specified time range. Use a smaller time range to avoid failures from large data volumes. | RDS MySQL, RDS SQL Server, RDS PostgreSQL, PolarDB for MySQL, PolarDB-X, Tair (compatible with Redis), ApsaraDB for MongoDB | Not supported | Instance ID; Node ID (optional); Time range (start_time and end_time) | {"operation_id":"important_performance_metrics_summary","input_parameters":{"instance_id":"xxxxxxx","node_id":"xxxxxxxx","start_time":"2026-02-05T20:30:08+08:00","end_time":"2026-02-06T20:30:08+08:00"},"direct_mode":true} |
| Recent deadlock analysis | Analyzes the latest deadlock log from the output of SHOW ENGINE INNODB STATUS. | RDS MySQL, PolarDB for MySQL | MySQL engines | Instance ID; Node ID (required for PolarDB for MySQL; primary node used by default) | {"operation_id":"latest_deadlock_analysis","input_parameters":{"instance_id":"xxxxxxx","node_id":"xxxxxxxxx"},"direct_mode":true} |
| Metadata lock and transaction blocking analysis | Analyzes metadata locks and transaction blocking in the current session. For RDS MySQL 8.0 and PolarDB for MySQL 8.0, enable Performance Schema before use. | RDS MySQL, PolarDB for MySQL | Not supported | Instance ID; Node ID (required for PolarDB for MySQL; primary node used by default) | {"operation_id":"lock_analysis","input_parameters":{"instance_id":"xxxxxx","node_id":"xxxxxxxx"},"direct_mode":true} |
| Storage analysis | Queries instance, database, and table information. Provides a space usage overview and a list of items to optimize. | RDS MySQL, RDS PostgreSQL, PolarDB for MySQL, PolarDB for PostgreSQL, PolarDB for PostgreSQL (Compatible with Oracle), PolarDB-X, ApsaraDB for MongoDB | MySQL and PostgreSQL engines | Instance ID; Node ID | {"operation_id":"storage_analyze","input_parameters":{"instance_id":"xxxxxx","node_id":"xxxxxxxx"},"direct_mode":true} |
| SQL Server storage analysis | Queries storage space usage for SQL Server instances and analyzes storage anomalies. | RDS SQL Server | Not supported | Instance ID | {"operation_id":"sqlserver_storage_analysis","input_parameters":{"instance_id":"rxxxxxxxxx"},"direct_mode":true} |
| Latency insight analysis (Tair/Redis) | Analyzes proxy node and data node latency from Tair (compatible with Redis) instances and identifies high-latency commands or nodes. Maximum analysis window: 30 minutes. | Tair (compatible with Redis) | Not supported | Instance ID; Node ID (required); Time range (start_time and end_time, max 30 minutes) | {"operation_id":"redis_latency_log_summary","input_parameters":{"instance_id":"xxxxxx","node_id":"xxxxxxxxx","start_time":"2026-02-05T20:37:03+08:00","end_time":"2026-02-06T20:37:03+08:00"},"direct_mode":true} |
| Large key query and analysis | Analyzes historical large keys for Tair (compatible with Redis) instances and returns information about corresponding hot keys. | Tair (compatible with Redis) | Not supported | Instance ID; Node ID (optional); Time range (start_time and end_time) | {"operation_id":"tair_history_large_key_query_and_analysis","input_parameters":{"instance_id":"xxxxxx","node_id":"xxxxxx","start_time":"2026-02-05T20:37:19+08:00","end_time":"2026-02-06T20:37:19+08:00"},"direct_mode":true} |
| Abnormal session identification | Queries information_schema.processlist and information_schema.innodb_trx in real time to identify abnormal sessions. | RDS MySQL, PolarDB for MySQL | MySQL engines | Instance ID; Node ID (required for PolarDB for MySQL; primary node used by default) | {"operation_id":"real_time_abnormal_session_identification","input_parameters":{"instance_id":"xxxxxxx","node_id":"xxxxxxxx"},"direct_mode":true} |
| Memory anomaly diagnosis (MySQL) | Analyzes whether memory usage is abnormal. If anomalies are found, identifies causes. If none are found, flags potential risks. | RDS MySQL, PolarDB for MySQL | Not supported | Instance ID; Node ID (required for PolarDB for MySQL; primary node used by default) | {"operation_id":"memory_usage_anomaly_diagnosis","input_parameters":{"instance_id":"xxxxxx","node_id":"xxxxxxx","start_time":"2026-02-05T20:38:58+08:00","end_time":"2026-02-06T20:38:58+08:00"},"direct_mode":true} |
