When Anti-DDoS Proxy always forwards traffic—even during quiet periods—your service incurs extra latency. Cloud service interaction eliminates that overhead: traffic flows directly to your cloud resource when no attack is detected, and automatically shifts to Anti-DDoS Proxy for scrubbing only when an attack occurs.
Prerequisites
Before you begin, make sure that:
Your service runs on an Alibaba Cloud resource with a public IP address—an elastic IP address (EIP), a Web Application Firewall (WAF) instance, an Elastic Compute Service (ECS) instance, or a Server Load Balancer (SLB) instance.
You have purchased one of the following instances:
Anti-DDoS Proxy (Chinese Mainland) — Profession mitigation plan
Anti-DDoS Proxy (Outside Chinese Mainland) — Insurance or Unlimited mitigation plan
ImportantThe instance's clean bandwidth and queries per second (QPS) must meet your service's mitigation requirements. For details, see Purchase an Anti-DDoS Proxy instance.
Your website is already added to the instance. See Add one or more websites.
The instance is forwarding traffic as expected. See Verify the forwarding configurations on your on-premises computer.
How it works
Traffic behavior changes based on whether an attack is in progress:
| Phase | Traffic behavior |
|---|---|
| No attack | Traffic goes directly from the client to your cloud resource. Anti-DDoS Proxy is not involved. |
| Attack detected | Traffic automatically shifts to Anti-DDoS Proxy for scrubbing. Only clean traffic is forwarded to your cloud resource. |
| After the attack stops | Anti-DDoS Proxy waits for the Waiting Time of Switchback you configure, then automatically switches traffic back to your cloud resource. |
Create a cloud service interaction rule
Log on to the Anti-DDoS Proxy console.Anti-DDoS Proxy console
In the top navigation bar, select the region that matches your instance:
Chinese Mainland — for Anti-DDoS Proxy (Chinese Mainland) instances
Outside Chinese Mainland — for Anti-DDoS Proxy (Outside Chinese Mainland) instances
In the left-side navigation pane, choose Provisioning > Sec-Traffic Manager.
On the General Interaction tab, click Add Rule.
In the Add Rule panel, set Interaction Scenario to Cloud Service Interaction, configure the remaining parameters, and click Next. Figure 1 Sample configuration of a cloud service interaction rule in the Anti-DDoS Proxy (Chinese Mainland) console
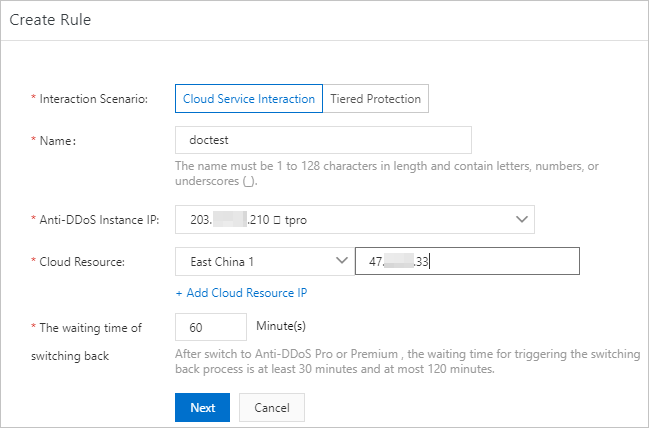
Parameter Description Interaction Scenario Select Cloud Service Interaction. Rule Name Enter a name of up to 128 characters. Letters, digits, and underscores (_) are supported. Anti-DDoS Pro Select the Anti-DDoS Proxy instance to associate. Resource for Interaction Enter the IP address of your cloud resource. Accepted types: EIP, ECS instance IP, SLB instance IP, WAF instance IP. Click Add IP Address of Cloud Resource to add more. Up to 20 IP addresses are supported. NoteWhen multiple IP addresses are added, all are associated with the same Anti-DDoS Proxy instance. If one IP is attacked, traffic shifts to the other IPs—not yet to Anti-DDoS Proxy. Traffic is sent to Anti-DDoS Proxy only when all IP addresses are under attack. To configure this multi-IP pattern explicitly, see Share one Anti-DDoS Proxy instance among multiple cloud resources.
