This topic describes how to migrate a VPC Firewall from the default active-active architecture to an active-standby architecture. This migration helps reduce latency caused by cross-zone traffic.
Example scenario
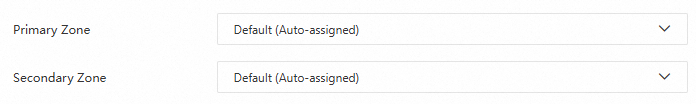
An enterprise creates a VPC Firewall in the Singapore region and selects the Default (Auto-assigned) option for the primary and secondary availability zones, as shown in the following figure.
The created VPC Firewall uses the default active-active architecture for disaster recovery. In this architecture, the Cloud Firewall cluster does not use proximity-based routing. Instead, it randomly distributes traffic between the two availability zones, which can result in cross-zone traffic.
To address this issue, VPC Firewall provides an active-standby architecture for disaster recovery. In this architecture, the VPC Firewall prioritizes traffic processing in the primary availability zone and fails over to the secondary availability zone only for disaster recovery.
If you have a VPC Firewall instance that uses an active-active architecture, you can follow the steps in this topic to migrate it to an active-standby architecture.
Before migration | After migration |
 |  |
Usage notes
The migration requires you to disable and delete all VPC Firewalls in the target region and then recreate them. Your existing access control policies are retained during this process.
When you enable or disable traffic redirection for a VPC Firewall that is attached to a Cloud Enterprise Network (CEN) Basic Edition instance, you may experience a brief routing disruption that lasts a few seconds.
When you perform the same action with a CEN Enterprise Edition instance, no routing disruption occurs.