| Memory anomaly identification (MySQL) | Identifies whether memory usage is abnormal or persistently high, and provides common causes. | RDS MySQL, PolarDB for MySQL | Not supported | Instance ID; Node ID (required for PolarDB for MySQL; primary node used by default) | {"operation_id":"memory_usage_anomaly_identification","input_parameters":{"instance_id":"xxxxxxx"},"direct_mode":true} |
| HA query and analysis | Queries and analyzes primary/secondary switchover records for an RDS MySQL instance, then outputs a concise report. | RDS MySQL | Not supported | Instance ID; Time range (start_time and end_time) | {"operation_id":"HA_records_query_and_diagnosis","input_parameters":{"instance_id":"xxxxxx","start_time":"2026-02-05T20:27:17+08:00","end_time":"2026-02-06T20:27:17+08:00"},"direct_mode":true} |
| Auto-increment ID overflow risk | Queries auto-increment ID usage to identify overflow risk. | RDS MySQL, PolarDB for MySQL | Not supported | Instance ID (optional); DB_NAMES; RATIO_FITER; REAL_TIME | {"operation_id":"auto_increment_usage_analyze","input_parameters":{"instance_id":"xxxxx"},"direct_mode":true} |
| Error log analysis | Analyzes deadlock, Warning, and Error entries in the database error log. Returns detailed deadlock information and causes. Important Enable | RDS MySQL, PolarDB for MySQL | Not supported | Instance ID; Node ID (required for PolarDB for MySQL; primary node used by default); Time range (start_time and end_time) | {"operation_id":"error_log_query_and_analysis","input_parameters":{"instance_id":"xxxxx","node_id":"xxxxx","start_time":"2026-02-05T20:29:05+08:00","end_time":"2026-02-06T20:29:05+08:00"},"direct_mode":true} |
Instance management
| Skill | Description | Supported cloud instances | Self-managed/other cloud | Required parameters | Sample API call |
|---|---|---|---|---|---|
| Overview of instances to be optimized | Lists instances under your account that require attention, including those with payload changes, sudden CPU spikes, sudden I/O spikes, high IOPS, memory spikes, or abnormal slow SQL counts. | RDS MySQL, RDS SQL Server, RDS PostgreSQL, PolarDB for MySQL, PolarDB for PostgreSQL, PolarDB-X, Tair (compatible with Redis), ApsaraDB for MongoDB | Not supported | Time range (start_time and end_time) | {"operation_id":"query_the_instances_that_need_to_be_optimized","input_parameters":{"start_time":"2026-02-05T20:38:24+08:00","end_time":"2026-02-06T20:38:24+08:00"},"direct_mode":true} |
| Instance information query | Queries instance details including engine type, engine version, instance ID, alias, region, and status. Filter by engine type or keyword. | RDS MySQL, RDS SQL Server, RDS PostgreSQL, PolarDB for MySQL, PolarDB for PostgreSQL, PolarDB-X, Tair (compatible with Redis), ApsaraDB for MongoDB | MySQL, PostgreSQL, Redis, and MongoDB engines | Engine type (optional); Keyword (optional) | {"operation_id":"list_instances","input_parameters":{"engine":"mysql","keyword":"111"},"direct_mode":true} |
| Instance topology query | Queries the topology of a database instance and detailed information for each node. | RDS MySQL, RDS SQL Server, RDS PostgreSQL, PolarDB for MySQL, PolarDB for PostgreSQL, PolarDB-X, Tair (compatible with Redis), ApsaraDB for MongoDB | Not supported | Instance ID | {"operation_id":"instance_topology_query_tool","input_parameters":{"instance_id":"xxxxxxx"},"direct_mode":true} |
| Instance configuration query | Queries instance configuration and status, including log settings, storage policies (hot/cold), audit features, Performance Insight status, and migration and version support. | RDS MySQL, RDS SQL Server, RDS PostgreSQL, PolarDB for MySQL, PolarDB for PostgreSQL, PolarDB-X, Tair (compatible with Redis), ApsaraDB for MongoDB | Not supported | Instance ID | {"operation_id":"get_instance_config","input_parameters":{"instance_id":"xxxxxxx"},"direct_mode":true} |