Waiting Time of Switchback The time Anti-DDoS Proxy waits after an attack stops before switching traffic back to your cloud resource. Valid range: 30–120 minutes. Set this to 60 minutes unless you have a specific reason to adjust it. Switchback conditions:
Scenario What happens Attack stops and waiting time elapses (automatic switchover) Traffic automatically switches back to the cloud resource. Manual switchover was used Traffic does not switch back automatically. Click Switchback to switch manually. Blackhole filtering is active on Anti-DDoS Proxy Traffic from a cloud resource cannot be switched to the instance—including before the waiting time that starts from when blackhole filtering was triggered. Blackhole filtering triggered on a cloud resource Traffic automatically switches to Anti-DDoS Proxy. Switchback is blocked until blackhole filtering is deactivated. Once deactivated, traffic switches back immediately regardless of the remaining waiting time. Blackhole filtering triggered on all associated cloud resources Switchback fails for all resources. As blackhole filtering is individually deactivated per resource, traffic switches back to that resource. Update your DNS records as prompted, then click Complete. For the rule to take effect, point your domain's DNS record to the CNAME provided by Sec-Traffic Manager. If your domain is managed through Alibaba Cloud DNS, update the record in the Alibaba Cloud DNS console. For verification steps, see Verify the forwarding configurations on your on-premises computer. For DNS update instructions, see Change the CNAME record to redirect traffic to Sec-Traffic Manager.
ImportantBefore you update the DNS record, verify the cloud service interaction rule by modifying the
hostsfile on your local computer. This helps you catch back-to-origin policy conflicts before they affect production traffic. CDN can change the origin host for back-to-origin requests; Anti-DDoS Proxy cannot. If you use CDN together with Anti-DDoS Proxy to retrieve data from Object Storage Service (OSS), traffic forwarded by Anti-DDoS Proxy will not be recognized by OSS, which interrupts your service. For background on origin hosts, see Configure the default origin host.
What's next
After the rule is created, perform the following operations from the General Interaction tab.
| Operation | When to use | Notes |
|---|---|---|
| Switch to Anti-DDoS | Traffic is not yet being scrubbed (the |  Available only when blackhole filtering is not active on the instance. After switching manually, traffic does not switch back automatically—click Switchback to return traffic to your cloud resource. Available only when blackhole filtering is not active on the instance. After switching manually, traffic does not switch back automatically—click Switchback to return traffic to your cloud resource. |
| Switchback | Traffic is being scrubbed by Anti-DDoS Proxy (the | 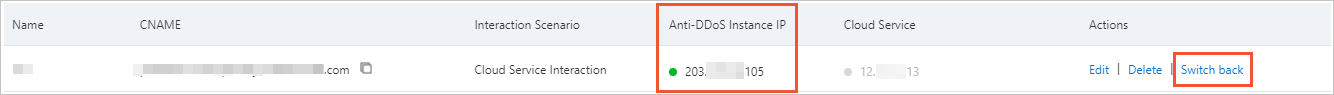 Before switching back, confirm that the attack has stopped and that your cloud resources are operating normally. This prevents the associated cloud resources from being added to sandboxes and prevents service interruptions. If blackhole filtering is active on all associated cloud resources, the switchback fails. Before switching back, confirm that the attack has stopped and that your cloud resources are operating normally. This prevents the associated cloud resources from being added to sandboxes and prevents service interruptions. If blackhole filtering is active on all associated cloud resources, the switchback fails. |
| Edit | Modify rule settings. | Interaction Scenario and Rule Name cannot be changed after the rule is created. |
| Delete | Remove the rule. | Warning Before deleting the rule, remove the Sec-Traffic Manager CNAME from your domain's DNS records. Deleting the rule while the CNAME is still in place may cause access to your website to fail. |