Cloud Firewall uses the AliyunServiceRoleForCloudFW service-linked role to access your resources in other Alibaba Cloud services, enabling access control, traffic monitoring, and traffic analysis. This role is created automatically when you first activate Cloud Firewall — you don't need to create or configure it manually.
This topic describes how to grant the required authorization and how to delete the role when it's no longer needed.
Prerequisites
Before you begin, ensure that you have:
An Alibaba Cloud account, or a Resource Access Management (RAM) user with permissions to create and delete service-linked roles
If your RAM user cannot automatically create the role, see FAQ.
Grant authorization
Cloud Firewall creates AliyunServiceRoleForCloudFW automatically when you complete the following steps for the first time. No action in the RAM console is required.
Subscription
Log on to the Cloud Firewall console.
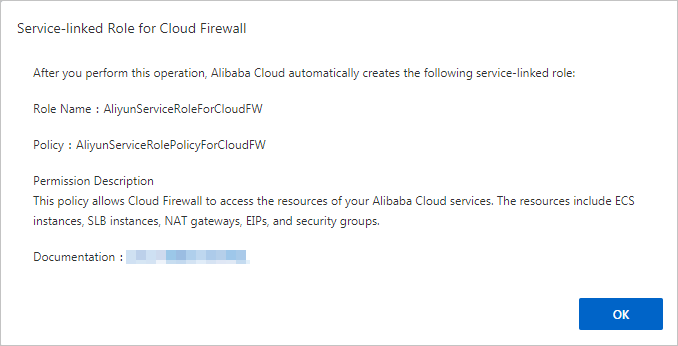
In the Service-Linked Role For Cloud Firewall dialog box, click OK.
If AliyunServiceRoleForCloudFW already exists, this dialog box does not appear and you can use Cloud Firewall immediately.
Pay-as-you-go
Go to the Cloud Firewall purchase page and set Product Type to Pay-as-you-go 2.0.
In the Service-linked Role section, click Create Service-Linked Role.
After authorization is complete, Alibaba Cloud creates AliyunServiceRoleForCloudFW for your Cloud Firewall instance. The role grants Cloud Firewall access to Elastic Compute Service (ECS), Virtual Private Cloud (VPC), Server Load Balancer (SLB), Application Load Balancer (ALB), Network Load Balancer (NLB), Simple Log Service (SLS), Bastionhost, Cloud Enterprise Network (CEN), Security Center, ApsaraDB RDS, Container Service for Kubernetes (ACK), PrivateLink, and other associated services.
To verify the role was created, go to the Roles page of the RAM console and search for AliyunServiceRoleForCloudFW.
Permissions of AliyunServiceRoleForCloudFW
The role is granted the AliyunServiceRolePolicyForCloudFW system policy. The policy allows Cloud Firewall to perform the following actions on the specified services:
| Service | Key permissions |
|---|---|
| ECS | Describe and manage instances, security groups, and network interfaces; import images; manage prefix lists |
| VPC | Describe and manage VPCs, vSwitches, route tables, NAT gateways, EIPs, VPN gateways, and traffic mirror sessions |
| SLB | Describe load balancers, listeners, and health status |
| ALB | List and describe load balancers, listeners, health status, and access control lists (ACLs) |
| NLB | List and describe load balancers, listeners, and health status |
| Simple Log Service | Create and manage projects, log stores, indexes, dashboards, and saved searches |
| Bastionhost | Describe instance attributes and regions |
| CEN | Describe and manage CEN instances, child instances, route entries, transit routers, and route maps |
| Security Center | Describe vulnerability lists, details, and cloud center instances |
| Certificate | Manage CA certificates and sub-CA certificates |
| ACK | Describe clusters, node pools, and namespaces; manage user permissions |
| ApsaraDB RDS | Describe DB instances |
| PrivateLink | Create and manage VPC endpoints |
| Resource Manager | List accounts |
| CloudMonitor | Query metric data |
| RAM | Create service-linked roles for CEN and PrivateLink; delete the Cloud Firewall service-linked role |