| View table creation statement | Retrieves the CREATE TABLE statement for a specified table. | RDS MySQL, RDS PostgreSQL, PolarDB for MySQL, PolarDB for PostgreSQL, PolarDB for PostgreSQL (Compatible with Oracle) | MySQL and PostgreSQL engines | Instance ID; Node ID; Database; Table; Schema (required for PostgreSQL) | {"operation_id":"show_create_table","input_parameters":{"instance_id":"XXXXXX","node_id":"XXXXXX","database":"XXXX","table":"XXXX"},"direct_mode":true} |
Security
| Skill | Description | Supported cloud instances | Required parameters | Sample API call |
|---|---|---|---|---|
| Security anomaly events | Queries anomalous security events across your instances, including account cracking attempts, sensitive data downloads, abnormal logins, mass data deletion, and dictionary attacks. Helps identify threats and take protective action. | RDS MySQL, RDS PostgreSQL, PolarDB for MySQL, PolarDB for PostgreSQL, PolarDB-X | None | {"operation_id":"security_describe_abnormal_events","input_parameters":{},"direct_mode":true} |
| Security baseline changes | Queries security baseline change trends for an instance within a specified time range. Identifies risk improvements, deteriorations, and long-unresolved items, with remediation guidance. | RDS MySQL, PolarDB for MySQL, PolarDB-X | Instance ID; Time range (start_time and end_time) | {"operation_id":"security_baseline_change_analysis","input_parameters":{"instance_id":"xxxxx","start_time":"2026-02-05T20:46:22+08:00","end_time":"2026-02-06T20:46:22+08:00"},"direct_mode":true} |
| Latest security baseline | Retrieves the latest security baseline inspection results for all instances under your account. Provides a comprehensive view of security configuration status and remediation guidance. | RDS MySQL, PolarDB for MySQL, PolarDB-X | None | {"operation_id":"security_latest_baseline_analysis","input_parameters":{},"direct_mode":true} |
| Sensitive data discovery | Queries sensitive data scan results for all instances under your account, including data classification and risk level. Supports data security management and compliance checks. | RDS MySQL, RDS PostgreSQL, PolarDB for MySQL, PolarDB for PostgreSQL, PolarDB-X | None | {"operation_id":"security_sensitive_scan_lookup","input_parameters":{},"direct_mode":true} |
| Global security risk trend | Queries and analyzes the time trend of global database security risks using histogram data. Identifies risk fluctuation patterns and abnormal peaks. | RDS MySQL, RDS SQL Server, RDS PostgreSQL, PolarDB for MySQL, PolarDB for PostgreSQL, PolarDB-X | None | {"operation_id":"describe_global_security_risk_histogram","input_parameters":{"start_time":"2026-02-05T20:43:09+08:00","end_time":"2026-02-06T20:43:09+08:00"},"direct_mode":true} |
| Instance security risk trend | Queries and analyzes the security risk time trend for a single instance. Uses histogram data to identify fluctuation patterns across risk dimensions such as abnormal SQL operations, SQL injection, and data breaches. | RDS MySQL, RDS SQL Server, RDS PostgreSQL, PolarDB for MySQL, PolarDB for PostgreSQL, PolarDB-X | Instance ID | {"operation_id":"describe_security_risk_histogram","input_parameters":{"instance_id":"xxxxxx","start_time":"2026-02-05T20:44:37+08:00","end_time":"2026-02-06T20:44:37+08:00"},"direct_mode":true} |
| Instance security alert statistics | Queries SQL security alert statistics for a single instance within a specified time range. Includes distribution by alert level (critical, warning, informational) and alert type (SQL injection, data breach, abnormal operation, and more). | RDS MySQL, RDS SQL Server, RDS PostgreSQL, PolarDB for MySQL, PolarDB for PostgreSQL, PolarDB-X | Instance ID | {"operation_id":"describe_sql_security_alert_stats","input_parameters":{"instance_id":"xxxxx","start_time":"2026-02-05T20:45:41+08:00","end_time":"2026-02-06T20:45:41+08:00"},"direct_mode":true} |
Get started with DAS Agent
Step 1: Access DAS Agent
On a PC
Log on to the DAS console.
