Overview
Background information
Virtual private clouds (VPCs) are the most basic components in cloud computing. The first step to migrate your business to the cloud is to create a VPC. Improper network design may result in potential scalability issues. Network reconfiguration not only increases costs but also can interrupt business workflows. If you want to limit Internet access for some businesses and isolate the businesses from each other, you can deploy one VPC in a region. We recommend that you take note of address allocation, subnetting, route configurations, and security hardening described in this topic.
Terms
VPC: A VPC is an exclusive private network in the cloud. You have full control over your VPC. For example, you can specify CIDR blocks, and configure route tables and gateways for your VPC. You can deploy cloud resources, such as Elastic Compute Service (ECS) instances, ApsaraDB RDS instances, and Server Load Balancer (SLB) instances, in your VPC. Each VPC consists at least of a private CIDR block, a vSwitch, and a route table.
Private CIDR block: When you create a VPC and a vSwitch, you must specify a private IP address range for the VPC in CIDR notation.
Route table: After you create a VPC, the system automatically creates a system route table and adds system routes to the table. The route table defines how traffic is forwarded for the VPC.
vSwitch: You can create vSwitches to divide a VPC into one or more subnets. vSwitches that are in the same VPC can communicate with each other. You can deploy your applications in vSwitches that belong to different zones to improve service availability.
IPv4 gateway: An IPv4 gateway is an Internet gateway that connects VPCs to the Internet. Inbound and outbound Internet IPv4 traffic is forwarded and controlled by IPv4 gateways, which facilitate the management and control of Internet access. You can configure routes for the IPv4 gateway of your VPC to regulate Internet access for instances in the VPC. For example, only vSwitches whose routes point to the IPv4 gateway can access the Internet.
NAT gateway: NAT gateways provide NAT services and are classified into Internet NAT gateways and VPC NAT gateways. If multiple ECS instances need to access the Internet, you can use the SNAT feature of an Internet NAT gateway to allow the ECS instances to access the Internet by using the elastic IP addresses (EIPs) of the NAT gateway. This saves public IP address resources. To improve network security, you can translate and hide cloud service addresses to prevent private address exposure. VPC NAT gateways can prevent IP address conflicts by translating private IP addresses.
SLB: If only one ECS instance is used to provide services over the Internet, a single point of failure (SPOF) may occur, which compromises system availability. We recommend that you use an SLB instance as the unified Internet traffic ingress and add multiple ECS instances in different zones to the SLB instance as backend servers. This prevents SPOFs and improves service availability.
Solution highlights
Security: Internet-accessible applications and Internet-inaccessible applications are deployed in different vSwitches. You can use access control lists (ACLs) to control access between the vSwitches and use security groups to control access between server groups. To harden application system security, you can use Cloud Firewall to enhance protection at the Internet borders, VPC borders, and NAT gateway borders.
Scalability: To ensure that your VPC can suit the requirements for long-term business development, you must reserve sufficient IP addresses that do not conflict with each other. Otherwise, your network architecture may require significant changes.
Reliability: We recommend that you use at least two vSwitches when you deploy one VPC in a region. To ensure active zone-redundancy, make sure that the vSwitches are deployed in different zones. You can combine VPC with other networking services to implement cross-zone deployment, such as NAT Gateway, SLB, and Cloud Enterprise Network (CEN).
Observability: You can use Network Intelligence Service (NIS) to visualize network quality, network traffic, network instance inspection and diagnostics, and network topology. Data visualization simplifies network O&M. You can also use flow logs and traffic mirroring to observe network traffic and troubleshoot errors.
Key design
The following key points show how to design the deployment of one VPC in a region from multiple dimensions to suit different requirements:
Clear network requirements
You must take into consideration all possible factors when you select the region and zones, such as the network latency and supported cloud services.
The Internet quality determines accessibility. You can use NIS to probe Internet accessibility and monitor daily probe results.
If your business requires low network latency, you can use NIS to test connectivity between cloud networks and monitor the network latency between zones in the same region or in different regions.
You must also confirm the purpose and requirements for using VPCs. For example, isolation requirements for VPCs in the production environment and in the staging environment are different. Security group configurations, ACL configurations, and Cloud Firewall configurations, and networking solutions are determined based on your network requirements.
Proper CIDR block allocation
Allocate a proper number of IP addresses to your VPC. Reserve sufficient IP addresses for business development but do not waste IP address resources. Deploy a proper number of public vSwitches and private vSwitches. Confirm the vSwitch that each application belongs to. Make sure that Internet-facing applications and internal-facing applications are deployed in secure domains in the VPC.