The full policy JSON is shown below for reference:
{
"Version": "1",
"Statement": [
{
"Action": [
"ecs:DescribeInstances",
"ecs:DescribeTags",
"ecs:JoinSecurityGroup",
"ecs:LeaveSecurityGroup",
"ecs:AuthorizeSecurityGroupEgress",
"ecs:DescribeRegions",
"ecs:DescribeVpcs",
"ecs:RevokeSecurityGroupEgress",
"ecs:ModifySecurityGroupAttribute",
"ecs:DeleteSecurityGroup",
"ecs:RevokeSecurityGroup",
"ecs:DescribeSecurityGroupAttribute",
"ecs:CreateSecurityGroup",
"ecs:AuthorizeSecurityGroup",
"ecs:DescribeSecurityGroups",
"ecs:DescribeSecurityGroupReferences",
"ecs:ModifySecurityGroupPolicy",
"ecs:ModifySecurityGroupRule",
"ecs:ModifySecurityGroupEgressRule",
"ecs:CreateNetworkInterface",
"ecs:DeleteNetworkInterface",
"ecs:DescribeNetworkInterfaces",
"ecs:CreateNetworkInterfacePermission",
"ecs:DescribeNetworkInterfacePermissions",
"ecs:DeleteNetworkInterfacePermission",
"ecs:AttachNetworkInterface",
"ecs:DetachNetworkInterface",
"ecs:ModifyNetworkInterfaceAttribute",
"ecs:DescribePrefixLists",
"ecs:ListTagResources",
"ecs:ImportImage",
"ecs:ModifyInstanceSpec",
"ecs:CreateImage"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"vpc:DescribeVpcs",
"vpc:DescribeNatGateways",
"vpc:DescribeSnatTableEntries",
"vpc:DescribeForwardTableEntries",
"vpc:DescribeBandwidthPackages",
"vpc:GetNatGatewayAttribute",
"vpc:ModifyNatGatewayAttribute",
"vpc:DescribeEipAddresses",
"vpc:DescribeRouterInterfaces",
"vpc:DescribeRouteTableList",
"vpc:DescribeRouteTables",
"vpc:DescribeVSwitches",
"vpc:CreateRouteEntry",
"vpc:DeleteRouteEntry",
"vpc:CreateVpc",
"vpc:DeleteVpc",
"vpc:CreateVSwitch",
"vpc:DeleteVSwitch",
"vpc:DescribeZones",
"vpc:CreateVirtualBorderRouter",
"vpc:ConnectRouterInterface",
"vpc:ModifyRouterInterfaceAttribute",
"vpc:DeleteRouterInterface",
"vpc:CreateRouterInterface",
"vpc:DeleteVirtualBorderRouter",
"vpc:DeactivateRouterInterface",
"vpc:DescribeVirtualBorderRouters",
"vpc:DescribePhysicalConnections",
"vpc:ModifyVirtualBorderRouterAttribute",
"vpc:DescribeVpcAttribute",
"vpc:DescribeVSwitchAttributes",
"vpc:DescribeHaVips",
"vpc:DescribeVpnConnections",
"vpc:DescribeVpnRouteEntries",
"vpc:DescribeVpnPbrRouteEntries",
"vpc:DescribeVpnGateways",
"vpc:DescribeSslVpnServers",
"vpc:AssociateEipAddress",
"vpc:UnassociateEipAddress",
"vpc:CreateRouteTable",
"vpc:DeleteRouteTable",
"vpc:AssociateRouteTable",
"vpc:UnassociateRouteTable",
"vpc:CreateSnatEntry",
"vpc:DeleteSnatEntry",
"vpc:DescribeSnatTableEntries",
"vpc:DescribeRouteEntryList",
"vpc:DescribeIpv6Addresses",
"vpc:ListVpcPeerConnections",
"vpc:CreateRouteEntries",
"vpc:DeleteRouteEntries",
"vpc:ModifyRouteEntry",
"vpc:DescribeRegions",
"vpc:CheckCanAllocateVpcPrivateIpAddress",
"vpc:CreateTrafficMirrorFilterRules",
"vpc:UpdateTrafficMirrorFilterAttribute",
"vpc:AddSourcesToTrafficMirrorSession",
"vpc:GetTrafficMirrorServiceStatus",
"vpc:ListTrafficMirrorFilters",
"vpc:CreateTrafficMirrorFilter",
"vpc:DeleteTrafficMirrorFilter",
"vpc:UpdateTrafficMirrorSessionAttribute",
"vpc:DeleteTrafficMirrorFilterRules",
"vpc:ListTrafficMirrorSessions",
"vpc:CreateTrafficMirrorSession",
"vpc:RemoveSourcesFromTrafficMirrorSession",
"vpc:DeleteTrafficMirrorSession",
"vpc:OpenTrafficMirrorService",
"vpc:UpdateTrafficMirrorFilterRuleAttribute"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"slb:DescribeRegions",
"slb:DescribeLoadBalancers",
