Use Bastionhost as a unified SSH proxy and audit center for Platform for AI (PAI) Data Science Workshop (DSW) instances. This eliminates scattered access points, enforces fine-grained access control, and records every session for security accountability—reducing risks such as data breaches, model tampering, and computing resource abuse.
Background
Algorithm engineers and operations and maintenance (O&M) engineers access PAI-DSW development environments over SSH to debug code, configure environments, and manage data. Without a centralized access layer, this creates several security gaps:
Scattered access points: Exposing SSH ports directly to the internet or office network expands the attack surface.
Shared privileged accounts: Multiple users sharing a
rootaccount makes it impossible to follow least privilege or assign clear operational responsibility.No operational visibility: Commands and file transfers inside DSW instances are invisible to administrators. When a security incident occurs, tracing its source is difficult.
Data exfiltration risk: Commands like
scpandwgetcan silently move sensitive model files and datasets out of DSW instances.
Why use Bastionhost
Bastionhost addresses each pain point above:
| Benefit | What it eliminates |
|---|---|
| Centralized SSH access | No public IP or exposed ports on DSW instances. All O&M traffic stays on the internal network, hiding real asset addresses from external scans. |
| Unified identity management | Integrates with Resource Access Management (RAM), Active Directory (AD), Lightweight Directory Access Protocol (LDAP), and Identity as a Service (IDaaS) to replace shared root accounts with real-name, individually tracked O&M identities. |
| Fine-grained access control and auditing | Binds specific users to specific host accounts with time and IP restrictions. Session logs and video playback cover every SSH session. |
| Non-intrusive integration | No agent installation on DSW instances. Add an asset, configure a rule, and bring new compute resources into the secure O&M system immediately. |
| Automated credential security | Automatic SSH key rotation, two-factor authentication (MFA), and batch script delivery reduce manual credential maintenance and lower the risk from operational errors. |
| End-to-end compliance | Centralized authentication, access control, and session recording support audit compliance requirements in regulated industries such as finance and government. |
Solution architecture
Bastionhost acts as the sole proxy between O&M engineers and PAI-DSW instances. Engineers never connect directly to DSW. Instead, they log on to Bastionhost, pass identity and permission checks, and Bastionhost proxies the connection to the target DSW instance.

The architecture has four layers:
Identity and authentication: Engineers use RAM user identities to log on to the Bastionhost O&M portal. Optional MFA adds a second factor. Bastionhost also integrates with AD, LDAP, and IDaaS for enterprise identity sources.
Access proxy: Bastionhost is the sole SSH entry point. It connects to PAI-DSW instances over the internal network inside a virtual private cloud (VPC), with no ports exposed to the internet.
Asset and permission management: PAI-DSW instances are registered as host assets. Administrators create authorization rules that bind users to host accounts, with optional restrictions on time windows and source IP addresses.
Control and audit: All SSH sessions are monitored and recorded in real time. Command control policies can block high-risk operations such as deleting model files or transferring data. All records are queryable and playable back, and can be archived to Simple Log Service (SLS) for long-term storage and analysis.
Prerequisites
Before starting, confirm the following:
Bastionhost edition: Use the Basic Edition for O&M without secret rotation. Use the Enterprise Dual-Engine Edition if you need SSH key rotation. For a full comparison, see Version comparison.
Network connectivity: The Bastionhost instance and DSW instances must be able to reach each other. They can be in the same VPC, or connected via a VPC peering connection or Cloud Enterprise Network (CEN).
SSH support: The DSW instance must accept SSH connections on port 22.
Step 1 of 5: Create a Bastionhost instance
Purchase a Bastionhost instance.
Go to the Bastionhost purchase page.
Specify the following configurations and click Buy Now to complete payment. For parameters not listed here, keep the default values or configure as needed. See Quickly purchase and log on to a Bastionhost instance for the full list.
Configuration item
Description
Example value
Region
Select the same region as your DSW instances.
China (Hangzhou)
Edition
Select the edition based on your needs. See Edition selection guide.
Enterprise Dual-Engine Edition
Enable the Bastionhost instance.
Log on to the Bastionhost console. In the top menu bar, select the destination region. > Note: On first access, create a service-linked role to enable comprehensive security O&M protection. Follow the on-screen prompt to create the role.
In the instance list, find the instance you created and click Enable. In the panel that appears, configure the following settings. See Enable a Bastionhost instance for details.