(Recommended) Configure a high-priority access control policy to allow all traffic during the migration to prevent traffic interruptions. For more information, see Configure an access control policy for a VPC Firewall.
Before you begin, record the CIDR blocks of the firewall VPC and the VSwitches. You can reuse this information when you recreate the firewall.
In an active-standby architecture, dependencies exist between the primary and secondary availability zones. The available options in the console reflect these dependencies.
Migrating to an active-standby architecture for CEN Basic Edition
To migrate a VPC Firewall for a Cloud Enterprise Network (CEN) Basic Edition instance from an active-active to an active-standby architecture, you must disable and delete all VPC Firewalls associated with that CEN instance in the target region, and then recreate them with the active-standby architecture.
Step 1: Disable and delete the VPC Firewalls
Log on to the Cloud Firewall console. In the left-side navigation pane, click Firewall.
On the tab, click Batch Disable.
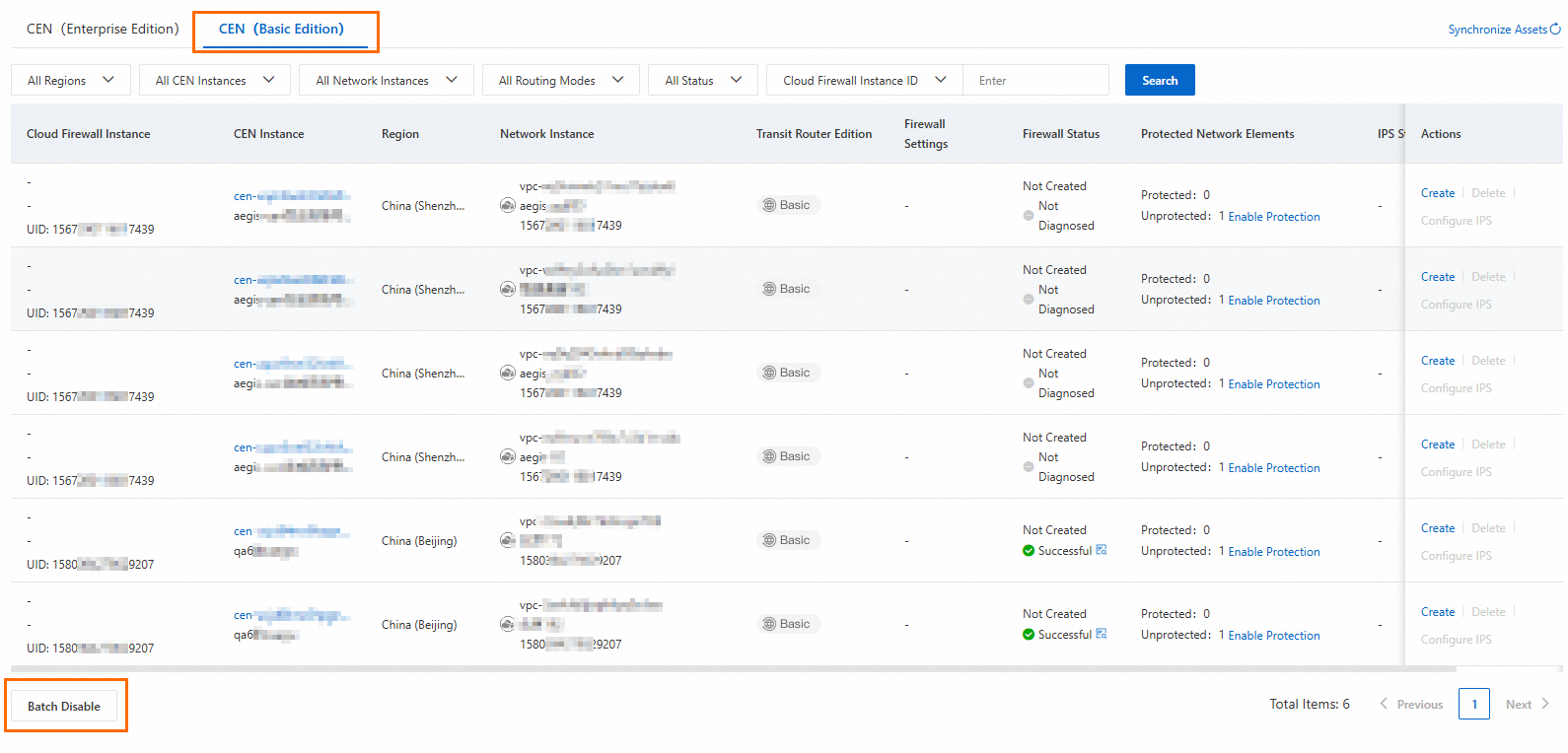
In the Batch Disable dialog box, select the CEN Instance and Region, and then click OK.
After the firewalls are disabled, locate them in the specified region and click Delete in the Actions column for each one.
Step 2: Create a VPC Firewall
Find the CEN instance in the target region and click Create in the Actions column.
In the Create Firewall panel, click Quick Diagnosis.
For a Basic Edition transit router, use this feature to verify that the prerequisites for creating a VPC Firewall are met. After the diagnosis is complete, you can view the results in the Enable Diagnosis wizard. If you are familiar with the creation process, you can skip the diagnosis and create the firewall directly. If the diagnosis fails, see Troubleshoot Cloud Firewall enablement failures for solutions.