Click the DAS Agent icon.
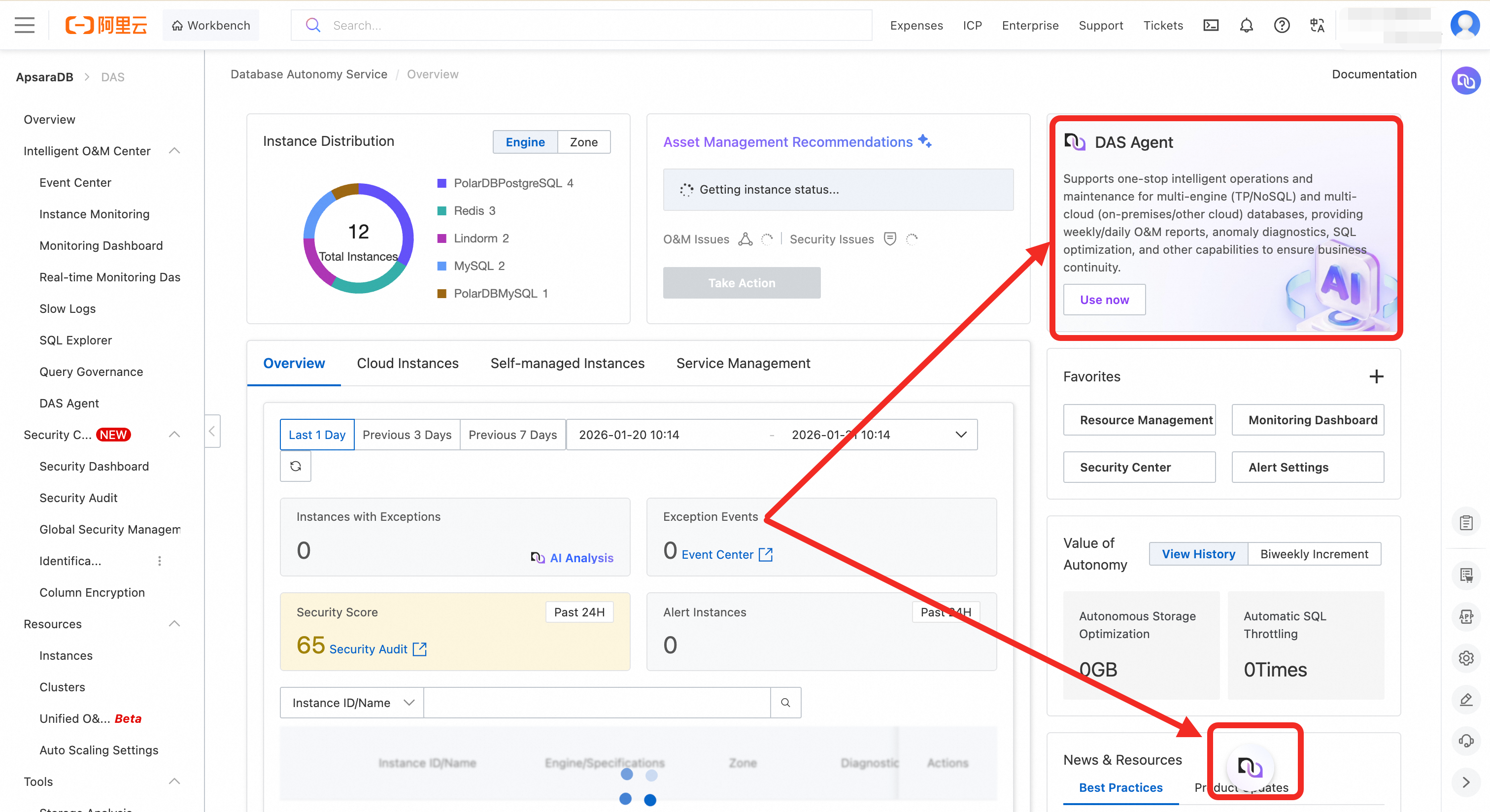
Select the appropriate instance type and complete the purchase. For specifications and billing details, see DAS Agent pricing.
