RAM Roles for Service Accounts (RRSA) lets you bind a RAM role to a specific Kubernetes service account, so only pods using that service account can assume that role. This eliminates static credentials in your code and enforces pod-level access control without granting broad node-level permissions.
To set up RRSA, complete the following steps in order:
-
Enable RRSA on the cluster — done once per cluster.
-
Configure a RAM role with the correct trust policy — done once per unique permission set.
-
Deploy your application with the required environment variables and volume mount — done for each pod that needs cloud service access.
How it works

When an application in a pod needs to call a cloud service API, the following sequence occurs:
-
ACS mounts an OpenID Connect (OIDC) token file into the pod using service account token volume projection. ACS clusters have this feature enabled by default.
-
The application uses the OIDC token to call the STS
AssumeRoleWithOIDCAPI operation and get a temporary Security Token Service (STS) token for the associated RAM role. -
The application uses the STS token to call the target cloud service API.
For this to work, the RAM role's trust policy must authorize the specific service account to assume it. The service account is identified by the oidc:sub condition in the trust policy, using the format system:serviceaccount:<namespace>:<serviceAccountName>.
Prerequisites
Before you begin, ensure that you have:
-
An ACS cluster
-
Access to the RAM console with permissions to create and modify RAM roles
Enable RRSA
-
Log on to the ACS console. In the left navigation pane, click Clusters.
-
Click the name of the target cluster. In the left navigation pane, choose Cluster Information.
-