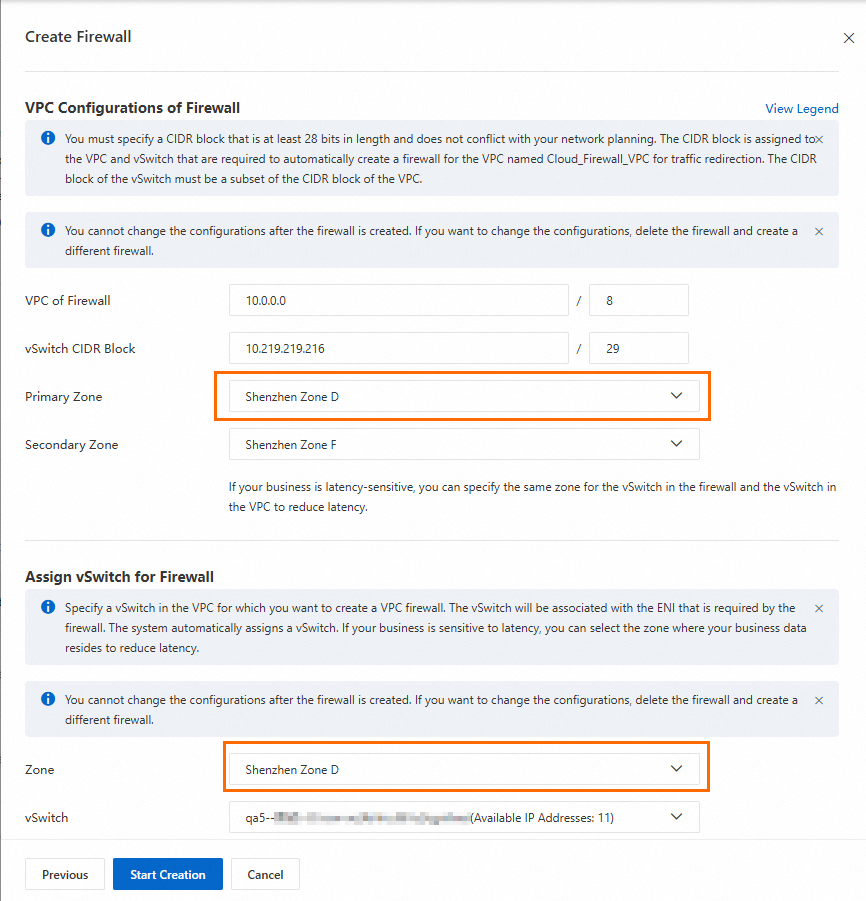
Configure the settings, including the CIDR block of the firewall VPC, primary and secondary availability zones, the VSwitch instance and its availability zone, and intrusion prevention.
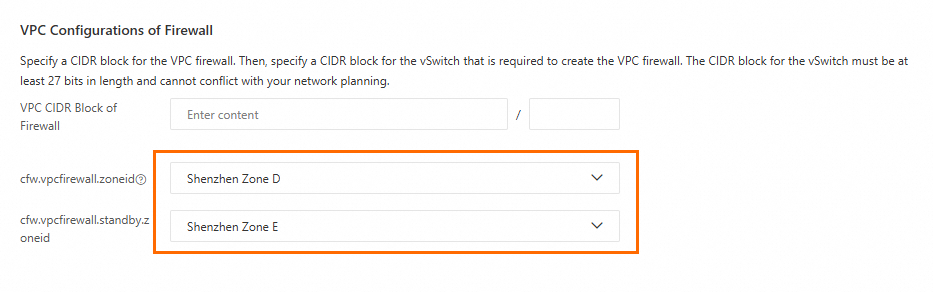
ImportantTo enable the active-standby architecture, set the Primary Zone and Secondary Zone in the VPC Configurations of Firewall section to the availability zones that handle your business traffic. This enables the active-standby architecture. However, if the Zone selected for the VSwitch of your business VPC is different from the Primary Zone, latency from cross-zone traffic may still occur.
For latency-sensitive applications, ensure that the Primary Zone in the VPC Configurations of Firewall section and the Zone for the VSwitch of your business VPC are set to the same availability zone that handles your business traffic. This minimizes latency.
The intrusion prevention settings apply to all network instances attached to the same CEN instance.
Click Start Creation to create the VPC Firewall.
After the firewall is created, repeat these steps to configure VSwitches for other VPCs in the CEN instance that require traffic redirection. Ensure that the availability zone for each VSwitch matches the primary availability zone of the firewall VPC.
