Bastionhost lets you connect to databases through an SSH tunnel and run O&M operations under full audit. This topic describes how to set up that tunnel from a Windows client using either a GUI tool or the command-line interface (CLI).
Supported databases include ApsaraDB RDS for MySQL, ApsaraDB RDS for SQL Server, and ApsaraDB RDS for PostgreSQL instances; PolarDB for MySQL, PolarDB for PostgreSQL, and PolarDB for PostgreSQL (Compatible with Oracle) clusters; and self-managed MySQL, SQL Server, PostgreSQL, and Oracle databases.
How it works
Bastionhost acts as an SSH jump host between your local machine and the target database. Your database O&M tool (or CLI) opens an SSH tunnel to the bastion host. Traffic through that tunnel is forwarded to the database, then recorded for audit.
Because of this architecture, your tool needs two sets of connection details:
SSH tunnel settings — the public O&M address and port of the bastion host, plus an O&M token as the password
Database settings — the actual address and port of the target database
Prerequisites
Before you begin, ensure that you have:
A database O&M tool that supports SSH tunnels installed on your local host (for example, DBeaver, DbVisualizer, Navicat Premium, or Navicat for MySQL)
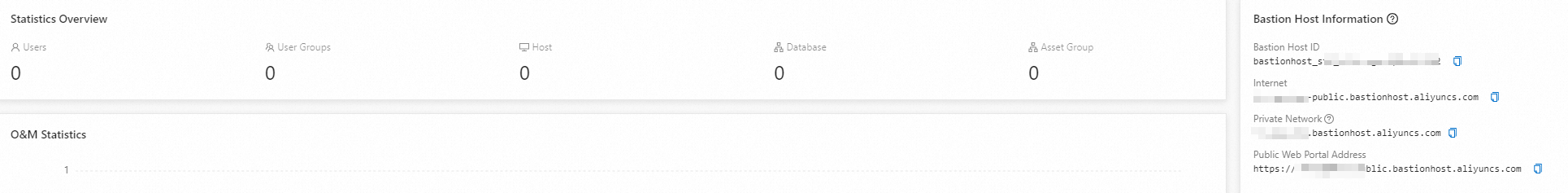
The public O&M address of your bastion host — get this from the Bastion Host Information section on the Overview page of the bastion host console. For instructions, see Log on to the console of a bastion host
Bastionhost provides fixed O&M addresses and supports dynamic O&M IP addresses. Use the O&M address rather than the raw IP address to avoid connection failures caused by IP address changes.
About O&M tokens
An O&M token is a short-lived credential you use as the SSH password when connecting through Bastionhost. Keep the following in mind:
Tokens are valid only within their configured validity period. The Bastionhost administrator sets this period. If O&M review is enabled, the period of the admin-approved token applies.
If the administrator allows it, you can renew a token before it expires. After expiry, apply for a new token. Renewal is not available when O&M review is enabled.
After an O&M token's settings change, apply for a new token or update the existing one for the change to take effect.
Audit records show the identity of the user who requested the token, not the usernames or asset accounts entered in the client.
If a token is valid but the connection still fails, either the concurrent connection limit has been reached (contact the administrator to upgrade the bastion host or release idle connections), or requests from your time window or source IP address have been blocked (contact the administrator to remove the restriction).
Connect using a GUI tool (Navicat Premium)
The following steps use Navicat Premium as an example. The same approach applies to other SSH-tunnel-capable tools.
Get an O&M token. See Obtain an O&M token.
If the database account is not hosted on the bastion host, configure the account details in the O&M Token dialog box before requesting the token. For details on creating a database account, see Use the database management feature.
Open Navicat Premium and create a new connection. On the General tab, set the database connection parameters:
Parameter Description Connection name A name for this connection Host The address of the target database User name The username for the database Password MySQL, SQL Server, or PostgreSQL: leave blank if the account is hosted on the bastion host; otherwise enter the database password. Oracle: if hosted, enter 123456and set the logon attribute as shown in the O&M token; if not hosted, enter the actual database password and set the logon attribute as shown in the O&M token.On the SSH tab, configure the SSH tunnel:
Parameter Description Use SSH tunnel Select Use SSH tunnel Host The public O&M address of your bastion host (from the Bastion Host Information section on the Overview page) Port The O&M port for SSH tunnels. Default: 60022User name Your bastion host username Password The O&M token you obtained in step 1 Double-click the new connection in Navicat Premium to log on to the database and run O&M operations.
Connect using the CLI
This example shows how to connect to a MySQL database over an SSH tunnel using the CLI.
The CLI method is not supported for Oracle databases.
Log on to the O&M portal. See Log on to the O&M portal.
In the left-side navigation pane, click Databases.
