Unrestricted internet access for your public-facing assets can lead to risks such as leaks of core business data and cyberattacks on your business systems. To mitigate these risks, you can configure an Internet Firewall access control policy to manage unauthorized access between your public assets and the internet. This helps reduce the risk of data exfiltration and minimizes your assets' internet-exposed attack surface. This topic shows how to configure an access control policy that allows an instance to access only a specific domain name.
Example scenario
In this scenario, you have an ECS instance that is associated with the elastic IP address 47.100.XX.XX. For security purposes, you need to configure a policy to allow this instance to access only the www.aliyun.com domain name.
Prerequisites
Before you begin, ensure that you have:
An active Cloud Firewall subscription with the Internet firewall feature enabled. For setup instructions, see Purchase Cloud Firewall and Internet Firewall
The public IP address of the server you want to protect
Procedure
Log on to the Cloud Firewall console.
In the navigation pane on the left, choose .
On the Outbound tab, click Create Policy. In the Create Outbound Policy panel, click the Create Policy tab.
Configure a high-priority policy to allow access to www.aliyun.com and a low-priority policy to deny all other outbound traffic.
Configure a policy to allow the instance to access www.aliyun.com. The key settings are as follows:
Parameter
Description
Example value
Source Type
The source of the network traffic. Select a source type and enter the corresponding address.
IP
Source
Enter the public IP address of the ECS instance. In this example, the IP address is 47.100.XX.XX/32.
Destination Type
The destination of the network traffic. Select a destination type and enter the corresponding address.
Domain Name
Destination
Enter the domain name that the instance is allowed to access: www.aliyun.com.
NoteYou can also perform a Domain Name System (DNS) lookup on the domain name and use the resolved IP address.
Protocol Type
The transport layer protocol. Valid values are TCP, UDP, ICMP, and ANY. If you are unsure of the protocol, select ANY.
TCP
Port Type
The destination port type and destination port.
Port
Port
Enter 0/0 to specify all ports.
Application
The application type of the traffic.
ANY
Action
The action to take on traffic that matches the policy.
Allow: allows the traffic.
Deny: blocks the traffic and does not send a notification.
Monitor: In this mode, traffic is allowed by default. You can filter and observe this traffic using the relevant fields in traffic logs. After a period of observation, you can change the action to Allow or Deny as needed.
Allow
Description
Enter a description for the policy to help you identify its purpose.
Allow policy for www.aliyun.com
Priority
The priority of the policy. The default is Lowest.
Highest
Policy Validity Period
Set the validity period for the policy. The policy can match traffic only within the validity period.
Always
One-Time: Select a single time period.
Recurring: Select a recurring time period and effective dates.
NoteThe start time of the effective date must be earlier than the end time. The policy is expected to take effect in 3 to 5 minutes.
If you select Repeat Indefinitely, the end time is automatically set to 2099-12-31.
Related FAQ: Does a policy take effect if the recurrence cycle spans multiple days?
Always
Status
Specifies whether to enable the policy. If you do not enable the policy when you create it, you can enable it from the policy list later.
Enabled
Configure a deny policy that blocks the instance from accessing all public IP addresses. The key settings are as follows:
Source: 47.100.XX.XX/32
Destination: 0.0.0.0/0, which indicates all IP addresses.
Protocol Type: ANY
Port: 0/0, which indicates all ports.
Application: ANY
Action: Deny
Priority: Lowest
After the policies are configured, ensure that the allow policy for www.aliyun.com has a higher priority than the deny policy for all other traffic.
View policy hits
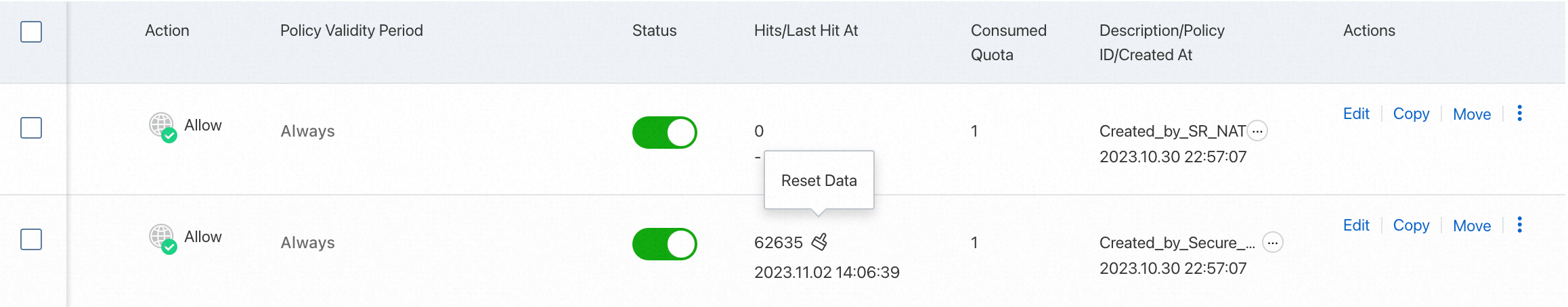
After your service has been running for a period of time, you can view the hit count and last hit time of access control policies in the Hits / Last Hit At column of the access control policy list.
Click the hit count to view the traffic logs on the Traffic Logs page. For more information, see Log audit.