The Attack Analysis page shows DDoS attack events detected on your protected assets, along with detailed traffic and mitigation data for each event. Use this page to understand the scale, source, and scrubbing outcome of any volumetric attack.
Prerequisites
Before you begin, ensure that you have:
An Anti-DDoS Origin Enterprise instance. For more information, see Purchase an Anti-DDoS Origin Enterprise instance.
The assets you want to protect added to the instance. For more information, see Add objects for protection.
Query attack events
Log on to the Traffic Security console.
In the left-side navigation pane, choose Network Security > Anti-DDoS Origin > Attack Analysis.
On the Attack Analysis page, select a time range to query attack events.
NoteYou can query attack events within the last six months.
The event list shows the following fields for each attack event:
Field Description Attack Types The type of attack. Only Volumetric Attack is supported. Attack Target The asset that was attacked. Start and End Time The start and end time of the attack. Owner Account of Event The Alibaba Cloud account to which the asset belongs. Peak Attack Throughput The peak attack bandwidth (bit/s) and peak packet forwarding rate (pps). NoteIf your Alibaba Cloud account has multi-account management enabled and is the management account, you can also filter by account range:
All accounts: View attack events for assets belonging to the management account and all member accounts. The assets must be added to instances that belong to the management account.
A single member: View attack events for assets belonging to a specific member account. The assets must be added to instances that belong to the management account.
For more information, see Use the multi-account management feature.
View event details
Click View Details in the Actions column of an attack event to open the Details of the incident page.
The page is organized into the following sections.
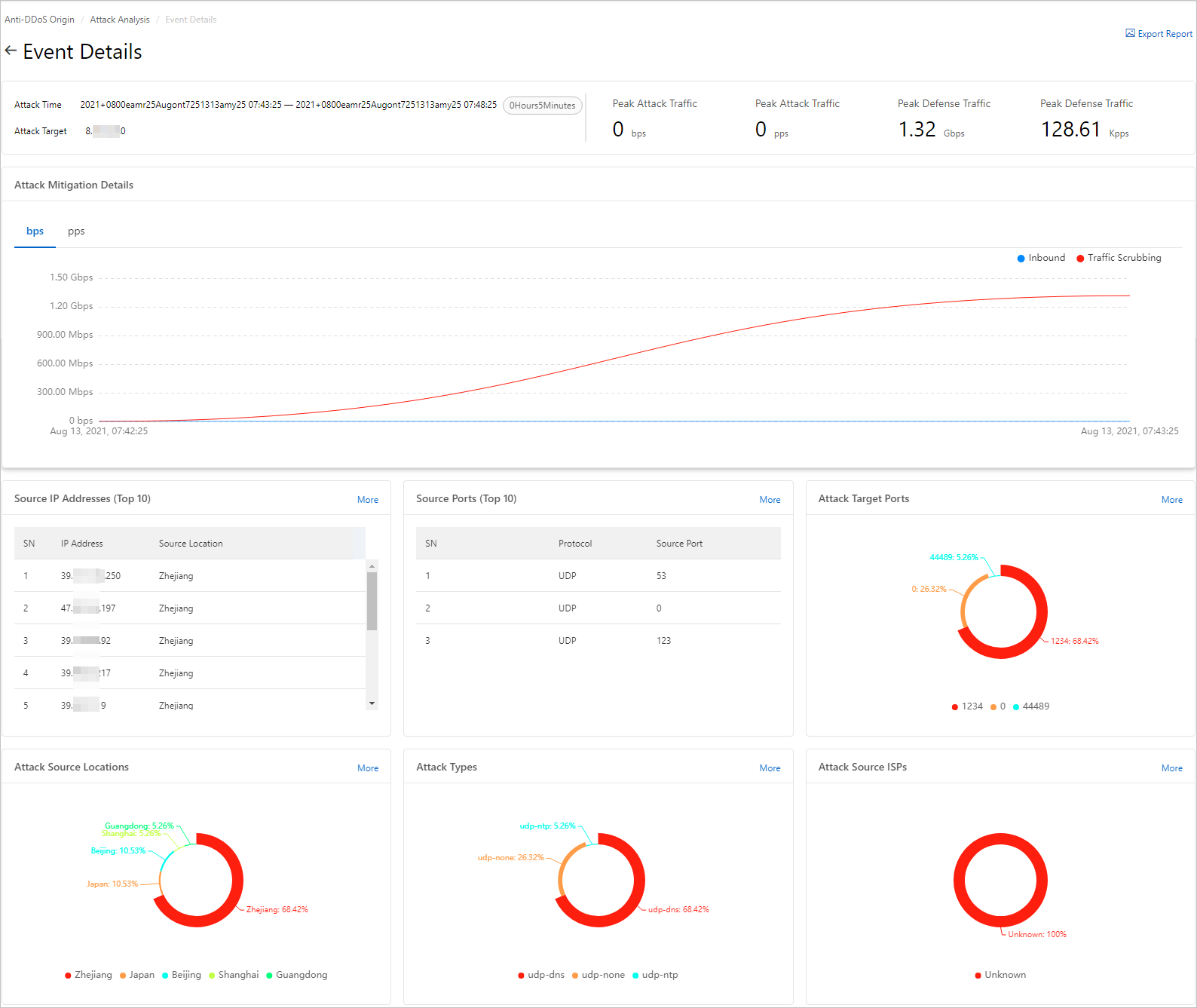
Summary metrics
The upper part of the page displays four key metrics:
| Metric | Description |
|---|---|
| Attack Time | The time window of the attack event. |
| Attack Target | The asset that was attacked. |
| Peak Attack Traffic | The peak bandwidth and peak packet forwarding rate of inbound attack traffic detected by the Anti-DDoS Origin Enterprise instance. Bandwidth is measured in bit/s and forwarding rate in pps. |
| Peak Defense Traffic | The peak bandwidth and peak packet forwarding rate of traffic scrubbed by the Anti-DDoS Origin Enterprise instance. Bandwidth is measured in bit/s and forwarding rate in pps. |
Attack mitigation details
The Attack Mitigation Details section shows time-series trends for:
Bandwidth of inbound traffic and scrubbed traffic (bit/s)
Packet forwarding rate of inbound packets and traffic scrubbing packets (pps)
Traffic dimension breakdowns
The following sections break down attack traffic by source, port, location, type, and ISP (Internet service provider). Each section shows the top 10 entries by default. Click More to view the top 100.
The requests shown in Attack Source IP Addresses, Source Ports (Top 10), and Attack Target Ports include both attack requests and normal service requests.
| Section | Description |
|---|---|
| Attack Source IP Addresses | Source locations and IP addresses of requests. Shows the top 10 IP addresses with the most requests. Click More to view the top 100. |
| Source Ports (Top 10) | Source ports and protocols of requests. Shows the top 10 ports with the most requests. Click More to view the top 100. |
| Attack Target Ports | Distribution of destination ports. Click More to view the distribution across all destination ports. |
| Attack Source Locations | Distribution of locations from which attack traffic originated. Click More to view the full geographic breakdown. |
| Attack Type | Distribution of attack types. Click More to view the full breakdown. |
| Attack Source ISPs | Distribution of ISPs from which attack traffic originated. Click More to view the full ISP breakdown. |