Mobile Web
Access and log on to the DAS Agent page.
Mobile web access is browser-only. In-app access is not currently supported.
Step 2: Configure DAS Agent
After purchase, configure DAS Agent to manage your instance groups. DAS provides different management capabilities depending on the edition:
Basic Edition (formerly Personal Edition): One agent managing up to 10 instances.
Enterprise Edition: Multiple agents managing different instance groups. A single instance can also be managed by multiple agents simultaneously—useful when multiple DBAs manage the same instances in shifts.
Configuration steps:
Log on to the Agent Management page.
(Enterprise Edition only) Click Add to create additional agents and define the instances each one manages.
In the Actions column of the target agent, click Edit to open the Edit Configuration page.
In the Associated Instances section, select the instance IDs for this agent to manage, then click OK
After configuration, each agent can perform diagnostics, answer questions, and interact only with the instances it manages.
Integration and console usage:
API integration: Connect using different agent IDs to ensure that different teams—such as DBAs or developers—access only the instances within their permission scope.
Console usage: Switch to the agent for the relevant country or region before performing O&M on the instances it manages.
Step 3: Configure permissions
Configure access permissions before using DAS Agent. DAS provides two built-in system policies:
| Policy | Permission level | Key capabilities |
|---|---|---|
AliyunHDMReadOnlyAccess | Read-only | View all instances in scope; use intelligent diagnosis, performance analysis, and natural language interaction. Cannot perform restarts or parameter modifications. |
AliyunHDMFullAccess | Full access | Full control: diagnosis, optimization, changes, and exports. Includes all AliyunHDMReadOnlyAccess capabilities. |
To assign a policy:
Log on to the RAM console.
In the left navigation pane, choose Identity Management > Users.
Find the target user and click Add Permissions in the Actions column.
In the Access Policy list, search for and select
AliyunHDMReadOnlyAccessorAliyunHDMFullAccess.Click OK.
Step 4: Run a diagnosis
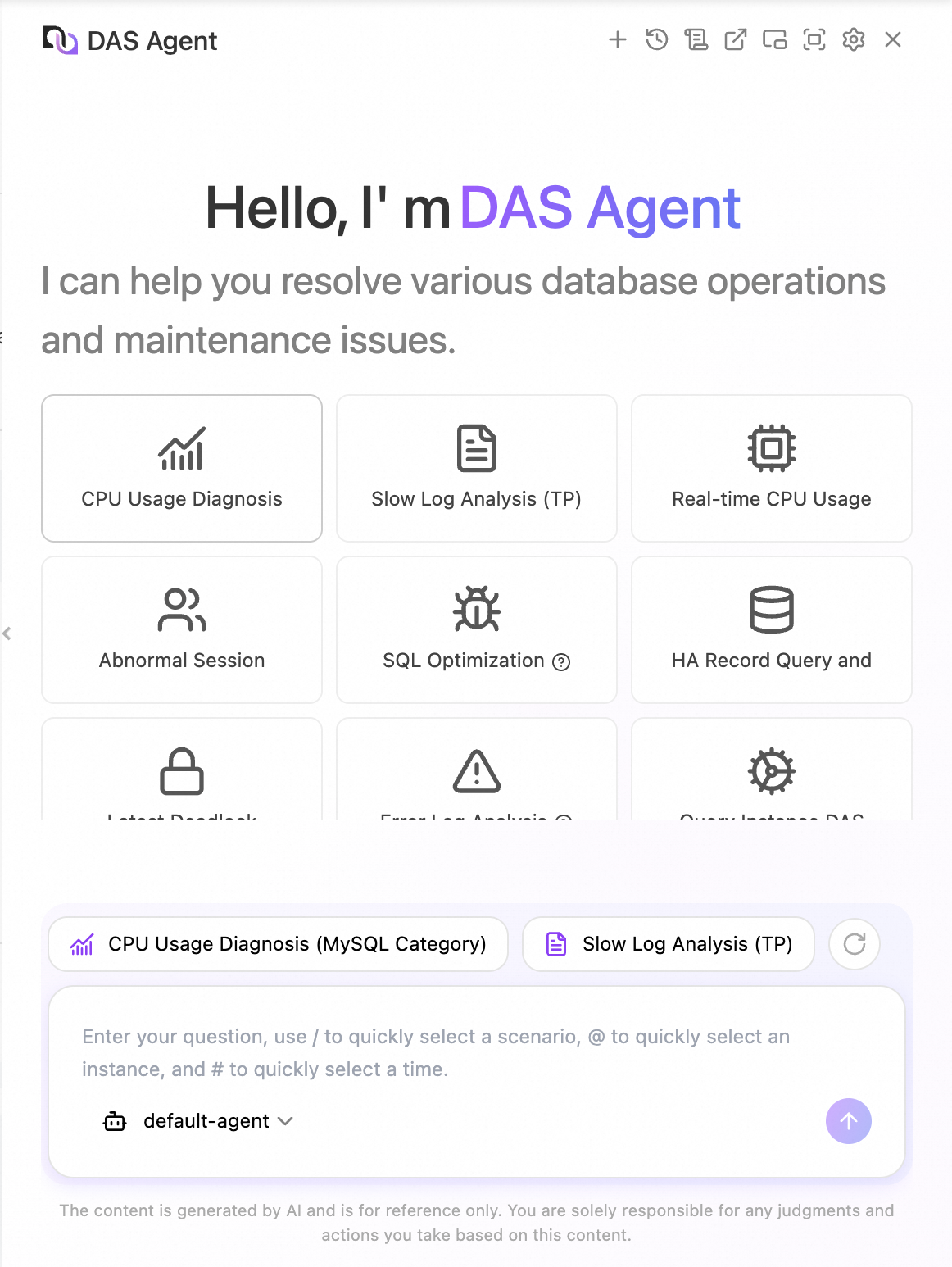
Start a diagnosis from a diagnostic card
Click the card for the scenario you want to diagnose.
In the dialog box, select the instance ID, time range, and other required parameters.
NoteRequired parameters vary by scenario. For example, SQL diagnosis and optimization requires both the database and the SQL statement to analyze.
Click OK.
Start a diagnosis through conversation
Type a question in the dialog box. DAS Agent automatically identifies your intent, matches the most relevant knowledge, and starts a diagnosis.
With its Agentic diagnostics capabilities, DAS Agent independently plans the diagnostic path based on your question and adjusts subsequent steps based on execution results. For example, if you ask to assess the health of an instance, it analyzes CPU usage, session count, memory usage, TPS, QPS, deadlocks, and slow SQL. If it detects a significant slow SQL issue, it proceeds with SQL optimization and provides index suggestions or statement rewrites.
