By default, RAM users and RAM roles have no permissions to call Alibaba Cloud service APIs. To grant a RAM user or RAM role access to Container Service for Kubernetes (ACK) or Container Compute Service (ACS) clusters, attach the appropriate RAM policies.
ACK uses a two-layer access model:
-
RAM permissions — control access to Alibaba Cloud platform APIs, such as creating, listing, or deleting clusters.
-
RBAC permissions — control access to Kubernetes resources inside a cluster, such as deployments, pods, and services.
RAM permissions are required first. RBAC permissions are configured separately after RAM authorization is complete. Completing this topic covers only the RAM layer; see Grant RBAC permissions to a RAM user or RAM role for the second layer.
Prerequisites
Before you begin, make sure that you have:
-
A RAM administrator account with permission to create and attach policies
-
Basic knowledge of policy elements, structure, and syntax. See Policy elements.
Custom policies
System policies grant access to all clusters. To restrict permissions to specific clusters or specific operations, create a custom policy.
Best practices
Follow the principle of least privilege when creating custom policies:
-
Grant only the permissions needed for the task.
-
Scope permissions to specific clusters using the cluster ID in the
Resourcefield. -
Start with system policies during onboarding, then refine with custom policies as access requirements become clear.
Step 1: Create a custom policy
-
Log on to the RAM console as a RAM administrator.
-
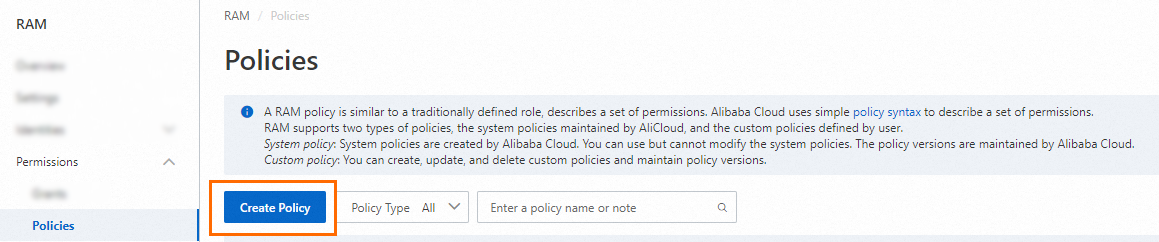
In the left-side navigation pane, choose Permissions > Policies.
-
On the Policies page, click Create Policy.
-
On the Create Policy page, click the JSON tab and enter the policy content. The following example grants read, list, describe, scale, and delete permissions on a specific cluster:
Scope ResourcevalueOne cluster "acs:cs:*:*:cluster/<cluster-id>"Multiple clusters One entry per cluster ID All clusters "*"{ "Statement": [{ "Action": [ "cs:Get*", "cs:List*", "cs:Describe*", "cs:ScaleCluster", "cs:DeleteCluster" ], "Effect": "Allow", "Resource": [ "acs:cs:*:*:cluster/<cluster-id>" ] }], "Version": "1" }Replace
<cluster-id>with the actual cluster ID, such ascae93341766c843479ae986b3305xxxxx. TheResourcefield controls which clusters the policy applies to: TheActionfield specifies which operations to allow. Wildcards are supported. -
Click OK. In the dialog that appears, enter a policy name and click OK.
-
On the Policies page, search by name or description to confirm the policy was created.
Step 2: Attach the custom policy to a RAM user or RAM role
Attach the custom policy the same way you attach a system policy. See Attach a system policy to a RAM user or RAM role.
Policy examples
Read-only access to a specific cluster
Minimum permissions for a RAM user to view cluster details:
{
"Statement": [{
"Action": [
"cs:Get*",
"cs:List*",
"cs:Describe*"
],
"Effect": "Allow",
"Resource": [
"acs:cs:*:*:cluster/<cluster-id>"
]
}],
"Version": "1"
}Non-cluster-specific API operations
Some API operations, such as DescribeEvents, are not scoped to a specific cluster. For these operations, set Resource to "*" in a separate Statement block. Do not add cluster IDs to the Resource field for non-cluster-specific operations.
The following example grants permission to call DescribeEvents alongside read access on a specific cluster:
{
"Statement": [
{
"Action": [
"cs:DescribeEvents"
],
"Effect": "Allow",
"Resource": [
"*"
]
},
{
"Action": [
"cs:Get*",
"cs:List*",
"cs:Describe*"
],
"Effect": "Allow",
"Resource": [
"acs:cs:*:*:cluster/<cluster-id>"
]
}
],
"Version": "1"
}What's next
RAM permissions grant access to cluster management APIs. To manage Kubernetes resources inside a cluster — such as deployments, pods, and services — also grant RBAC permissions.
Before configuring RBAC, make sure the RAM user or RAM role has at least read-only permissions on the target cluster:
{
"Statement": [{
"Action": [
"cs:Get*",
"cs:List*",
"cs:Describe*"
],
"Effect": "Allow",
"Resource": [
"acs:cs:*:*:cluster/<cluster-id>"
]
}],
"Version": "1"
}Then configure RBAC authorization. See Grant RBAC permissions to a RAM user or RAM role.