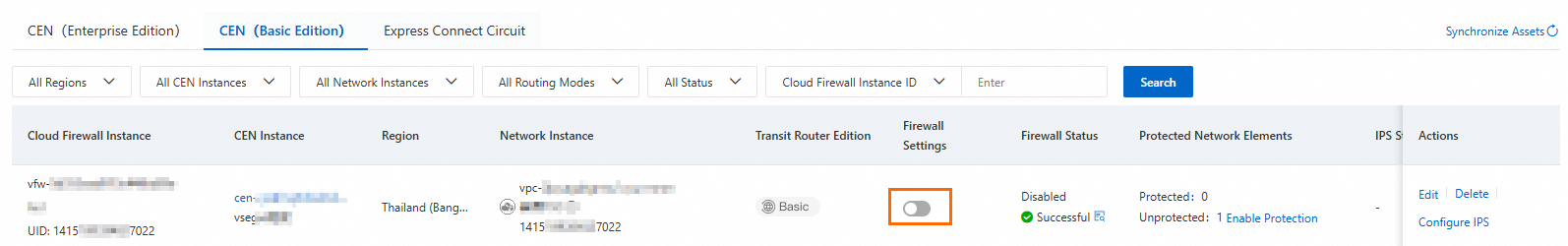
After all VPCs in the region are configured, enable the firewall for each VPC by turning on the toggle in the Firewall column.
Migrating to an active-standby architecture for CEN Enterprise Edition
To migrate a VPC Firewall for a CEN Enterprise Edition instance from an active-active to an active-standby architecture, you must delete the traffic redirection scenario in the target region, recreate the VPC Firewall, and then restore the original traffic redirection scenario.
Step 1: Disable and delete the traffic redirection scenario
Log on to the Cloud Firewall console. In the left-side navigation pane, click Firewall.
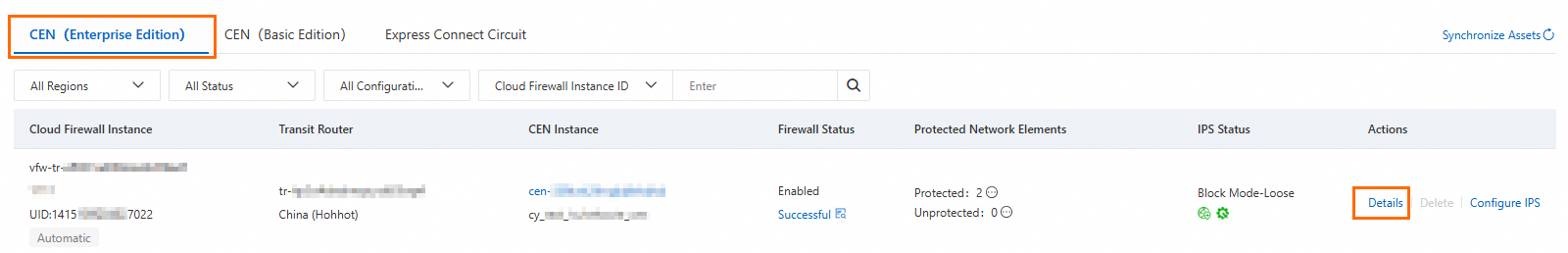
On the tab, find the firewall for the target region and click Details in the Actions column.
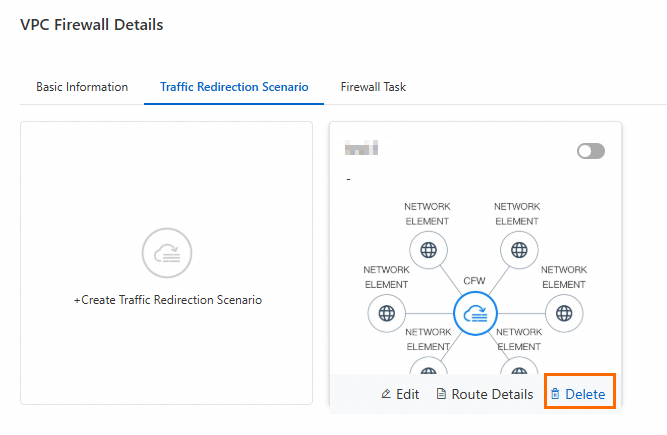
On the tab, disable the scenario by turning off the switch.