Use keyboard shortcuts to speed up your workflow:
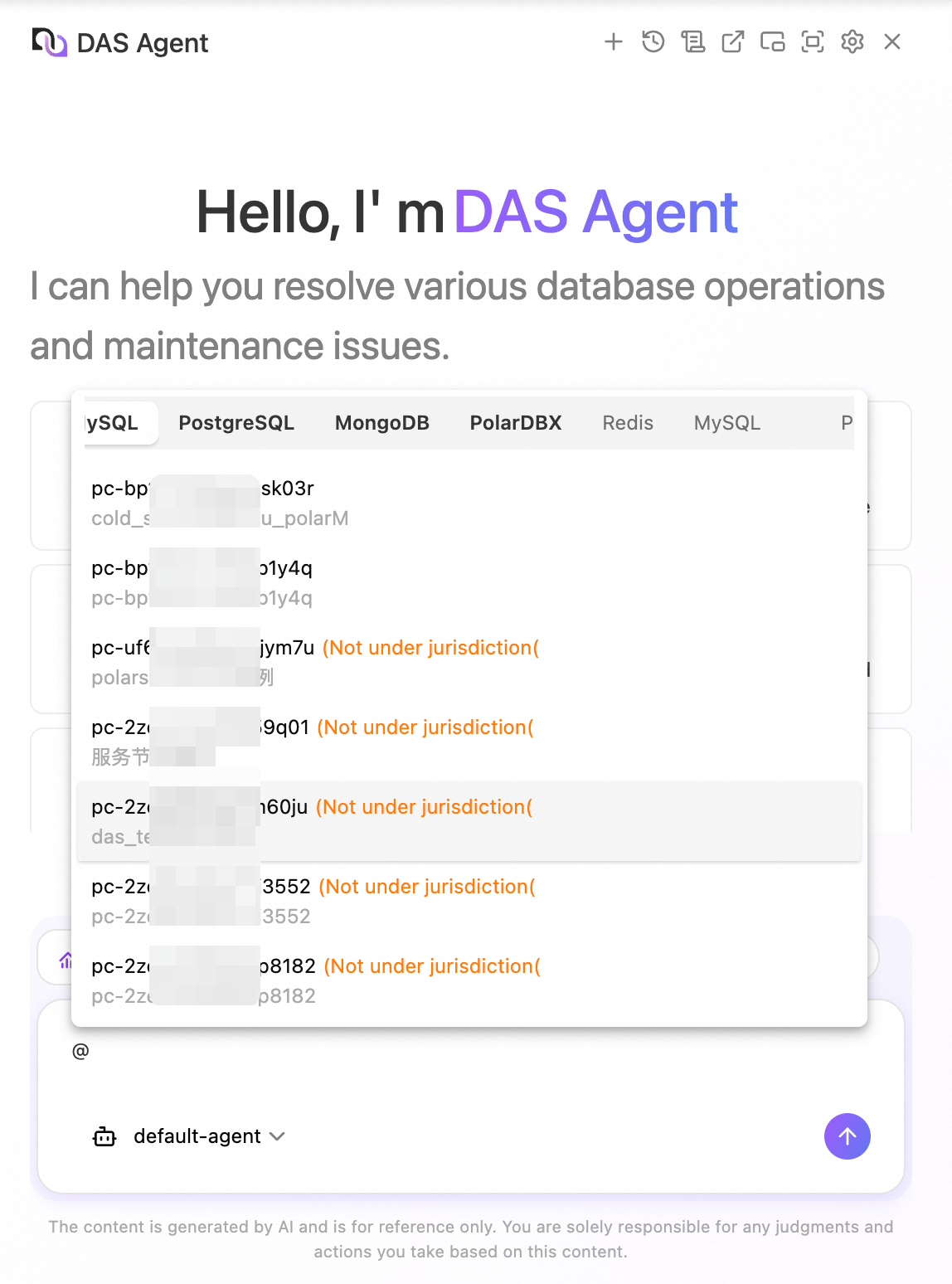
/— bring up diagnostic scenarios@— pull the instance list#— select a time range
Step 5: View the O&M daily report
The intelligent O&M daily report is available for all instances managed by the Enterprise Edition. Each day, DAS Agent analyzes core O&M metrics and delivers a structured summary, including:
Anomaly alert details
High-value slow SQL identification
Disk space usage trends
Invalid index detection results
CPU, memory, and I/O resource usage
This gives your team a unified, actionable O&M overview—helping you understand database health, catch proactive risk warnings, and target optimizations precisely.
To view the report:
In the DAS console, choose Toolbox > Database O&M Daily Report from the left navigation pane.
Find the target report.
In the Actions column, click View Details.