Precise routes
If you want to use public vSwitches and private vSwitches to isolate public applications from private applications, you need to associate the public vSwitches and private vSwitches with different route tables to isolate network traffic. You can enable gateway route tables to limit Internet access for the vSwitches.
Security
You can use security groups and ACLs to limit inbound and outbound traffic for your VPC. For example, you can configure security group rules for each instance or service to allow access only to specified ports or over specified protocols. Security groups and ACLs provide basic protection. To enhance security, we recommend that you use Cloud Firewall.
Inbound and outbound rules for Internet traffic
We recommend that you use an SLB instance as the Internet ingress for Internet traffic. If you have a large number of servers that require Internet access, you can use a NAT gateway as the Internet egress. If you want to deploy a NAT gateway and an SLB instance in your VPC, you must assign a separate vSwitch for the NAT gateway and VPC. The vSwitch of the Internet ingress and egress must be isolated from the vSwitch of your applications to increase networking flexibility and security.
High availability
When you design your VPC, take into consideration the high availability and scalability requirements. When you deploy one VPC in a region, we recommend that you use at least two vSwitches.You can combine VPC with other networking services to implement cross-zone deployment, such as NAT Gateway, SLB, and CEN.
O&M and monitoring
High observability help O&M engineers and developers quickly identify errors, optimize performance, and predict potential failures. We recommend that you use NIS, flow logs, and traffic mirroring to visualize O&M.
Best practices

Solution overview
When you design the deployment of one VPC in a region, you must design the entire network architecture based on your business requirements, including the internal network of your data center, hybrid cloud networks, and wide area network in the cloud.
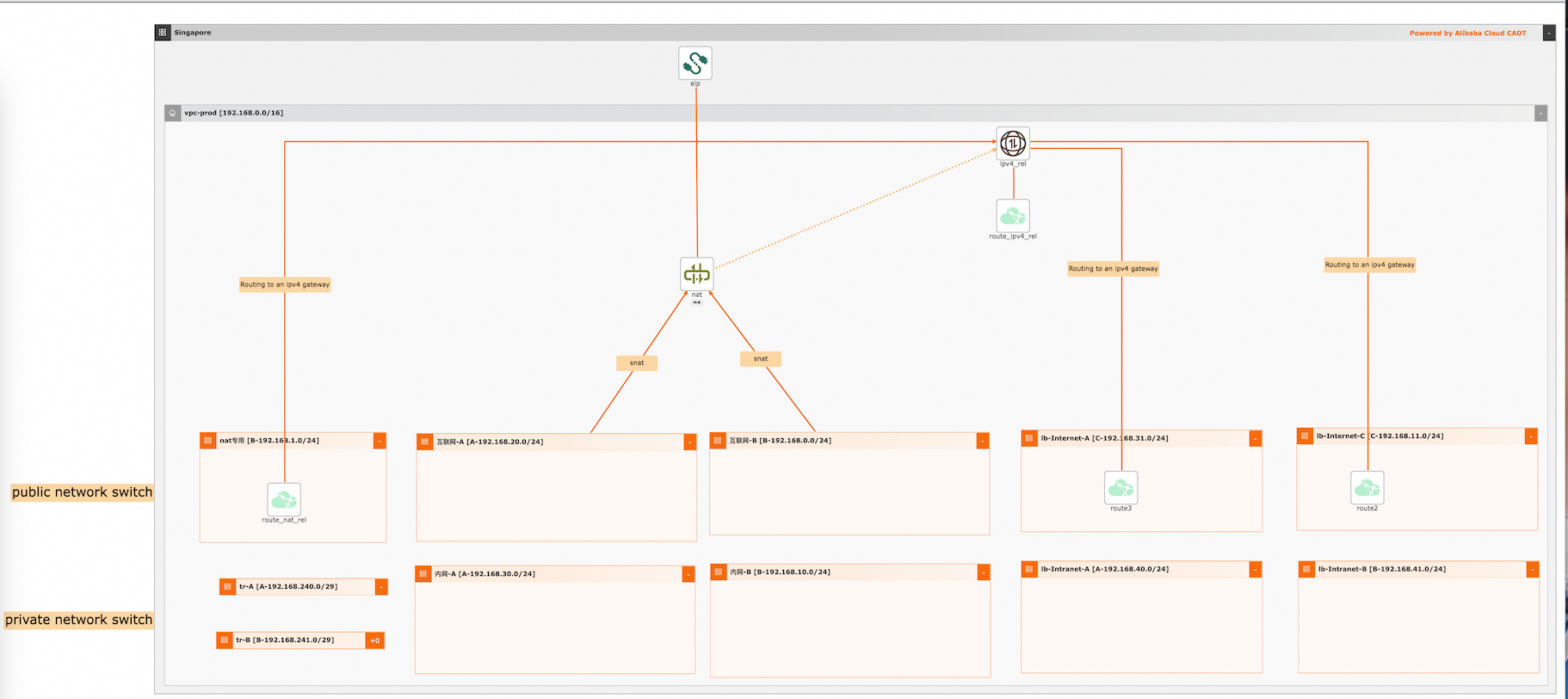
This solution uses VPC, vSwitches, and IPv4 gateways to build a data center in the cloud. Only one VPC is deployed in the region.