In the Disable Traffic Redirection Scenario dialog box, select Roll Back Route and click OK. This is the recommended option.
While the scenario is being disabled, you can monitor the task progress on the Firewall Task tab.
After the traffic redirection scenario is disabled, click Delete. Then, close the VPC Firewall Details panel.
Step 2: Delete the VPC Firewall
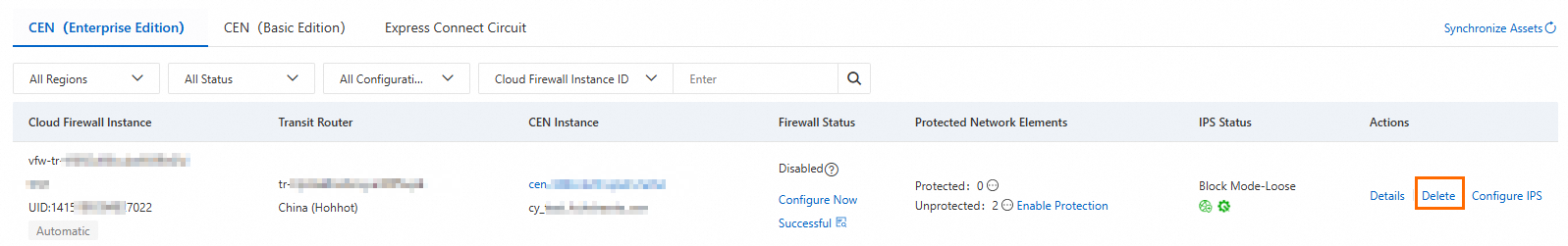
Find the VPC Firewall for the target region and click Delete in the Actions column.
In the Delete dialog box, click OK to delete the firewall instance.
Step 3: Create a VPC Firewall and configure traffic redirection
Find the CEN instance for the target region and click Create in the Actions column.
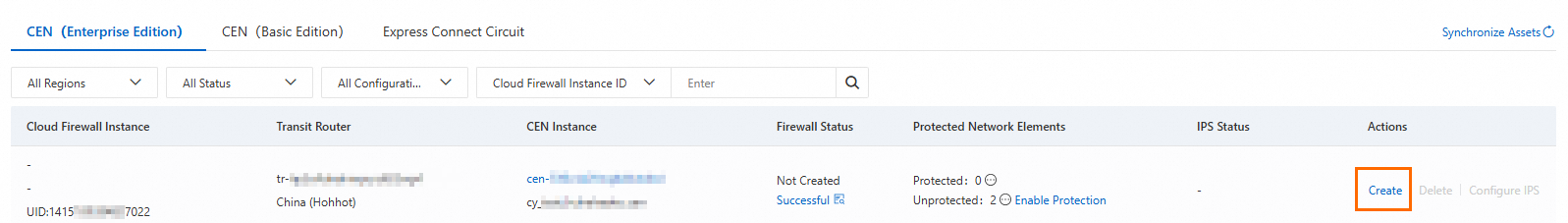
In the Create Firewall panel, select Automatic and click Quick Diagnosis.
For an Enterprise Edition transit router, use this feature to verify that the prerequisites for creating a VPC Firewall are met. After the check is complete, you can view the results in the Precheck wizard. If you are familiar with the creation process, you can click Skip and start creation now.. If the check fails, see Troubleshoot Cloud Firewall enablement failures for solutions.
Configure the settings, including the CIDR block of the firewall VPC, primary and secondary availability zones, and intrusion prevention.
ImportantFor latency-sensitive applications, select the availability zones where your business workloads run as the primary and secondary zones to reduce latency.
The intrusion prevention settings apply to all network instances attached to the same CEN instance.
After the VPC Firewall is created, click Next to reconfigure the traffic redirection scenario.
Click Next to complete the configuration. The VPC Firewall and its traffic redirection scenario are then enabled.