On the Databases page, find the target database and click O&M Token in the O&M Token column.
In the O&M Token dialog box, select a database account and click Obtain O&M Token.
If the database account is not hosted on the bastion host, configure the account details in the dialog box first. See Use the database management feature.
Open a terminal and run the following command to create the SSH tunnel:
Parameter Description Example <localport>A local port to listen on after the tunnel is created. Choose any unused port. 3307<databaseAddress>The address of the target database rm-xxxx.mysql.rds.aliyuncs.com<databasePort>The port of the target database 3306<bastionusername>Your bastion host username alice<bastionAddress>The public O&M address of your bastion host (from the Bastion Host Information section on the Overview page) bh-xxxx.bastionhost.aliyuncs.com<bastionPort>The O&M port for SSH. Default: 6002260022ssh -N -L <localport>:<databaseAddress>:<databasePort> <bastionusername>@<bastionAddress> -p <bastionPort>When prompted for a password, enter the O&M token and press Enter.
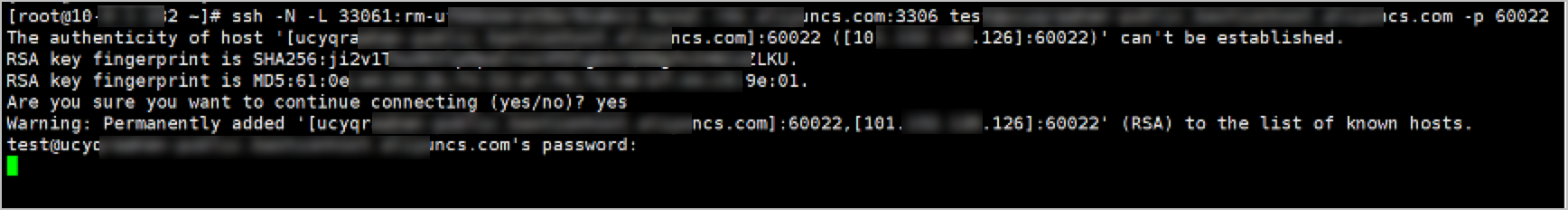
Open a new terminal window and verify that the local port is listening. If
LISTENappears in the output, the tunnel is active.
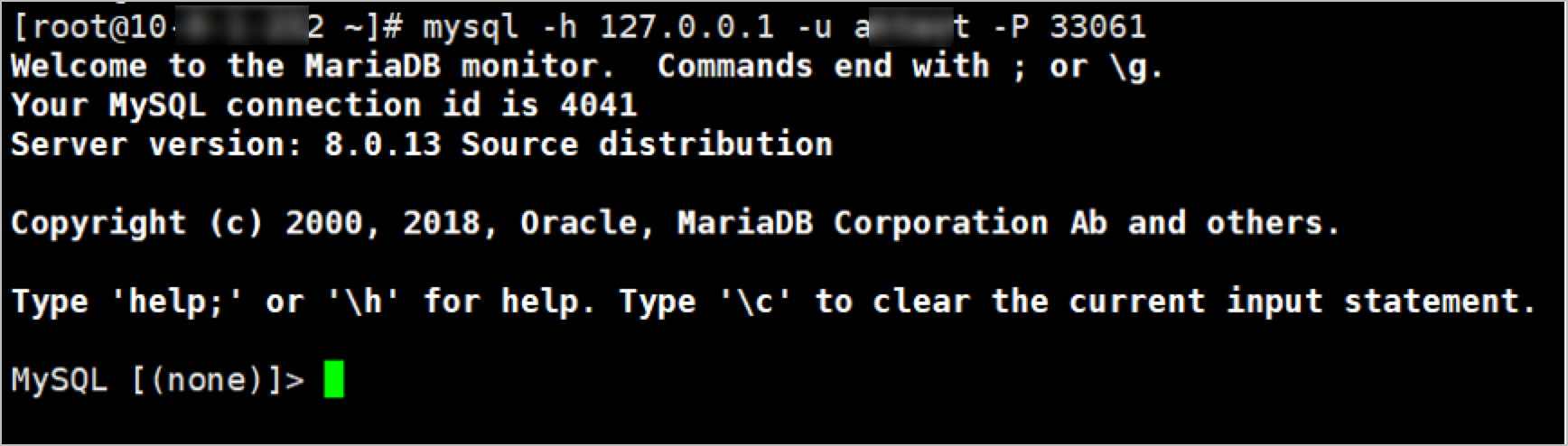
Connect to the MySQL database:
<accountname>: the username of the MySQL database<localport>: the local port you specified in step 5
mysql -h 127.0.0.1 -u <accountname> -P <localport>After the connection is established, run commands to perform O&M operations on the database.