Security: The VPC is divided into public vSwitches and private vSwitches, Internet-facing applications are deployed in the public vSwitches. Internal-facing applications and databases are deployed in the private vSwitches. In the preceding figure, servers in vSwitch A and vSwitch B cannot access the Internet even if they have a public IP address. You can improve application security by using security groups, ACLs, and Cloud Firewall.
Scalability: Cloud resources such as ECS instances, networks, and storage devices occupy IP addresses. We recommend that you use a large subnet mask to reserve sufficient IP addresses. If IP addresses are insufficient due to improper planning, you can add secondary CIDR blocks to provide more IP addresses. You cannot modify secondary CIDR blocks. A VPC supports multiple public vSwitches and private vSwitches that allow you to deploy multiple applications.
Reliability: Make sure that you create at least two vSwitches of each type and deploy the vSwitches in different zones to implement active zone-redundancy.
Observability: You can use NIS to visualize network quality, network traffic, network instance inspection and diagnostics, and network topology.
Procedure
Select a region and zones
Select a region based on your user locations. Select zones based on cloud resource stock and latency requirements. For more information, see Monitor average network latencies between zones or between regions and Monitor the Internet access latency.
Allocate IP addresses
You can use the standard RFC CIDR blocks:
10.0.0.0/8,172.16.0.0/12, and192.168.0.0/16, or their subsets as the VPC CIDR blocks. You can also specify custom VPC CIDR blocks. You cannot specify100.64.0.0/10,224.0.0.0/4,127.0.0.0/8,169.254.0.0/16, or one of their subnets as the custom CIDR block.If you have multiple VPCs or want to set up a hybrid cloud environment between a VPC and your data center, we recommend that you specify the subsets of the RFC CIDR blocks for your VPCs. In this case, we recommend that you set the subnet mask length to 20 bits or smaller. Make sure that the CIDR blocks of the VPCs and your data center do not overlap. When you plan the CIDR block of a vSwitch, you need to consider the number of ECS instances and other cloud resources that can be created in the vSwitch. We recommend that you specify a large CIDR block to reserve sufficient IP addresses for later use. However, do not specify a CIDR block that greatly exceeds your business requirements. Otherwise, the idle IP addresses of the VPC are wasted and other VPCs cannot scale out due to insufficient IP addresses.
Design vSwitches
NoteCreate at least two vSwitches of each type and deploy the vSwitches in different zones to implement active zone-redundancy.
vSwitch
Resource in the vSwitch
Public vSwitches that have Internet access
SLB vSwitch
Only an Internet-facing SLB instance, such as an ALB or NLB instance, is deployed. No ECS instance is deployed.
NAT gateway vSwitch
Only NAT gateways are deployed. No ECS instance is deployed.
Application vSwitch
Internet-facing application servers are deployed. However, ECS instances cannot access the Internet even if they have a public IP address. ECS instance can use the SLB instance or NAT gateway to communicate with the Internet.
Private vSwitches that do not have Internet access
SLB vSwitch
Only an internal-facing SLB instance, such as an ALB or NLB instance, is deployed. No ECS instance is deployed.
Application vSwitch
Internal-facing application servers or databases are deployed. The server do not have Internet access.
Transit router vSwitch
The VPC uses the transit router to communicate with other VPCs and virtual border routers (VBRs) that are attached to the CEN instance.
Design route tables
vSwitch
Zone
Associated route table
Route configuration
Public vSwitches
SLB vSwitch
Zone E and Zone F
System route table
Point the default route to the IPv4 gateway and add the ECS instances in vSwitch A to the SLB instance. The SLB instance functions as the ingress for Internet traffic.