Configuration item
Description
Example value
Select network
Select the VPC and vSwitch. The VPC cannot be changed after the instance is enabled. Use the same VPC as your DSW instances to ensure internal network connectivity.
test_vpc
Select vSwitch and primary zone
The Enterprise Dual-Engine Edition supports active-active deployment across primary and secondary vSwitch zones. Select the primary zone vSwitch.
vsw_1
ECS security groups
Add the instance to at least one basic security group. Access rules are automatically generated to allow the instance to reach assets in that group. Note: A Bastionhost instance cannot be added to an advanced security group—configure access rules in advanced security groups manually. Bastionhost also cannot be added to security groups managed by other cloud products; create a new basic security group if needed.
test_sg
Click Next. After the startup check passes, click Enable.
The instance enters the Initializing state. This typically takes 10 to 15 minutes.
When the status changes to Running, the instance is ready.
Enable public network access. In the instance list, find your instance and turn on the Network > Internet switch
 .
.
Step 2 of 5: Create a DSW instance
Log on to the PAI console. Select the target region. In the left navigation pane, click Workspace List and select your workspace.
In the left navigation pane, choose Model Development and Training > Data Science Workshop (DSW). Go to the Developer Environment Instances tab and click Create Instance. Configure the following parameters. For parameters not listed here, keep the defaults or see List of all console parameters.
Configuration item Description Example value Instance name Enter a name for the instance. dsw_test Resource type Specify the resource type. Public Resources Resource specification Select a specification. If the specified specification is out of stock, choose another from the list. ecs.gn7i-c8g1.2xlarge(1 A10 GPU, 8 vCPUs, 30 GiB memory)Image configuration Select Alibaba Cloud image. ModelScope images offer broad compatibility and a comprehensive set of third-party libraries. modelscope:1.31.0-pytorch2.8.0-gpu-py311-cu124-ubuntu22.04(Python 3.11, CUDA 12.4)VPC configuration Select the same VPC as your Bastionhost instance. test_vpc Security group Select the target security group. test_sg Enable SSH Turn on this switch. On SSH Public Key Generate an SSH key pair following Generate an SSH public key and paste the public key here. — Custom service Add the listener port to the Inbound rules of the security group. Listener port: 22 Click OK. When the instance status changes to Running, the instance is ready.
If the Bastionhost and DSW instances are in different VPCs, connect them via a VPC peering connection or Cloud Enterprise Network (CEN). To verify connectivity after setup, use Network diagnosis.
Step 3 of 5: Add the DSW instance as a host asset
Create a host.
Log on to the Bastionhost console. Find your instance and click Manage in the Actions column.
In the left navigation pane, choose Assets > Hosts. Then choose Import Other Hosts > Create Host. Fill in the following fields and click Create. See Create a host for details.
Configuration item
Description
Example value
Operating system
Select the OS type of the DSW instance.
Linux
Host IP address
Enter the DSW instance's internal IP address. Find it in the PAI console under Instance Configuration > Network Information > Internal IP Address > User NIC.
192.168.1.40
Hostname
Set a descriptive name.
dsw-model-dev
Create a host account. In the host list, find the host you created and click Create host account in the Actions column. Configure the following settings and click Create. See Manage host accounts for details.
Configuration item Description Example value Protocol Select the connection protocol. SSH Logon name Enter the username for SSH logon. DSW instances provide only the rootuser by default.root Privileged account Specify whether this is a privileged account. Yes Authentication type Select the authentication method. Private Key Private key Upload the private key that matches the SSH public key configured in Step 2. — Encryption Password If you set a passphrase when generating the key pair, enter it here. —
Step 4 of 5: Configure authorization and access policies
Create a user. In the left navigation pane, choose Users > Users. Then choose Import Other Users > Create User. Fill in the following fields and click Create. See Manage users for details.
Configuration item Description Example value Logon name Username for logging on to the Bastionhost portal. user1 Authentication method Authentication method for the Bastionhost portal. Local Authentication Password Logon password. — Confirm password Confirm the password. — Display name Name shown in the console. user1 Mobile number Used for SMS-based two-factor authentication when MFA is enabled. 159\*\*\*\*\*\*\* Email Used for email-based two-factor authentication when MFA is enabled. test\*\*\*@aliyun.com Grant host permissions to the user.
In the user list, find the user you created and click Permission on Host in the Actions column to open the Managed Hosts page.
Click Permission on Host. In the panel, select the target host and click OK. See Grant asset permissions to a user for details.
Grant host account permissions to the user.
Find the host you authorized in the previous step. In the Authorized Accounts column, click No accounts found. Click here to authorize the user to manage the accounts of the asset group.
