Expose a Knative Service over HTTPS by creating a TLS certificate, storing it as a Kubernetes Secret, and binding it to a DomainMapping. This guide uses OpenSSL to generate a self-signed certificate for the domain helloworld.knative.top.
Prerequisites
Before you begin, ensure that you have:
-
Knative deployed in your ACS cluster. See Deploy Knative
-
A Knative Service to expose. The steps below use a sample Service named
helloworld-go
Step 1: Create a Knative Service
-
Log on to the ACS console and click Clusters in the left-side navigation pane.
-
On the Clusters page, click the ID of the cluster you want to manage. In the left-side navigation pane of the cluster details page, choose Applications > Knative.
-
On the Services tab of the Knative page, set Namespace to default and click Create from Template. Select Sample Template, then click Create. A Knative Service named
helloworld-gois created.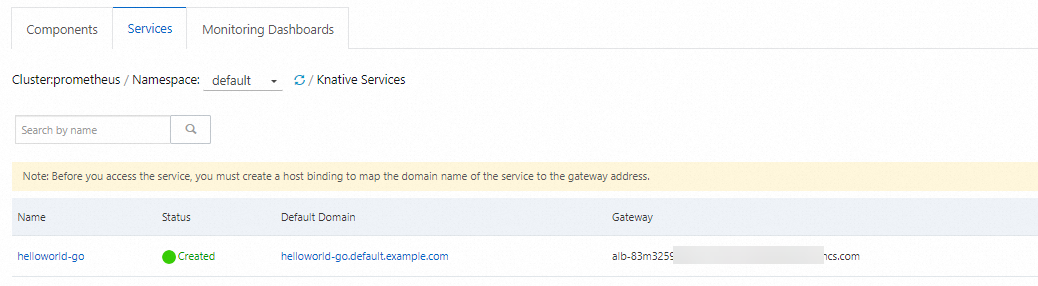
Step 2: Create a TLS certificate as a Secret
Kubernetes Secrets store sensitive data such as certificates and private keys. The following steps use OpenSSL to create a self-signed certificate valid for 3,650 days, then store it in a Secret named secret-tls.
-
Generate a self-signed certificate for
helloworld.knative.top:openssl genrsa -out knativetop-key.pem 4096 openssl req -subj "/CN=helloworld.knative.top" -sha256 -new -key knativetop-key.pem -out knativetop.csr echo subjectAltName = DNS:helloworld.knative.top > extfile.cnf openssl x509 -req -days 3650 -sha256 -in knativetop.csr -signkey knativetop-key.pem -out knativetop-cert.pem -extfile extfile.cnfExpected output:
Signature ok subject=CN = helloworld.knative.top Getting Private keyThis produces two files: a private key (
knativetop-key.pem) and a certificate (knativetop-cert.pem). -
Encode the certificate files using Base64:
-
Encode the private key:
cat knativetop-key.pem | base64Expected output:
a25hdGl2ZXRvcC1r****** -
Encode the certificate:
cat knativetop-cert.pem | base64Expected output:
a25hdGl2ZXRvcC1jZ******==
-
-
Create a TLS Secret from the certificate files:
kubectl create secret tls secret-tls --key knativetop-key.pem --cert knativetop-cert.pemExpected output:
secret/secret-tls created
Step 3: Create a DomainMapping
A DomainMapping maps a custom domain name to a Knative Service. Adding a tls block to the DomainMapping spec enables HTTPS using the Secret created in the previous step.
-
Create a file named
helloworld.knative.top.yaml:vim helloworld.knative.top.yaml -
Add the following content, save, and exit:
apiVersion: serving.knative.dev/v1beta1 kind: DomainMapping metadata: name: <domain-name> namespace: <namespace> spec: ref: name: <service-name> kind: Service apiVersion: serving.knative.dev/v1 tls: secretName: <tls-secret-name>Replace the placeholders with your values:
Placeholder Description Example <domain-name>The custom domain name to map to the Service helloworld.knative.top<namespace>The namespace containing both the DomainMapping and the Service default<service-name>The name of the Knative Service to expose helloworld-go<tls-secret-name>The name of the TLS Secret created in Step 2 secret-tls -
Apply the DomainMapping:
kubectl apply -f helloworld.knative.top.yamlExpected output:
domainmapping.serving.knative.dev/helloworld.knative.top created -
Verify that the DomainMapping is ready:
kubectl get domainmapping helloworld.knative.topExpected output:
NAME URL READY REASON helloworld.knative.top https://helloworld.knative.top TrueThe
URLcolumn showshttps://, confirming that TLS is active. IfREADYis notTrue, wait a few seconds and run the command again.
Step 4: Test HTTPS access
Test access through your ingress. The -k flag bypasses TLS verification and is required when using a self-signed certificate.
ALB
Add a listener on port 443 in your AlbConfig:
apiVersion: alibabacloud.com/v1
kind: AlbConfig
metadata:
name: knative-internet
spec:
config:
...
listeners:
- port: 443
protocol: HTTPS # Valid values: HTTP, HTTPS, QUIC
...Then test with the Application Load Balancer (ALB) Ingress address:
# Replace alb-ppcate4ox6******.cn-beijing.alb.aliyuncs.com with your ALB Ingress address
curl -H "host: helloworld.knative.top" https://alb-ppcate4ox6******.cn-beijing.alb.aliyuncs.com -kMSE
Test with the Microservice Engine (MSE) Ingress address:
# Replace 8.141.XX.XX with your MSE Ingress address
curl -H "host: helloworld-go.default.example.com" https://8.141.XX.XX -kASM
Test with the Service Mesh (ASM) Ingress address:
# Replace 8.141.XX.XX with your ASM Ingress address
curl -H "host: helloworld-go.default.example.com" http://8.141.XX.XX -kAll three options return:
Hello Knative!What's next
Configure health checks for your Knative Services to monitor their availability. See Configure port probing in Knative.