On the Basic Information tab, find the Security and Auditing section and click Enable next to RRSA OIDC.
-
In the confirmation dialog, click Confirm.
Enabling RRSA takes 2 to 3 minutes. If Cluster Status stays on Updating, click the refresh icon in the upper-right corner to reload the page. When the status changes to Running, RRSA is enabled. Hover over Enabled next to RRSA OIDC to view the OIDC provider URL and ARN — you will need these in the next steps.
After RRSA is enabled, ACS automatically creates a dedicated OIDC issuer for the cluster and registers an identity provider named ack-rrsa-<cluster_id> in your Alibaba Cloud account. The identity provider uses the OIDC issuer for single sign-on (SSO).
Configure a RAM role
Each unique permission set requires one RAM role. Choose one of the following options based on whether you are creating a new role or updating an existing one.
Create a new RAM role
This example creates a role named demo-role-for-rrsa that grants the service account demo-sa in the rrsa-demo namespace read-only access to Container Service clusters.
-
Log on to the RAM console with an Alibaba Cloud account.
-
In the left navigation pane, choose Identities > Roles. On the Roles page, click Create Role.
-
In the Create Role panel, click Switch To Editor to create a role.
-
In the Create Role panel, configure the role using Visual Editor with the following settings, then click OK.
Configuration item Value Effect Allow (default) Principal Click Identity Provider > Edit. Set the type to OIDC and select the identity provider for your cluster (for example, ack-rrsa-<cluster_id>).Action sts:AssumeRole(selected by default)Condition — oidc:iss Added automatically after selecting the identity provider. Keep the default value. Condition — oidc:aud Added automatically after selecting the