NAT gateway vSwitch
Zone E and Zone F
Application vSwitch
Zone E and Zone F
Custom route table 1
Point the default route to the NAT gateway. The ECS instances can use the NAT gateway to communicate with the Internet or be added to the SLB instance to provide services to the Internet. No default route that points to the IPv4 gateway is configured. vSwitch A does not have a default route that points to the IPv4 gateway. The ECS instances cannot communicate with the Internet even if they have a public IP address. This hardens system security because the Internet ingress of the ECS instances is under full control.
Private vSwitches
SLB vSwitch
Zone E and Zone F
Custom route table 2
Deploy an internal-facing SLB instance and add the ECS instances in vSwitch B to the SLB instance. The ECS instances provide internal services. No default route that points to the NAT gateway or IPv4 gateway is configured.
Application vSwitch
Zone E and Zone F
Deploy ECS instances or security-sensitive databases as a private network environment. Do not configure a route that points to the NAT gateway or IPv4 gateway. Do not add the ECS instances to an Internet-facing SLB instance. The ECS instances do not have Internet access.
Transit router vSwitch
Zone E and Zone F
The VPC uses the transit router to communicate with other VPCs and VBRs that are attached to the CEN instance. You need to configure custom routes that point to the transit router.
Design security protection
You can improve application security by using security groups, ACLs, and Cloud Firewall.
Server security: Associate a security group with the server group of ECS instances to control access to the ECS instances. Security groups are stateful. Changes to the inbound rules of a security group are automatically applied to the outbound rules of the security group.
vSwitch security: Associate an ACL with a vSwitch to control access to the vSwitch. ACLs are stateless. To allow responses from the vSwitch, you must configure an allow rule in the outbound direction.
Advanced security:
Internet firewall: After you enable an Internet firewall for Internet-facing assets, Cloud Firewall filters inbound and outbound traffic based on traffic analysis policies, intrusion prevention policies, threat intelligence rules, virtual patching policies, and access control policies. Then, the Internet firewall checks whether inbound and outbound traffic matches the specified conditions and blocks unauthorized traffic. This ensures the security of traffic between Internet-facing assets and the Internet.
NAT firewall: After you enable a NAT firewall or a NAT gateway, the NAT firewall monitors all outbound traffic from internal-facing resources in VPCs to the NAT gateway, including resources in the same VPC and resources across VPCs.
VPC firewall: A VPC firewall monitors and manages traffic between VPCs and traffic between a VPC and a data center.
Design O&M
We recommend that you combine NIS with flow logs and traffic mirroring to visualize O&M.
NIS: A network O&M tool that supports network quality visualization, topology visualization, and traffic visualization. You can use NIS to perform inspection and instance diagnostics.
Flow logs: Flow logs can be used to collect the 5-tuple information about elastic network interfaces (ENIs), VPCs, and vSwitches. You can analyze flow logs to check ACL rules, monitor network quality, and troubleshoot network errors.
Traffic mirroring: This feature can mirror specific packets that go through ENIs and can be used for content inspection, threat monitoring, and troubleshooting.
Remediate invalid configurations
Insufficient IP addresses: If addresses are insufficient due to improper planning, you can add secondary CIDR blocks to provide more IP addresses. You cannot modify secondary CIDR blocks.
IP address conflicts: If your VPC is assigned sufficient CIDR blocks, you can create vSwitches with nonoverlapping CIDR blocks and migrate your applications to the vSwitches. You can also resolve IP address conflicts by using VPC NAT gateways, which can translate private IP addresses. However, NAT gateways increase route configuration complexity. We recommend that you do not use NAT gateways unless necessary.
Virtualize the architecture on CADT
Deploy one VPC in a region
Scenario | Item | References |
Deploy one VPC in a region | Template ID | 51N54AV10ZTRRTRW |
Template library address | ||
Sample code |
Visualized deployment architecture
Procedures
Visualized deployment
Create required cloud resources, including 1 VPC, 11 vSwitches, 1 IPv4 gateway, and 3 custom route tables.
Create an application based on a template. The default region is China (Shanghai). Create the cloud resources, instead of using existing cloud resources.
Save and verify the application, and calculate the fees. In this example, all cloud resources are billed on a pay-as-you-go basis.
Confirm the configurations, select a protocol, and start the deployment of all resources. Routes are automatically configured.
API calls
Call the corresponding API operations to deploy and use cloud resources.
Refer to the documentation to initialize the configurations by using a command-line interface (CLI).
Refer to the sample YAML file to deploy and output the architecture.
If you want to change the region, change the value of the area_id field. For example, change cn-hangzhou to cn-shanghai.