This topic describes how to configure Transport Layer Security (TLS) versions and cipher suites for your CDN domain to balance browser compatibility and security. Configure TLS settings after you enable HTTPS for your domain.
TLS versions
TLS is designed to ensure the security and integrity of data that is transmitted between two applications. A typical use case of TLS is HTTPS. HTTPS, also known as HTTP over TLS, is a secure version of HTTP. HTTPS runs below the top application layer (HTTP) and above the transport layer (TCP). HTTPS provides data encryption and decryption services.
Version | Description | Mainstream browser |
TLSv1.0 | In 1999, RFC 2246 introduced TLS 1.0 as an update to SSL 3.0. However, TLS 1.0 is vulnerable to various attacks, such as BEAST and POODLE attacks. TLS 1.0 is no longer recommended for network protection due to weak encryption performance. TLS 1.0 is not compliant with Payment Card Industry Data Security Standard (PCI DSS). |
|
TLS 1.1 | In 2006, RFC 4346 introduced TLS 1.1 as an update to TLS 1.0. TLS 1.1 fixed specific vulnerabilities in TLS 1.0. |
|
TLS 1.2 | In 2008, RFC 5246 introduced TLS 1.2, which is a widely used TLS version. |
|
TLS 1.3 | In 2018, RFC 8446 introduced TLS 1.3 as the latest TLS version. TLS 1.3 supports the zero round trip time (0-RTT) mode and allows you to establish faster connections. TLS 1.3 supports only key exchange algorithms of perfect forward secrecy to enhance security. |
|
Configure TLS settings
An SSL certificate is configured before you configure TLS. For more information, see Configure an SSL certificate.
By default, TLS 1.0, TLS 1.1, TLS 1.2, and TLS 1.3 are enabled.
Log on to the CDN console.
In the left navigation pane, click Domain Names.
On the Domain Names page, find the target domain name and click Manage in the Actions column.
In the domain's navigation pane, click HTTPS.
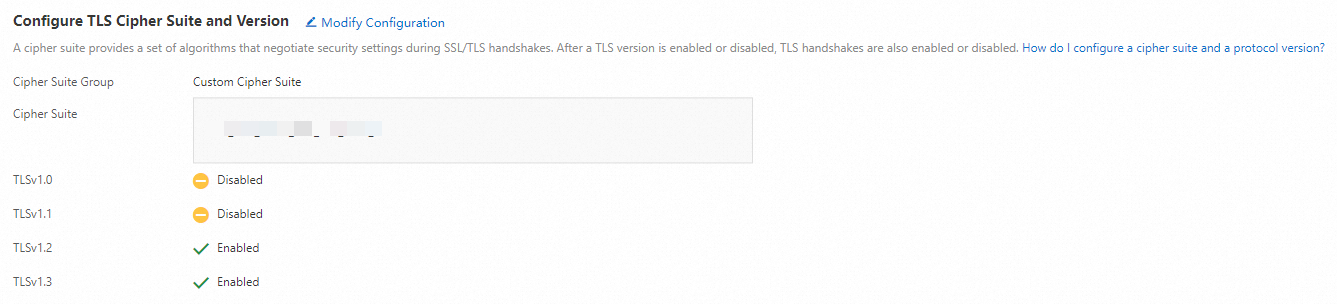
In the Configure TLS Cipher Suite and Version section, configure the cipher suite and versions based on your business requirements.
The following cipher suites are supported. Select a cipher suite based on your business requirements:
All Cipher Suite Groups (Default): Provides low security and high compatibility. For information about supported encryption algorithms, see Default TLS encryption algorithms.
Enhanced Cipher Suite: Provides high security and low compatibility. Supported encryption algorithms:
TLS_AES_256_GCM_SHA384
TLS_AES_128_GCM_SHA256
TLS_CHACHA20_POLY1305_SHA256
ECDHE-ECDSA-CHACHA20-POLY1305
ECDHE-RSA-CHACHA20-POLY1305
ECDHE-ECDSA-AES128-GCM-SHA256
ECDHE-RSA-AES128-GCM-SHA256
ECDHE-ECDSA-AES128-CCM8
ECDHE-ECDSA-AES128-CCM
ECDHE-ECDSA-AES256-GCM-SHA384
ECDHE-RSA-AES256-GCM-SHA384
ECDHE-ECDSA-AES256-CCM8
ECDHE-ECDSA-AES256-CCM
ECDHE-ECDSA-ARIA256-GCM-SHA384
ECDHE-ARIA256-GCM-SHA384
ECDHE-ECDSA-ARIA128-GCM-SHA256
ECDHE-ARIA128-GCM-SHA256
Custom Cipher Suite: Select a cipher suite based on your business requirements.
For more information about TLS versions, see Background information.