identity provider. Keep the default value. Condition — oidc:sub Click Add a condition. Set Condition Key to oidc:sub, Operator toStringEquals, and Condition Value tosystem:serviceaccount:<namespace>:<serviceAccountName>. For this example, usesystem:serviceaccount:rrsa-demo:demo-sa.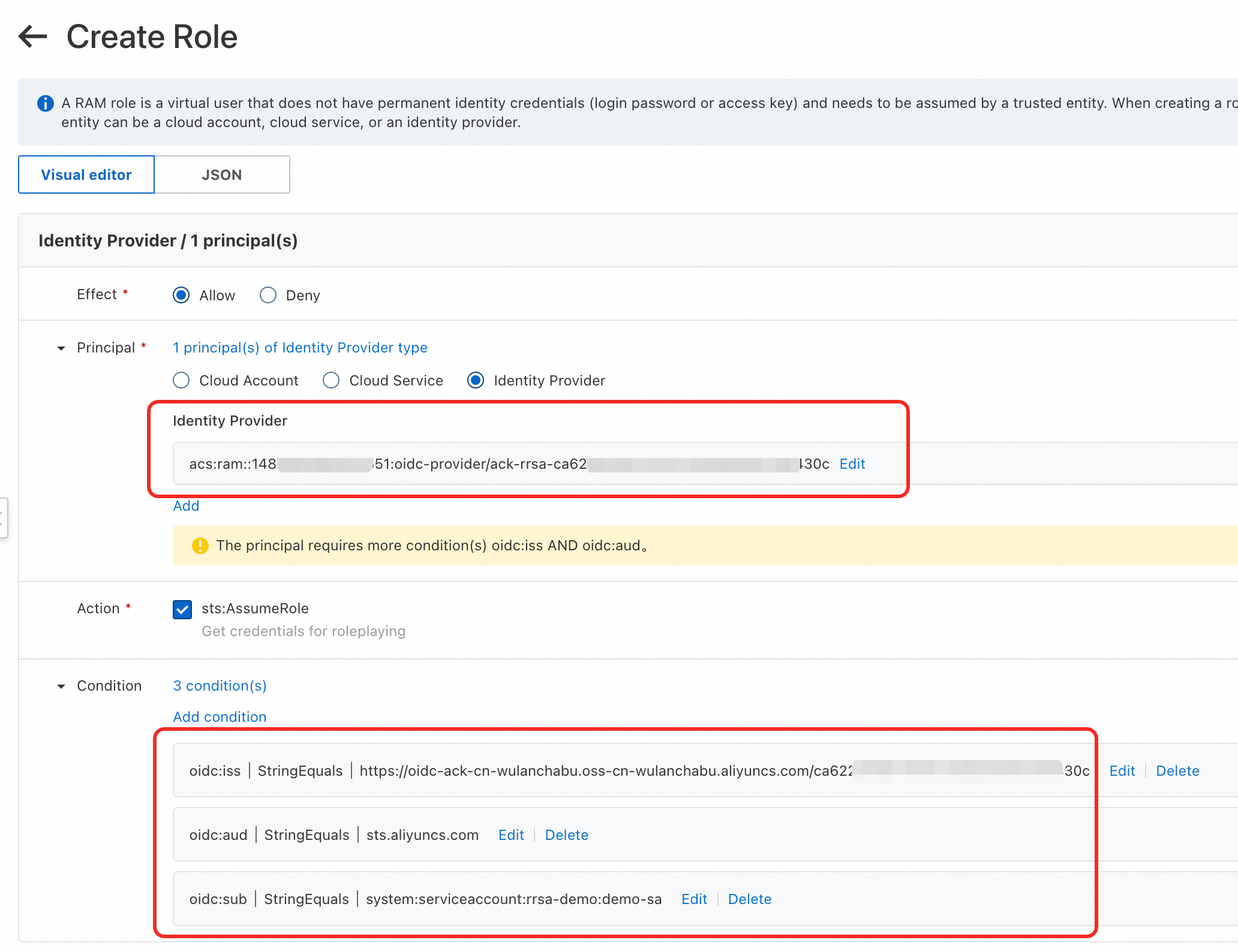
-
In the dialog that appears, enter the role name
demo-role-for-rrsaand click OK. -
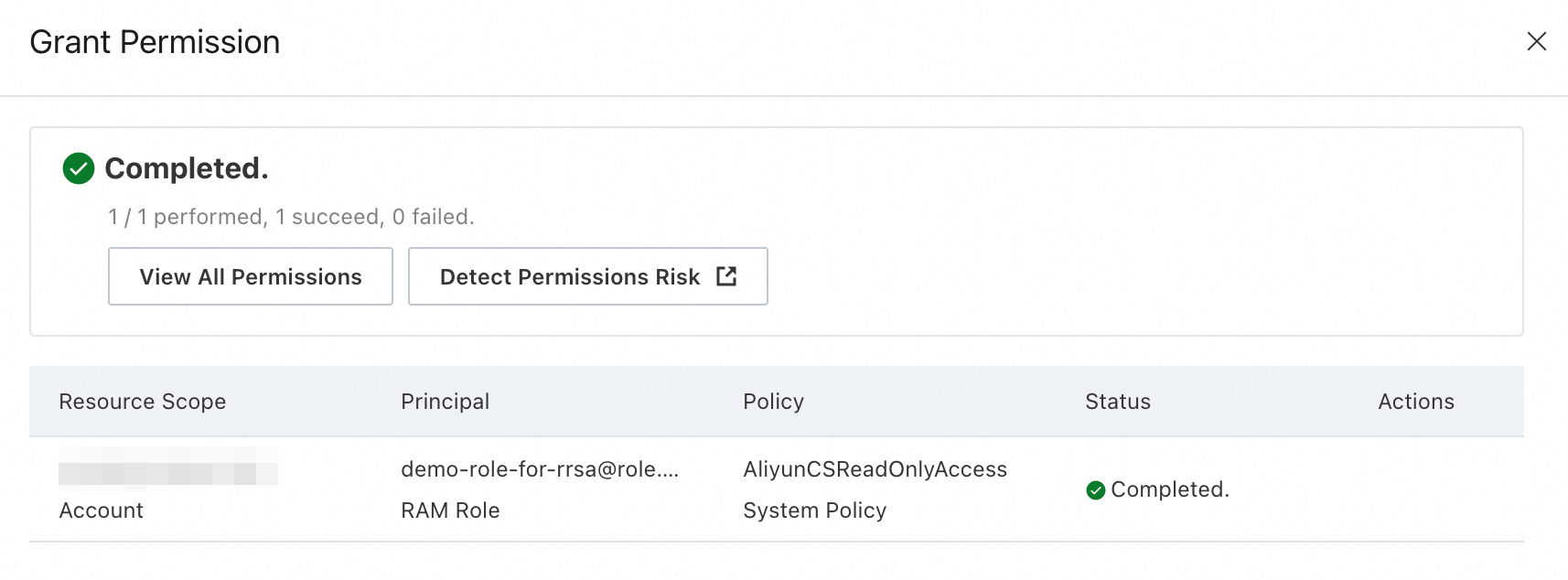
Attach the AliyunCSReadOnlyAccess system policy to the role. For details, see Grant permissions to a RAM role.
Update an existing RAM role
To let an application use an existing RAM role, add the following Statement block to the role's trust policy. For details on editing trust policies, see Edit the trust policy of a RAM role.
Replace the placeholders before saving:
-
<oidc_issuer_url>: the OIDC provider URL. Hover over Enabled next to RRSA OIDC on the Basic Information tab of the Cluster Information page. -
<oidc_provider_arn>: the OIDC provider ARN. Found in the same location. -
<namespace>: the namespace of the application. -
<service_account>: the service account used by the application.
{
"Action": "sts:AssumeRole",
"Condition": {
"StringEquals": {
"oidc:aud": "sts.aliyuncs.com",
"oidc:iss": "<oidc_issuer_url>",
"oidc:sub": "system:serviceaccount:<namespace>:<service_account>"
}
},
"Effect": "Allow",
"Principal": {
"Federated": [
"<oidc_provider_arn>"
]
}
}Deploy the application
-
Create a file named
demo.yamlwith the following content. Replace the placeholders before applying:-
<role_arn>: the ARN of the RAM role. Find it on the Basic Information tab in the RAM console. -
<oid_provider_arn>: the OIDC provider ARN. Hover over Enabled next to RRSA OIDC on the Basic Information tab of the Cluster Information page.