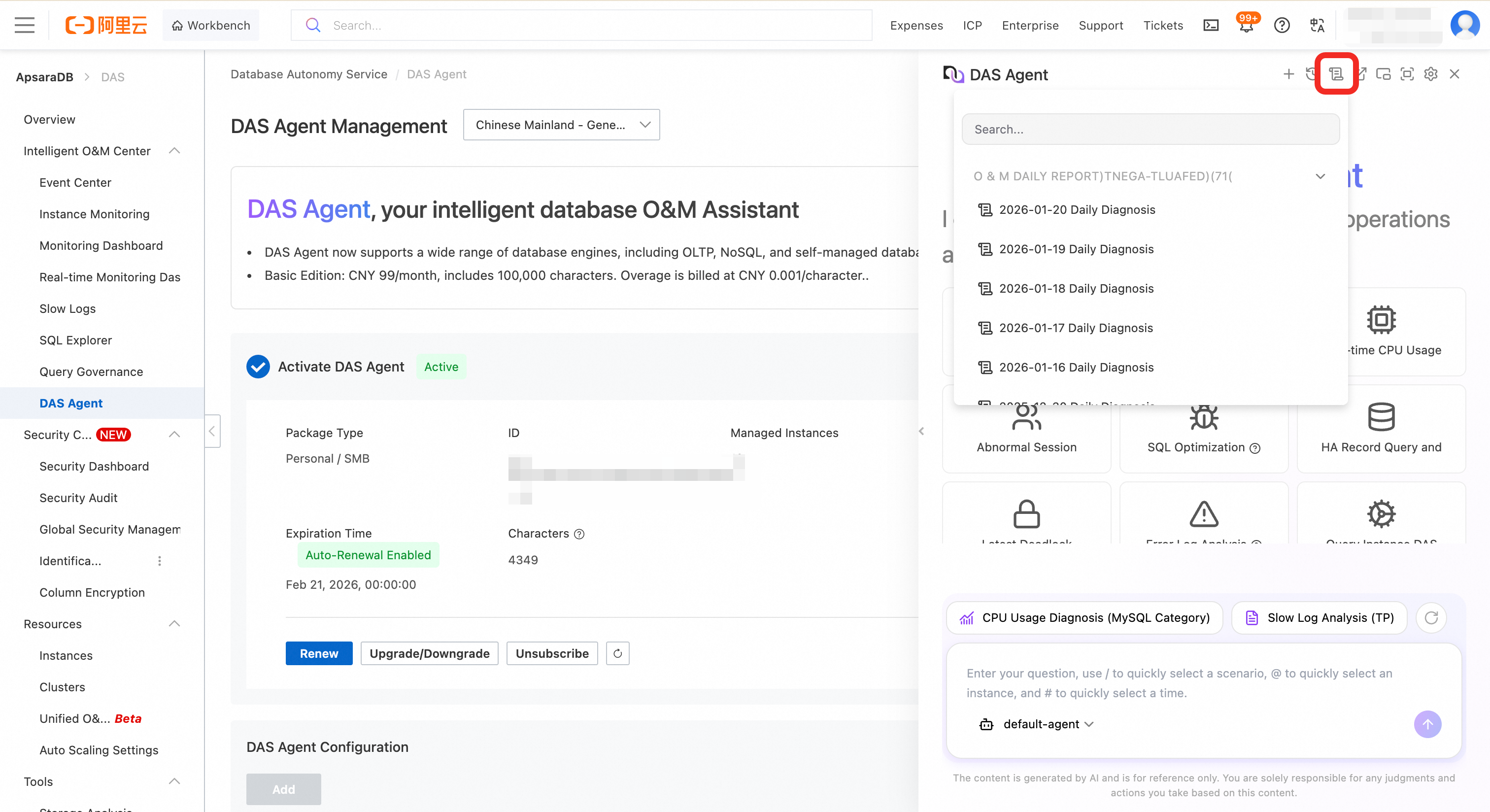
Alternatively, click the ![]() icon at the top of the DAS Agent page to go directly to the report.
icon at the top of the DAS Agent page to go directly to the report.