"slb:DescribeLoadBalancerAttribute",
"slb:DescribeLoadBalancerUDPListenerAttribute",
"slb:DescribeLoadBalancerTCPListenerAttribute",
"slb:DescribeLoadBalancerHTTPListenerAttribute",
"slb:DescribeLoadBalancerHTTPSListenerAttribute",
"slb:DescribeHealthStatus",
"slb:DescribeAccessControlListAttribute"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"alb:DescribeRegions",
"alb:ListLoadBalancers",
"alb:GetLoadBalancerAttribute",
"alb:ListListeners",
"alb:GetListenerAttribute",
"alb:GetListenerHealthStatus",
"alb:ListAcls",
"alb:ListAclEntries"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"nlb:DescribeRegions",
"nlb:ListLoadBalancers",
"nlb:GetLoadBalancerAttribute",
"nlb:ListListeners",
"nlb:GetListenerAttribute",
"nlb:GetListenerHealthStatus"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"log:PostLogStoreLogs",
"log:GetProject",
"log:ListProject",
"log:GetLogStore",
"log:ListLogStores",
"log:CreateLogStore",
"log:CreateProject",
"log:DeleteProject",
"log:GetLogStoreLogs",
"log:GetIndex",
"log:CreateIndex",
"log:UpdateIndex",
"log:CreateDashboard",
"log:ClearLogStoreStorage",
"log:UpdateLogStore",
"log:UpdateDashboard",
"log:CreateSavedSearch",
"log:UpdateSavedSearch",
"log:DeleteLogStore",
"log:DeleteSavedSearch",
"log:GetSavedSearch",
"log:ListSavedSearch",
"log:DeleteDashboard",
"log:GetDashboard",
"log:ListDashboard",
"log:GetLogStoreHistogram"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"yundun-bastionhost:DescribeInstance",
"yundun-bastionhost:DescribeRegions",
"yundun-bastionhost:DescribeInstances",
"yundun-bastionhost:DescribeInstanceBastionhost",
"yundun-bastionhost:DescribeInstanceAttribute"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"cen:DescribeCens",
"cen:DescribeCenAttachedChildInstances",
"cen:DescribeCenAttachedChildInstanceAttribute",
"cen:AttachCenChildInstance",
"cen:DetachCenChildInstance",
"cen:PublishRouteEntries",
"cen:WithdrawPublishedRouteEntries",
"cen:DescribePublishedRouteEntries",
"cen:DescribeCenRegionDomainRouteEntries",
"cen:ModifyCenAttribute",
"cen:CreateCenRouteMap",
"cen:DeleteCenRouteMap",
"cen:ModifyCenRouteMap",
"cen:DescribeCenRouteMaps",
"cen:DescribeCenChildInstanceRouteEntries",
"cen:CreateCenChildInstanceRouteEntryToCen",
"cen:DeleteCenChildInstanceRouteEntryToCen",
"cen:ListTransitRouters",
"cen:CreateTransitRouter",
"cen:DeleteTransitRouter",
"cen:ListTransitRouterAttachments",
"cen:CreateTransitRouterVpcAttachment",
"cen:DeleteTransitRouterVpcAttachment",
"cen:UpdateTransitRouterVpcAttachmentAttribute",
"cen:UpdateTransitRouterPeerAttachmentAttribute",
"cen:CreateTransitRouterVbrAttachment",
"cen:DeleteTransitRouterVbrAttachment",
"cen:ListTransitRouterPeerAttachments",
"cen:ListTransitRouterVpcAttachments",
"cen:ListTransitRouterVbrAttachments",
"cen:ListTransitRouterAvailableResource",
"cen:CreateTransitRouterRouteTable",
"cen:UpdateTransitRouterRouteTable",
"cen:DeleteTransitRouterRouteTable",
"cen:ListTransitRouterRouteTables",
"cen:CreateTransitRouterRouteEntry",
"cen:DeleteTransitRouterRouteEntry",
"cen:ListTransitRouterRouteEntries",
"cen:ListTransitRouterRouteTableAssociations",
"cen:AssociateTransitRouterAttachmentWithRouteTable",
"cen:DissociateTransitRouterAttachmentFromRouteTable",
"cen:ListTransitRouterRouteTablePropagations",
"cen:EnableTransitRouterRouteTablePropagation",
"cen:DisableTransitRouterRouteTablePropagation",
"cen:ModifyCenUserQuota",