--- apiVersion: v1 kind: Namespace metadata: name: rrsa-demo --- apiVersion: v1 kind: ServiceAccount metadata: name: demo-sa namespace: rrsa-demo --- apiVersion: v1 kind: Pod metadata: name: demo namespace: rrsa-demo spec: containers: - args: - rrsa - demo env: - name: ALIBABA_CLOUD_ROLE_ARN value: <role_arn> - name: ALIBABA_CLOUD_OIDC_PROVIDER_ARN value: <oid_provider_arn> - name: ALIBABA_CLOUD_OIDC_TOKEN_FILE value: /var/run/secrets/ack.alibabacloud.com/rrsa-tokens/token image: registry.cn-hangzhou.aliyuncs.com/acs/ack-ram-tool:1.0.0 imagePullPolicy: Always name: demo volumeMounts: - mountPath: /var/run/secrets/ack.alibabacloud.com/rrsa-tokens name: rrsa-oidc-token readOnly: true restartPolicy: OnFailure serviceAccount: demo-sa serviceAccountName: demo-sa volumes: - name: rrsa-oidc-token projected: defaultMode: 420 sources: - serviceAccountToken: audience: sts.aliyuncs.com expirationSeconds: 3600 # Unit: seconds. Valid values: 600 (10 minutes) to 43200 (12 hours). path: tokenThe three environment variables configure authentication for the application:
Environment variable Description ALIBABA_CLOUD_ROLE_ARNARN of the RAM role to assume ALIBABA_CLOUD_OIDC_PROVIDER_ARNARN of the OIDC identity provider registered by ACS ALIBABA_CLOUD_OIDC_TOKEN_FILEPath to the OIDC token file mounted by ACS -
-
Apply the manifest:
kubectl apply -f demo.yamlThe application uses the OIDC token and the two ARNs to call the STS
AssumeRoleWithOIDCAPI operation, get a temporary STS token for the RAM role, and then call cloud service APIs with that token. For details, see AssumeRoleWithOIDC.
Verify
Print the application log to confirm it can list clusters:
kubectl -n rrsa-demo logs demoExpected output:
20**/**/** 08:35:23 ======= [begin] list ACK clusters with RRSA =======
clusters:
cluster id: cf***, cluster name: foo*
cluster id: c8***, cluster name: bar*
cluster id: c4***, cluster name: foob*
20**/**/** 08:35:24 ======= [end] list ACK clusters with RRSA =======Optional: test permission revocation
To verify that RRSA enforces access control, detach the AliyunCSReadOnlyAccess policy from the role. For details, see Remove permissions from a RAM role.
Wait 30 seconds, then print the log again:
kubectl -n rrsa-demo logs demoThe 403 error confirms that the permission change took effect:
20**/**/** 10:09:33 ======= [begin] list ACK clusters with RRSA =======
20**/**/** 10:09:33 SDKError:
StatusCode: 403
Code: StatusForbidden
Message: code: 403, STSToken policy Forbidden for action cs:DescribeClusters request id: XXXX
Data: {"accessDeniedDetail":{"AuthAction":"cs:DescribeClusters","AuthPrincipalDisplayName":"demo-role-for-rrsa:ack-ram-tool","AuthPrincipalOwnerId":"XXXX","AuthPrincipalType":"AssumedRoleUser","EncodedDiagnosticMessage":"XXXX","NoPermissionType":"ImplicitDeny","PolicyType":"ResourceGroupLevelIdentityBasedPolicy"},"code":"StatusForbidden","message":"STSToken policy Forbidden for action cs:DescribeClusters","requestId":"XXXX","status":403,"statusCode":403}What's next
Some Alibaba Cloud SDKs support OIDC-based authentication natively, so your application can call cloud service APIs without manually managing STS tokens. The following SDK versions support RRSA:
| Language | Minimum SDK version | Demo |
|---|---|---|
| Go | Alibaba Cloud Credentials for Go 1.2.6 and later | Go SDK demo |
| Java | Alibaba Cloud Credentials for Java 0.2.10 and later | Java SDK demo |
| Python 3 | Alibaba Cloud Credentials for Python 0.3.1 and later | Python 3 SDK demo |
| Node.js and TypeScript | Alibaba Cloud Credentials for TypeScript/Node.js 2.2.6 and later | Node.js and TypeScript SDK demo |
For the STS API reference, see AssumeRoleWithOIDC.