Select the target account (for example,
[ssh] root) and click Update. See Grant asset account permissions to a user for details.
(Optional) Create a command control policy. Control policies let you block specific commands—for example, preventing engineers from running file exfiltration commands on DSW instances.
In the left navigation pane, click Control Policies. Then click Create Control Policy.
Fill in the following fields and click Create Control Policy. See Configure a control policy for details.
Configuration item
Description
Example value
Name
Policy name.
block-dsw-dangerous-cmds
Command policy
Click Command Policy and set: Commands that require control to (Blacklist) Listed Commands Are Not Allowed, then add the specific command.
Command:
ifconfigOn the Assets and users to which policy is attached page:
Select Takes Effect on Selected All Assets. Choose Asset > Hosts > Associate Host, select the target host, and click OK.
Select Apply to Selected Users. Choose Users > Associate User, select the target user, and click OK.
(Optional) Create a key rotation task — Enterprise Dual-Engine Edition only. Automatic SSH key rotation generates a new key pair on a schedule. The public key is updated on the DSW instance, and the private key stored in Bastionhost is replaced.
In the left navigation pane, choose Assets > Password Change. Then click Create Password Change Task.
In the panel, fill in the following fields and click Create. See Create a password change task for details.
Configuration item
Description
Example value
Task name
Name for the task.
test_task
Task type
Select Key Rotation to rotate SSH key pairs.
Key Rotation
Execution method
Select Periodic for recurring rotation or Scheduled for a one-time run.
Scheduled
Executed at
Specify when the task runs.
2025-12-23 17:23:45
After the task is created, click Associate Account in the panel. On the Managed Accounts tab, click Add Host Account, select the target host account, and click Add.
Step 5 of 5: Verify and audit
Log on to the Bastionhost portal.
Go to the Bastionhost instance management page. In the left navigation pane, click Overview.
Open the URL shown under Bastion Host Information > Public Web Portal Address. Log on with the user you created (for example, user1). > Note: If prompted for Two-factor authentication, select a verification method and complete the verification.
After logon, you are directed to the Hosts page of the Bastionhost portal.
Connect to the DSW instance. On the Hosts page, find the target host (for example, dsw-model-dev). In the Remote Connection column, click the
 icon to open a terminal session.
icon to open a terminal session.Verify the control policy. If you configured a command control policy, run a blocked command in the terminal—for example,
ifconfig. If the policy is working, the terminal returnspermission denied by rule.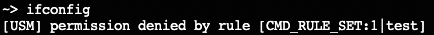
Review session records. Go to the Bastionhost instance management page. In the left navigation pane, choose O&M Audit > Session Audit to search sessions and play back recorded operations. See Search for and view sessions for details.
Risk description
Overly broad permissions: Authorization rules that are too permissive or command policies that are too lenient undermine the security goal. Follow least privilege when assigning permissions.
Network policy changes: Changes to security group rules or network access control lists (ACLs) in the VPC may interrupt connectivity. When adjusting network policies, keep port 22 open between Bastionhost and the DSW instance.
DSW instance IP address changes: After a DSW instance stops and restarts, its internal IP address may change. If the IP changes, update the corresponding host asset in Bastionhost—otherwise connections will fail. For critical DSW instances, configure a fixed private IP address or use an automated script to update the address.
FAQ
Bastionhost cannot connect to the DSW instance
| Possible cause | Solution |
|---|---|
| Network connectivity issue | Run a network diagnosis in the Bastionhost console. See Network diagnosis. |
| DSW instance security group blocks Bastionhost | Check the inbound rules of the DSW instance security group and confirm that TCP port 22 is allowed from the Bastionhost security group. |
| DSW instance IP address has changed | Check the latest internal IP address in the PAI console and update the host asset in Bastionhost. |
A "permission denied" or key error appears during logon
| Possible cause | Solution |
|---|---|
| SSH public key not correctly configured on the DSW instance | Check the public key on the DSW instance and confirm it was added correctly. |
| Private key in Bastionhost does not match the DSW instance's public key | In the host account configuration in Bastionhost, re-upload the correct private key. |
| User, asset, and host account not correctly associated in the authorization rule | Check the authorization rules in Bastionhost and confirm that the user, host, and host account are all correctly bound. |
The command control policy is not in effect
| Possible cause | Solution |
|---|---|
| Policy not associated with the target user or asset | In the policy management section, check the association scope and confirm the policy is linked to the correct user and asset. |
| Command matching rule is incorrect | Check the command format in the policy—verify that wildcards are correct and that the pattern matches the command as actually run. |