"cen:ReplaceTransitRouterRouteTableAssociation",
"cen:CheckTransitRouterService",
"cen:ListTransitRouterPrefixListAssociation"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"netana:DescribeNetworkQuotas",
"netana:DescribeNetworkQuotaRequestResult",
"netana:CreateNetworkQuotaRequest"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"privatelink:CheckProductOpen",
"privatelink:OpenPrivateLinkService",
"privatelink:CreateVpcEndpoint",
"privatelink:DeleteVpcEndpoint",
"privatelink:ListVpcEndpoints",
"privatelink:ListVpcEndpointZones",
"privatelink:AddZoneToVpcEndpoint",
"privatelink:RemoveZoneFromVpcEndpoint",
"privatelink:ListVpcEndpointServicesByEndUser"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"yundun-sas:DescribeVulList",
"yundun-sas:DescribeVulDetails",
"yundun-sas:DescribeCloudCenterInstances"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"yundun-cert:DescribeCACertificateList",
"yundun-cert:GetUserStatus",
"yundun-cert:CreateTestOrder",
"yundun-cert:CreateRootCACertificate",
"yundun-cert:CreateSubCACertificate"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"cs:DescribeUserQuota",
"cs:DescribeClusterNodes",
"cs:DescribeClusterNodePools",
"cs:DescribeClusterNodePoolDetail",
"cs:DescribeUserClusterNamespaces",
"cs:DescribeClustersV1",
"cs:DescribeClusterUserKubeconfig",
"cs:DescribeClusterResources",
"cs:DescribeClusterDetail",
"cs:GetClusters",
"cs:DescribeUserPermission",
"cs:UpdateUserPermissions",
"cs:GrantPermissions",
"cs:CleanClusterUserPermissions"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"rds:DescribeDBInstances"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": "ram:CreateServiceLinkedRole",
"Resource": "*",
"Effect": "Allow",
"Condition": {
"StringEquals": {
"ram:ServiceName": "cen.aliyuncs.com"
}
}
},
{
"Action": [
"resourcemanager:ListAccounts"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"cms:QueryMetricList",
"cms:QueryMetricData",
"cms:QueryMetricLast"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": "yundun-aegis:DescribeAccesskeyLeakList",
"Resource": "*",
"Effect": "Allow"
},
{
"Action": "ram:DeleteServiceLinkedRole",
"Resource": "*",
"Effect": "Allow",
"Condition": {
"StringEquals": {
"ram:ServiceName": "cloudfw.aliyuncs.com"
}
}
},
{
"Action": "ram:CreateServiceLinkedRole",
"Resource": "*",
"Effect": "Allow",
"Condition": {
"StringEquals": {
"ram:ServiceName": "privatelink.aliyuncs.com"
}
}
}
]
}For more information about access policy syntax, see Policy elements.
Delete the service-linked role
AliyunServiceRoleForCloudFW can only be deleted after your Cloud Firewall instance expires and is automatically released.
To delete the role:
Wait for your Cloud Firewall instance to expire and be automatically released.
Delete AliyunServiceRoleForCloudFW from the RAM console. For instructions, see Delete a RAM role.
FAQ
Why can't my RAM user automatically create AliyunServiceRoleForCloudFW?
RAM users require explicit permissions to create or delete AliyunServiceRoleForCloudFW. Attach the following policy to the RAM user, then try again. For instructions on attaching policies, see Grant permissions to a RAM user.
{
"Statement": [
{
"Action": [
"ram:CreateServiceLinkedRole"
],
"Resource": "acs:ram:*:ID of your Alibaba Cloud account:role/*",
"Effect": "Allow",
"Condition": {
"StringEquals": {
"ram:ServiceName": [
"cloudfw.aliyuncs.com"
]
}
}
}
],
"Version": "1"
}